Once frozen, a Tether-blacklisted wallet almost never comes back. Only 3.6% of addresses placed on the blocklist in 2025 were later removed, according to BlockSec data.
More than half of the funds tied to those wallets were permanently destroyed using the contracts’ “destroyBlackFunds” function — a detail that underscores just how final these enforcement actions tend to be.
Freezes Surge Across Tron And Ethereum
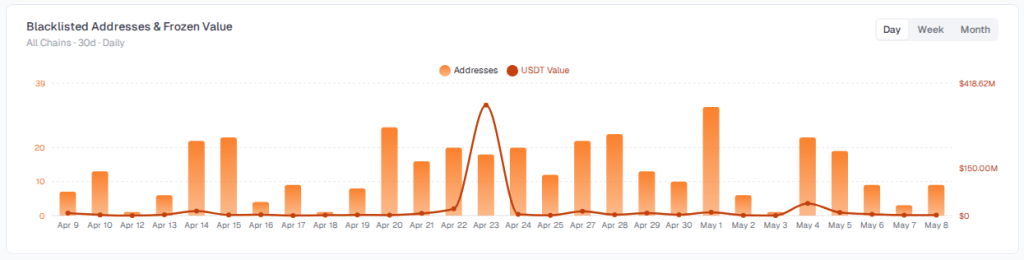
In the past 30 days alone, Tether froze over $514 million in USDT across 370 addresses on the Ethereum and Tron networks.
BlockSec’s USDT Freeze Tracker shows 328 of those addresses were on Tron, with about $506 million locked there. Ethereum accounted for 42 addresses and $8.73 million. The gap between the two networks points to Tron as the main front in Tether’s enforcement push.
Source: BlockSec
The pace is picking up. All of 2025 saw Tether blacklist 4,163 addresses and freeze a combined $1.26 billion. At the current rate, that annual total could be surpassed well before December.
A broader study covering 2023 through 2025 put the cumulative figure at roughly $3.3 billion across 7,268 addresses — far ahead of rival stablecoin issuer Circle over the same period.
Seeing Tether freeze over $500M in USDT across Tron and Ethereum really shows how much compliance still shapes crypto behind the scenes.
This makes me appreciate using platforms like BingX while staying more aware of custody, liquidity, and where funds actually move onchain.... pic.twitter.com/K0cNTrcmWX
— Crypto Axtrol (@CryptoAxtrol) May 8, 2026
Law Enforcement Plays A Growing Role
Some of the largest recent freezes were tied directly to government investigations. In April, Tether coordinated with the US Treasury’s Office of Foreign Assets Control to lock more than $344 million in USDT across two Tron addresses.
Officials said those wallets were linked to suspected sanctions evasion involving Iran. Months earlier, in February, Tether assisted authorities in seizing over $61 million connected to pig butchering scams — a form of fraud where victims are manipulated into sending large sums under false pretenses.
Tether had previously disclosed that it froze around $4.2 billion in tokens over three years due to links with illicit activity, with $3.5 billion of that amount locked since 2023 as law enforcement agencies stepped up crypto-related investigations.
Broader Questions Around Freeze Powers
The surge in blacklisting has sparked debate beyond stablecoins. Some decentralized finance projects have used upgradeable contracts and admin controls to halt or recover funds after major exploits, raising questions about who holds those powers and when they should be used.
For stablecoins like USDT, issuers retain direct control over minting and burning. Data shows these freeze mechanisms are now a routine part of fraud, sanctions, and scam investigations — used not occasionally, but consistently and at scale.
Featured image from Halo, chart from TradingView