The Real Quantum Threat to Bitcoin: 99% of People Get It Wrong
Quantum Computing's Real Threat to Bitcoin: 99% Misunderstand
The article clarifies widespread misconceptions about quantum computing's threat to Bitcoin. Key points:
- Bitcoin uses digital signatures, not encryption, making "collect now, decrypt later" attacks irrelevant.
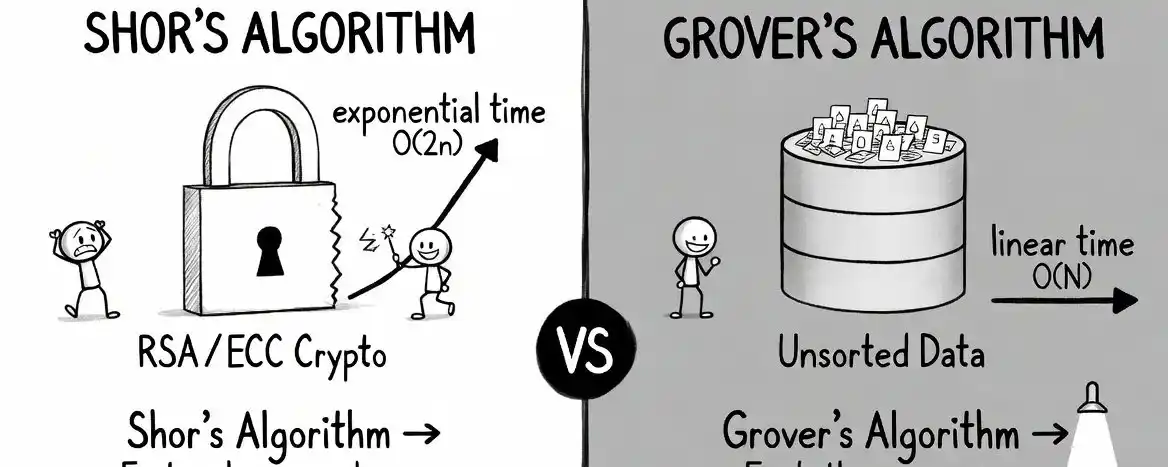
- Quantum computers cannot crack Bitcoin mining (requires energy exceeding the sun's output) but threaten signatures via Shor's algorithm.
- Only ~6.26M BTC (30-35% of supply) are at risk due to exposed public keys (legacy P2PK, reused addresses). Modern unused addresses remain safe.
- Media exaggerations (e.g., "9-minute break") misrepresent research; actual quantum attacks require non-existent hardware and are likely decades away.
- Bitcoin can upgrade (BIP-360 proposes post-quantum signatures), but the community must accelerate efforts (estimated 7-year timeline).
- The real urgency stems from classical cryptographic risks (e.g., mathematical breakthroughs breaking secp256k1), not just quantum threats.
- Recommendations: avoid address reuse, monitor BIP-360, migrate to quantum-resistant addresses when available, and ignore sensationalized headlines.
Conclusion: The threat is real but distant. Panic is unwarranted, but complacency is dangerous. Proactive engineering is essential.
marsbit04/07 10:32