Abstract
Web3 computing has room to grow in the decentralized cloud computing, AI blockchain network and Decentralized Virtual Private Network (VPN) segments.
The problems in Web2 today are largely characterized by security breaches due to single point of failure, big tech dominance arising from data colonialism and privacy breaches suffered by centralized VPN enterprises.
Web3 computing will share the Web2 computing market in the near future. The demand for Web3 computing will be reliant on demands from other blockchain networks, NFT data links and marketplaces, Augmented Reality, Virtual Reality and Peer-to-Peer (P2P) enterprises.
Web3 AI processing and computing power will solve the process of automation by making use of on-chain data. Data fed by users could drive the neural network to learn much faster than Web2 today. In Web3, the AI networks will aggregate and develop AI functions for each user. The partnership between AI and blockchain has the potential to speed up automation processes in the future. Such automation takes place in supply chain, manufacturing, oracles and personal artificial intelligence. It is hoped that on-chain AI will develop the artificial general intelligence to solve problems which humans are not capable of solving today.
The targeted Decentralized Virtual Private Network (dVPN) market focuses on private connections via the power of citizens worldwide. dVPN has the potential to become the market player to secure user privacy in order to counter big tech censorship and also powerful entities who have traditionally profited at the expense of user data privacy. In the future, dVPN will solve the problems arising from single point of failure and privacy breaches from big tech dominance.
Decentralized computing will firmly become the backbone for the processing, networking and computing of blockchain data — the massive virtual data center of the blockchain world.
1. Problems with centralized cloud computing
Cloud computing has experienced exponential growth since 2020. Meanwhile, Global IT Spend forecast also has a CAGR of 20%. Since the Covid-19 pandemic, the work from home trend has also driven the adoption of cloud computing. Many top firms and industries rely on cloud computing for revenue, including Tesla and Nio in the electric vehicle industry and Nvidia and AMD in the data and chip production industry. The growth in worldwide entire IT capital spend is expected to hit US$15 trillion from 2022 to 2030.

Figure 1: Nvidia powering AV revolution
Source: Investor.nvidia.com
Figure 2: NVDA stock price dips
Source: Tradingview.com
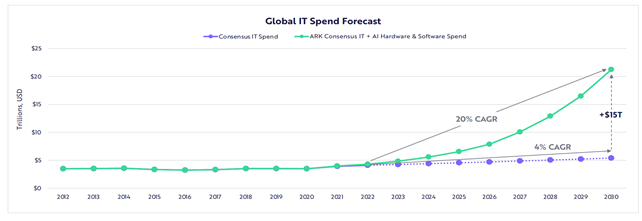
Figure 3: Global IT Spend Forecast
Source: Research.ark-invest.com
On top of cloud computing, the AI industry is also experiencing tremendous growth. According to Arkinvest 2022, projected hardware spend driven by AI has a CAGR of 102% from 2021 to 2025. Machine learning and deep neural networks as elements of AI are the main driver behind the automation of everything by machines. However, the development of AI also faces a bottleneck because machine learning requires a large amount of data. Due to this, data collection is hampered by user privacy. Also, a large amount of financial resources are key for developing AI. Financial resources and data collection are barriers to AI. This presents the requirement for the blockchain network to protect user privacy, while native tokens can be used to incentivize the research and development of AI.
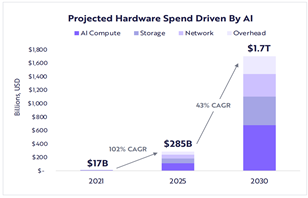
Figure 4: Projected hardware spend driven by AI
Source: Research.ark-invest.com
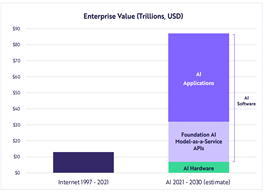
Figure 5: Enterprise value comparison
Source: Research.ark-invest.com
However, privacy and data protection concerns linger. In 2021, the total number of data breaches on 500 and more healthcare data records stood at 700, more than three times the 2010 figure of 199. The number of data breaches also went up exponentially from 157 in 2005 to 1001 million in 2020.
