Author: Zero Time Technology
Preface
With the rapid development of DeFi, "Decentralized Finance" has evolved from a niche toy for geeks into fertile ground for ordinary people chasing high yields. Staking, liquidity mining, lending for interest... various strategies emerge endlessly, with annual percentage yields (APY) often reaching tens or even hundreds of percent, making it hard to resist.
However, the flip side of yield is risk. On April 1, 2026, Solana's leading perpetual contracts DEX, Drift Protocol, suffered a major attack, with losses estimated between $220 million and $285 million, making it the largest DeFi hack of 2026 so far.
This event once again sounds the alarm: In the DeFi world, there is no customer service to help you recover funds, no bank to back you up. Every interaction is your full responsibility for your assets.
To help everyone avoid risks, the Zero Time Technology security team, based on real attack cases, has summarized 5 key security checks that must be completed before participating in DeFi. These will help you identify risks before you act and safeguard the bottom line of your asset security.
How is DeFi Risk Actually Happening?
Many people think hacker attacks are far away from them, but the reality is: most asset losses occur during users' "normal operations."
You didn't do anything particularly wrong, you were just negligent in one step. Here are the four most common risk pathways:
1. Improper Approval → Assets Transferred Away
You clicked "Approve" once, granting the contract unlimited permission to access your wallet. Once the contract turns malicious or gets hacked, assets are emptied instantly.
2. Visiting a Phishing Website → Wallet Compromised
You searched for a project, clicked the top ad link, and the page looked exactly like the official site. After connecting your wallet, your seed phrase or signature was already captured by the hacker.
3. Contract Vulnerability → Funds "Legally Stolen"
The project itself is legitimate, but the code has a vulnerability. Hackers exploit the vulnerability to bypass restrictions and extract funds from the protocol's treasury—your assets are among them.
4. Project Rug Pull → Liquidity Drained
The project team was a scam from the start. Once enough of your funds are deposited, they directly withdraw the coins from the liquidity pool, and the token's value instantly drops to zero.
Understanding where the risks come from, the following 5 checks will show you exactly where each measure strikes.
✅Check 1: Contract Security — Open Source + Audit is the Baseline
Many people have their assets stolen not because hackers are highly skilled, but because the project contract itself is "toxic."
⚠️Your goal is not to "trust the project," but to:
•Is the code open source: Check on a block explorer (like Etherscan, Solscan) if the contract is "Verified." An unopen-sourced contract is like hiding the rules in a black box—don't touch it.
•Has it been audited: Go to audit firm websites like CertiK, PeckShield, SlowMist, search for the project name, confirm there is a genuine audit report, and that critical vulnerabilities have been fixed.
•Does it have a history of vulnerabilities: Use third-party platforms like DeFi Safety, RugDoc, input the contract address, and check the security score and past risk records.
🚩High-Risk Signals:
•Contract not open source
• No third-party audit report, or only "self-audited"
• Contract deployed just days before launch
🔗Pro Tip: On the block explorer's "Contract" page, if you see "Source Code Not Verified," close the page immediately.
✅Check 2: Authorization Management — Don't Let Contracts Have "Unlimited Withdrawal"
Many people have their assets stolen not by being hacked, but by approving contracts they shouldn't have. Clicking "Approve" once is like giving the contract a key—if that key is a "master key," the contract can open the door to all assets of that type in your wallet at any time.
⚠️Key Checks
•Is it requesting "unlimited approval": In the approval pop-up, if the amount shows "unlimited" or the uint256 maximum value. This means the contract can transfer an unlimited amount of your assets, not limited by the amount you deposited.
•Is it an unfamiliar contract address: Carefully verify the contract address of the approval target. Does it match the address published by the project's official channels? A difference of one letter could be phishing.
👉Recommendations
•Prefer "Minimum Approval": When approving, manually change the amount to the quantity needed for the current transaction. For example, if you are only depositing 0.1 ETH, set the approval amount to 0.1 ETH. Wallets like Rabby and customized MetaMask versions support this feature.
