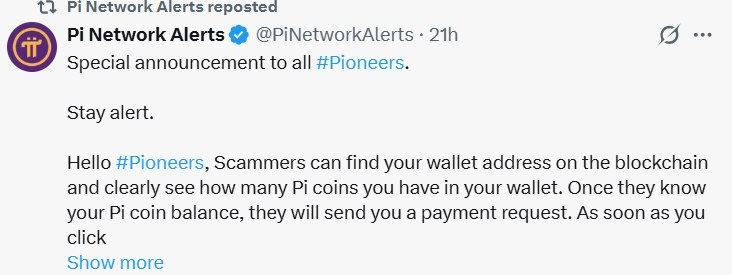
The Pi network, which is the mobile-first Cryptocurrency and web3 blockchain, recently posted a tweet on DEC 30 that the team has warned that scammers are exploiting the Payment request feature to steal Pi tokens from users’ balances. In the Pi network, the wallet balances are publicly visible, and the attackers are targeting the high-balance wallets and sending the payment request to the wallet as an impersonation of official Pi accounts or community moderators.
Once the user approves the payment request, the Tokens will be instantly transferred to the scammers’ account and will be gone forever. No reversal or recovery will be done. The Community reports indicate the scams are widespread, and one scammer’s wallet has received more than 838,000 PI tokens. Overall, more than a million PI tokens have been lost throughout the year. This created a panic situation among the users, and even the experienced users were tricked because the request looked legitimate.
Pi Core Team Denies System Vulnerability, Addresses Market and User Impact
After this incident happened, many users called it a wallet flaw, but the Core team clarified that the problem is from the human approval, not the protocol Flaw. They say that the wallet never sends funds on its own, and the transfer only happens after the user’s approval. This behavior exists in all major Crypto wallets. So to stop this scam, the PI network has disabled all payment requests network-wide. This stops the scams instantly and prevents further user losses. This makes the PI token safe, and it was the fastest way to contain the damage.
The token is currently trading at $0.204 with a market cap of 1.7 billion. The Token has dropped to 10% due to this issue. Recently, the token has updated its ecosystem by adding Standardized KYC to cut the verification backlogs by 50% and speed up mainnet migration for millions of users. Another update is from the testnet DEX, which makes the trading safer and easier by using Pi as the main trading Pair and improving the liquidity. This makes the token regain its momentum, and it has increased by 0.7% in 24 hours.
Highlighted Crypto News:
XDC Network Momentum Test: Will It Break Resistance or Slip Back to Lows?