In the history of commerce, wherever wealth surges and accumulates, there is a tug-of-war between law and order.
Looking back from the end of 2025, the issuance scale of global stablecoins has firmly surpassed the $300 billion mark, nearly tripling from last year, with monthly trading volume reaching an astonishing 4 to 5 trillion dollars. Stablecoins, as a type of crypto asset, have shed the label of "geek toys" and have become the primary gateway for traditional finance to enter the digital world.
However, beneath the prosperity lies a shadow. According to the latest industry report, the scale of funds received by illegal addresses globally in 2025 is projected to exceed $51.3 billion. When hundreds of billions of dollars can cross borders in seconds, traditional regulatory methods often can't keep up with this flow speed, making it difficult to distinguish between legitimate business and criminal proceeds in real-time.
In this world where rules are not yet fully formed, Professor Zhou Yajin is a special entrepreneur.
Zhou Yajin's career path is a typical example of an elite scholar deeply colliding with industry. In 2010, he went to the United States to pursue his Ph.D., delving into the field of mobile security for five years. Later, he and his advisor, Professor Jiang Xuxian, joined Qihoo 360, completing the first step from the laboratory to the industry front line. In 2018, he chose to return to Zhejiang University to take up a teaching post. Three years later, he plunged back into the industry wave, founding the blockchain security company BlockSec.
Over the past four years, Zhou Yajin has led BlockSec through a shift in business focus. Starting from initial smart contract code auditing, they gradually extended into deeper areas such as security monitoring, fund tracing, and anti-money laundering (AML) compliance.
Zhou Yajin and his team have long been deeply involved in specialized research on on-chain data. They even used technical means to "lurk" in black market groups like Southeast Asian telecom fraud, mastering a vast amount of little-known underlying survival landscapes. Through his perspective, we might see the most real interest games in this new digital world.
The following is Zhou Yajin's account, edited and compiled by the Beating Editorial Department after an exclusive interview.
Kite is the first Layer 1 blockchain for AI agent payments. This underlying infrastructure enables autonomous AI agents to operate in an environment with verifiable identity, programmable governance, and native stablecoin settlement.
Kite was founded by senior experts in AI and data infrastructure from Databricks, Uber, and UC Berkeley. It has completed a $35 million financing round, with investors including PayPal, General Catalyst, Coinbase Ventures, 8VC, and several top investment foundations.
From Code Auditing to the Anti-Money Laundering Battlefield
I pursued my Ph.D. in the United States from 2010 to 2015, under the guidance of Professor Jiang Xuxian. At that time, we worked on mobile security, particularly Android malware detection, which was relatively early globally. After graduating in 2015, I followed my advisor to Qihoo 360 to industrialize our research results.
In 2018, I joined Zhejiang University, moving from the industry back to academia. At that time, China was experiencing the small ICO boom around 2017-2018, which brought blockchain into the view of a small group of people. I also started looking into blockchain security. I observed frequent on-chain security incidents at the time. The academic world already had many good solutions, but looking back at the industry, not much was being done well; in fact, very few were paying attention to these issues.
So in 2021, Professor Wu Lei and I co-founded BlockSec.
Initially, everyone's perception of a "blockchain security company" was extremely stereotypical: aren't you just doing audits? Indeed, we started with smart contract auditing. Because we had academic research积累 (accumulation) and an elite team, we quickly gained a foothold in the auditing business. But my perspective in founding the company was that I didn't want it to be just a security service company. Because auditing only addresses pre-launch security, and for post-launch protection, there weren't particularly good solutions in the industry at that time.
So in 2022, while doing audits, we also started developing an on-chain attack monitoring platform. Our product concept at the time was to continuously monitor on-chain transactions. If an attack transaction occurred, it could be automatically blocked. During this process, we found that even with auditing and monitoring, projects could still be attacked. Additionally, there were many consumer-side security incidents like phishing and private key loss, where users lost money, which衍生出 (derived) new demands.