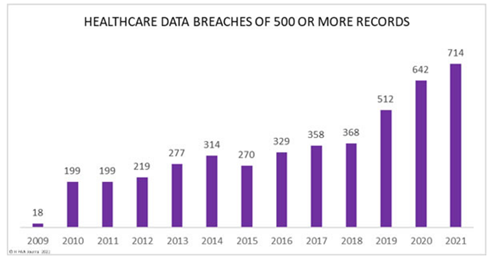
Figure 6: Healthcare Data Breaches by Year
Source: www.hipaajournal.com
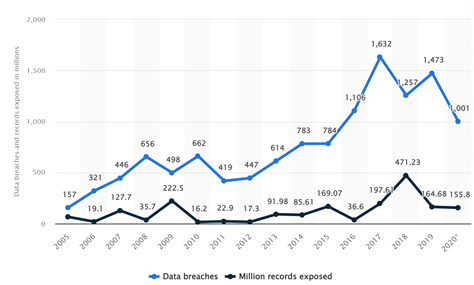
Figure 7: Annual number of data breaches and exposed records in the United States from 2005 to 2020
Source: www.statista.com
The reason for the significant amount of data hacks due to centralized entities is because data is stored, transferred and networked. A single set of single nodes are responsible for protecting multiple data sources during the computing process — a single point of failure.
Data colonialism is another issue. Data is often referred to as the oil of the current century, with big techs dominating the data market. As most of the data is collected by big tech through different use cases, giants such as FANMAG dominate collection of user behavioral data. Now, even Tesla is acquiring driver behavior data through adoption of Electric Vehicles and FSD (full self-driving). Big tech basically collects user behavior data and sells it back to the people. For example, a person searches for a pair of shorts on Facebook and joins private groups that sell secondary clothes and accessories. The person then goes to Instagram and ads appear show up with displaying shirts and shorts. The person feels attracted to the ads. The ads lead the person to an online apparel shop and closes the deal with the Instagram user. Facebook, who owns Instagram, makes revenue from the apparel shop because Facebook formed a contractual relationship with the shop using the URL link from Instagram.
Figure 8: Big tech dominance on privacy
Source: https://edri.org/our-work/how-big-tech-maintains-its-dominance/
Blockchain may be the possible solution to such privacy concerns. The blockchain network could act as decentralized cloud computing network to support AI development and protect privacy through dVPN.
2. What is Web3 computing and AI
Cloud computing refers to service providers providing processing power for the client through connections with the internet. Web3 computing is categorized into the following 3 items, with different use cases:
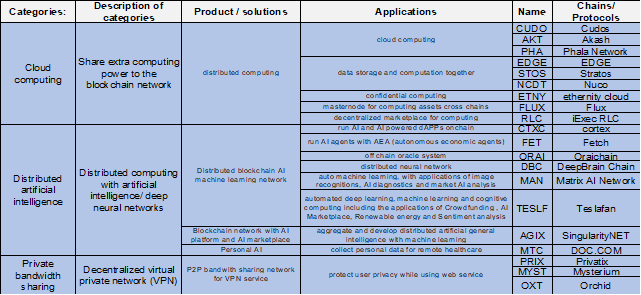
Table 1: Categories of Web 3 computing products
Source: Huobi Research Institute
What is Web3 computing? Web3 computing comprises distributed computing and a decentralized blockchain network. Cloud computing is explained above as the provision of processing power over the internet. Cloud computing applications are mainly classified into data processing, data transfer and networking. For example, Spotify uploads their user data to Amazon Web Services (AWS). Spotify software engineers want to compute user analytics using AWS, like daily user activity surge and daily hottest daily podcasts. The user data is uploaded to AWS’s database. The data is networked and processed from different loads of AWS from the storage basis to computing basis within the server. The results are transferred back and stored in the AWS as database. In such a case, the Web2 server and network is provided as a centralized service, which poses a threat to data protection due to having central point of failure. The blockchain network thus absorbs values that used to be stored in centralized entities. The distribution channels, data networking and processing are secured by the blockchain network.
