Preface
With the popularization of the blockchain concept, virtual currencies have gradually entered the public view but have also been targeted by criminals as a new tool for online pyramid scheme crimes. These criminals, under the banner of "blockchain innovation" and "virtual currency appreciation," use highly inflammatory rhetoric such as "guaranteed profits," "get rich overnight," and "only goes up, never down" to lure the public into blind investment.
Different from traditional pyramid schemes, virtual currency online pyramid schemes rely on online platforms, using the decentralized and highly anonymous nature of virtual currencies as the scheme's emblem. They lure participants with "high returns," require them to develop downlines through invitation codes, build a multi-level organizational structure, and use the number of recruits, recharge amount, and hierarchy level as the basis for rebates. They are more concealed, have a wider reach, and are extremely harmful.
To help everyone see the true nature of such scams and avoid property risks, the Lingshi Technology security team, based on industry security practices and a series of blockchain security popular science articles, focuses on the theme of virtual currency online pyramid schemes, breaking down the scam tactics and teaching identification and prevention techniques.
I. Virtual Currency Online Pyramid Scheme Models
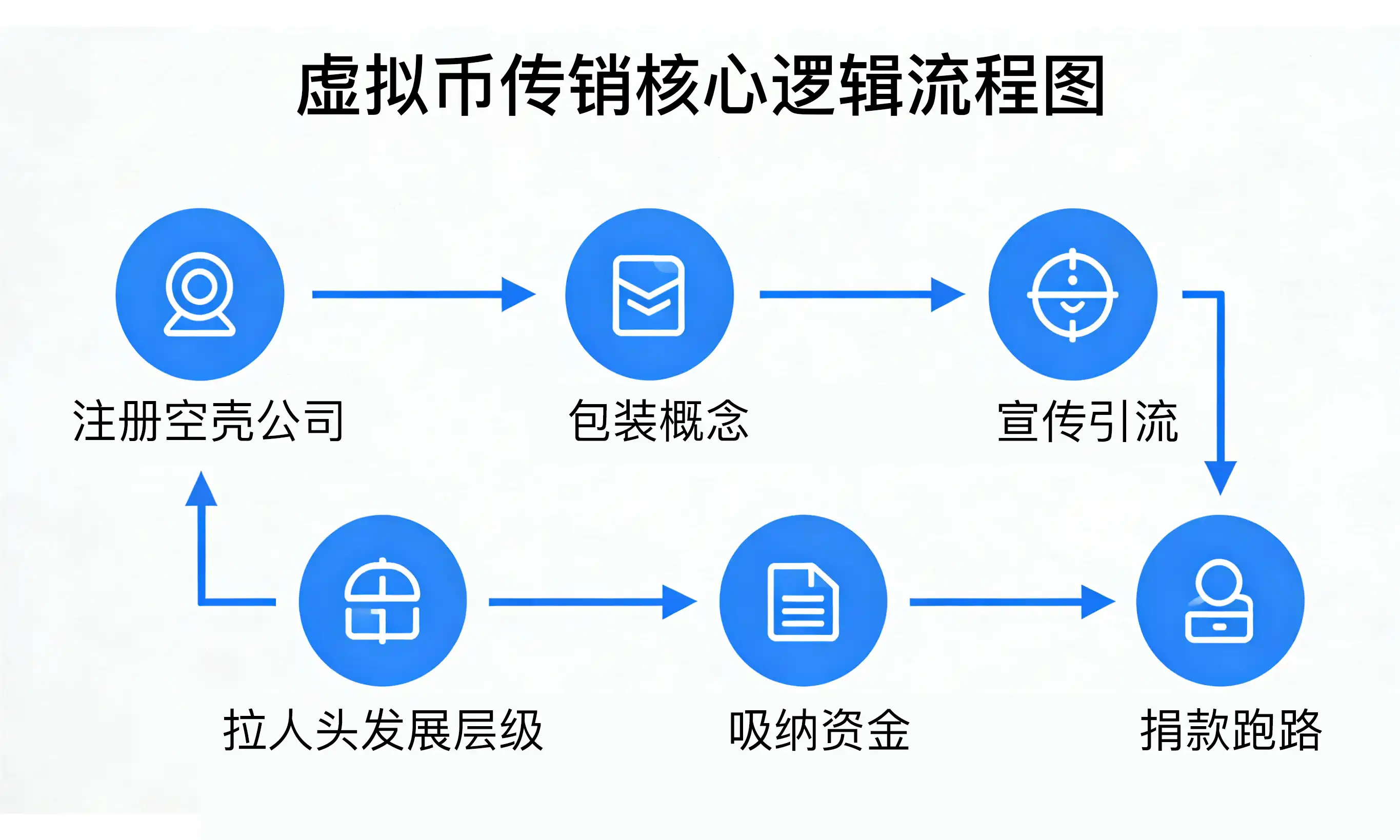
The core logic of pyramid schemes has commonalities: scheme leaders typically register shell companies at home and abroad, build websites, establish trust in the name of charity, wealth management, healthcare, etc., then promote the value of virtual currencies through channels like WeChat, QQ, and offline lectures, using "high rebates" to encourage "recruiting people" to develop downlines, ultimately敛财 (amassing wealth) by absorbing member funds. With blockchain technology, these schemes have衍生出 (derived) multiple new models that are more subtle and deceptive:
1. Contract Exchange Model
Criminal groups利用 (utilize) the derivative attributes of virtual currency contract trading to build山寨 (copycat) trading platforms and issue platform coins (used as handling fees), claiming to provide trading services for mainstream coins like BTC and ETH. In reality, using the "contract exchange" as a幌子 (pretext), they诱导 (induce) investors to open high-value accounts and use pyramid-style rebates, "partner systems," and other high rewards to lure them into developing downlines. What seems like high returns actually targets the investor's principal. After illegally敛财 (amassing wealth), they often软跑路 (perform a "soft exit") with excuses like "hacker attacks" or "new coin settlements."
2. Staking Mining Model