When a project gets hacked or a user gets phished, they need to report it to law enforcement and explain clearly where the money went. So starting in 2022, we developed a fund flow tracking product. This product was completely SaaS-based; users could subscribe and use it directly—we didn't adopt a To B sales model.
The user profile for this product surprised us greatly. Besides law enforcement agencies, media journalists were using it, financial institutions were using it, and even many private detectives taking on side jobs were using it. These users from different backgrounds helped us refine the product during use, attracting more users. Combined with our existing attack detection engines, phishing detection engines, etc., these labels and data gradually沉淀 (precipitated) into our deepest moat.
The turning point occurred around late 2024 to early 2025.
At that time, the issuance volume of stablecoins began to surge wildly. This market was no longer only participated in by Crypto Native people. Many from traditional finance started entering, and the first virtual currency they encountered was stablecoins. These people have a strong sense of compliance. As soon as they entered, they would ask: I want to use stablecoins, so how do I solve the AML (Anti-Money Laundering) and CFT (Countering the Financing of Terrorism) issues?
The market lacked good compliance products, and we恰好 (happened to) have underlying label data accumulated over three years, so we quickly launched an anti-money laundering product. The whole process was quite natural. We evolved from a pure security service provider to a comprehensive "security + compliance" supplier based on market demand changes.
