In the blink of an eye, I've been working in the wallet space for four years now.
Many people think the wallet landscape in 2025 is already solidified, but that's not the case—it's full of undercurrents. This year alone:
- Coinbase newly released a CDP wallet, built on TEE technology at its core.
- Binance's MPC wallet introduces key shard custody into a TEE environment.
- Bitget just launched social login functionality last week, underpinned by TEE custody.
- OKX Wallet rolled out smart account features based on TEE.
- MetaMask and Phantom introduced social login, which is essentially encrypted storage of key shards.
While no particularly dazzling new players have emerged this year, the existing players have undergone earth-shaking changes in their ecosystem positioning and underlying technical architectures.
This transformation stems from drastic changes in the upstream ecosystem.
With the BTC and inscription ecosystem fully receding, many wallets have begun to adopt a new positioning as "gateways,"承接 (undertaking) emerging tracks like Perps (perpetual contracts), RWA (stock-like assets), and CeDeFi (a combination of centralized and decentralized finance).
This shift has actually been brewing for years.
Follow along with this article to deeply understand the flowers blooming in the shadows and their impact on future users.
2. Reviewing the Development Stages of the Wallet Track
Wallets are a rare necessity product in the blockchain industry and an entry-level application that, besides public chains, was among the first to break through tens of millions of users.
2.1 Phase One: The Single-Chain Era (2009-2022)
In the early days of the industry (2009-2017), wallets were extremely difficult to use, even requiring local node operation. We'll skip this phase.
By the usable phase, self-custody became the preferred choice—after all, in a decentralized world, "trust by default is not the foundation" is the survival basis. MetaMask, Phantom, Trust Wallet, OKX Wallet, and other familiar products were the stars of this period.
From 2017 to 2022, the market entered an explosion period for public chains/L2s. Although most chains still adhered to Ethereum's EVM architecture, building a good compatible tool was sufficient to meet needs.
During this period, the core positioning of wallets was "good tools." Although the industry could see the commercial远景 (vision) of traffic gateways and DEX entry points, security, ease of use, and stability were the primary requirements.
However, from 2023 to 2025, the situation changed.
Heterogeneous public chains like Solana, Aptos, and BTC (during the inscription period) completely captured the user market. Although Sui itself developed well, after a hacking incident, large funds became somewhat hesitant due to the drawbacks of excessive centralization.
Driven by the "fat protocol, thin application" financing era, although VCs saw meager returns, the market landscape did change.
2.2 Phase Two: The Multi-Chain Era (2022-2024)
Facing the multi-chain格局 (landscape), even established players like MetaMask had to转型 (pivot), beginning to build-in support for Solana, BTC, etc. Top players like OKX Wallet and Phantom implemented multi-chain compatible architectures even earlier.
The core标志 (indicator) for judging multi-chain compatibility is how many chains are supported and where transactions are sent from—this represents a lot of work handled in the backend, with the client only responsible for signing. From the user's perspective, it's about whether they need to find their own RPC nodes to use the wallet.
Now, multi-chain compatibility is almost standard. Persisting long-term with a single chain can easily become unsustainable because chain hotspots constantly change.
A typical case is the Keplr wallet, which focuses on the Cosmos ecosystem, but this track never really took off. Many application chains built quickly based on Cosmos gradually fell silent after launch. As the barrier to building EVM L2s gets lower and lower, the situation for single-chain wallets might ease, but their ceiling is also there.
After the basic tools became good enough, users began to awaken to business needs within wallets!
True asset owners don't just custody assets; they actively drive them—seeking the best yield opportunities, choosing interaction targets. But users are also tortured by the complexity of interacting with various DApps and have to constantly be wary of phishing sites.
Since that's the case, why not just use the wallet's built-in functions?
2.3 The Business Competition Branching Period
The competitive focus of various wallets shifted to the business level,典型的是 (typically) aggregated DEXs and aggregated cross-chain bridges. Although Coinbase explored integrating social features, this demand was过于伪需求 (too much of a pseudo-demand) and never gained much traction.
