At around midnight Beijing time yesterday, on-chain analyst Specter X discovered a case where nearly 50 million USDT was transferred to a hacker's address due to failure to carefully verify the transfer address.
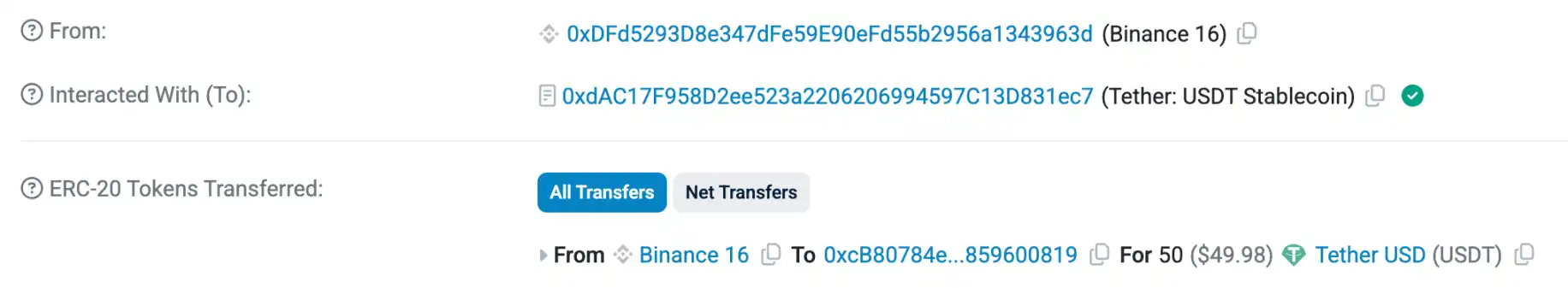
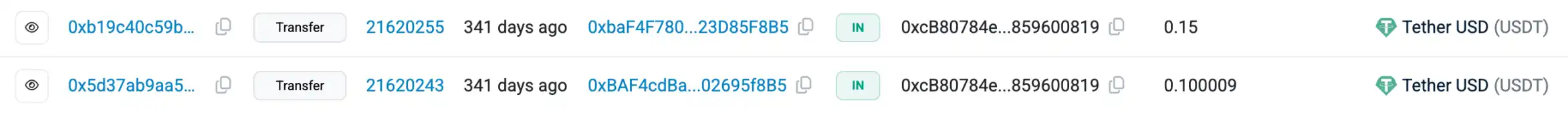
According to the author's investigation, this address (0xcB80784ef74C98A89b6Ab8D96ebE890859600819) withdrew 50 USDT from Binance at approximately 13:00 Beijing time on the 19th for a test transaction before a large withdrawal.
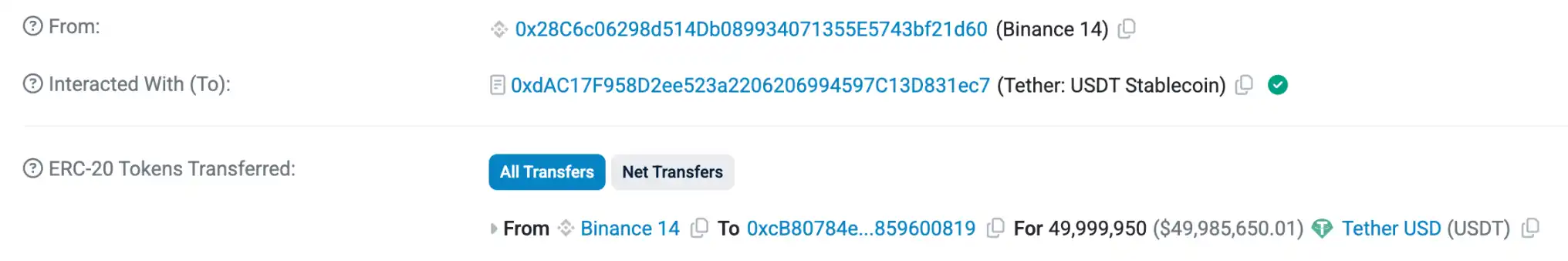
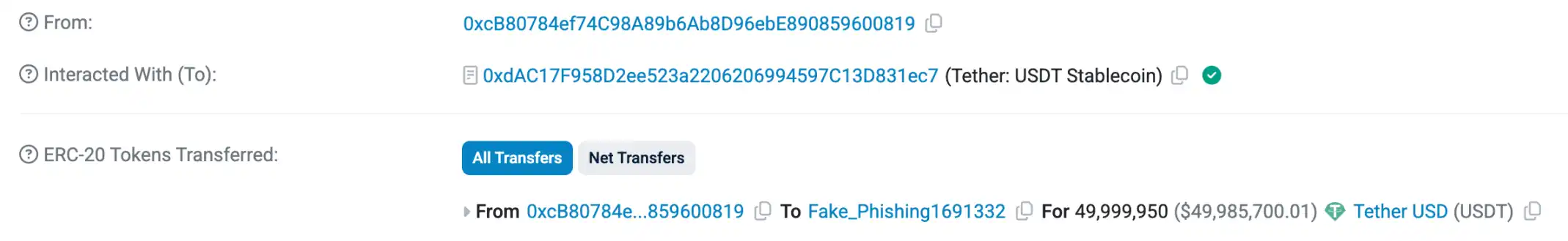
About 10 hours later, the address withdrew 49,999,950 USDT from Binance in one go. Combined with the previous 50 USDT withdrawal, the total amounted to exactly 50 million.