Lurking
To do anti-money laundering, you first need to deeply understand how the black and gray markets actually use money.
From our research perspective, cryptocurrency crimes are typically divided into two categories: one is "crypto-native," such as attacks targeting code vulnerabilities in DeFi protocols, private key theft, or phishing. Without blockchain, these crimes wouldn't exist at all.
The other category is "crypto-driven," such as telecom fraud, ransomware, and human trafficking. The emergence of cryptocurrency极大地提高了 (greatly enhanced) the efficiency and anonymity of their cross-border transfers. In these scenarios, what shocked us the most was the human trafficking within the Southeast Asian telecom fraud industry chain.
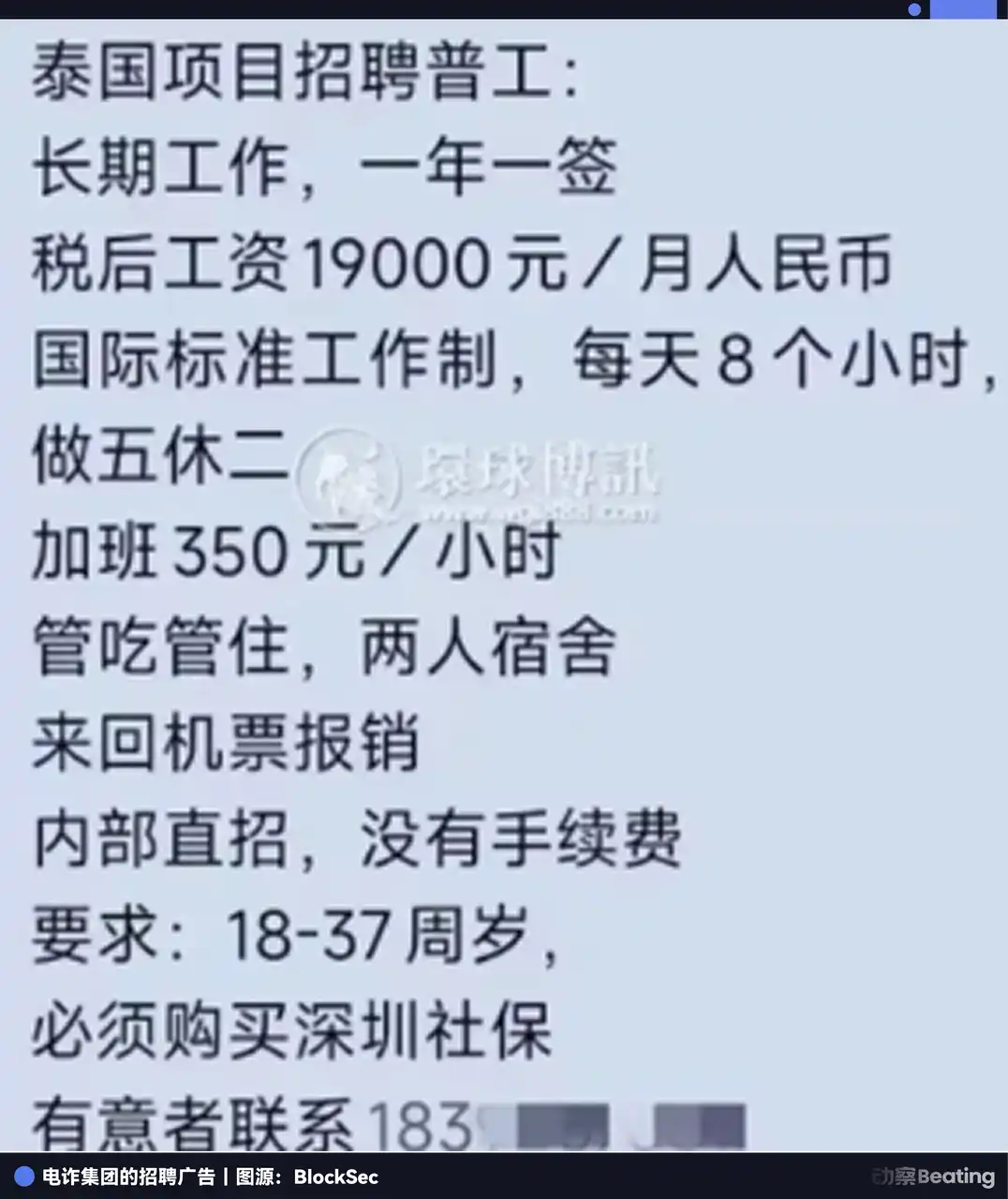
Many people feel that telecom fraud is far from them, but look at their recruitment ads—the诱惑力 (enticement) is extremely precise: starting monthly salary of 19,000 RMB, covering air tickets, food, and accommodation, and even earnestly promising "must purchase Shenzhen social security." This诈骗手段 (fraud method) specifically targeting young people aged 18 to 37 has deceived a large number of victims into crossing the border and entering those fraud parks distributed in Myanmar, Cambodia, or Laos.
Today's fraud parks have an organizational structure as strict as正规公司 (legitimate companies), complete with finance, technology, and call operation groups. To maintain this massive operation, they need to constantly replenish "labor." The parks (demand side) and human traffickers (supply side) don't know each other and have no trust in online communication.