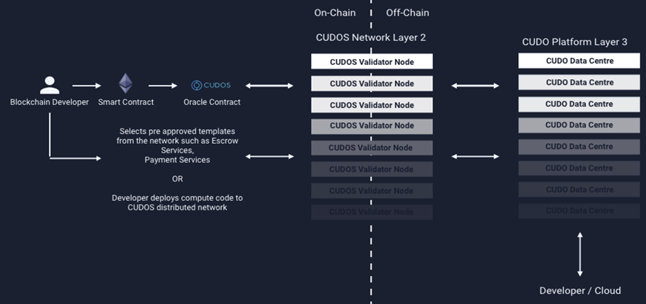
Figure 9: Cudos validator networks
Source: Cudos whitepaper
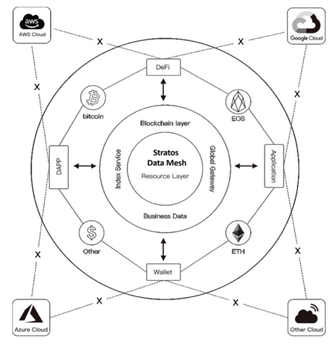
Figure 10: Stratos data mesh, Web 3 computing network links data flow to other blockchains and applications
Source: Cudos whitepaper
In Web3 computing, computing power from each user is shared across the blockchain network to process data. User data is protected using the private key while the data is computed and verified by the public key. The data is uploaded on-chain while the identity of the user is hidden for privacy protection. After that, the data is networked from blocks to miners in a proof of work system or validators in a proof of stake system. The miners and validators compute data from the blocks and generate results. For example, if Audius is bridged to Cudos, Audius artists will be able to upload their user and streaming activity data to Cudos. The blocks are split to different Cudos validators. Cudos validators receive the data and process the daily activities to spot streaming pattern, including distribution of users based on geographical location. Cudos validators only know the public key of the Audius artists, but the validators do not know the private keys and private information of the artists. Therefore, the privacy of the Audius artists is protected. At the end of the computing contract, Audius artists receive the streaming results data pattern from the Cudos networks.
Blockchain distributed cloud computing can also be described as the Web3 Airbnb network. The extra processing power can be conceptualized as spare real estate or an empty apartment owned by real estate owners and rented out through the Airbnb network. In Web3, the network is distributed with encrypted data protection. The Airbnb users buy the Airbnb rental offers of extra room to stay for a duration of time and pay for the duration of stay. Likewise, Web3 computing users pay the computing service providers for the computing duration needed for results to be generated. The Airbnb apartment can be likened to the extra processing power in the computers.
After cloud computing received sufficient development, mainstream enterprises started to adopt artificial intelligence. The adoption of cloud computing has facilitated the utility of artificial intelligence. For example, Nvidia increases a large proportion of research and development costs to increase the number of data centres, while part of the funds is used to develop deep learning and deep neural networks. Meanwhile, the multi-GPU-accelerated training also cultivates room to develop AI, including PyTorch, TensorFlow (Google), PaddlePaddle, MXNet and Deep Graph Library.
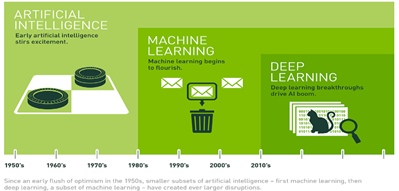
Figure 11: Artificial intelligence development timeline
Source: https://investor.nvidia.com/home/default.aspx
AI is also closely linked with the blockchain network and can be used to provide predictive models for users via the blockchain. For example, in PAI network, the deep neural network is used to provide data for the generation of personal artificial intelligence that is responsible for socializing with different clients on behalf of the user, such as speaking to Airbnb customers about travel itineraries and local food guide.
VPN (virtual private network) has also found a spot in the Web3 space. VPN originally served as a private channel for nodes to communicate with one another in a censorship-resistant environment. However, the data generated by users in such an environment is collected by single or a group of companies — resulting in a single point of failure. In Web3 VPN, otherwise known as dVPN (decentralized virtual privacy network), the blockchain is involved.
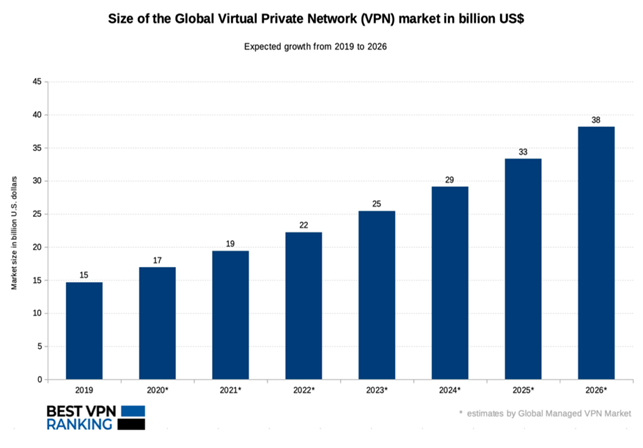
Figure 12: Size of the global virtual private network (VPN) market
Source: https://bestvpnranking.com/vpn-market-size-in-2020/
Therefore, the future of Web3 computing will develop in the categories of decentralized cloud computing, distributed artificial intelligence and decentralized virtual privacy networks.
