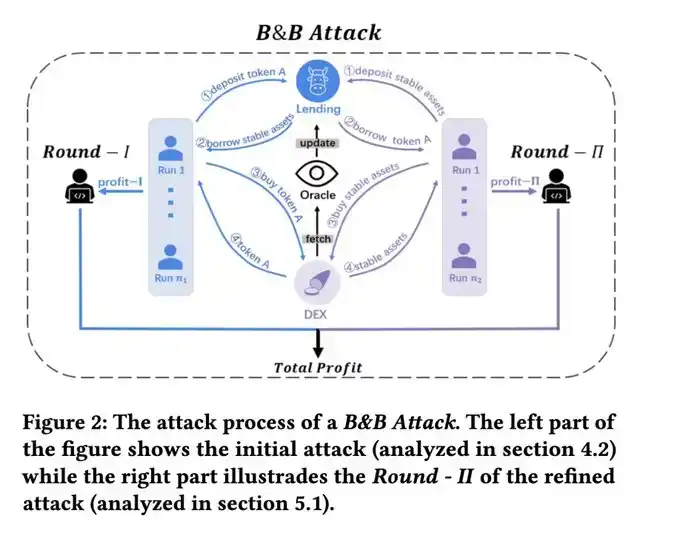
Two hours ago, VenuV's THE token was hit with a classic Mango Markets-style price manipulation attack.
The attacker targeted the low-liquidity collateral THE:
· First, collateralized THE
· Borrowed other assets
· Used the borrowed assets to buy more THE
· Pushed THE price higher
· Waited for the time-weighted average oracle price to update, then obtained higher collateral value and continued the cycle of borrowing.
Due to THE's extremely poor on-chain liquidity, its price was driven from $0.27 to nearly $5. The oracle price subsequently updated to around $0.5 (time-weighted average), giving the attacker room to further amplify leverage.
More critically, THE itself has a supply cap.
Normally, this would limit the attacker's ability to expand their position. But they used a classic old trick to bypass it: the Compound fork donation attack. After depositing a large amount of THE, they directly transferred THE to the vTHE contract, "donating" to further inflate the collateral value recognized by the system and break through the cap.
Attack transaction: 0x4f477e941c12bbf32a58dc12db7bb0cb4d31d41ff25b2457e6af3c15d7f5663f
After the first wave of the attack, THE's price stabilized around $0.5.
At this point, the attacker could have walked away with the borrowed assets. But they clearly wanted to maximize profits, so they continued to use the borrowed assets to buy THE, attempting another pump.
The problem arose: Although the price was abnormally high, selling pressure from the market became extremely intense. The attacker kept buying but could barely push the price higher. Eventually, they almost exhausted their borrowing capacity, and their position's health factor dropped close to 1, nearing liquidation.
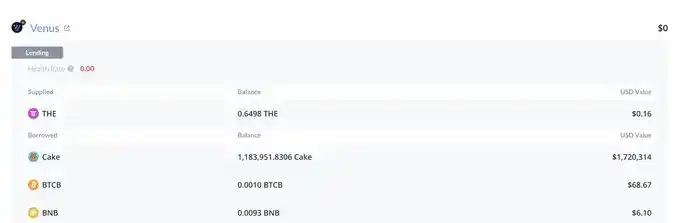
By then, the situation was very clear: The attacker's collateral, including their pre-prepared assets and THE bought during the attack, had a nominal value of about 30M. But the core issue with this collateral was—there was simply not enough liquidity to absorb it. Once liquidation began, this THE would be dumped onto the market. And no one in the market could possibly absorb such a large volume at these inflated prices.
So what did I do?
When liquidation started, I directly opened a short position on THE. And this was a position where relatively higher leverage could be applied.
The reason was simple: High valuation, low liquidity, massive passive selling pressure, no buyers.
The outcome was unsurprising: After the liquidation ended, THE's price fell all the way back to around $0.24, even lower than the pre-attack price, because original holders also sold during the process.
I closed my short position here, profiting about 15K.
In the end, Venus was left with about 2M in bad debt.
As for how much the attacker actually profited, I haven't done a complete analysis; but judging from the operations of some addresses, they likely made little to no profit, or even blew themselves up. However, the attacker might still have profited from off-chain perp positions (just like our operation).
Venus's ~2M bad debt address: https://debank.com/profile/0x1a35bd28efd46cfc46c2136f878777d69ae16231
This incident once again demonstrates:
In DeFi, "nominal collateral value" does not equal "liquidation value". When the collateral itself lacks liquidity, the system sees 30M, but the market might only be able to realize a fraction of that.
In 2023, I published a paper titled 'Unmasking Role-Play Attack Strategies in Exploiting Decentralized Finance (DeFi) Systems' which provides a detailed mathematical model of this type of attack. Interested readers can refer to: https://dl.acm.org/doi/10.1145/3605768.3623545