Treasury sent Congress its GENIUS‐Act‐mandated report on “innovative tools” to fight crypto‐enabled illicit finance.
A Crypto’s “Hold Law” And A Privacy Paradox
In a 32-page report submitted to the US Congress this March, the U.S. Treasury Department has endorsed lawful uses of crypto mixers (a service that takes in cryptocurrency from many different users, mixes all those coins together, and then sends each user back an equivalent amount from the pool, but from different addresses than the ones they used to deposit) in favor of privacy.
However, it has also urged lawmakers to create a new “digital‐asset‐specific hold law” so platforms can freeze suspicious funds.
Mixers, Privacy And DPRK
The report notes favorably that mixing and similar tools “can be used by lawful users seeking to enhance financial privacy on public blockchains,” including for “protecting sensitive information about personal wealth, business transactions, or charitable donations from public view. It adds that Treasury “recognizes that privacy‐enhancing technologies, including mixers and other obfuscation tools, may serve legitimate purposes when used by compliant actors in line with applicable AML/CFT requirements.”
On the other side, the same report also stresses that North Korea’s cyber units and major ransomware crews rely on mixers, cross‐chain bridges, and rapid swaps as core infrastructure to launder massive hauls from hacks and fraud. The report cites billions of dollars in stolen digital assets tied to DPRK actors and details how those funds are pushed through mixers and into stablecoins before being bridged and cashed out, using the same tools that ordinary users might pick for privacy.
What The “Hold Law” Would Do
Therefore, to tackle this paradox, the report proposes a “hold law” that would ensure that legitimate, clean, users keep their privacy while unlawful or suspicious activity can be addressed. Under the proposal, crypto exchanges and other regulated platforms would gain a clear and legal “pause button” for suspicious funds. The report recommends that “Congress establish a digital‐asset‐specific statutory ‘hold’ authority” that would allow platforms “to temporarily retain or delay the movement of digital assets associated with suspected illicit activity while appropriate legal process is pursued.” Firms could temporarily hold or delay those assets when strong red flags appear, with statutory cover for doing so.
The idea would be to give law enforcement time to act against ransomware crews, large fraud schemes, or state‐sponsored hackers, while limiting the tool to narrowly defined, high‐risk cases so routine customer flows are not frozen by default.
TradFi and Legacy media have often linked mixers to money laundering, with Tornado Cash as the obvious cautionary tale. Ethereum co‐founder Vitalik Buterin has repeatedly argued that mixers are neutral tools, even saying he used Tornado Cash to make a private donation to Ukraine, and is now backing ‘compliant’ designs like Privacy Pools that aim to protect on‐chain privacy without commingling with known dirty funds.
Another Piece On The GENIUS Act Puzzle
The report is part of the broader GENIUS Act framework, the law Trump signed to create a federal regime for payment stablecoins and push “innovative” tools against illicit finance. It fulfills a mandate for Treasury to spell out how AI, digital identity, and blockchain analytics should be used under a risk‐based AML approach.
The report also proposes a preferred tech stack (AI, digital ID, blockchain analytics, APIs) that regulated platforms should deploy under a risk‐based AML approach.
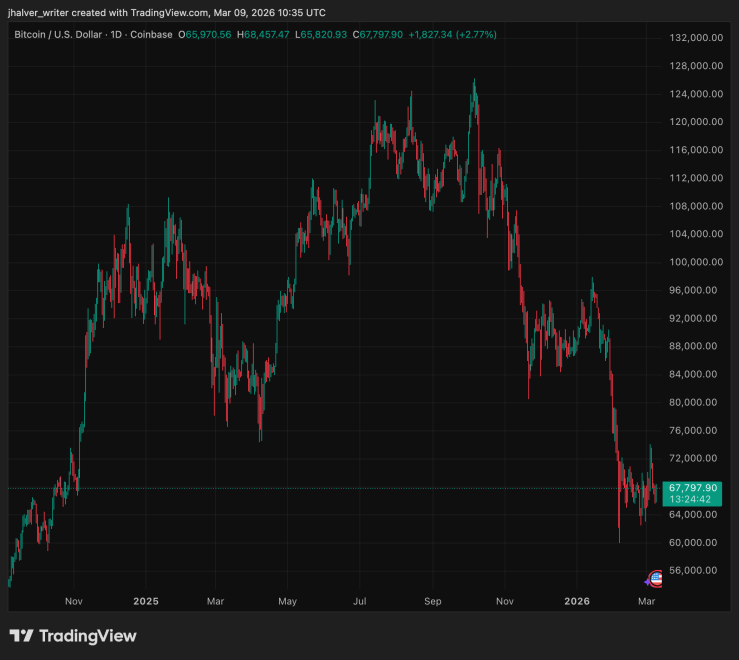
BTC's price trends to the downside on the daily chart. Source: BTCUSD on Tradingview
Cover image from ChatGPT, BTCUSD chart from Tradingview