Google’s decision to pull its post-quantum cryptography migration timeline forward to 2029 has landed hard in Bitcoin and crypto, because the company did not just change a policy deadline. It paired that warning with a new whitepaper arguing that breaking the 256-bit elliptic curve cryptography used across major blockchains may require far fewer quantum resources than many in the market had assumed.
That is the link Castle Island Ventures General Partner Nic Carter seized on in a series of X posts on Tuesday, arguing that the answer to what Google “saw” was this paper itself. The whitepaper, dated March 30 and co-authored by researchers from Google Quantum AI alongside Justin Drake and Dan Boneh, lays out updated estimates for attacking the secp256k1 curve that sits at the center of Bitcoin-era signature security.
Specifically, this paper. It’s a brand new resource estimate that’s wildly lower than prior estimates of what it would take to break ECC-256. Featuring the Google Quantum AI team + Justin Drake + Dan Boneh https://t.co/dYRld7HbJY pic.twitter.com/qXlAvzBQkv
— nic carter (@nic_carter) March 31, 2026
In Google’s formulation, Shor’s algorithm could solve the target problem with either no more than 1,200 logical qubits and 90 million Toffoli gates, or no more than 1,450 logical qubits and 70 million Toffoli gates. On a superconducting architecture, the authors say those circuits could run in minutes with fewer than half a million physical qubits.
That is the real shock to the Bitcoin threat model. Google’s March 25 blog post said the company moved to a 2029 migration target because of progress in quantum hardware, error correction and quantum factoring resource estimates, and said it had already adjusted its threat model to prioritize post-quantum migration for authentication services. The crypto paper then gave markets a concrete reason for why that deadline may have moved.
The paper is also unusual in how it handles disclosure. Rather than publishing the attack circuits in full, the authors say they used a zero-knowledge proof to validate the results without leaking sensitive details. Google framed that as a responsible-disclosure choice in a field where public discussion can itself create fear and instability, especially when the assets in question are bearer instruments with no recourse layer.
That choice fed directly into the reaction on X. Dragonfly’s managing partner Haseeb Qureshi called the result “wild,” writing: “Google Research demonstrates a ~20x more efficient implementation of Shor’s algorithm that could break ECDSA keys within minutes with ~500K physical qubits. Google is now are more confident on a 2029 post-quantum transition. We are no longer looking at mid 2030s, we could have quantum computers of this scale by the end of the decade.”
He added that Google’s decision not to publish the actual circuits, and instead publish a proof that they exist. “They believe this result is so severe that they are not publishing the actual circuits. They instead published a ZKP proving that they know of the quantum circuit with these properties. This is very atypical, showing Google thinks this is serious shit. All blockchains need a transition plan ASAP. Post-quantum is no longer a drill,” he added.
This is wild. Google Research demonstrates a ~20x more efficient implementation of Shor’s algorithm that could break ECDSA keys within minutes with ~500K physical qubits.
Google is now are more confident on a 2029 post-quantum transition. We are no longer looking at mid 2030s,... https://t.co/jGzFk5uLc0 pic.twitter.com/O4V1VbiXkf
— Haseeb >|< (@hosseeb) March 31, 2026
Ethereum Foundation researcher Justin Drake pushed the same point even further. “Today is a monumentous day for quantum computing and cryptography. Two breakthrough papers just landed,” he wrote. “The results are shocking. I expect a narrative shift and a further R&D boost toward post-quantum cryptography.”
In a separate post, he added: “My confidence in q-day by 2032 has shot up significantly. IMO there’s at least a 10% chance that by 2032 a quantum computer recovers a secp256k1 ECDSA private key from an exposed public key. While a cryptographically-relevant quantum computer before 2030 still feels unlikely, now is undoubtedly the time to start preparing.”
Today is a monumentous day for quantum computing and cryptography. Two breakthrough papers just landed (links in next tweet). Both papers improve Shor’s algorithm, infamous for cracking RSA and elliptic curve cryptography. The two results compound, optimising separate layers of...
— Justin Drake (@drakefjustin) March 31, 2026
For Bitcoin specifically, the most important part of the paper is not some vague future threat to “crypto,” but the distinction it draws between attacks on dormant or exposed keys and attacks on live transactions. The authors argue that fast-clock architectures such as superconducting and photonic systems could eventually enable “on-spend” attacks, where a public key exposed during transaction flow is broken quickly enough to race the original payment into a block.
Their estimate explicitly says fast-clock systems could solve ECDLP in about nine minutes on average, putting Bitcoin’s roughly 10-minute block cadence uncomfortably close to the attack window. The paper points to private mempools and commit-reveal schemes as possible mitigations, but treats migration to post-quantum cryptography as the actual answer.
Just as important, Google tries to narrow the panic. The paper says quantum attacks on Bitcoin proof-of-work via Grover’s algorithm are not a practical concern “in the next several decades,” arguing that discussion should stay focused on signatures, not mining. That matters because it shifts the debate away from network collapse scenarios and toward wallet design, key exposure, mempool privacy and upgrade coordination.
The broader message is hard to miss. Google’s paper ends by urging “all vulnerable cryptocurrency communities to join the migration to PQC without delay,” and its separate security timeline now points to 2029, not some comfortably distant date in the mid-2030s.
Bitcoin has spent years treating quantum risk as a long-range problem. What changed this week is that a major quantum lab put a much tighter engineering estimate around the threat, and some of the sector’s most technically literate observers immediately started talking less about whether the transition will be needed and more about how fast it has to begin.
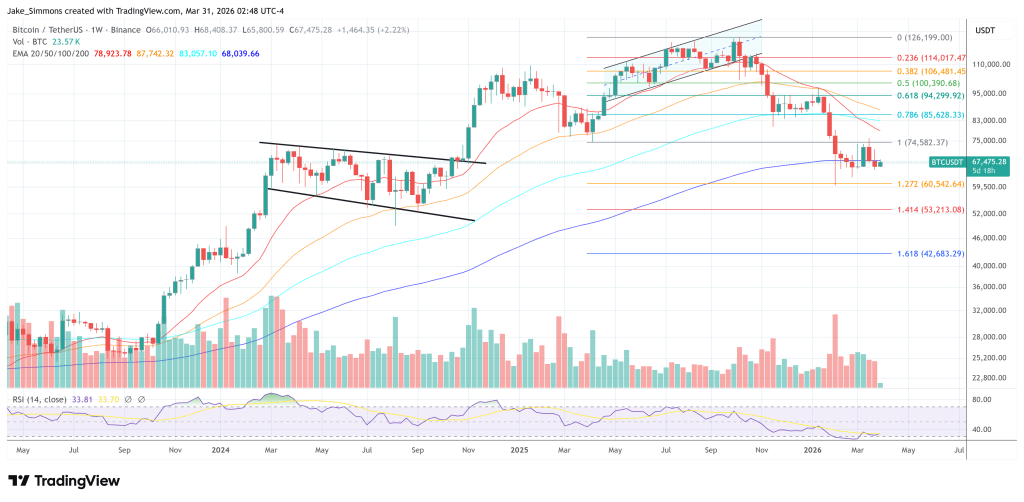
At press time, Bitcoin traded at $67,475.