Written by: Tiger Research
Key Points
- The core advantage of blockchain—transparency—can expose corporate trade secrets and investment strategies, posing substantial risks to businesses.
- Fully anonymous privacy models like Monero do not support KYC or AML, making them unsuitable for regulated institutions.
- Financial institutions require selective privacy, which protects transaction data while remaining compatible with regulatory compliance.
- Financial institutions must determine how to connect with open Web3 markets for expansion.
1. Why is Blockchain Privacy Necessary?
One of the core features of blockchain is transparency. Anyone can inspect on-chain transactions in real-time, including who sent the funds, to whom, the amount, and when it was sent.
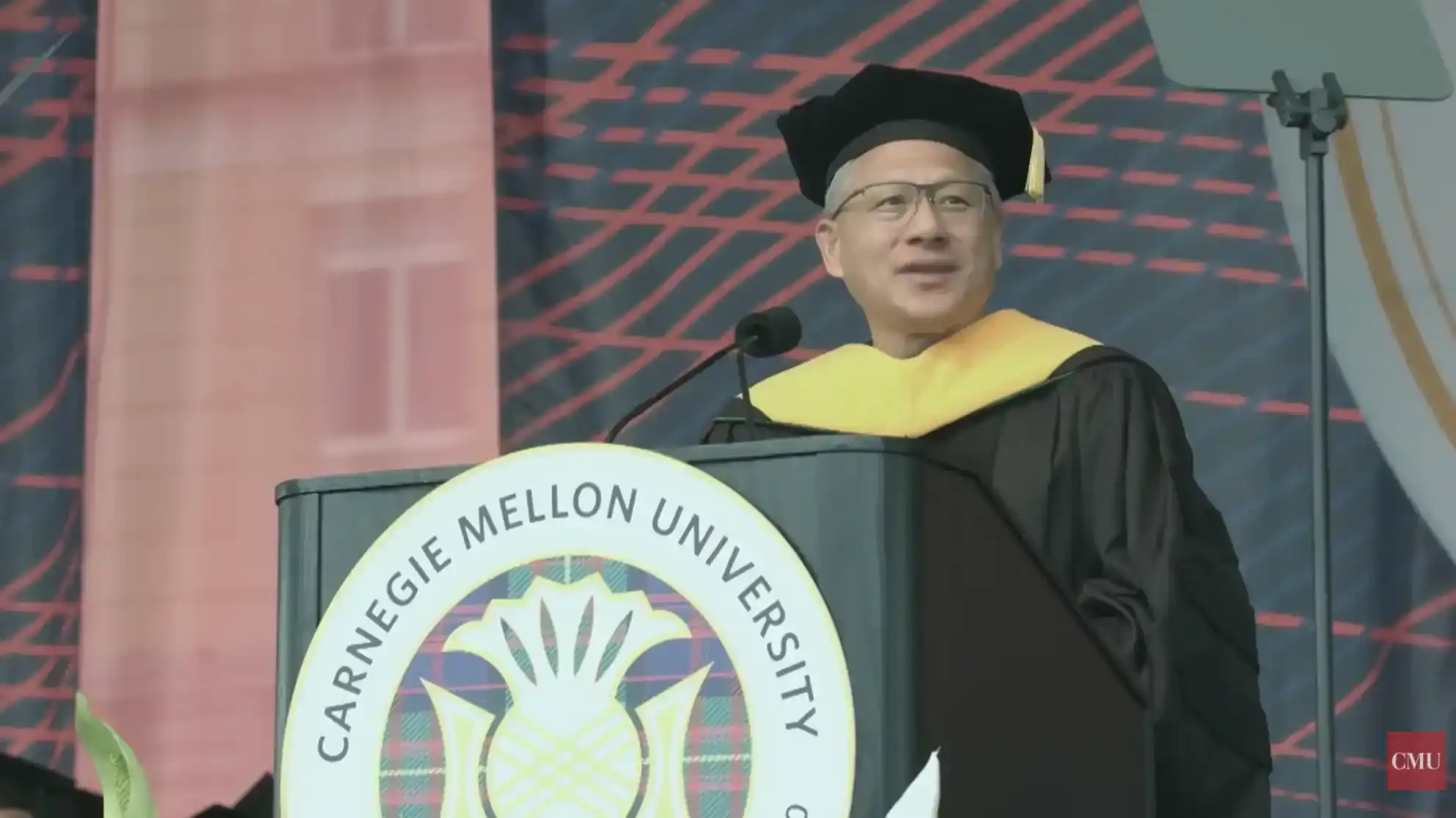
However, from an institutional perspective, this transparency presents obvious problems. Imagine a scenario where the market can observe how much NVIDIA transferred to Samsung Electronics, or precisely when a hedge fund deployed its funds. Such visibility would fundamentally alter competitive dynamics.
