Author: SlowMist
On April 7, 2026, the U.S. Federal Bureau of Investigation (FBI) released the "2025 Internet Crime Report." This report, coinciding with the 25th anniversary of the FBI's Internet Crime Complaint Center (IC3), is based on over 1 million complaints collected in 2025. It provides an in-depth analysis of the historic loss scale exceeding $20.877 billion, victim profiles, core crime types like investment fraud, and focuses on the evolving trends of artificial intelligence (AI) in online scams, as well as breakthroughs in asset recovery by law enforcement.
This article will interpret the core content of the report, helping readers quickly grasp the dynamic changes in global cybersecurity threats in 2025 and enhance their awareness and prevention capabilities against complex online fraud and AI-driven threats.
Key Point One: 2025 IC3 Complaint Data
1. Overall Situation
In 2025, IC3 received a total of 1,008,597 complaints, involving total losses as high as $20.877 billion, a 26% increase compared to 2024, with an average loss of approximately $20,699 per incident. Among these, 85% of the losses were caused by online fraud.
2. Cryptocurrency-Related Situation
Cryptocurrency-related complaints totaled 181,565, causing cumulative losses of $11.366 billion, a 22% increase from 2024. Among these, 18,589 investors suffered losses exceeding $100,000. Among all complainants, the 60+ age group had the highest proportion.
Key Point Two: Victim Group Analysis
1. Overall Age Distribution
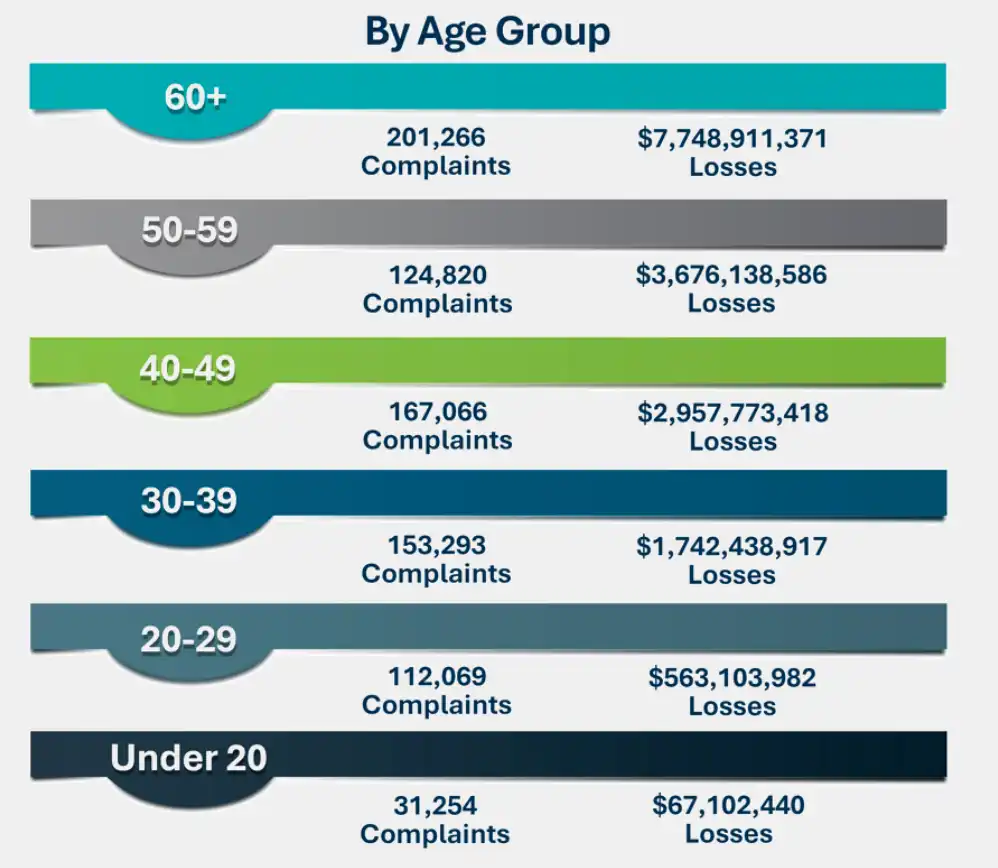
-
60 and over: 201,266 complaints, losses approx. $7.75 billion.
-
50-59: 124,820 complaints, losses approx. $3.68 billion.
-
40-49: 167,066 complaints, losses approx. $2.96 billion.