Returning to rigid needs, users need to complete multi-chain asset transfers from a single wallet entry point. Here, coverage, speed, and slippage became the core competition points.
The DEX field can be further extended to derivative trading: RWA (like tokenized stocks), Perps (perpetual contracts), prediction markets (hot in the second half of 2025,毕竟 (after all) the World Cup is in 2026).
Parallel to DEX is the DeFi yield demand.
After all, on-chain APY is higher than traditional finance:
- Coin-denominated strategies: ETH staking offers about 4% APY, Solana staking + MEV offers about 8% APY (details可见 (can be seen in) the extensive research report: The Evolution and Merits of MEV on Solana), more aggressive strategies can involve liquidity pools (LP), cross-chain bridge LPs.
- Stablecoin strategies: Although yields are relatively lower, APY can be boosted with循环杠杆操作 (recursive leverage operations).
So by this year (2025), at the peak of business competition, the wallet infrastructure simultaneously ushered in another upgrade.
The reason is that the aforementioned transactions are too complex—not just the complexity of the transaction structure, but also the complexity of the transaction lifecycle.
To achieve truly high yields, automated trading is needed: dynamic position adjustment, timed limit orders (not just market orders), dollar-cost averaging, stop-loss, and other advanced functions.
But these functions were simply impossible to achieve in the pure self-custody era.
So, is it about complete "security first" or "profit first"? It's not really a dilemma because the market inherently has different demands.
Just like during the heyday of Telegram Bots, lots of players handed over their private keys for automatic trading opportunities—a high-risk model of "if you're scared, don't play; if you play, don't be scared." In comparison, large service providers making wallets must consider brand and reputation.
Is there a solution that can both securely custody private keys and relatively ensure the service provider doesn't run away?
Of course there is! This brings us to this year's underlying custody technology upgrade.
3. The Underlying Custody Technology Upgrade Period
Returning to the underlying technical upgrades mentioned at the beginning, let's analyze them one by one.
3.1 Farewell to the Pure Self-Custody Era
First, the moves by pure wallet manufacturers like Metamask and Phantom are relatively lighter, more experience-driven, because social login only solves user scenarios like cross-device use and recovery, not fully切入 (cutting into) specific application layer tracks.
But their transformation does, to a certain extent, bid farewell to the era of complete self-custody.
Self-custody has degrees, but no one can truly define what is complete and what is not.
First, self-custody itself means the user's private key is only stored on the user's device. But this has had many problems in the past.
Locally encrypted stored private keys, if the device is compromised, can be brute-forced, with strength relying on the user's password.
When syncing across devices or backing up, it always has to be copied out, making the operating system's clipboard permissions a direct lifeline.
It's memorable that a certain wallet manufacturer, on the page for copying the private key, only pasted the first part by default, requiring the user to manually type the remaining few characters, which directly caused a more than 90% drop in reported private key theft cases during that period. Later, hackers learned and brute-forced the remaining characters, indirectly entering another period of对抗 (confrontation).
After the Ethereum Prague upgrade, due to the extremely high permissions of 7702, obscure signatures, and the特殊性 (particularity) of full-chain impact, high-phishing-risk things like permit 2 were激發 (stimulated) again.
So, the root of self-custody is that users simply aren't accustomed to the industry background of完全控制资产 (completely controlling assets) themselves.
After all, the private key is with the user, that's自然没问题 (naturally fine). But if an encrypted copy of the private key is kept on the server to prevent the窘境 (predicament) of complete loss if the user's local device is lost, does that still count as self-custody?
The answer from Metamask and Phantom is, it also counts. But at the same time, it must also prevent the service provider from malicious acts.