The level of information disclosure tolerable for individuals differs from what businesses and financial institutions can accept. A company's transaction history and the timing of institutional investments constitute highly sensitive information.
Therefore, expecting institutions to operate on a blockchain where all activities are fully exposed is unrealistic. For these participants, a system without privacy is less of a practical infrastructure and more of an abstract ideal with limited real-world application.
2. Forms of Blockchain Privacy
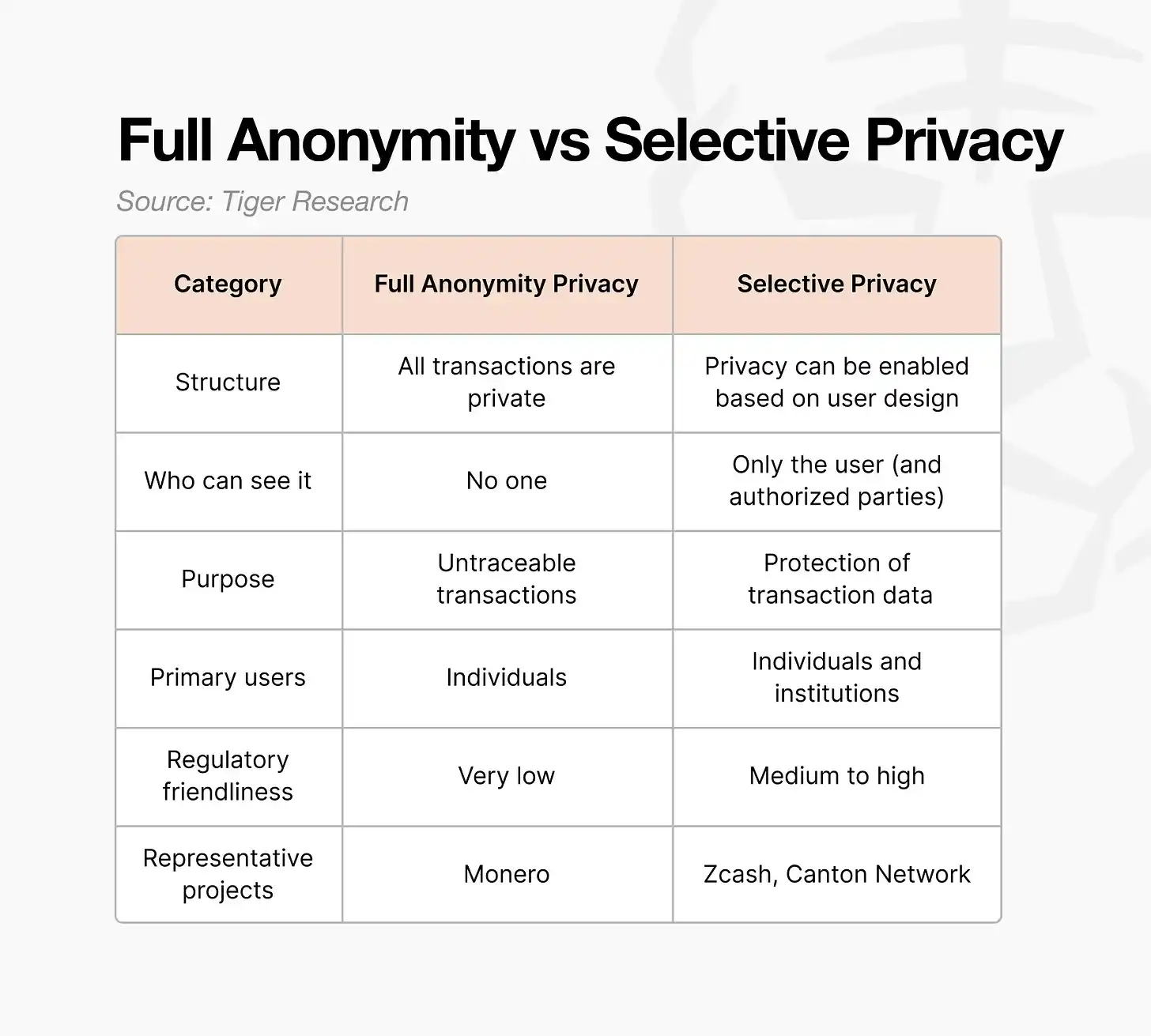
Blockchain privacy is generally divided into two categories:
- Fully Anonymous Privacy
- Selective Privacy
The key difference lies in whether information can be disclosed when another party requires verification.
