Author: Deep Tide TechFlow
Last week, KelpDAO was hacked for nearly $300 million, making it the largest negative security incident in DeFi so far this year.
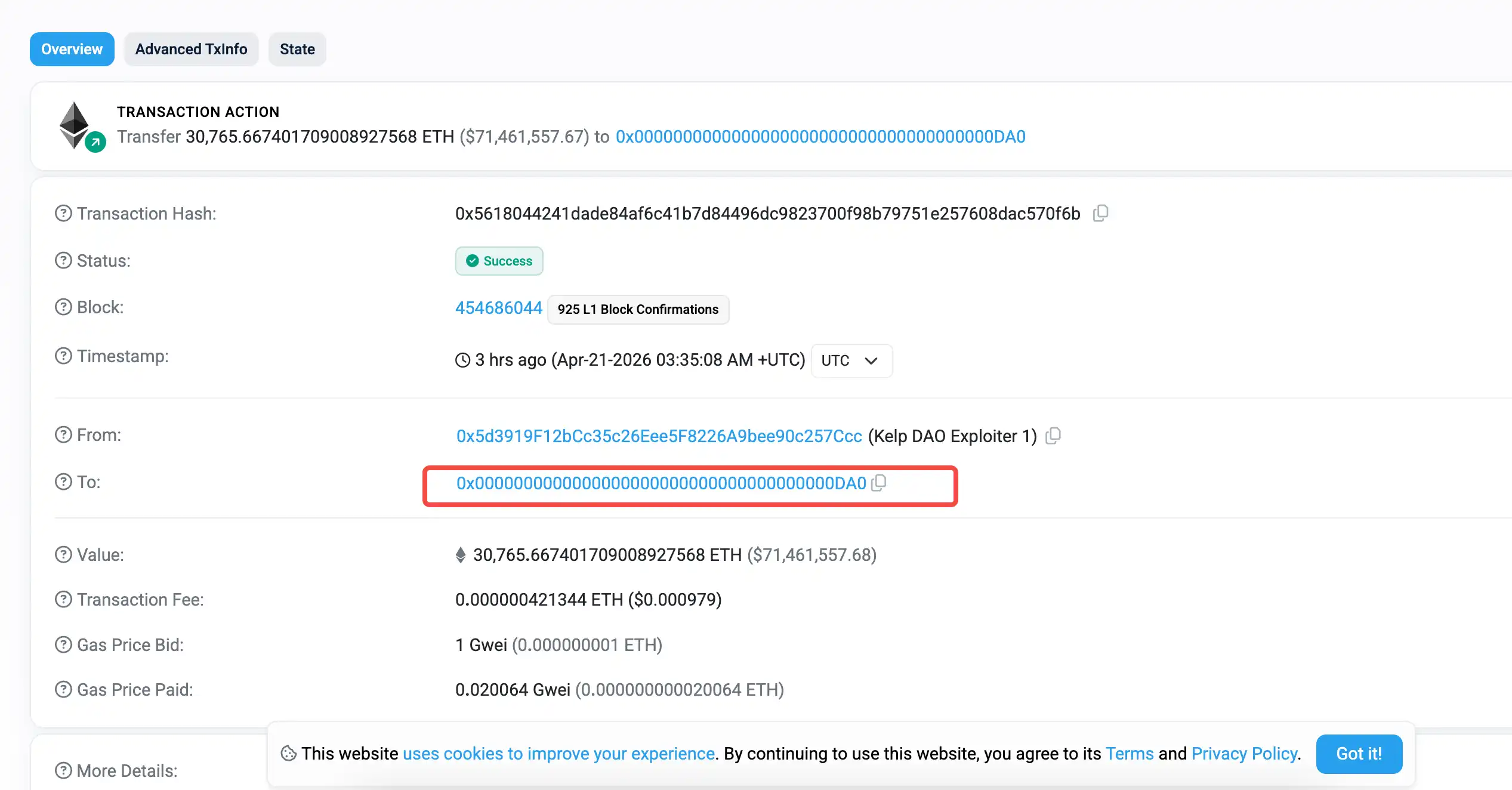
The stolen ETH is now scattered across multiple chains, with approximately 30,765 ETH remaining in an address on the Arbitrum chain, worth over $70 million.