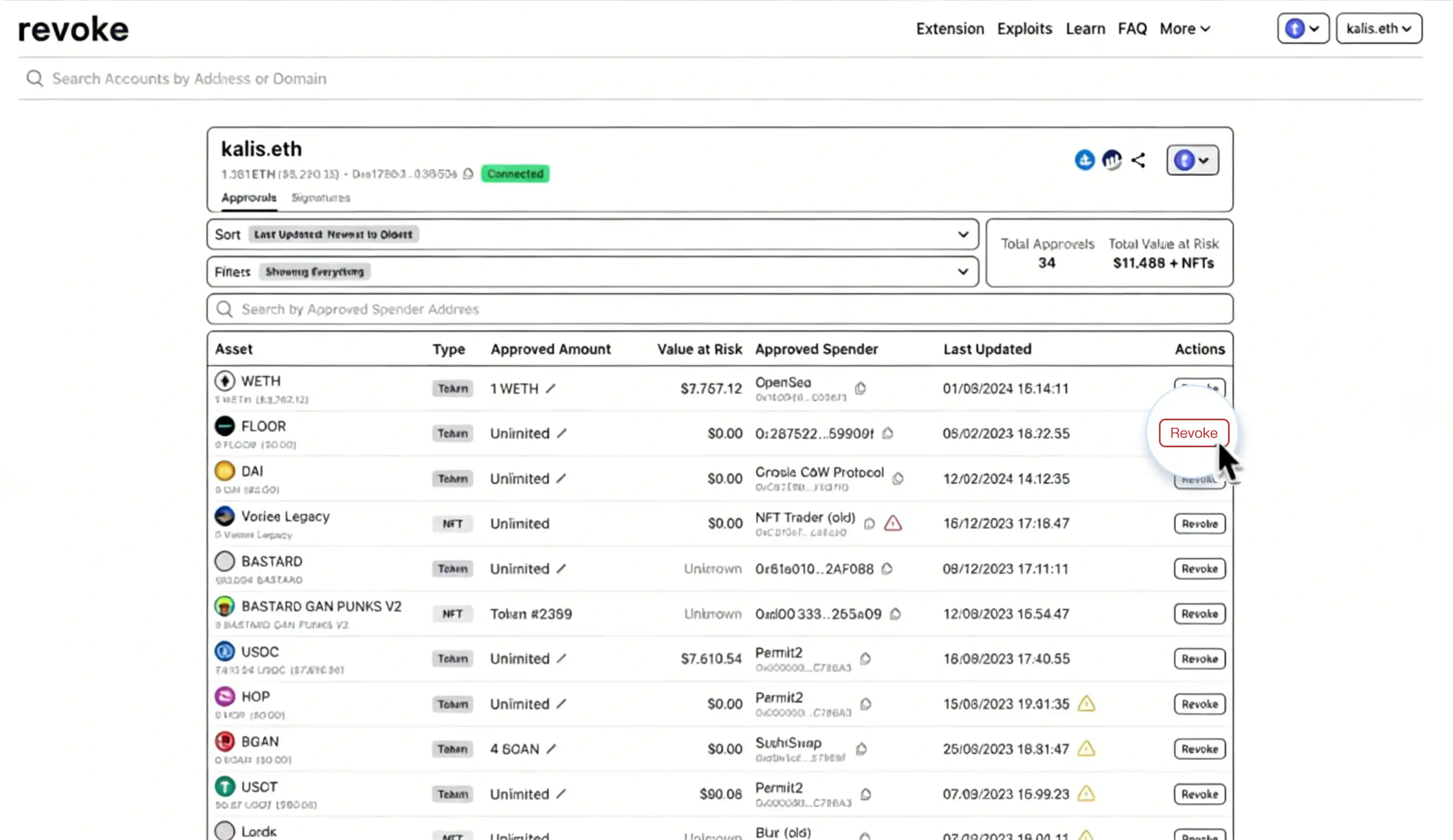
•Regularly Review Approvals: Visit revoke.cash or etherscan.io/tokenapprovalchecker to see which contracts you have approved. If you find suspicious or unrecognized ones, revoke them with one click.
Example interface from revoke.cash website. The circled "Unlimited" approvals are recommended to be revoked promptly.
✅Check 3: Official Entry Points — Phishing Sites Are Scarier Than Hackers
According to statistics, over 60% of DeFi asset losses come from phishing attacks, not contract vulnerabilities.
⚠️Common Tactics
•Imitating Official Websites: Domain names differ by only one letter (e.g., uniswap.com vs uniswao.com), with the page completely copied.
•Fake Airdrop Pages: Promoting "free XX airdrop claims" on Twitter, Discord. After connecting your wallet, approvals are used to transfer assets away.
•Search Engine Ad Poisoning: Searching for "Uniswap," the first ad might be a phishing site with a domain name extremely similar to the official one.
👉Recommendations
•Only Enter Through Official Channels: Get the official link from the project's official Twitter, Discord announcements, or GitHub repository. Do not trust search engine ads.
•Bookmark Frequently Used DeFi Sites: Add the official websites of protocols you often use to your browser bookmarks and always enter from there.