3. Web3 computing adoption & market potential: Where are we headed?
The computing world has evolved from when users originally used hardware desktop computers to process data, to how laptops are now used to compute and retrieve data from Web2 cloud providers. After considering market potential, the mechanism of each category of Web3 computing will be explained and compared below:
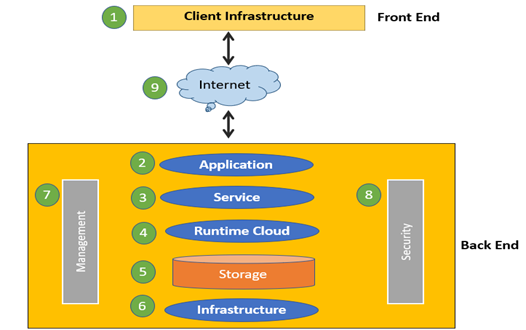
Figure 13: Cloud computing frontend & backend
Source: www.guru99.com
NFT marketplace and metaverse are the next milestones for the Web3 computing path. Up until now, most NFT content and metaverse processing spaces have been placed in Web3 servers. Single point of failure will be the weakness if Web2 servers still conduct the majority of backend processing. As most blockchains only store and process the NFT transaction data, most content like graphics, jpeg and mp3 are currently not stored and processed on-chain. If hackers infiltrate the backend by Web2 back doors, the data will be void. According to the above figure, cloud computing algorithms basically follow such frontend and backend designs. Basically, data networking, transfer and processing goes with the security, data management, storage, runtime cloud, services and application. For the time being there are loads of blockchain protocols that provide decentralized storage like Arweave and Filecoin. However, most other parts of data computing rely on Web2, including security, service, application and runtime cloud, where the cloud provides runtime and execution environment for virtual machines. This is the case when NFT transactions are processed with faults and malicious activities. Processing images, graphics, audio augmented reality and virtually reality will gain market share for distributed computing for a more secure and decentralized economy for the NFT marketplace, which saw US$3.5 billion in trading volume in April, a 40% gain over March 2022.
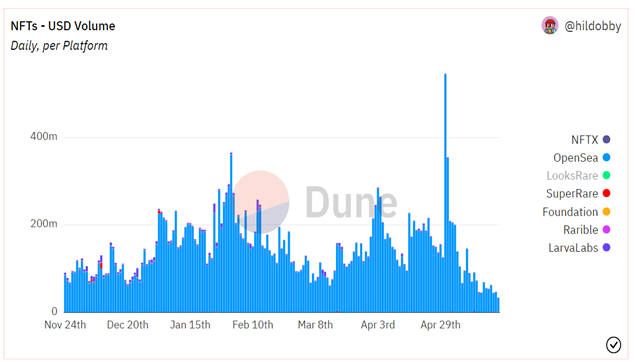
Figure 14: NFT daily trading volume
Source: Dune analytics
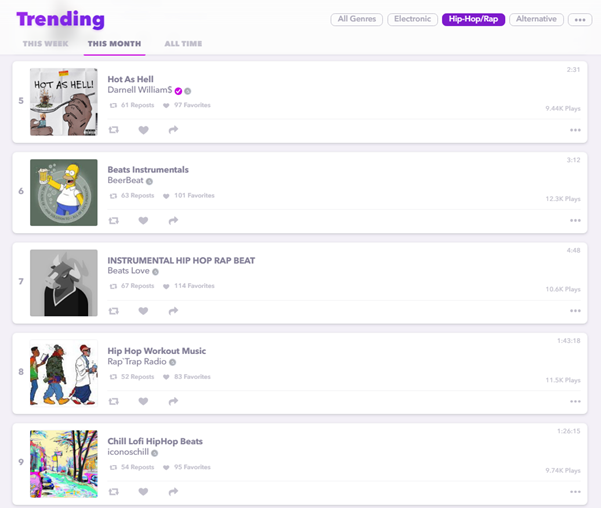
Figure 15: Audius’ trending song list
Source: https://audius.co/trending
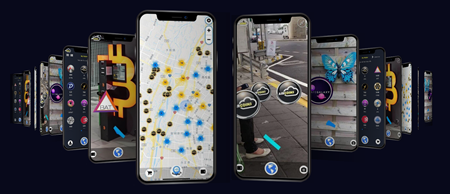
Figure 16: AirCoin’s play-to-earn user interface
Source: https://www.aircoins.io/
Apart from NFT & metaverse, on-chain data also has the potential to command a firm position in the data computing marketplace. For example, Akash is providing a peer-to-peer cloud computing marketplace for Bitcoin mining. Cudos, another decentralized computing network, has use cases for 3D rendering, machine learning simulation and medical modelling/imaging. Permaweb, a protocol built on Arweave, uses data stored on Arweave to compute a decentralized web. The permaweb uses HTTP as a web format, completely similar to Web2, but uses decentralized data network storage node to link up a decentralized web with permanent data storage.