Project parties, under the banner of "mining to receive virtual currency rewards," attract participants to抵押 (stake) specified mainstream coins to a project address they provide. The staking period ranges from 3 months to 1 year, during which funds cannot be随意划转 (freely transferred). To套取 (siphon off) more funds, the project party informs participants that "higher hashrate leads to more mining rewards," and the hashrate increase is directly tied to the "amount of staked coins," "number of downlines developed," and "amount staked by downlines." Once the project address gathers sufficient funds, the project party will卷走 (abscond with) all the mainstream coins.
3. Wealth Management Wallet Model
Project parties, using "virtual currency appreciation services" as a噱头 (gimmick), build wealth management wallet APPs and issue空气币/山寨币 (air coins/copycat coins), exaggerating the project's prospects and claiming to earn price differences through "cross-exchange arbitrage." Participants must obtain a member account through an upline recommendation, bind the hierarchical relationship, and pay a designated virtual coin as an门槛费 (entry fee) to activate the "arbitrage function." Profit rebates are directly linked to the recharge amount and the number of downlines. In reality, the platform's coin issuance and price fluctuations are manipulated by the project party's backend. Profits displayed are false numbers. Once the target funds are reached, they卷款跑路 (abscond with the money).
4. Smart Contract Model
Criminal groups利用 (utilize) the smart contract features of DeFi (Decentralized Finance), deploy the involved smart contract to the blockchain, package it as a wealth management project, and promote high returns within communities. Different from other models, this scam has no involved APP. Participants must search for the project's DApp link through mainstream wallets to participate. The hierarchical relationship is bound through the participating addresses. Once participants transfer virtual coins to the project's contract address, the suspects directly control the funds and卷币跑路 (abscond with the coins).
5. Quantitative Trading Bot Model
Quantitative trading bots are essentially辅助交易工具 (auxiliary trading tools) that bind to exchange APIs and have no withdrawal permissions, but are exploited by criminal groups as carriers for pyramid schemes. These APPs attract downloads with buzzwords like "smart strategy," "24-hour automatic trading," and "low risk, stable profits." They require new users to hold mainstream coins and transfer them into the APP as a participation门槛 (threshold). Rebates and commissions are obtained by拉人头 (recruiting people). The platform misleads users by伪造 (fabricating) profit data, while in reality, they have already secretly transferred the users' virtual coins.