2.1. Fully Anonymous Privacy
Fully anonymous privacy, simply put, hides everything.
The sender, receiver, and transaction amount are all hidden. This model stands in direct opposition to traditional blockchains, which prioritize transparency by default.
The primary goal of fully anonymous systems is to prevent third-party surveillance. Rather than enabling selective disclosure, they aim to completely prevent external observers from extracting meaningful information.
Source: Tiger Research
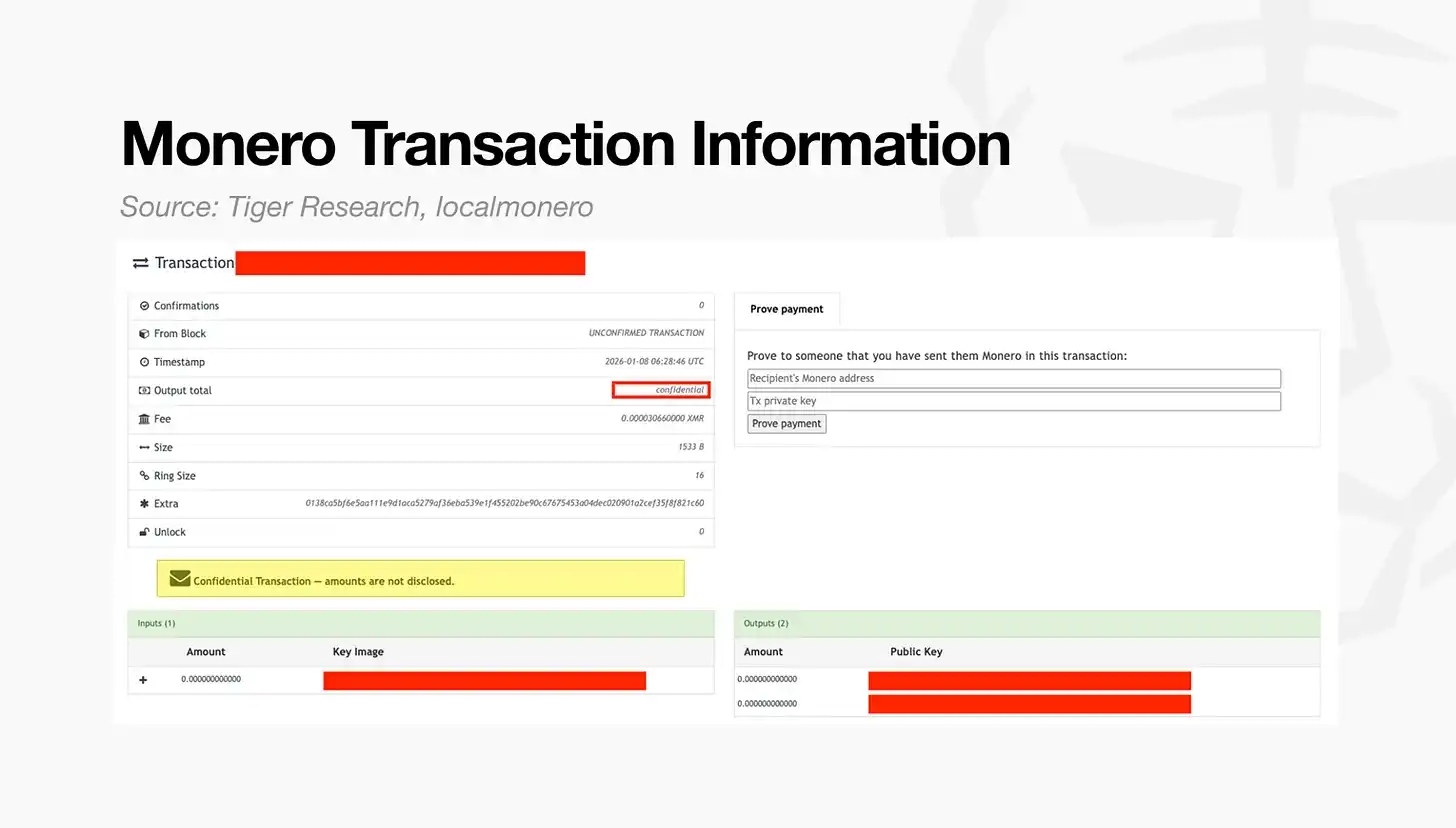
The above image shows a Monero transaction record, a representative example of fully anonymous privacy. Unlike transparent blockchains, details such as the transfer amount and counterparty are not visible.