3.2 First, Metamask
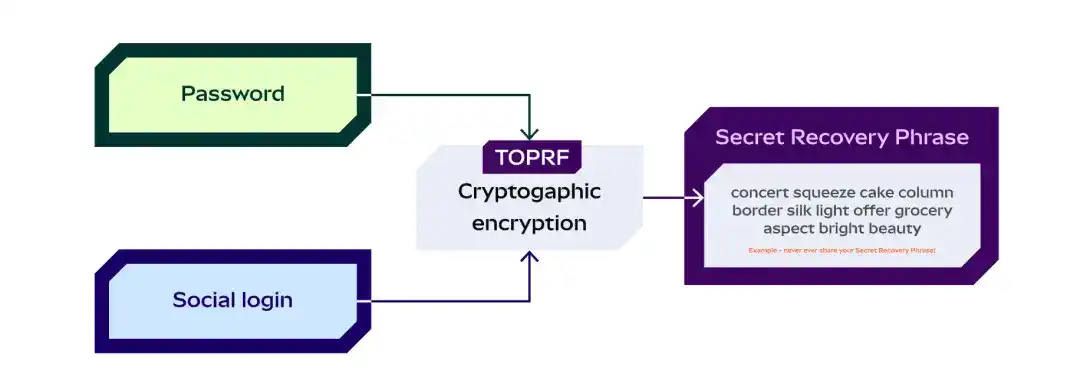
Their approach is simple: the user logs in with an email and sets a password. The two are combined to form something called TOPRF (Threshold Oblivious Pseudorandom Function), which is used to encrypt the user's private key. The encrypted private key can naturally be backed up.
Then this TOPRF is distributed using the typical SSS (Shamir's Secret Sharing algorithm). These social login service providers then obtain the encrypted data through social verification, which must be combined with the user's password to be fully decrypted.
So the security risk isn't completely absent; after all, weak passwords + email theft still pose a risk, and if the user forgets the password,自然恢复不出来 (naturally it can't be recovered). But the benefit is greater convenience, and the experience is basically consistent with Web2.
3.3 Looking at Phantom
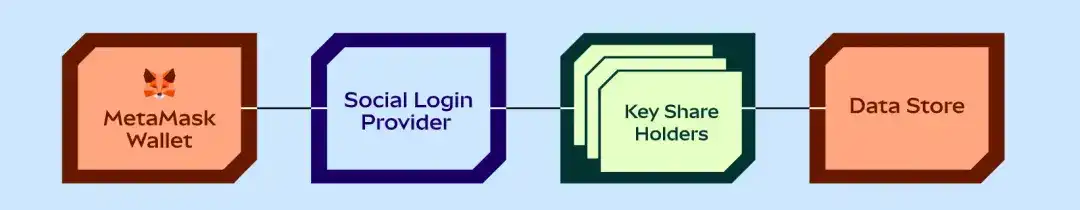
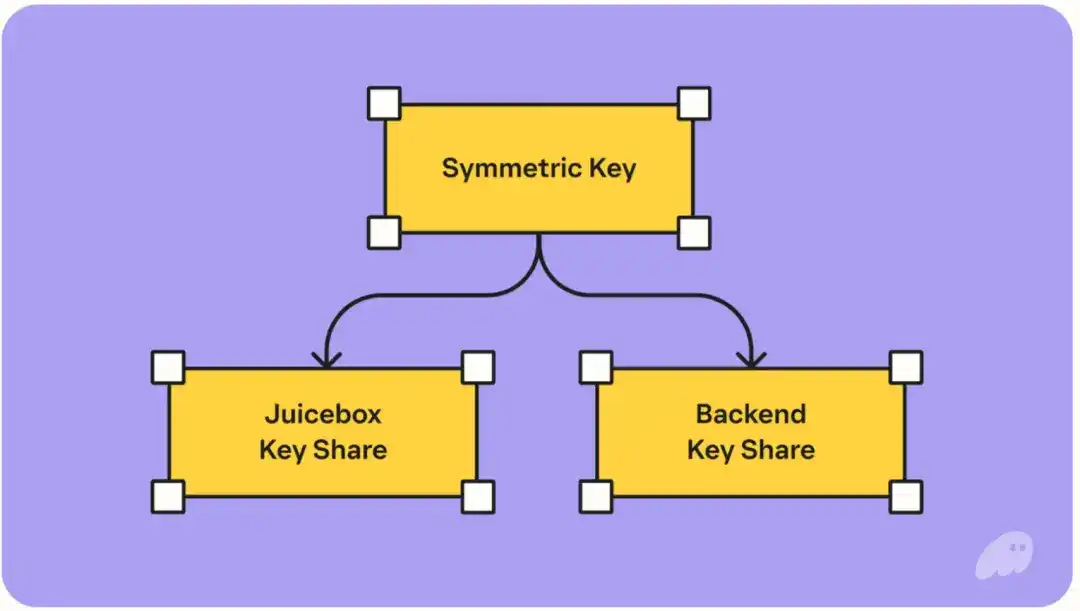
Looking at the diagram, the overall architecture is more complex, but the essence is still back-end storage of the encrypted private key, with sharded management of the encryption/decryption key.
