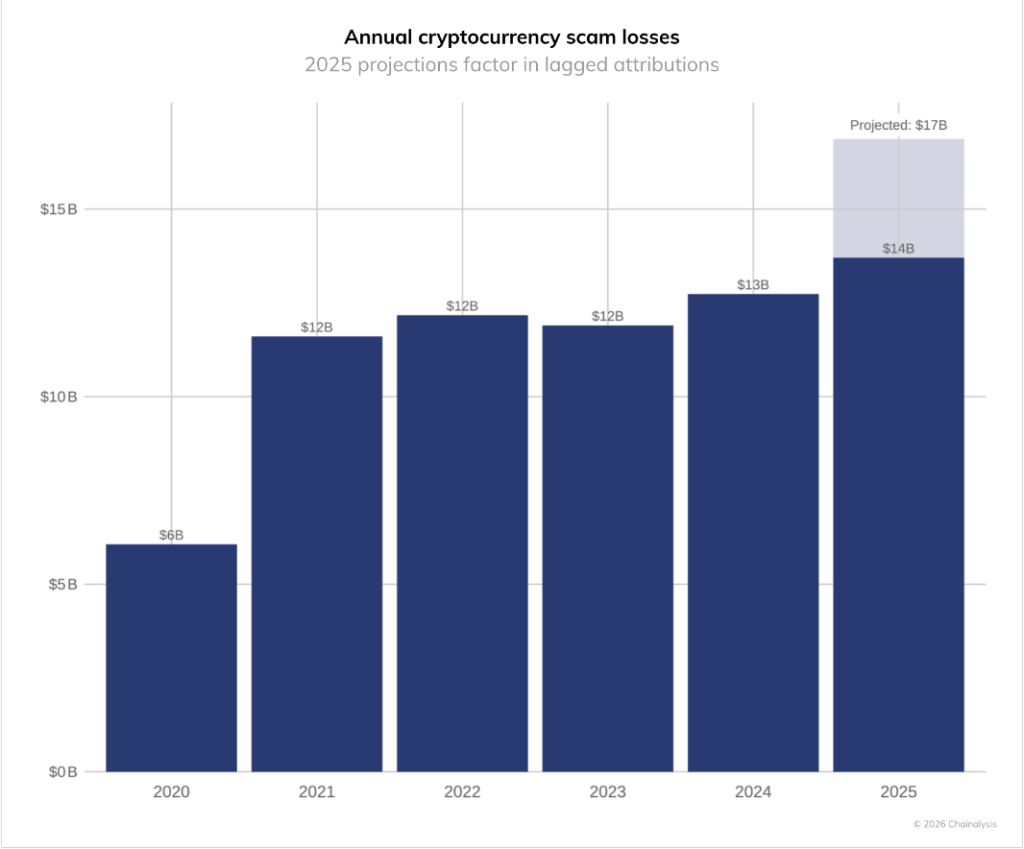
Impersonation scams exploded in 2025, growing by about 1,400% and driving some of the biggest losses seen in crypto fraud to date. According to analysis by Chainalysis, scammers used AI tools, voice cloning and fake customer-support schemes to scale up attacks, pushing total scam losses on chain into the low-double-digit billions.
Impersonation Scams Jump Dramatically
Reports have disclosed that the rise was not just in the number of cases but in how much each case cost victims. The average amount taken in impersonation schemes rose by over 600% compared with the prior year, a jump that turned many small cons into large heists. Chainalysis highlights the role of automated tooling and commercially available phishing services that let scammers run scams like factories.
Source: Chainalysis
Criminals Used AI And Deepfakes
Fraudsters leaned heavily on AI techniques in 2025. Based on reports, AI-generated voice and face clones, paired with very believable messages, helped criminals impersonate exchange staff, celebrities or close contacts. These methods increased both reach and success rates. Industry writeups and analysts show that AI-enabled scams were several times more profitable than older approaches.
A High-Profile Example Shows The Risk
One public example involved scammers posing as a major exchange and clearing nearly $16 million from victims in a single operation. That case became a headline because it showed how quickly an impersonation scam can turn into a mass theft when it uses polished fake identities and coordinated social engineering. Financial news outlets and industry trackers used that case to illustrate the shift in tactics.
Operations Became Industrialized
Based on Chainalysis data, scam groups now resemble small businesses. They outsource parts of the fraud chain — writing scripts, buying deepfake clips, and hiring money movers. This setup made fraud more efficient and harder to disrupt. One analysis found AI-assisted schemes were about 4.5 times more profitable than traditional scams, a gap that attackers exploited to level up operations quickly.
Estimates of total crypto scam losses for 2025 vary by outlet, but multiple sources put the number well into the billions. Some trackers reported $14 billion in funds stolen on chain, while Chainalysis noted the figure could be as high as $17 billion once more data is tallied. The difference reflects how quickly new incidents were discovered and how some thefts moved off public rails.
Featured image from Unsplash, chart from TradingView