-
30-39: 153,293 complaints, losses approx. $1.74 billion.
-
20-29: 112,069 complaints, losses approx. $560 million.
-
Under 20: 31,254 complaints, losses approx. $67.1 million.
2. Cryptocurrency Victim Group
In cryptocurrency investment fraud, the 60+ age group had the highest number of complaints (13,685), with loss amounts as high as $2.76 billion, far exceeding other age groups. This group also suffered the most in cryptocurrency ATM/Kiosk scams, with related complaints reaching 6,188 and losses of approximately $257 million. Due to a relative lack of understanding of emerging financial technologies and payment methods (such as cryptocurrency ATMs, QR code transfers, etc.) and relatively weak anti-fraud awareness, individuals aged 60 and over have become key targets for scammers.
Notably, many victims, after being scammed initially, fell victim to secondary scams by trusting so-called "fund recovery services" – in "Recovery Scams," this age group again ranked first with 2,529 complaints and losses exceeding $540 million.
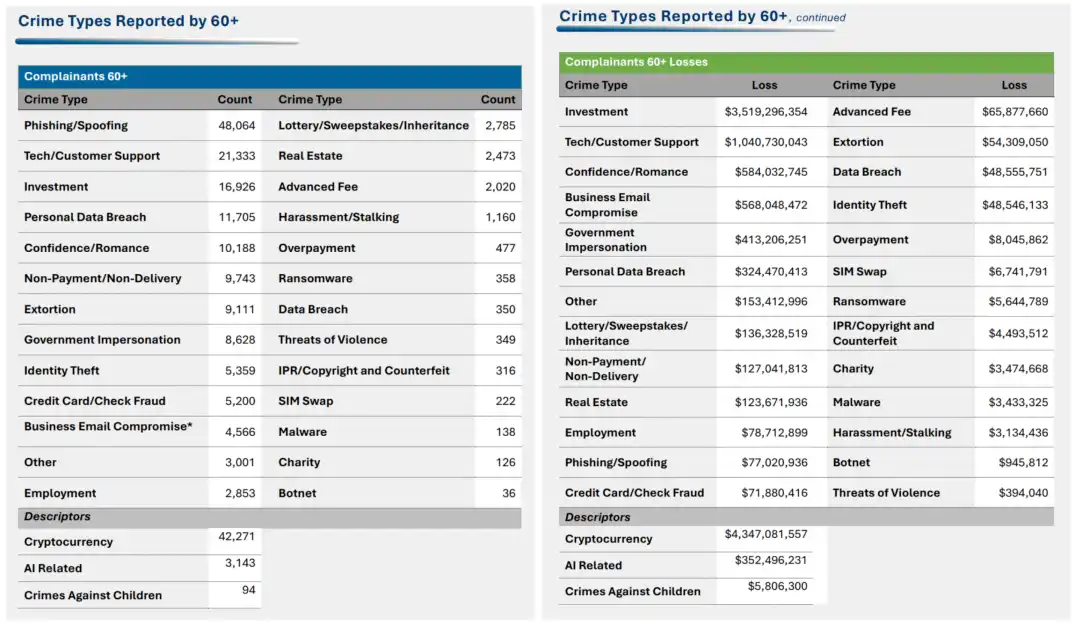
3. Main Types of Scams Targeting the 60+ Age Group
-
Scam types with Highest Complaint Numbers: Phishing / Vishing / Smishing / Pharming, Tech Support / Customer Service Fraud, Investment Fraud, Personal Data Breach, Confidence Fraud / Romance.
-
Scam types with Highest Losses: Investment Fraud, Tech Support / Customer Service Fraud, Confidence Fraud / Romance, Business Email Compromise (BEC), Government Impersonation.
Key Point Three: Crime Type Analysis
1. By Number of Complaints
-
Phishing/Vishing/Smishing/Pharming: 191,561.
-
Extortion: 89,129.
-
Investment Fraud: 72,984.
-
Personal Data Breach: 67,456.
-
Non-Payment / Non-Delivery: 56,478.
2. By Loss Amount
-
Investment Fraud: approx. $8.649 billion.
-
Business Email Compromise (BEC): approx. $3.047 billion.
-
Tech Support / Customer Service Fraud: approx. $2.135 billion.
-
Personal Data Breach: approx. $1.315 billion.
-
Confidence Fraud / Romance: approx. $929 million.