Two characteristics illustrate why this model is considered fully anonymous:
- Output Totals: The ledger does not display specific numbers but shows values as "confidential." Transactions are recorded, but their content cannot be interpreted.
- Ring Signature Size: Although a single sender initiates the transaction, the ledger mixes it with multiple decoys, making it appear as if multiple parties are sending funds simultaneously.
These mechanisms ensure that transaction data remains opaque to all external observers without exception.
2.2. Selective Privacy
Selective privacy operates on a different assumption. Transactions are public by default, but users can choose to make specific transactions private by using designated privacy-enabled addresses.
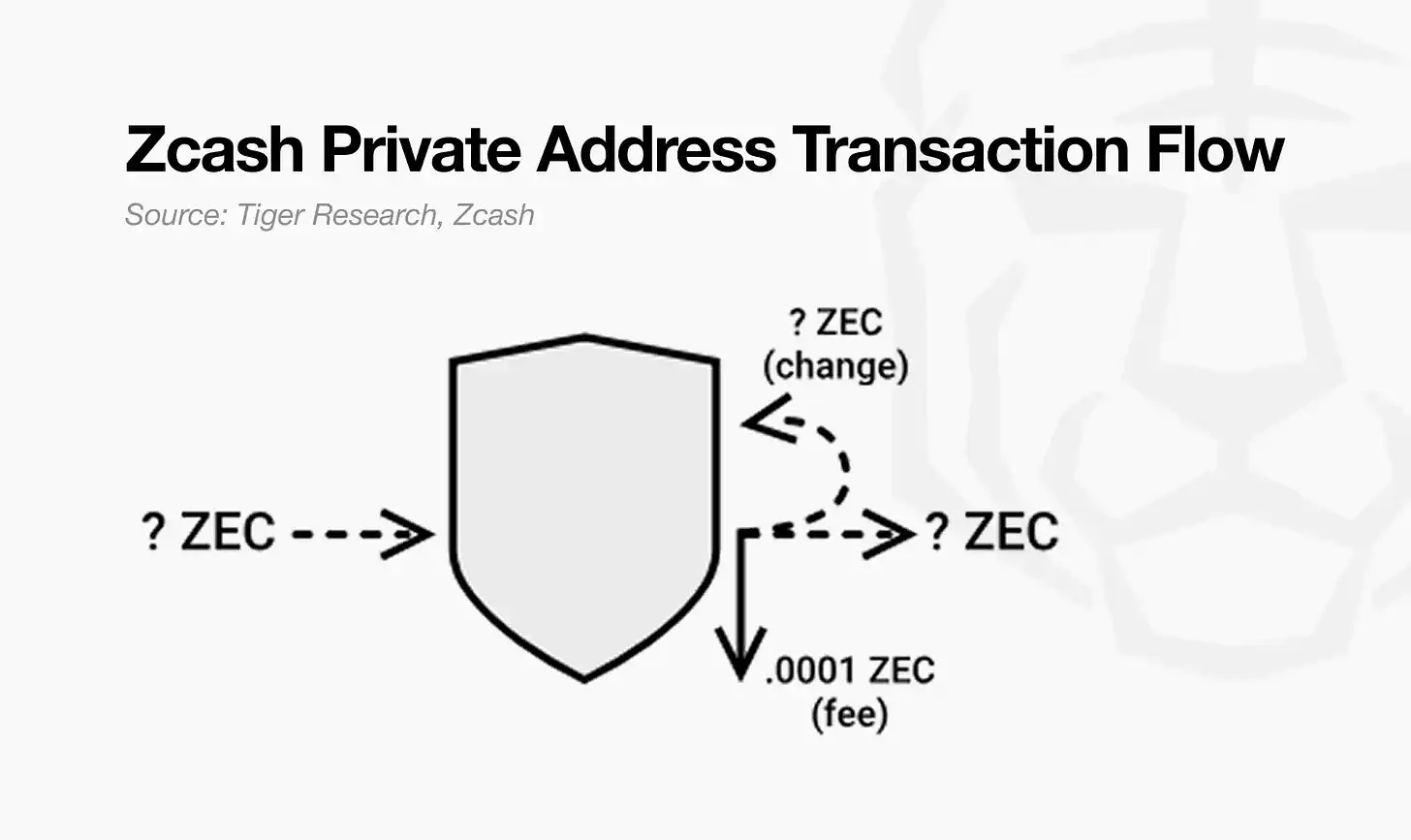
Zcash provides a clear example. When initiating a transaction, users can choose between two address types:
- Transparent Addresses: All transaction details are publicly visible, similar to Bitcoin.
- Shielded Addresses: Transaction details are encrypted and hidden.
Source: Tiger Research
The above image illustrates which elements Zcash can encrypt when using shielded addresses. Transactions sent to shielded addresses are recorded on the blockchain, but their content is stored in an encrypted state.
While the existence of the transaction remains visible, the following information is hidden:
- Address Type: Shielded (Z) addresses are used instead of transparent (T) addresses.
- Transaction Record: The ledger confirms that a transaction occurred.
- Amount, Sender, Receiver: All are encrypted and cannot be observed externally.
- Viewing Rights: Only parties granted a viewing key can inspect the transaction details.