II. Core Harms of Virtual Currency Online Pyramid Schemes
Virtual currency online pyramid schemes not only infringe on personal property but also cause multiple impacts on financial order and social stability:
◆ Irreversible Property Loss: After the pyramid scheme collapses or the operators abscond, virtual currency funds are mostly transferred to overseas addresses, making tracking extremely difficult. Participants' losses are basically irrecoverable;
◆ Risk of Involvement in Illegal Activities: Participants who develop downlines to a certain scale may become accomplices in the pyramid scheme and bear legal responsibility;
◆ Disruption of Financial Order: Funds flow无序 (disorderly) without supervision, easily滋生 (breeding) associated crimes like money laundering and illegal fundraising, impacting the real economy;
◆ Damage to Industry Ecology: Using the names "blockchain" and "virtual currency" to commit fraud misleads the public's understanding of blockchain technology and hinders the development of legitimate and compliant blockchain industries.
Typical Cases
In recent years, virtual currency pyramid scheme scams have occurred frequently. Typical cases serve as a wake-up call: In the 2024 "XX Coin" pyramid scheme case, the criminal group built a virtual currency trading platform, lured people with "30% annualized returns from staking mining," developed over 100,000 downlines, involved金额 (amounts involved) reached 230 million RMB. The leaders eventually absconded with the funds overseas, leaving most participants with nothing. In the 2023 "Smart Contract Wealth Management" scam, over 5,000 people were attracted by a packaged DeFi project, involved funds reached 170 million RMB. Funds were transferred instantly after being sent to the contract address and have not been recovered to this day.
The commonality of these cases is: they all use "high returns" as the core bait, rely on "recruiting people" for hierarchical rebates, and ultimately end with "absconding." The anonymity of virtual currencies multiplies the difficulty of case detection and fund recovery.
III. How to Identify if it Has the Characteristics of a Pyramid Scheme Crime?
◆ Check if the virtual currency acts as an entry fee for the pyramid scheme activity, i.e., whether it is used as a payment method for purchasing goods or services;
◆ Pay attention to whether the virtual currency is used by the pyramid scheme organization as a basis for calculating remuneration or rebates;
◆ Observe whether the virtual currency is used to deceive more people into participating in the pyramid scheme活动 (activity);
◆ Scrutinize the profit model, focusing on whether profits are primarily illegally gained from the investments of participants at various levels, whether participants'收益 (income) is settled in virtual currency, and whether their earnings depend mainly on the number of downlines and their investment amount, rather than on the market price fluctuations of the virtual currency.
IV. Regulatory Policy Red Lines
China explicitly prohibits any illegal issuance and trading of virtual currencies and更严厉打击 (more severely cracks down on) virtual currency-related pyramid scheme activities:
◆ In 2021, the central bank and multiple departments jointly issued the "Notice on Further Preventing and Dealing with Virtual Currency Trading Speculation Risks," clarifying that virtual currencies are not legal tender, do not have the same legal status as legal tender, and their trading and speculation activities carry extreme legal risks;
◆ Article 224之一 (one) of the "Criminal Law of the People's Republic of China" clearly states that organizing and leading pyramid scheme activities are criminal offenses, punishable by up to five years of fixed-term imprisonment or criminal detention, and a fine; if the circumstances are serious, the punishment is more than five years of fixed-term imprisonment and a fine;
◆ Regulatory authorities across the country持续开展 (continuously carry out) special campaigns to整治 (rectify) virtual currency pyramid schemes,查封冻结 (sealing and freezing) involved platforms and fund accounts, and追究 (pursuing) criminal responsibility against relevant personnel according to the law.