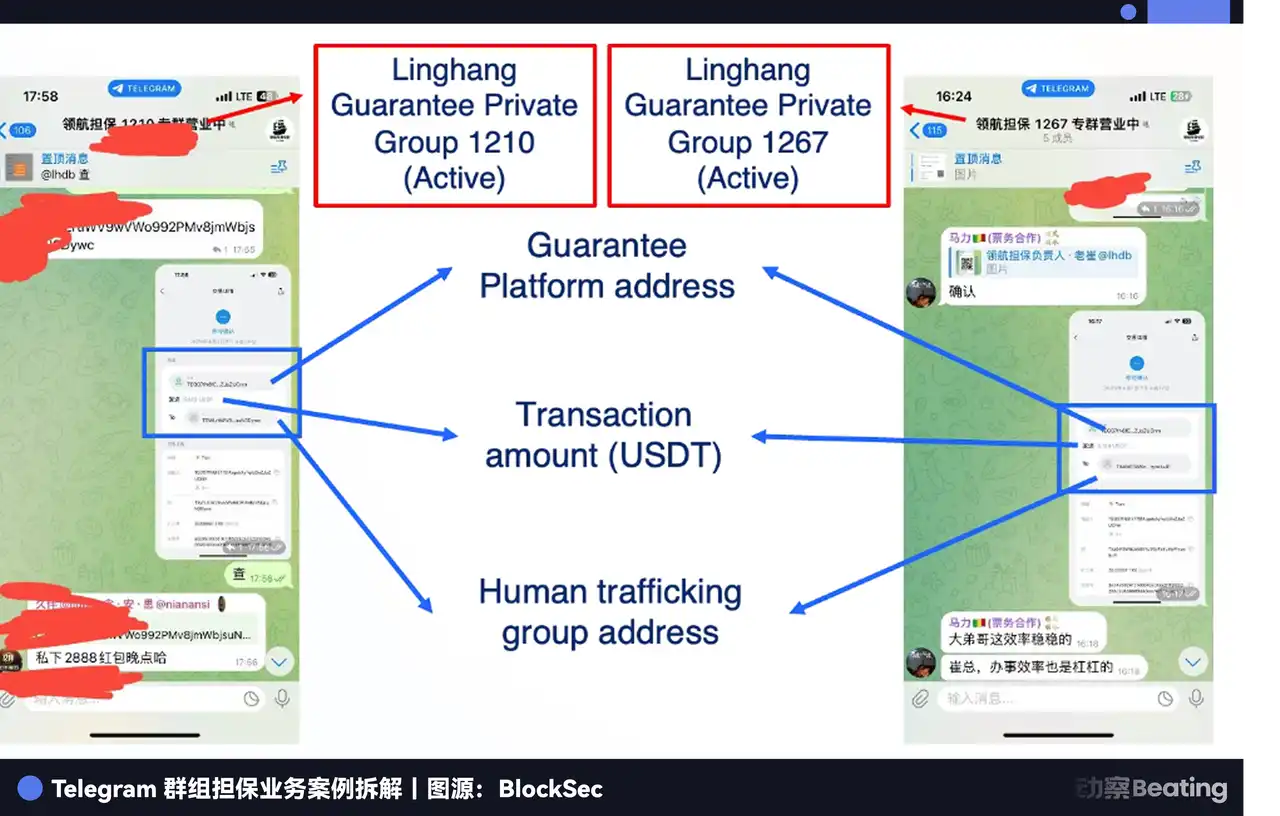
Thus, an intermediary环节 (link) specifically designed to provide credit endorsement for illegal transactions was born: the "labor guarantee platforms."
The operating logic of this system is very similar to Taobao. The park first deposits a amount of USDT as collateral on the guarantee platform; the human trafficker is responsible for luring the victims across the border to a designated "inspection" location. After both parties confirm无误 (without error) in a private Telegram group, the platform releases the collateral to the trafficker. This transaction believes in "money arrives when the person arrives." If either party tries to renege, the platform will freeze or confiscate the collateral according to the rules to compensate the other party.
To attract business, these platforms open many public channels on Telegram to "show muscle." For example, in the channels of Linghang Guarantee or Haowang Guarantee, system bots release real-time transaction screenshots and on-chain transfer records. They even run promotions like正规电商 (legitimate e-commerce), such as代收佣金 (collecting commissions on behalf), or "buy 10 ads get 2 free."
This is also the most direct entry point for us to observe the black market.
From February to August 2025, we developed an automated system to continuously lurk in these groups and gather intelligence. Because the chats in the groups are filled with jargon, we specifically trained a large language model for analysis.