Just when everyone thought the story was over, a sequel emerged today.
According to on-chain security firm PeckShield, the funds in the hacker's address on the Arbitrum chain were transferred out a few hours ago. Strangely, the funds were moved to a bizarre address that appears to be almost all zeros: 0x00000...
Everyone was speculating: Did the hacker burn the funds by sending them to a black hole address? Or did they have a change of heart or get recruited?
Neither.
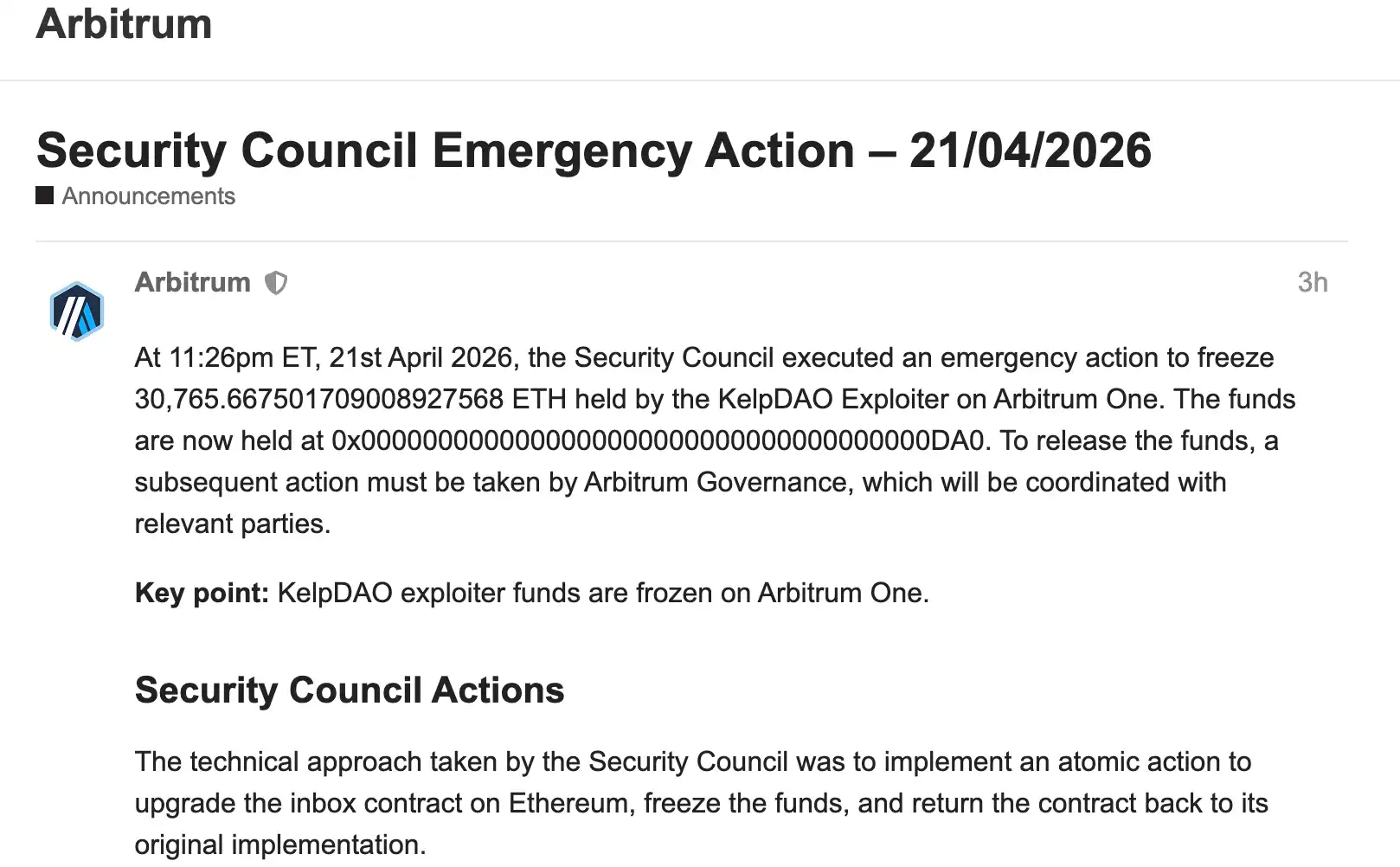
A few hours ago, the Arbitrum official forum posted an emergency action announcement explaining the situation. The hacker's funds were transferred by the Arbitrum Security Council.
