On January 8, 2026, the Truebit Protocol was hacked, resulting in a loss of 8,535.36 ETH (approximately $26.44 million). The Truebit Protocol officially confirmed the incident in the early hours of the following day. The ExVul security team conducted a detailed analysis of the vulnerability, with the results as follows:
Attack Process
Attacker's address:
0x6c8ec8f14be7c01672d31cfa5f2cefeab2562b50
Attack transaction hash:
0xcd4755645595094a8ab984d0db7e3b4aabde72a5c87c4f176a030629c47fb014
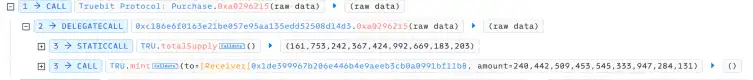
The attacker completed the attack by cyclically calling getPurchasePrice→0xa0296215→0xc471b10b for four rounds. The first cycle is analyzed as an example.
1. The attacker first called the getPurchasePrice(240442509453545333947284131) function, which returned 0.
2. The attacker called the 0xa0296215(c6e3ae8e2cbab1298abaa3) function with msg.value as 0. Finally, 240442509453545333947284131 TRU were successfully minted.
3. The attacker called the 0xc471b10b(c6e3ae8e2cbab1298abaa3) function. Finally, 240442509453545333947284131 TRU were burned, and 5105.06 ETH were obtained.
Attack Logic Analysis
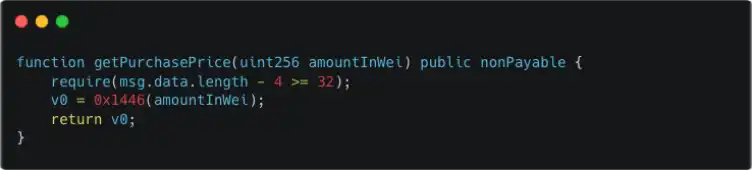
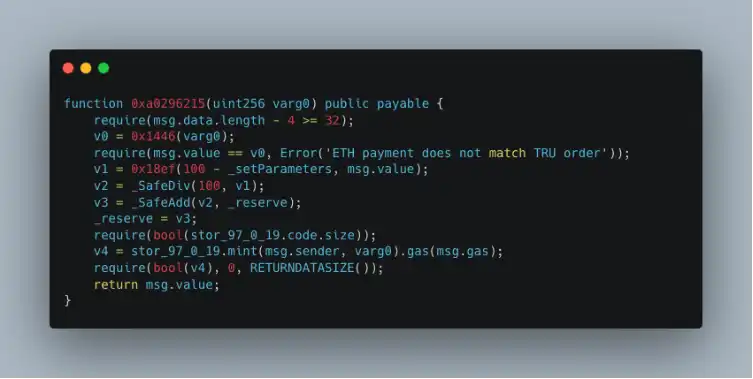
By understanding the above attack process, it is clear that there is an issue with the logic of the getPurchasePrice function and the 0xa0296215 function. The following is an in-depth analysis (since the contract is not open source, the code below is decompiled).
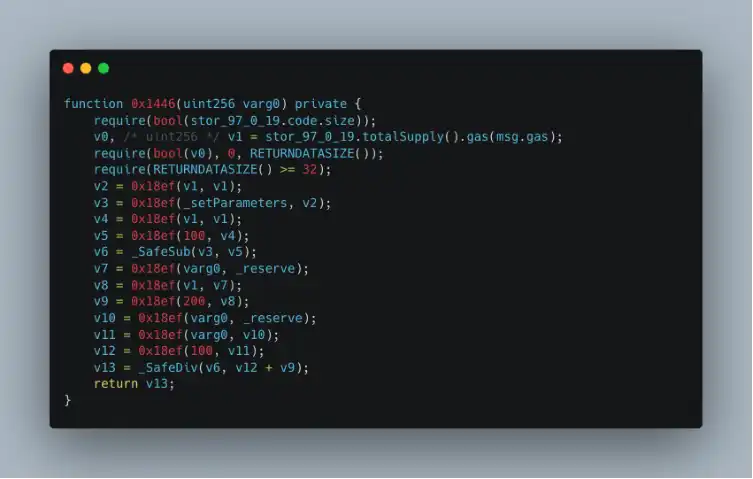
By comparing the common points of the two functions, we can see that the 0x1446 function is used to calculate how much ETH is needed to purchase a specified amount of TRU. Clearly, the logic of the 0x1446 function is flawed, leading to an incorrect ETH calculation. The logic within the 0x1446 function is analyzed in detail below.
Observing the logic in the 0x1446 function, since the final calculation result v13 == 0, the calculation logic mentioned above must be problematic. It is important to note that the 0x18ef function is the same as _SafeMul, so the issue lies in the native addition v12 + v9 (the contract version is ^0.6.10, so there is no overflow check).
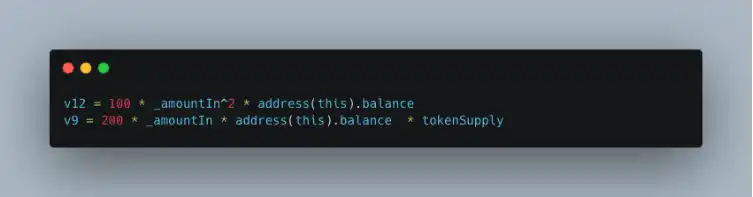
v12 and v9 represent:
Based on the above analysis, the attacker's strategy was to input a huge _amountIn to cause v12 + v9 to overflow into a very small value, ultimately resulting in (v12 + v9) / v6 == 0.
Summary
The root cause of the Truebit Protocol attack is a severe integer overflow vulnerability in its token purchase price calculation logic. Since the contract uses Solidity ^0.6.10 and lacks safety checks for critical arithmetic operations, it ultimately led to a significant loss of 8,535.36 ETH. The latest versions of Solidity have already mitigated overflow vulnerabilities. This attack was likely discovered by hackers using AI to automatically scan older DeFi protocols that are already live (including recent attacks on Balancer and yETH). We believe such attacks exploiting AI to target older DeFi protocols will become increasingly common in the near future. Therefore, we recommend that project teams conduct new security audits of their contract code. If vulnerabilities are found, they should upgrade the contract or transfer assets as soon as possible, and implement on-chain monitoring to detect anomalies promptly and minimize losses.