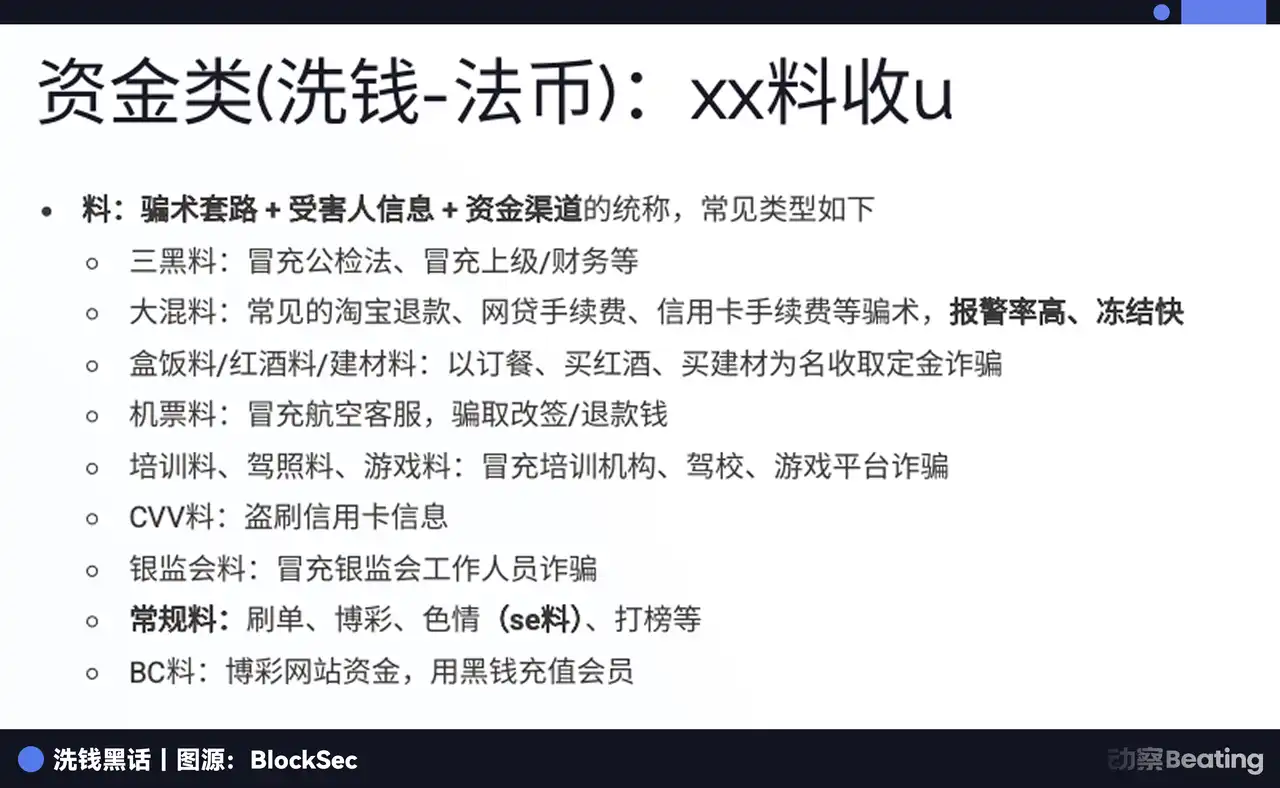
In the black market's jargon, victims are "fish," fraud tactics and victim information are called "material" (料 liao). The material is finely categorized: there's "three black material," "mixed material," "air ticket material," etc. Based on the money laundering环节 (stage), it is also divided into "first-hand material" received directly from the victim, and "second-hand material" that has undergone layering processing.
There is also a job called "手机口" (shouji kou, mobile port). Accomplices within China use audio cables or specific APPs to relay overseas fraud calls to domestic mobile phones for dialing, bypassing carrier anti-fraud interception, earning about 200 USDT per hour. They recruit many small-town youths to do this.
In these black market groups,甚至公然流传着 (even openly circulated) "Anti-Police Tutorials," meticulously teaching everyone how to calmly deal with investigations, such as insisting that the phone was lost, deleting scripts and encrypted communication software in advance. The end of the tutorial writes a very ironic sentence—"Salute to everyone who works hard."
Through half a year of automated monitoring, for one of these guarantee platforms, we identified a total of 634 addresses associated with human trafficking gangs, with累计追踪到的 (cumulatively tracked) illegal transaction amount接近 (approaching) $12 million. At the most active time, 10 people were sold into parks daily through this one guarantee platform. The actual situation might be more severe because other guarantee platforms exist.
When tracking the flow of funds, we found that绝大部分 (the vast majority) of this money is on the Tron chain, primarily using the stablecoin USDT. Because Tron has a low operational threshold and cheap transaction fees, it is very suitable for these criminal gangs with limited technical水平 (level). Although Tron fees have also increased now, they have developed usage habits and find it difficult to switch to other methods.