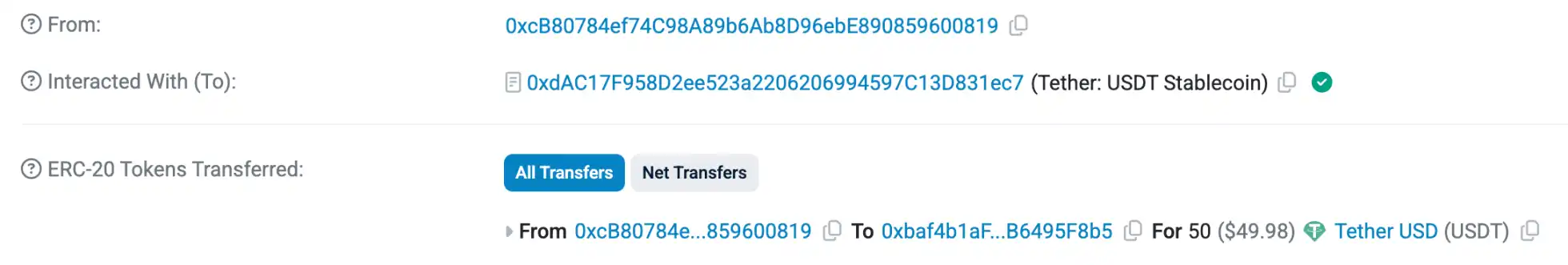
Approximately 20 minutes later, the address that received the 50 million USDT first transferred 50 USDT to 0xbaf4...95F8b5 for testing.
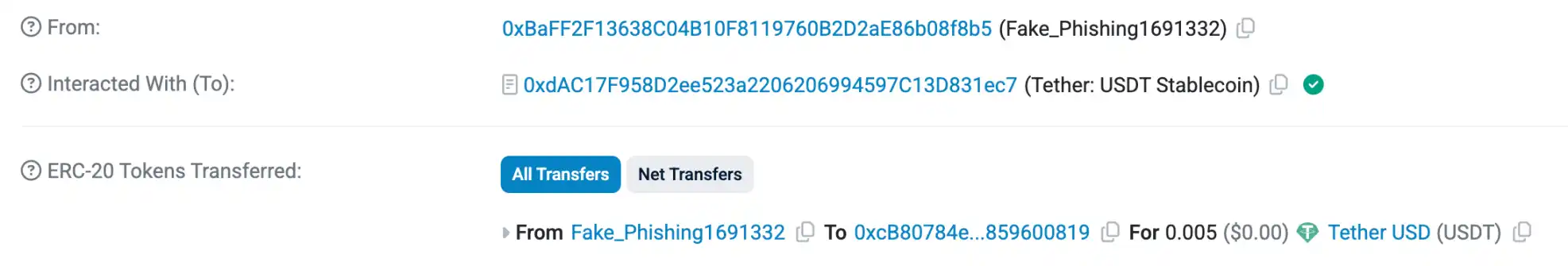
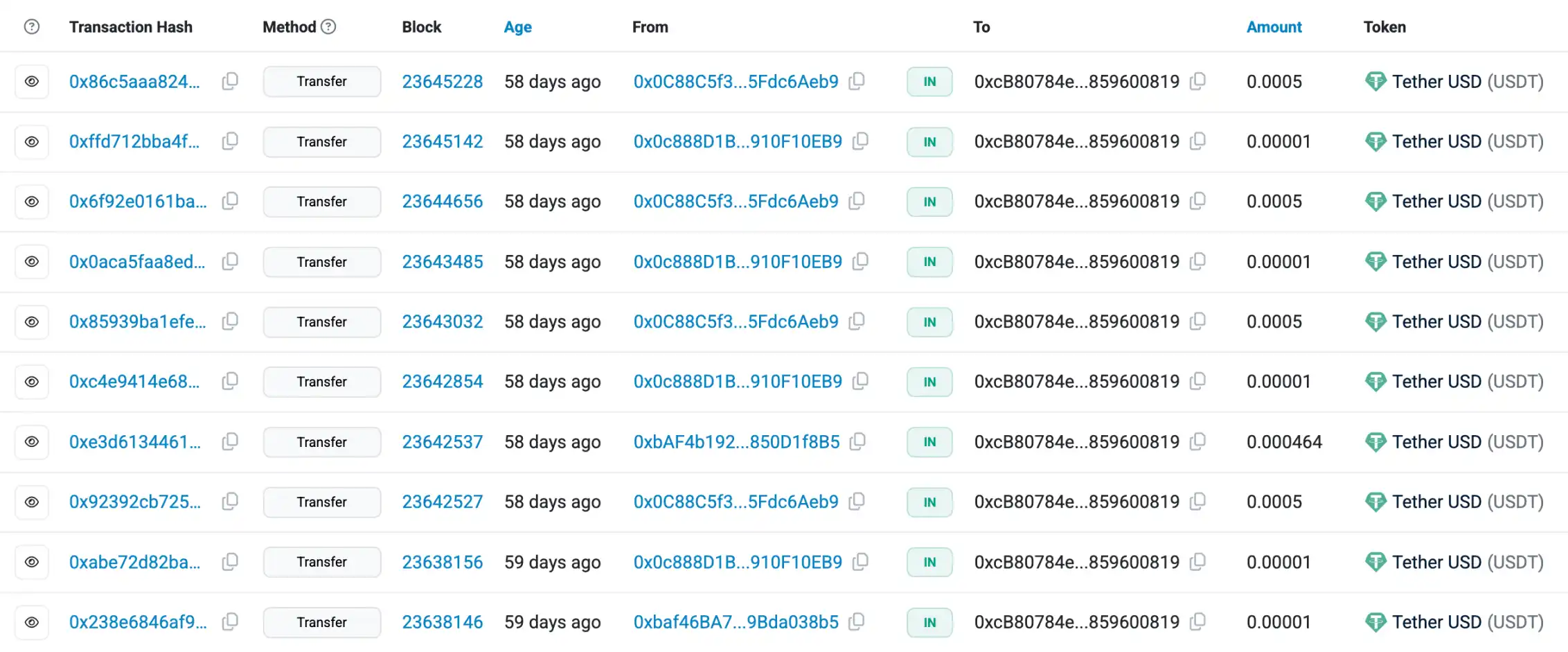
Within less than 15 minutes after the test transfer was completed, the hacker's address 0xbaff...08f8b5 transferred 0.005 USDT to the address holding the remaining 49,999,950 USDT. The address used by the hacker had similar beginning and ending characters to the address that received the 50 USDT, indicating a clear "address poisoning" attack.
10 minutes later, when the address beginning with 0xcB80 was preparing to transfer the remaining 40 million+ USDT, likely due to negligence, it copied the address from the previous transaction—the one used by the hacker for "poisoning"—and directly sent nearly 50 million USDT into the hands of the hacker.
With $50 million secured, the hacker began money laundering actions 30 minutes later. According to SlowMist monitoring, the hacker first swapped USDT for DAI via MetaMask, then used all the DAI to purchase approximately 16,690 Ethereum, kept 10 ETH, and transferred the remaining Ethereum to Tornado Cash.
Around 16:00 Beijing time yesterday, the victim addressed the hacker on-chain, stating that formal criminal proceedings had been initiated and that a substantial amount of reliable intelligence about the hacker's activities had been collected with the assistance of law enforcement, cybersecurity agencies, and multiple blockchain protocols. The victim stated that the hacker could keep $1 million and return the remaining 98% of the funds; if complied with, no further action would be taken; if not, criminal and civil liabilities would be pursued through legal channels, and the hacker's identity would be made public. However, as of now, the hacker has not responded.