The combination of AI and blockchain can be applied to complex applications in everyday industrial scenarios. There are loads of demands from processing and artificial intelligence including cross industry analytics, data types processing. The examples include customer service, car manufacturing, healthcare, market trading analytics and supply chain.
The market share of dVPN concerns the growing need for privacy. Data is computed on-chain without disclosing any of the computing searchable solely using public data. This decentralized virtual privacy channel is the Web3 form of Web 2 VPN. It distributes the computing power to process and network data channels for users in a blockchain network.
However, the artificial intelligence and deep neural network market is at an early stage of development, and the market has not established a proposition for the value of such products. In 2022, the total market capitalization of AI is only US$37 billion, which accounts for only 24% of the total AMD marketcap, 8.7% of NVDA and 7.8% of TSM, the three leading chip producing companies.
The combination of artificial intelligence and blockchain computing signal the beginning of the road to the Web3 market. The AI blockchain computing network needs a time to evolve and develop where an MVP could be adopted to become an established market.
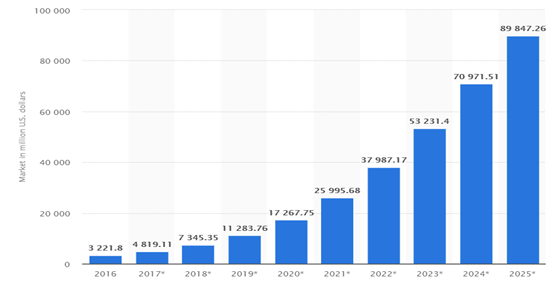
Figure 17: Artificial intelligence marketcap growth projections
Source: medium.com/dataseries
Decentralized computing can gain market share due to its potential in the NFT, metaverse and blockchain data spaces. AI combined with the power of the blockchain network has the potential to gain market share in the deep learning industry, with real world applications. However, this combination needs time to prove itself. dVPN’s selling point is how no single entity can collect all the data generated by the user, so privacy is protected to a large extent.
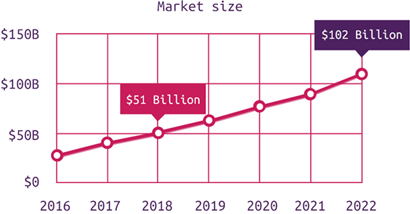
Figure 18: dVPN market size
Source: steemit.com
4. Explanations and comparisons of Web3 computing solutions
The decentralized cloud computing network sub sector is developing the product of distributed cloud computing. The applications from distributed computing are mainly cloud computing, data storage and computation combined solutions, master node of computing and decentralized marketplace for providing computing services.
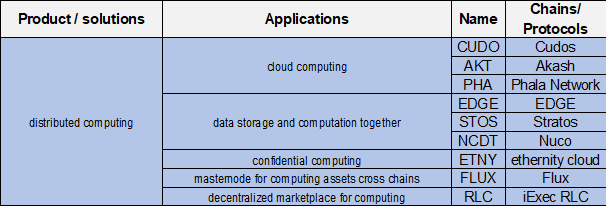
Table 2: Distributed computing
Source: Huobi Research Institute
For example, Cudos is a proof of stake tendermint blockchain. The network supports maximally 100 computing service providers, with maximally 1,000 CVN s. Quantitative scoring is provided for service provider, including staking score, reliability score, availability score and security score. Each service providers are scored to place its market reputation. Each data service provider rents out their processing unit including their processing units to perform data computing. It also launched mining applications for GPUs, CPUs and ASICs. The layer 2 Cudos network and layer 3 computing platform will possibly be developed in 2022.