•Don't Click Unfamiliar Links: Be suspicious of any link sent by anyone (including group members, private messages).
🔗Pro Tip: Install wallet extensions like Rabby or MetaMask's phishing detection version; they automatically block known phishing domains.
✅Check 4: Abnormal Yields — High Returns Inevitably Hide High Risks
If a project:
• Offers APY far above the average market rate (e.g., stablecoin APY over 20%)
• Emphasizes "risk-free arbitrage," "guaranteed profits"
• Encourages "early participation, quick investment," creating FOMO (Fear Of Missing Out) sentiment
It can basically be judged: Risk ≈ Promised Return × 10
Many Rug Pull projects use "high yield" to attract liquidity. Their initial yields might come from new users' principal (a Ponzi scheme). Once the inflow of new funds slows down, the project team directly pulls the liquidity and runs away.
👉Recommendations
•Compare to Market Benchmarks: Mainstream DeFi protocols (like Aave, Compound) typically offer stablecoin APY between 2% - 8%. Be highly vigilant if it's 3 times higher than this range.
•Check the Project's Lifespan: Projects offering super high yields just days after launch are likely "honeypots."
•Search Project Name + scam / rug: Use Google or Twitter search to see if there are user reports.
🚩 One Rule: If it seems too good to be true, it probably is.
✅Check 5: Asset Isolation — Don't Put All Your Eggs in One Wallet
Many users only have one main wallet, where all assets, all DeFi interactions, and all NFT mints are done. Once this wallet is phished, approves a malicious contract, or has its private key leaked, all assets are wiped out at once.
Recommend establishing a "Three-Wallet" system:
⚠️The essence is: Control single-point risk, avoid "total loss in one go"
• Participate in new projects or unverified protocols always using a temporary wallet, depositing the minimum amount required for testing.
• Regularly clean approvals for the interaction wallet (weekly or monthly).
• Keep core assets in a cold wallet, never sign, never approve, never connect to any website.
More Frightening Than Hackers Are the "Insiders"
Besides external attacks, there is another often overlooked risk—malicious insiders. They could be developers, operations staff, or even customer support.
⚠️Where do internal threats come from?
• Developers or auditors planting backdoors: Developers and auditors have commit access and system access. If any one of them turns malicious, they can plant backdoors, steal sensitive keys, and it's hard to detect as it's disguised as normal development activity.
• Core permission managers stealing: Those holding the admin private keys, if they have ill intentions, can empty all user assets in one go.
• Employees exploiting job permissions to steal user information: In February 2026, a 34-year-old network engineer at a Hong Kong cryptocurrency investment company used his system access rights to unauthorizedly log into the company database and stole approximately 2.67 million USDT (about HK$20.87 million) from about 20 clients. This employee had been with the company for 4 years, responsible for APP development and maintenance—it was this "legitimate access" that enabled the theft.
👉How to prevent?
• Individual Users: Choose protocols with a "timelock" (major operations require a 24-48 hour delay), pay attention to whether the project's multi-signature managers are publicly transparent.
• Project Teams: Core permissions must be managed with multi-signature wallets, set a timelock buffer period, and regularly audit internal access logs.
Why Do You "Get Hit" Even When You're "Very Careful"?
Because attacks have shifted from "technical vulnerabilities" to "human vulnerabilities."
⚠️Common Psychological Pitfalls
• "This project is hot, it should be fine"
• "Everyone is using it, nothing will happen"
• "I'll only do it once, it won't be me"
👉 The reality is: Attackers only need you to make one mistake
⚠️New Trend: AI + Phishing Attacks
• Highly imitated official website pages
• Automatically generated customer service dialogues
• Precisely targeted user投放 (投放 -投放 means delivery/targeting)
👉It's becoming increasingly difficult for users to distinguish real from fake
The Simplest Set of DeFi Security Principles
If you can't remember all the checks, remember these 3 👇
• Don't approve recklessly
• Don't click unfamiliar links
• Don't go All in on one project
🔑 In a nutshell: The risk in DeFi is not in the code you don't understand, but in every operation you overlook.
Conclusion
DeFi has brought openness and freedom, but also new security challenges. From the Drift Protocol incident to daily phishing attacks, risk has long shifted from "extreme events" to "constant threats."
Facing the complex on-chain environment, what truly protects assets is not luck, but awareness and habits.
If you have doubts about the DeFi project you are currently using, it is recommended to conduct a security check as soon as possible.
👉In the on-chain world, security is not an add-on; it's the entry ticket.