This is the core of selective privacy. Transactions remain on-chain, but users control who can view their content. When necessary, users can share a viewing key to prove transaction details to another party, while all other third parties remain unable to access that information.
3. Why Financial Institutions Prefer Selective Privacy
Most financial institutions have Know Your Customer (KYC) and Anti-Money Laundering (AML) obligations for every transaction. They must retain transaction data internally and respond immediately to requests from regulators or supervisory bodies.
However, in an environment built on fully anonymous privacy, all transaction data is irreversibly hidden. Because the information cannot be accessed or disclosed under any conditions, institutions are structurally unable to fulfill their compliance obligations.
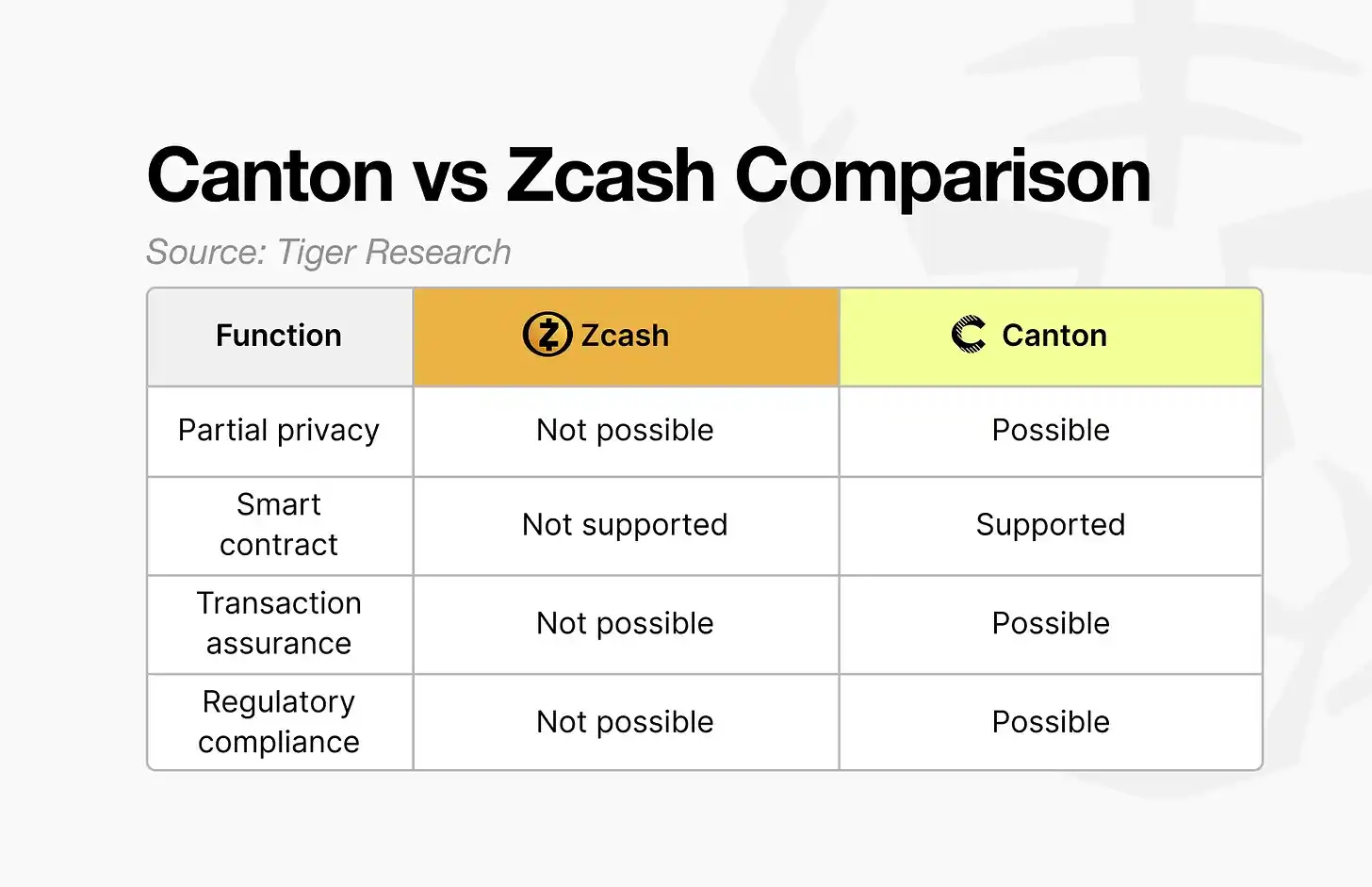
A representative example is the Canton Network, which has been adopted by the Depository Trust & Clearing Corporation (DTCC) and is currently used by over 400 companies and institutions. In contrast, Zcash, although also a selective privacy project, has seen limited real-world institutional adoption.
What is the reason for this difference?
Source: Tiger Research
Zcash offers selective privacy, but users cannot choose which information to disclose. Instead, they must choose whether to disclose the entire transaction.
For example, in a transaction where "A sends $100 to B," Zcash does not allow only the amount to be hidden. The transaction itself must be either fully hidden or fully disclosed.
In institutional transactions, different participants require different information. Not all participants need access to all data in a single transaction. However, Zcash's structure forces a binary choice between full disclosure and full privacy, making it unsuitable for institutional transaction workflows.
In contrast, Canton allows transaction information to be divided into separate components for management. For example, if a regulator only requires the transaction amount between A and B, Canton enables the institution to provide only that specific information. This functionality is achieved through Daml, the smart contract language used by the Canton Network.
Other reasons for institutional adoption of Canton are covered in more detail in previous Canton research.
4. Privacy Blockchains in the Institutional Era
Privacy blockchains evolve as demands change.
Early projects like Monero aimed to protect individual anonymity. However, as financial institutions and corporations began entering the blockchain environment, the meaning of privacy shifted.
Privacy is no longer defined as making transactions invisible to everyone. Instead, the core goal has become protecting transactions while still meeting regulatory requirements.
This shift explains why selective privacy models like the Canton Network have gained traction. Institutions need more than just privacy technology; they need infrastructure designed to match real-world financial transaction workflows.
In response to these demands, more institution-oriented privacy projects continue to emerge. Looking ahead, the key differentiator will be how effectively privacy technology can be applied to practical transaction environments.
Alternative forms of privacy that run counter to the current institution-driven trend may emerge. However, in the short term, privacy blockchain is likely to continue evolving around institutional transactions.