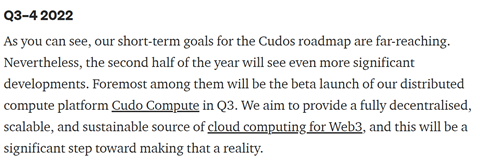
Figure 19: Cudo compute platform will be launched in 2022 Q3
Source: medium.com/cudos
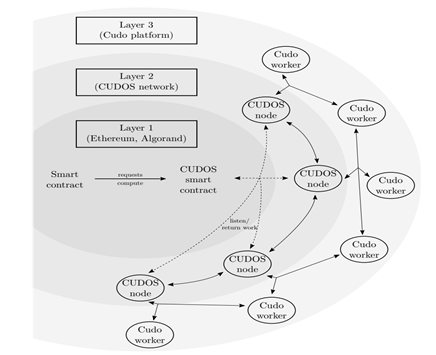
Figure 20: Cudo platform is labelled as the layer 3 element of the Cudos blockchain
Source: Cudos whitepaper
Meanwhile, the access to gravity bridge will be developed soon. Cudos has suggested using AMD SEV and Intel SGX chips for hardware. Apart from that, Akash is a tendermint proof of stake-based consensus blockchain. The Akash network also includes a marketplace, which is a P2P decentralized marketplace for cloud computing. Cloud providers and users come across a decentralized order book to deploy a cloud service once the pricing matches the user’s expectations. Cloud providers can then lease their extra processing power to web users. Akash partnered with Arweave and ArDrive for computing storage. And it also becomes a medium for helium cloud hosting.
Besides, projects on cloud computing also works on value chain integration of computing and data storage. Stratos, a storage and computing oriented protocol, is able to outsource storage capabilities to external blockchains like Arweave and IPFS. The meta service layer runs with proof of access for auditing, indexing, routing, matching and managing resources and demand with network statistics for computing services. Stratos application also includes accelerated Network for video distribution, NFT platform, oracle system, social media, edge computing and IoT. Nuco also combines the algo, data and storage together. user data is stored, transferred and computed then segmented and compressed, finally protected with firewall.
Flux is a layer 2 decentralized web3 infrastructure to provide masternode computing for interoperability across different blockchains. Now Flux works as a cross chain asset wrapping lending and borrowing infrastructure. Cross chain interoperability includes SOL, ETH, KDA, Auora, Near, Terra, XZC, MATIC and HECO.
Distributed artificial intelligence applies to support cloud computing with deep neural networks. The product solutions are distributed blockchain AI machine learning cloud computing network, blockchain network with AI platform and AI marketplace and distributed personal AI.
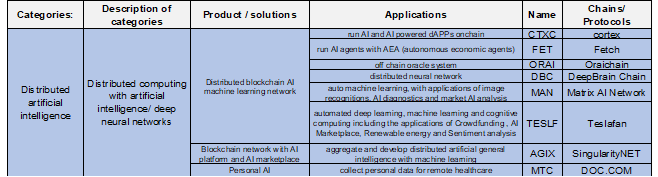
Table 3: Distributed artificial intelligence
Source: Huobi Research Institute
Cortex Chain combines artificial intelligence on-chain. It is a proof of work blockchain with proof of work consensus as a distributed blockchain AI machine learning network. It uses distributed file system based on DHT (Distributed Hash Table) or IPFS as a storage layer solution to reduce network load data. When the load is reduced by reducing storage to DHT and IPFS, the load can keep up with AI algorithms. The AI algorithm can machine-learn on chain and drive the adoption of AI powered dApps. CTXC consists of the following framework. First, verification of AI operators is completed through the Z3 prover. Second, the AI operator opens the AI library to correlate references. Third, the randomAI workload proof algorithm performs the network consensus. CTXC has the future applications of AI stablecoin AI DAO AI DeFi AI data privacy Distributed file system Cortexflow, an off-chain machine learning.
Fetch.ai is the blockchain network combined with artificial intelligence agents. It uses tendermint proof of stake consensus algorithm. It uses an Agent Communication Network to perform machine to machine communications. Machine learning logic can be implemented on-chain. The agent communication network is composed of AEA (autonomous economic agents). Groups of AEA form an MAS (multi-stakeholder multi-agent systems). There are 4 functions of MAS. MAS serves as a means to interact with other AEAs, agents and services in a structured way. It delivers messages via the Internet of blockchain. Also, it has access to financial settlement and search and discovery systems. These AEA allows M2M communication and allows a fast interface between artificial intelligence to work on the data from AEA through M2M means. Fetch.ai works with Catena-X autonomous vehicle stakeholder for scalable network.