Conclusion
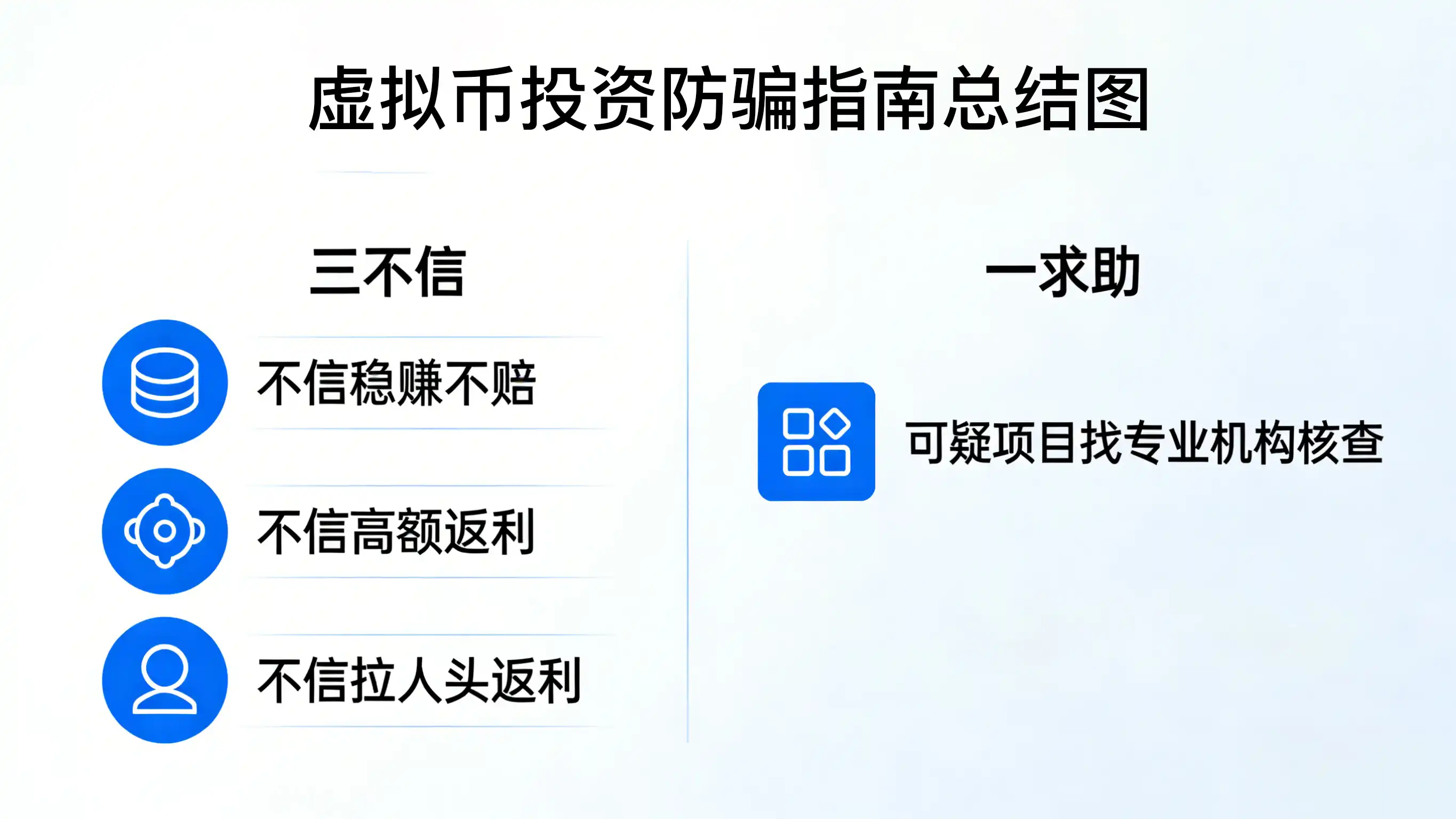
The essence of virtual currency online pyramid schemes is "using the name of new technology to conduct pyramid schemes." No matter how complex the packaging, the core always revolves around the套路 (tactic) of "recruiting people, hierarchical rebates, defrauding funds." Faced with various temptations of virtual currency investment, remember the basic logic that "high returns必然伴随 (inevitably accompany) high risks, and guaranteed profits are a scam." Guarding the bottom line of not being greedy for profits and not following blindly can effectively avoid most risks.
As an enterprise focused on blockchain security, the Lingshi Technology security team is always committed to providing security guarantees for the public and enterprises: We can use blockchain security detection technology to help identify technical vulnerabilities and abnormal fund flows in virtual currency pyramid scheme platforms; provide free scam consultation services to help everyone analyze the compliance of suspicious projects; and continuously output security popular science content to enhance public blockchain security awareness. If you encounter suspicious virtual currency investment projects, please feel free to contact us at any time. Let's jointly resist illegal financial activities and protect property safety.