Analyzing the fund flows of over 120 gangs, we found that more than 34.9% of these illegal proceeds ultimately flowed to OKX's hot wallets, 6.9% to Binance, and 14.4% to hot wallets related to汇旺 (Huiwang).
When you can see clearly how this money comes from and how it flows, anti-money laundering is not an empty phrase. This real data captured from the underlying groups is the core barrier in current security and compliance.
12 Seconds: "Intercepting" Hackers in the Mempool
In the security industry, there has always been a complex: auditing only ensures the code is secure at the moment of launch. But once the project is live, it faces 24/7 scrutiny from global hackers. If auditing is "static defense," can we find a way to do "dynamic interception"?
In 2022, while doing audits, we launched an on-chain attack monitoring platform. The underlying logic of this product is to watch Ethereum's Mempool. You can think of the mempool as a waiting room. All transactions must queue here before being officially packed into a block and recorded in the ledger.
In this waiting room, we not only watch ordinary user transactions but also those scripts with attack signatures. Once a suspected attack transaction is detected, our system immediately starts automatic analysis in a private chain environment: What does it want to do? Is the logic valid? How much money will it steal?
The most thrilling博弈 (game) usually happens within a brief 12 seconds.
After the Ethereum Merge, the block time was fixed at 12 seconds. This means that from the moment a hacker sends an attack instruction to the moment the transaction is actually confirmed and packed, there is an extremely short window. These few seconds are the golden rescue time留给 (left for) white hats.
After confirming the attack, our system automatically generates a "Front-running" transaction. The content of this transaction is almost identical to the hacker's, but the key difference is that we change the recipient address from the hacker's wallet to a pre-set security address.
To outrun the hacker, we must obtain packing priority from the miners.
Hackers, pursuing profit maximization, usually set a standard Gas Fee. We, through algorithms, set the Gas Fee very high, even directly giving a portion of this money to the miners. Driven by profit, miners will prioritize packing our transaction. When our transaction executes successfully, the hacker's transaction automatically becomes invalid.
This capability has saved many projects in实战 (actual combat).
The most typical instance was when we successfully intercepted an attack against a certain protocol in the mempool, rescuing 2909 Ethereum for the project方 (party) at once. The hacker had already triggered the vulnerability, and tens of millions of dollars were about to be stolen. Our monitoring system instantly alerted and completed attack simulation, transaction generation, and Gas bidding within seconds. Ultimately, that huge sum was transferred to our security address one step ahead of the hacker.
In the past, if a project was hacked, they could only ask for help on Twitter or negotiate with the hacker for a bounty to return the money. But now, through technical means, we intercept the money强行 (forcibly) just before the hacker succeeds.
Only if you understand the code better than the hacker and run faster than the hacker can you hold the last line of defense in this "Code is law" dark forest.
Epilogue
If the crypto world of the past decade was a "gold rush," then standing at the node of 2025, what we see is a return to "certainty." As the stablecoin scale surges towards $300 billion magnificently, as a new digital financial system moves from "wilderness" to "city-state," technology is no longer just a lever for wealth; it must first become a shield against the dark side of human nature.
The transformation experienced by Zhou Yajin and his team essentially reflects this business logic. From code auditing to dynamic interception, to deep diving and dismantling black industry chains, this is not the孤勇 (lonely courage) of an individual, but a defense mechanism inevitably generated as technology evolves to a certain scale. In this world where code is law, if the stubborn problems of illegal fund flows and security defenses are not solved, then the so-called "financial revolution" will forever remain a game for a minority.
In commercial history, any industry that can go mainstream has experienced the pain of moving from chaos to rule of law. This might be a long and tedious process, but as Zhou Yajin said, the final form of security is "unperceivable."
Only when security becomes like air—ubiquitous yet ignored by everyone—can this once volatile digital wasteland be considered truly civilized.