The difference from小狐狸 (the little fox - Metamask) is that the key used for encryption is split into 2 parts. They introduced another service provider called the JuiceBox network to store one of the parts. Social login + a pin (4 digits) must be combined to use its shard.
Overall, the user only needs to ensure the email isn't stolen and the pin isn't forgotten to recover access at any time.
Of course, in the extreme case of JuiceBox and Phantom colluding, they could also decrypt the assets, but at least the hacker's attack cost changes from a single point to multiple parties. Moreover, Juicebox is a network, and its security design is distributed across multiple validators.
It can be said that in terms of social recovery, these two companies are making certain compromises while adhering to the bottom line, but it's a good change compared to suppressing user experience (UX) for low-probability events.
The author believes this is a good转变 (shift), because what the blockchain industry needs most is to embrace ordinary users, not force ordinary users to become industry experts.
4. Self-Custody Using Trusted Technology Environments (TEE)
The social login mentioned earlier can only solve the recovery problem, but not the automated trading problem.
So each company's approach here is somewhat different.
First, some background: TEE stands for Trusted Execution Environment. It is essentially still a server, but this server ensures that its memory environment and running process cannot be read or interfered with, even by the AWS provider or the server owner.
Additionally, once it starts running a program, it publicizes a file called an Attestation. The party interacting with the TEE can verify whether this document matches the open-source version they publicized.
Only when the program running matches the specified open-source version will the two correspond, thus proving trustworthiness. This has many applications in the industry already:
- For example, Avalanche's official cross-chain bridge uses SGX (a TEE model) to run its公证人验证者 (notary validators).
- For example, on the Ethereum mainnet, already 40% of the blockchain completes transactions and block production through Buildr net, which is also TEE-based underneath.
- Not to mention various financial banks, which strictly control internal risks and have basically introduced TEE. Head exchanges, under the compliance background of 2025, have also expensively introduced TEE for cold and hot wallet signature custody.
Although using TEE also has its difficulties, such as lower machine performance (can be堆 (stacked) with money) and宕机风险 (downtime risk) (loss of memory information), plus upgrade complexity.
The remaining question is how the various exchange manufacturers provide TEE services in wallets.
4.1 Coinbase and Bitget's Solutions
It was hard to imagine at first, but Coinbase, a compliant exchange listed on the US stock market, has the most centralized version.
And Bitget's logical architecture is almost identical.
Essentially, they only use the TEE as a service for generating private keys and driving signatures. But how does the TEE verify that this service truly represents the user's intention?
Coinbase完全基于 (completely relies on) the user logging in, relying on backend authentication to forward instructions to the TEE to complete the transaction.
Bitget is the same. Although information is scarce, currently it doesn't seem to show a signing page on the client side, and directly sets up an eip-7702 address for the new address, thus achieving gas sponsorship.
