Author: Chloe, ChainCatcher
In September 2025, the multi-signature wallet of Web3 social platform UXLink was brutally looted. Within just a few hours, the hacker made off with over ten million dollars in assets and maliciously dumped a massive amount of minted tokens, causing the token price to flash crash by over 70% instantly. However, the most absurd part of this disaster was not the attack itself, but the hacker's "amateur" performance afterwards.
Unlike the typical money-laundering playbook, this hacker did not rush to disappear. Instead, they funneled the stolen ETH and stablecoins into DEXs, making frequent trades on CoW Swap. According to on-chain data from Arkham, this address accumulated nearly 625 transactions within just six months, with paper losses once reaching as high as $4.8 million.
Reconstructing the technical path of this attack reveals the hacker's unconventional behavior patterns and the harsh reality behind them: in the face of this bear market cycle, even with the advanced skills to steal money on-chain, once you return to market trading, everyone is on a level playing field.
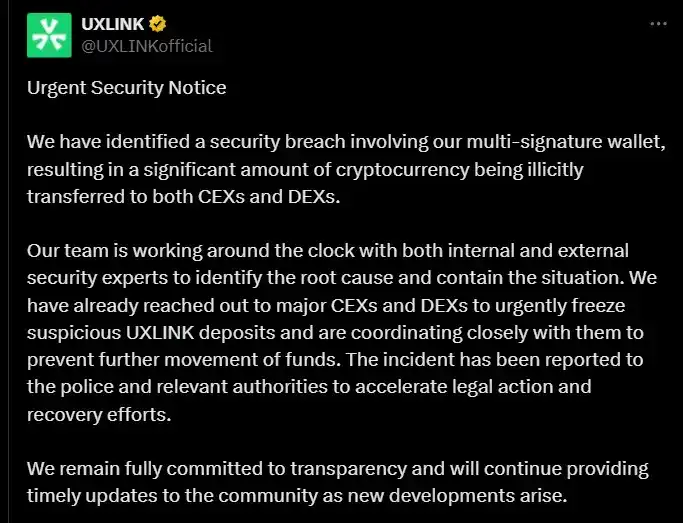
UXLink Multi-Sig Wallet Security Breach, Losses Exceed Ten Million Dollars
Blockchain security company Cyvers first detected abnormal activity in UXLink's multi-signature wallet on September 22, 2025, and issued an urgent alert. UXLink officials subsequently confirmed that their core multi-sig wallet had been compromised, with losses exceeding $11.3 million.
The technical path of this attack was quite clear. The hacker targeted a vulnerability in the multi-sig wallet's delegateCall function, successfully exploiting it to alter the contract logic. The attacker first removed the wallet's original legitimate admin permissions; then, by calling the addOwnerWithThreshold function, they forcibly inserted themselves as a new wallet owner. At this point, UXLink's relied-upon multi-sig security mechanism was completely bypassed, and control of the wallet was entirely transferred.
What followed was a frenzied looting of on-chain assets. The stolen assets included approximately $4 million USDT, $500,000 USDC, 3.7 WBTC, 25 ETH, and about $3 million worth of UXLINK native tokens. Simultaneously, the hacker minted a massive amount of UXLINK tokens on the Arbitrum chain and dumped them onto the market. The token price plummeted over 70% in a short time, crashing from around $0.30 to below $0.10, wiping out over $70 million in market capitalization.
An Unconventional Path: Abandoning Mixer Cash-Outs, Staying On-Chain to Trade and Battle
According to the standard script for crypto crime, the next act should have been: the hacker sends the assets into Tornado Cash for anonymization, launders the money in batches through countless hop addresses, and finally completes the entire money laundering and cashing-out process. But this attacker chose an unconventional path.