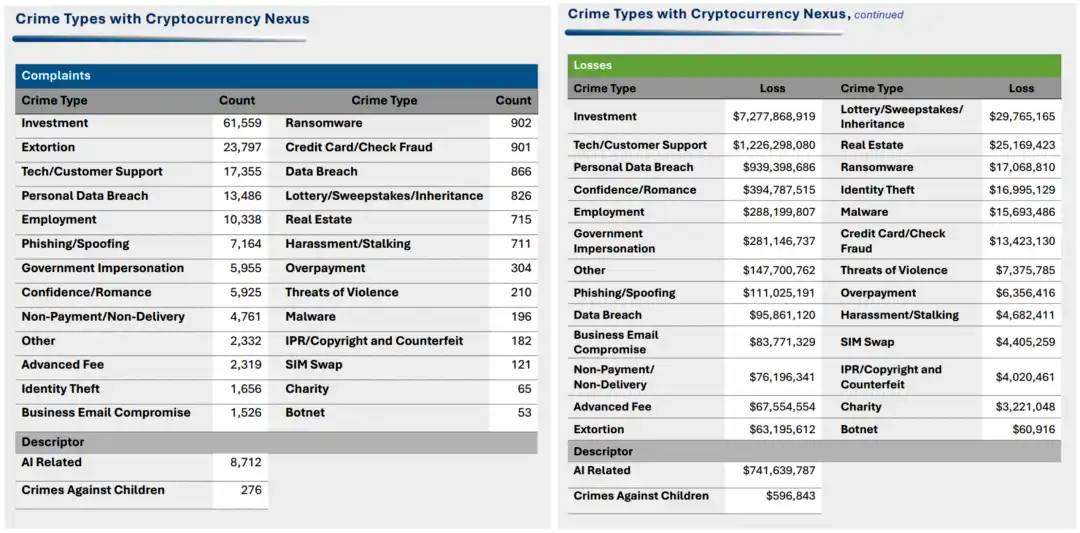
3. Cryptocurrency-Related Crime
-
Most Complaints: Investment Fraud (61,559), Extortion (23,797).
-
Highest Losses: Investment Fraud (approx. $7.28 billion), Tech Support / Customer Service Fraud (approx. $1.23 billion).
Key Point Four: Online Fraud and Law Enforcement Achievements
1. Overall Situation of Online Fraud
In 2025, IC3 received 452,868 online fraud complaints, causing $17.697 billion in losses, accounting for 85% of the year's total losses.
The transaction types with the highest number of complaints included cryptocurrency, wire transfer / ACH transfer, debit card / credit card, peer-to-peer (P2P) transfer, gift card / prepaid card, check / cashier's check, and cash.
2. Typical Scam Techniques
-
Account Takeover: approx. 4,700 cases, losses $359.7 million.
-
Gold Courier Scam: approx. 725 complaints, losses $311.8 million.
-
Investment Club Scam: approx. 1,600 complaints, losses $160 million.
-
Government Impersonation: approx. 32,000 complaints, losses $798 million.
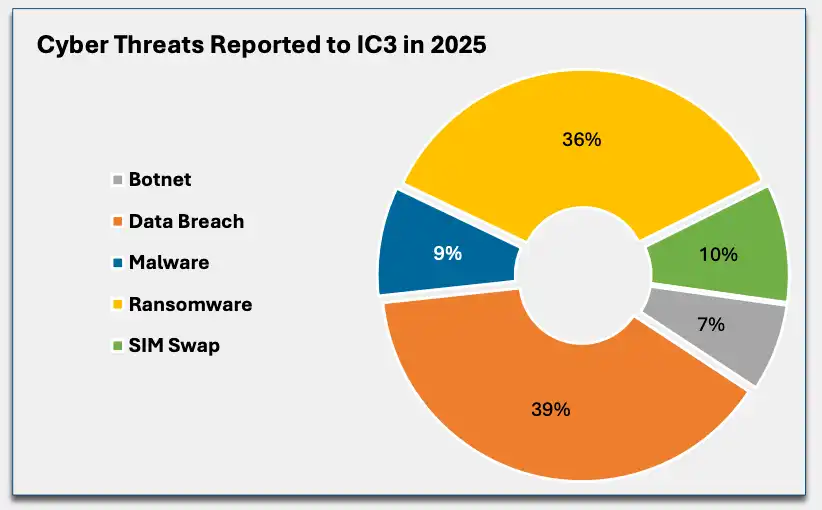
3. Cyber Threats
Cyber threat types reported to IC3 in 2025 included:
-
Data Breach: 39%, the most numerous type.