To sum up shortly, artificial intelligence really gives us an opportunity to solve problems by being the autonomous solution of analysing data. However, the dawn of market emergence of both blockchain and artificial intelligence requires time costs. Specifically speaking, artificial intelligence has little applications as a viable product compared to the IT industry. Loads of limitations during and after the development of AI begin to reveal. Especially when deep learning model is placed in deep neural network, the AI starts to show the model’s limitations and developers seek to re-model from the beginning. Another metrics to evaluate the project potential is to look at the experience and the confidence based on founders. AGIX’s founder has more than 15 years of experience in AI. He began working as the chairman of Artificial General Intelligence Society in 2010 and the chairman of OpenCog Foundation since 2008. Yet, the limitation of artificial general intelligence is revealed alongside with the development of SingularityNet.
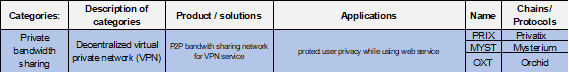
Table 4: Private bandwidth sharing
Source: Huobi Research Institute
DVPN is going to take away parts of the market share of the VPN system provided by centralized entities. Privatix, Mysterium and Orchid use similar protocol architecture to provide decentralized peer to peer bandwidth sharing networks. In these dVPN systems, blockchain bandwidth providers share parting of their computing power as bandwidth for the blockchain network. Meanwhile, blockchain users use the bandwidth provided on the network to serve the internet. Unlike traditional VPNs, centralized entities provide centralized servers and computing power to individual users. Multiple hacks were identified with regard to user information when these centralized bandwidth and servers are exposed to security risks. Orchild, a dVPN app, provides the interface to decentralized VPN through Orchid app with the settlement of currency OXT. It uses a proof of stake system to secure network privacy from validators.
Figure 21: OXT’s dVPN app
Source: https://www.orchid.com/vpn/
Privatixis built on Ethereum to provide p2p bandwidth sharing. Bandwidth providers can sell their bandwidth based on PRIX settlement currency. Developers using PRIX to run dApps are able to avoid censorship from centralized servers and bandwidth. The dApps providers are also provided with the privacy being censorship resistant by PRIX network.
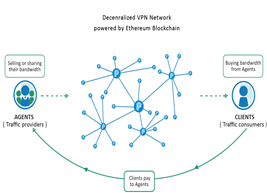
Figure 22: Decentralized VPN network
Source: https://privatix.io/

Figure 23: DVPN structure
Source: https://privatix.io/
5. Conclusion
The targeted computing market for solely blockchain cloud computing is the retail segment, based on metaverse, NFT, validator and decentralized data market. Meanwhile, the orientation of AI combined with blockchain network development focuses on enterprise values such as healthcare and supply chain management. Such emerging market leads to opportunities for private equities. The dVPN market focuses on citizens who demand censorship-resistant networks and provide a privacy platform for dApp users and developers.
The whole decentralized computing market is about to emerge. Although its development remains in a pre-MVP stage, the demand for it is stunning. Validators, minders, metaverse builders, play-to-earn users, decentralized web developers, NFT owners and NFT exchanges require full stack migration from Web2 to Web3. Decentralized computing will play a role like the tech giants and cloud computing enterprises in Web2, like Microsoft’s office cloud file transfer, AWS’ remote database and Nvidia’s AI neural network. Back in 2018, users could not withdraw funds when everything was crashing. Liquidity providers could not transfer funds out of the protocols itself while some are injured with rugpull by HTML backdoors. Such problems will be solved if web3 computing works out with blockchain networks.
In the future, Web3 users will be able to freely enjoy decentralized web on both frontend and backend processing. The Web3 market will share the Web2 computing economy. Either collaboration or competitions will be seen, if Web3 computing goes massive. Web2 computing giants will focus on the processing and computing market of the social Web2 and some huge enterprises. Meanwhile, the Web3 computing market will gain the capital investment and revenues from blockchain networks, retail users, start-ups and enterprises that choose their data to be verified and processed with privacy protections. More cloud computing enterprise will adopt blockchain and combine their computing solutions to become a more capable full stack computing hub.