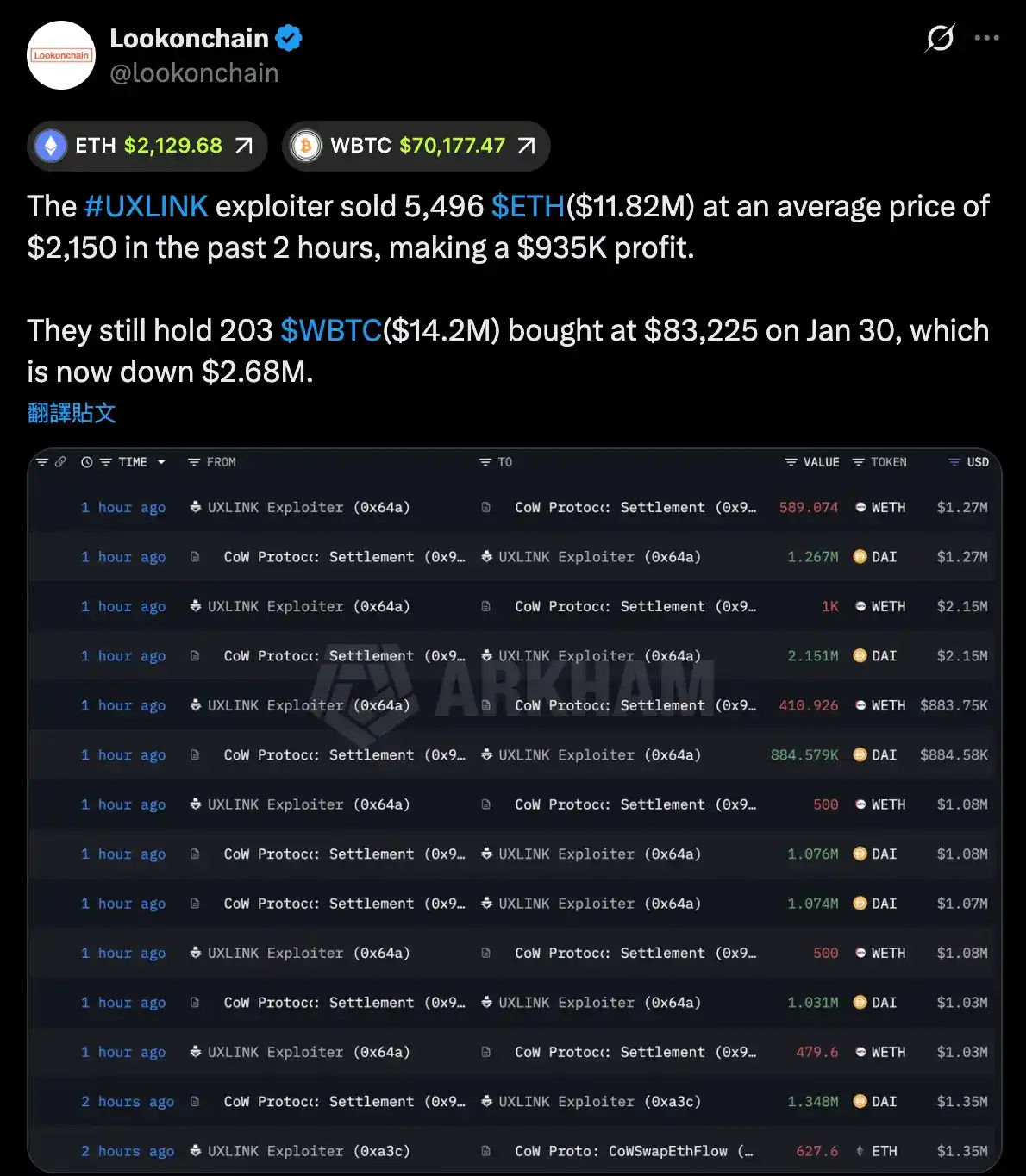
About 48 hours after the attack, the hacker exchanged 1,620 ETH for approximately 6.73 million DAI. This should have been the first expected signal of "cashing out," and several on-chain analysts promptly locked onto this on-chain behavior. However, over the next six months, this address's behavior pattern completely deviated from the calm and stealth of a professional hacker, instead embarking on a frenzy of on-chain trading.
According to on-chain data tracking by Arkham, this address accumulated a staggering 625 transaction records in just six months, with activity highly concentrated on the decentralized exchange CoW Swap. Its trading frequently switched between WETH and DAI, with an operational frequency far exceeding that of a typical long-term holder. Therefore, rather than a hacker who stole tens of millions, he更像 (more like) a trader, or perhaps a retail investor accustomed to "buying the dip, holding through volatility, and exiting only near the cost basis."
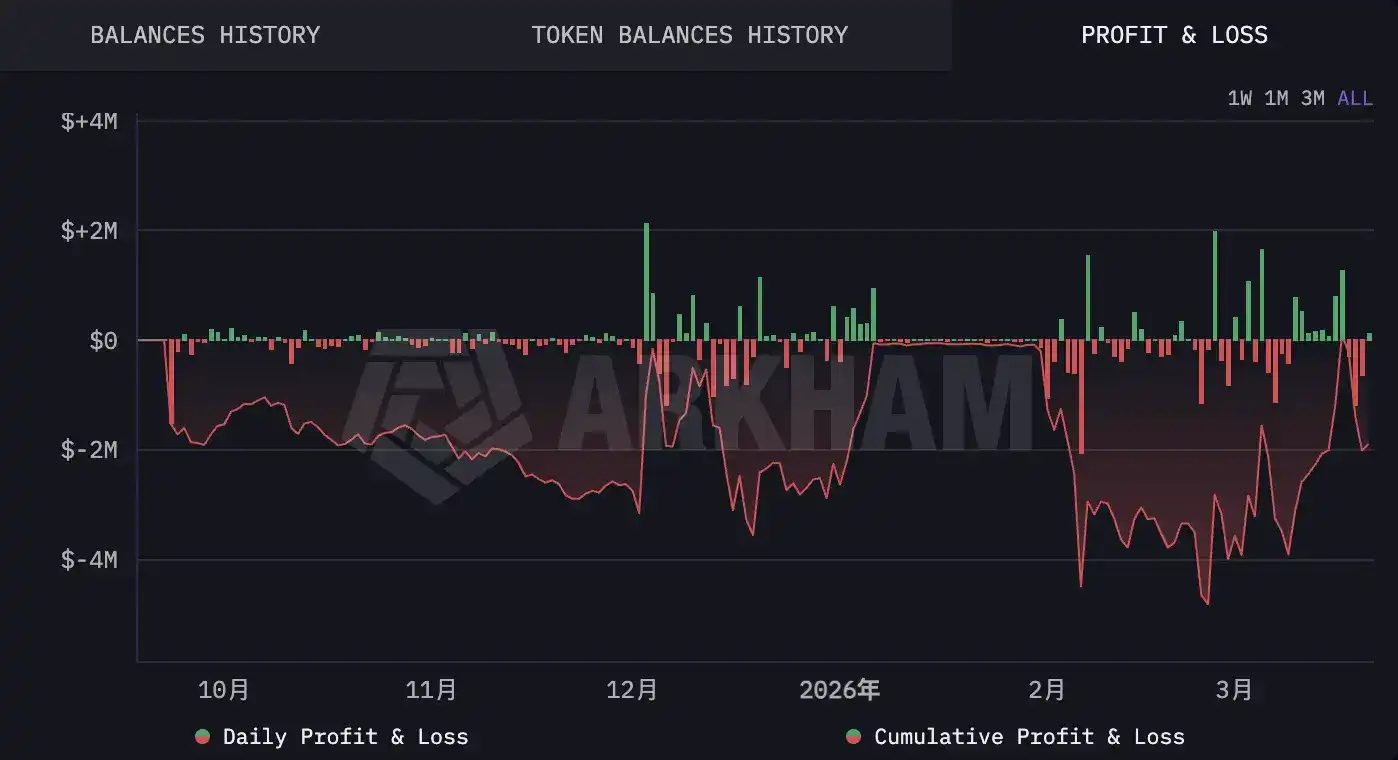
Poor Trading Skills: Paper Losses Once Exceeded $4 Million, Almost Back to Square One After Six Months
According to Arkham's P&L tracking data, from October 2025 to early February 2026, the attacker's address saw paper losses repeatedly exceed $3 million; entering February, the losses hit a record high of $4.8 million. His trading pattern was highly consistent: constantly averaging down at lows, holding on during volatility, and only choosing to exit when the price好不容易 (finally) climbed back near the cost basis.
It wasn't until late March that this hacker finally caught a break. On CoW Swap, he exchanged 5,496 ETH for approximately 11.86 million DAI at an average price of $2,150. This operation brought him a paper profit of about $935,000, finally bringing his overall portfolio back to the break-even line. However, his WBTC position was simultaneously eroding these profits. The hacker bought 203 WBTC on January 30, 2026, at an average price of $83,225. As of recently, this position was sitting on a paper loss of about $2.68 million. This entry point恰好 (coincidentally) hit a temporary market rebound high—once again, he bought at a relative peak.
The Transparent Prison and the Long Road to Recovery
The UXLink incident provides a unique perspective in the history of crypto crime: an attacker operating under the spotlight, continuously leaving highly visible transaction trails, allowing global on-chain analysts to fully document their behavioral process.