The advantage of this system可以说 (can be said to be) that at least the private key for the user's assets is indeed in the TEE. But as for whether the backend will put other strange instructions in there, that is neither verifiable nor falsifiable.
But fortunately, there is evidence on the chain.
Therefore, the author believes that Coinbase et al. are essentially betting on the exchange's reputation. After all, whether the private key is exported must be recorded, which can rule out user fraud for insurance purposes. The only risk is the exchange itself acting maliciously, which is actually consistent with the underlying model of users trusting CEXs.
4.2 Bn (Binance) and Okx
Comparing the MPC of these two and OKX's SA (Smart Account), the logic is essentially the same. In driving transactions, OKX will pop up an intent authorization signing page. Combined with the logic of verifying intent within the TEE, the user's authorization level is higher, but the comprehensive user understanding cost is also higher.
Binance's MPC is more influenced by its existing technical system (MPC is actually quite limited in multi-chain expansion). After introducing TEE, it requires the user to encrypt and transmit a shard from their local device into the TEE. OKX's method involves the user's own local mnemonic phrase being encrypted and transmitted into the TEE.
As a user, don't worry too much about the security risk here. Reliable communication between TEE and client is very mature nowadays; theoretically, it completely prevents man-in-the-middle attacks. After all, using the TEE's public key for asymmetric encryption means only the private key can decrypt it.
There are also some detailed experience differences, like how long MPC/private keys last inside the TEE before expiring and how to renew them. These are engineering issues and won't be expanded upon.
Analyzing the design motivation, the benefit of this design is mainly migration cost, avoiding the cold start problem where users have to migrate assets to experience new advanced features.
For example, CB's (Coinbase's) approach focuses on the payment track, allowing traditional e-commerce service providers without local private key management experience to call private keys via API to complete on-chain operations.
And Binance's approach is combined to target the CeDeFi track, allowing users who usually watch price charts to more easily operate and purchase on-chain assets from similar interfaces, ignoring issues like gas, slippage, and multiple chains.
5. Summary
How to evaluate 2025, and how to view the future?
The author believes this year is a year of silence for wallets, but also a year of transformation. There wasn't much fanfare, but big things were done quietly.
In today's multi-chain environment, simply being a useful tool is already insufficient to support a large-scale wallet team (and its supporting infrastructure). It inevitably needs various value-added services for oxygen supply. And it just so happened that this year was also an explosion year for applications, with the Perps track reborn, RWA (stock direction), prediction markets, and payments all showing improvement simultaneously.
The market is gradually moving from fat memes to diverse Dex demands.
Moreover, memes only seem like a big market because the trading is too fast and the流水金额 (flow amount) is too high. Actually, it's always the same group of people playing, the hotspots change, but user growth isn't large.
Combined with various new custody systems backed by TEE and the reputation of each exchange.
And in the macro trend, AI will become increasingly powerful, as will AI trading. Previous wallets were only prepared for people, not for AI.
So what the author sees is that next year will see an even richer explosion in applications because the underlying technology has become more mature. There will definitely still be a gap period because the TEE approach is still for big exchanges; they are unlikely to easily open their external entry points completely like Coinbase did.
Additionally, users playing Dex with funds is only part of the demand. There is a much larger user base that just wants to earn some stable money. Combined with subsidies during various promotion periods and various airdrops, plus some APY, they are very satisfied.
CeDeFi products that can capture on-chain yields will be the first landing point for many Cex users (Note: this mainly refers to CeDeFi with independent addresses; shared address types like Bitget's cannot capture this).
Finally, there have been significant improvements in cryptographic technology this year with passkeys, although this article hasn't covered them. But more and more public chains like Ethereum and Solana are gradually integrating the R1 curve (which passkeys natively support) through precompiled contracts. So wallets incorporating passkeys are also a伏笔 (foreshadowing) (although their recovery and cross-device sync are tricky), so there aren't many good applications yet.
After all, any product that can streamline high-frequency demand will eventually find its place.