However, the remarkable part is that without knowing the private key of the hacker's address, the Arbitrum Council neither froze the funds nor had the authority to transfer them. Instead, they directly issued a transfer instruction "in the name of the hacker."
The hacker was unaware, the private key was not leaked, and the on-chain records made it look like the hacker had performed the operation themselves.
The principle behind this operation is that all cross-chain messages between Arbitrum and Ethereum must pass through a bridge contract called Inbox. The Security Council used its emergency authority to temporarily upgrade this contract, adding a new function:
It allows sending cross-chain transactions in the name of any wallet address, without needing that wallet's private key.
They then used this function to forge a message, with the sender field filled as the hacker's wallet, and the content being "Transfer all my ETH to the frozen address." The Arbitrum chain received it and executed it as usual, resulting in the bizarre scene captured in the on-chain transfer screenshot above.
After transferring the hacker's funds, the contract was immediately downgraded back to its original version. The upgrade, forgery, transfer, and restoration were all completed within a single Ethereum transaction. Other users and applications were completely unaffected.
This operation is unprecedented in Arbitrum's history.
According to the forum announcement, the Security Council first confirmed the hacker's identity with law enforcement, pointing to North Korea's Lazarus Group, the most active state-level hacker organization in the DeFi space this year. The council conducted a technical assessment to ensure it would not affect other users before taking action.
Since the hacker was in the wrong first, this move carries a bit of a "don't blame us for not playing by the rules" sentiment. As for the subsequent handling of the frozen ETH, it will go through Arbitrum's DAO governance vote and be coordinated with law enforcement.
Recovering over $70 million in stolen funds is undoubtedly a good thing. But it's worth noting the prerequisite for achieving this: 9 out of the 12 members of the Security Council can sign to bypass all governance votes and upgrade any core on-chain contract with zero delay.
Praising the Outcome, Worrying about the Capability?
Currently, the community's reaction is divided.
Some think Arbitrum did a great job, protecting assets at a critical moment, which actually adds a bit of confidence in L2. Others ask a very direct question: If 9 people can sign to move any asset in anyone's name, can this still be called decentralization?
In my opinion, the two sides are actually talking about different things.
The former is talking about the result, the latter is talking about the capability. The result of this incident is certainly good—over $70 million in stolen funds was recovered. But the capability demonstrated by Arbitrum this time—to modify contract functions via multi-sig—is neutral in itself; what it is used for in the future, whether it can be used, and how it is used, all actually depend on the council's governance.
However, for most people using Arbitrum, this discussion might be less relevant than another fact. Arbitrum is not special; currently, almost all mainstream L2s retain similar emergency upgrade permissions.
The chain you are using most likely also has a similar Security Council with similar capabilities. This is not a unique choice by Arbitrum; it's almost a universal design for L2s at this stage.
Looking at it from another angle, this offensive and defensive battle actually reveals a bigger picture.
The attacker is North Korea's Lazarus Group, attributed to at least 18 DeFi attacks since the beginning of this year. Just three weeks ago, they stole $285 million from Drift Protocol using a completely different method.
On one side, state-level hackers are constantly upgrading their attack methods; on the other, L2s are starting to use underlying permissions to fight back. The security war in DeFi is entering a new stage, moving beyond "post-incident freezes, on-chain shouting, and praying for white hats to intervene."
In extraordinary times, they created a master key to open the hacker's address, and melted the key after use. Just judging by this incident alone, having the capability to respond to hacker attacks is not a bad thing.
And if we must elevate this to a philosophical discussion about "this is not decentralized at all," then there are many more things to talk about. The crypto industry has no shortage of centralized operations. This time, at least, it was handling a negative incident and solving a problem, not creating one.
Looking back more pragmatically, KelpDAO was robbed of $292 million, and only over $70 million was recovered—less than a quarter of the total. The remaining ETH is still scattered on other chains. Over $100 million in bad debt on Aave remains unresolved, and it's still unknown how much rsETH holders will get back.
Even though Arbitrum invoked god-like permissions, this battle is clearly far from over.