This likely did not stem from the hacker's negligence, but rather from an outdated perception of "security." He might have believed that as long as the assets were分散 (dispersed) across multiple addresses and operations were conducted on DEXs to avoid the KYC hurdles of CEXs, he could maintain anonymity. However, the rapid evolution of on-chain analysis tools has made this judgment seem overly optimistic. Institutions like Arkham, Lookonchain, PeckShield, and SlowMist almost instantly锁定 (locked onto) every large anomalous movement. Every move the hacker made was laid bare under public scrutiny. This hacker, though sitting on millions, seemed to be in a transparent digital prison.
For the UXLink project team, this situation is both a slight comfort and a significant dilemma. The assets, although not vanished, remain on the traceable blockchain; but in the on-chain world lacking jurisdictional intervention, a vast chasm still lies between "visible" and "recoverable."
Although UXLink quickly completed a new contract audit, token swap, and user compensation plan post-incident to rebuild market confidence, the token price had already fallen from its December 2024 high of $3.75 to around $0.0044, a drop of 99%. For UXLink, patching code vulnerabilities might take only weeks, but rebuilding an ecosystem from near-zero ruins remains a long and arduous journey.
The Bear Market Shows No Mercy, Treating Everyone Equally
The story of the UXLink hacker has become a microcosm of "market reality," rather than just a security incident.
Although he possessed sophisticated skills, able to precisely capture the delegateCall vulnerability and bypass multi-sig defenses, completing a meticulous harvest within hours; however, after the funds were received, he faced the same困境 (dilemma) as any ordinary retail investor: the market doesn't care where the chips came from, ETH still fell during the holding period, and BTC got套牢 (trapped) after the position was built.
This outcome warrants no pity, yet is full of irony. The assets the attacker painstakingly stole were ultimately worn down by market fluctuations, with the paper value six months later almost unchanged from entry. He is not the first ETH holder to suffer losses in a bear market, nor will he be the last speculator反噬 (burned) by the market when trying to buy the dip in WBTC.