-
Ransomware: 36%, second highest.
-
SIM Swapping: 10%.
-
Malware: 9%.
-
Botnet: 7%.
Among these, 3,600 ransomware complaints caused over $32 million in losses. Main ransomware variants included Akira, Qilin, INC./Lynx/Sinobi, BianLian, Play, Ransomhub, Lockbit, Dragonforce, SAFEPA, Medusa.
In response to the frequent ransomware attacks, the FBI recommends that businesses and organizations take the following key protective measures:
-
Create off-site or offline backups, and regularly maintain backup and recovery mechanisms;
-
Remove default passwords and credentials when installing software;
-
Disable and remove unnecessary protocols by default;
-
Enable multi-factor authentication (MFA) for all services whenever possible;
-
Protect initial intrusion points;
-
Implement network segmentation to prevent ransomware spread;
-
Timely update all operating systems, software, and firmware.
4. Asset Recovery Achievements
-
In 2025, the FBI Recovery Asset Team (RAT) through the Financial Fraud Kill Chain (FFKC) intercepted 3,900 cases, froze funds totaling $679 million, with a fund interception success rate of 58%.
-
"Operation Level Up" issued warnings to over 8,000 potential victims, preventing over $500 million in potential losses for these victims.
-
Collaborated with Indian law enforcement to combat call center scams, resulting in over 475 arrests through 27 joint operations.
-
In financial fraud programs, successfully froze and recovered multiple large sums of money.
Key Point Five: Application of Artificial Intelligence (AI) in Cybercrime
1. Overall Situation
In 2025, IC3 received over 22,000 complaints involving AI-related information. The total losses from these complaints exceeded $893 million.
2. By Number of Complaints
-
Investment Fraud: 4,356.
-
Extortion: 1,764.
-
Personal Data Breach: 1,204.
-
Phishing/Impersonation Scam: 803.
-
Harassment/Stalking: 763.
3. By Loss Amount
-
Investment Fraud: approx. $632.04 million.
- <极速 dir="ltr" role="presentation">Business Email Compromise (BEC): approx. $30.26 million.
-
Tech Support / Customer Service Fraud: approx. $19.46 million.
-
Confidence Fraud / Romance: approx. $19.04 million.
-
Personal Data Breach: approx. $18.77 million.
4. Specific Applications of AI in Typical Scam Scenarios
According to the report, AI has been widely used in the following typical scam scenarios:
-
Business Email Compromise (BEC): Using AI to generate emails模仿ing executive tone or issuing transfer instructions through voice cloning, with related losses exceeding $30 million in 2025;
-
Confidence Fraud / Romance: Using AI to generate fake identities and dialogue scripts, even using voice cloning to simulate family member求助 scenarios, with related losses exceeding $19 million;
-
Job Scams: Using voice forgery or deepfake technology in remote interviews to gain internal corporate access, with losses接近 $13 million;
-
Investment Fraud: Using AI to mass-generate personalized communication content and forge videos and语音 endorsements by celebrities or authorities, with related losses exceeding $632 million.
Overall, AI is lowering the barrier to entry for scams and significantly enhancing their scalability and disguise capabilities.
Summary
The FBI's "2025 Internet Crime Report" further reveals the deep-seated evolution of the current cybercrime ecosystem: on one hand, the scale of fraud continues to rise, with cryptocurrency remaining an important载体 for fund transfer and money laundering; on the other hand, criminal methods are accelerating their shift from traditional "opportunistic fraud" to "precise, industrialized operations," especially the high-intensity penetration into the elderly population and the spread of secondary scams like "recovery scams," reflecting attackers' deep exploitation of victim psychology and behavioral patterns. Meanwhile, the introduction of artificial intelligence technology is significantly lowering the barrier to fraud and amplifying attack efficiency, gradually evolving online fraud into a complex threat system with automation and scalability features.
Although law enforcement agencies have achieved phased results in fund interception and international cooperation, the overall loss scale and growth trend indicate that the risk situation remains severe. For ordinary users, establishing basic risk identification capabilities and anti-fraud awareness has become a "required course" in the digital age; for industry participants and regulatory agencies, how to enhance the comprehensive identification capabilities for fund flows, behavioral patterns, and异常 signals at the technical level, and strengthen cross-regional collaborative governance, will be key to应对 future new types of cybercrime.