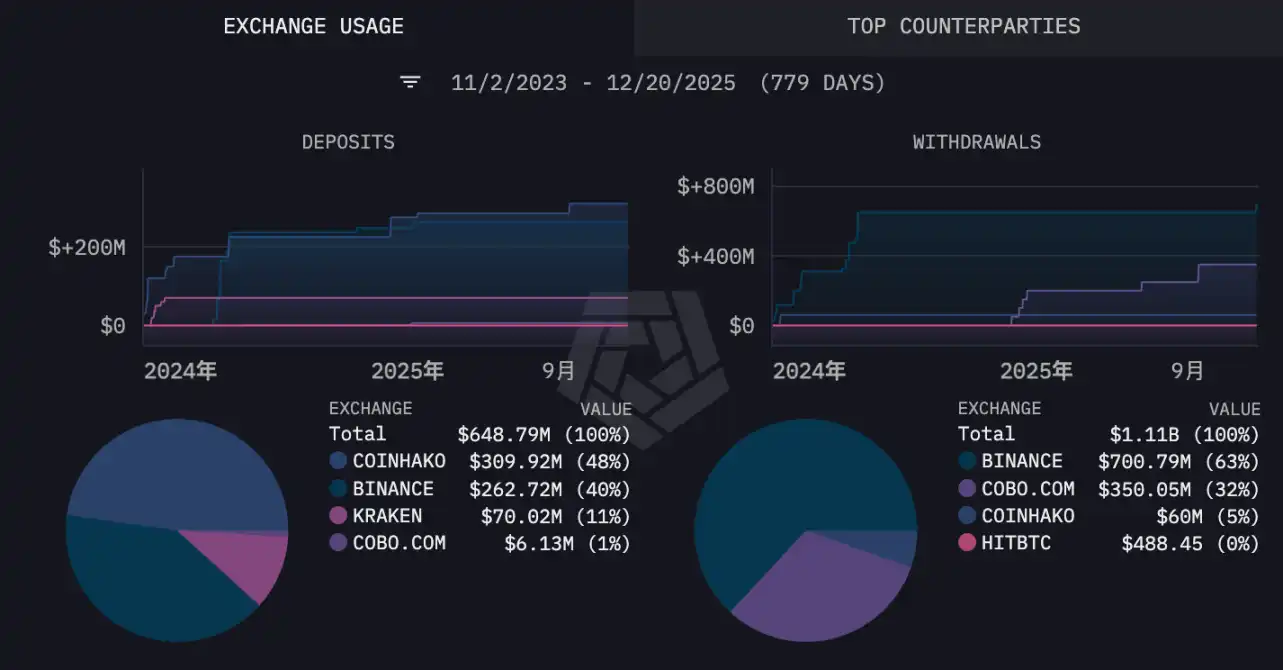
According to data compiled by the Arkham platform, this address has records of large transfers with addresses associated with Binance, Kraken, Coinhako, and Cobo. Binance, Kraken, and Cobo need no introduction, while Coinhako might be a less familiar name. Coinhako is a Singapore-based cryptocurrency exchange platform established in 2014. It obtained a Major Payment Institution license from the Monetary Authority of Singapore in 2022, making it a regulated exchange in Singapore.
Given that this address uses multiple exchange platforms and Cobo's custody services, and its ability to quickly contact various parties and complete the tracking of the hacker within 24 hours of the incident, the author speculates that this address most likely belongs to an institution rather than an individual.
A "Careless Mistake" Leads to Major Loss
The only explanation for falling victim to an "address poisoning" attack is "carelessness." Such attacks can be avoided simply by double-checking the address before transferring, but clearly, the protagonist of this incident skipped this crucial step.
Address poisoning attacks began to emerge in 2022, originating from "vanity address" generators—tools that allow customization of the beginning of an EVM address. For example, the author could generate an address starting with 0xeric to make the address more labeled.
This tool was later discovered by hackers to have a design flaw allowing brute-force attacks on private keys, leading to several major fund theft incidents. However, the ability to generate addresses with customized beginnings and endings also gave some ill-intentioned individuals a "clever idea": by generating addresses similar in beginning and ending to a user's commonly used transfer addresses, and transferring small amounts to the user's other addresses, some users might, due to carelessness, mistake the hacker's address for their own and actively send on-chain assets into the hacker's pocket.
Past on-chain information shows that the address beginning with 0xcB80 was a major target for such poisoning attacks even before this incident, with attacks beginning nearly a year ago. This attack method essentially involves hackers betting that you will eventually get lazy or inattentive and fall for it. Ironically, it is this seemingly transparent attack method that continues to ensnare "careless" victims one after another.
Regarding this incident, F2Pool co-founder Wang Chun expressed sympathy for the victim on Twitter (X), mentioning that last year, to test if his address had a private key leak, he transferred 500 BTC to it, only to have 490 BTC stolen by hackers. Although Wang Chun's experience was unrelated to address poisoning attacks, he likely meant to convey that everyone has moments of "stupidity," and we should not blame the victim for carelessness but rather direct our criticism towards the hackers.
$50 million is no small amount, but it is not the largest loss from such attacks. In May 2024, an address transferred over $70 million worth of WBTC to a hacker's address due to a similar attack, but the victim eventually recovered almost all the funds with the assistance of security company Match Systems and the Cryptex exchange. However, in this case, the hacker quickly converted the stolen funds into ETH and transferred them to Tornado Cash, making it uncertain whether recovery is possible.
In April, Casa co-founder and chief security officer Jameson Lopp warned that address poisoning attacks are spreading rapidly, with as many as 48,000 such incidents occurring on the Bitcoin network alone since 2023.
Including fake Zoom meeting links on Telegram, these attack methods are not sophisticated, but it is precisely this "simple" approach that can make people let their guard down. For those of us in the dark forest, being extra cautious is never wrong.