*This report is jointly produced by Beosin and Footprint Analytics
Preface
This research report is initiated by the Blockchain Security Alliance and co-authored by its members, Beosin and Footprint Analytics, aiming to provide a comprehensive exploration of the global blockchain security landscape in 2025. Through the analysis and assessment of the current state of global blockchain security, the report will reveal the security challenges and threats currently faced, and provide solutions and best practices. Blockchain security and regulation are key issues for the development of the Web3 era. Through the in-depth research and discussion in this report, we can better understand and address these challenges to promote the security and sustainable development of blockchain technology.
1. Overview of the 2025 Web3 Blockchain Security Landscape
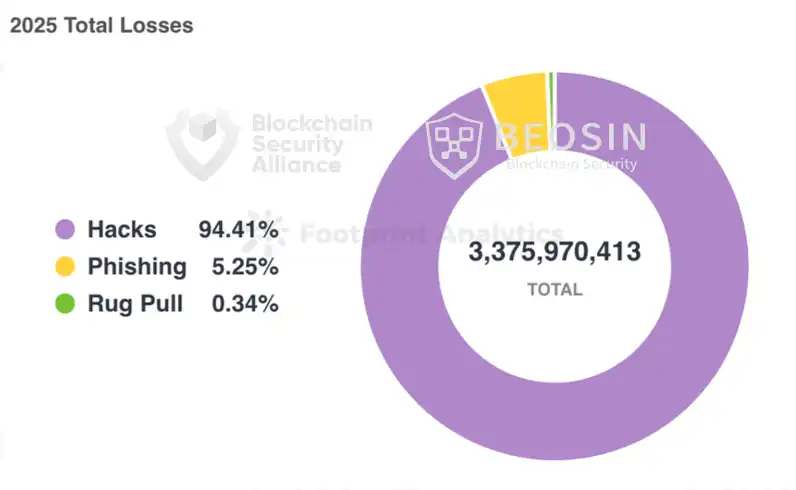
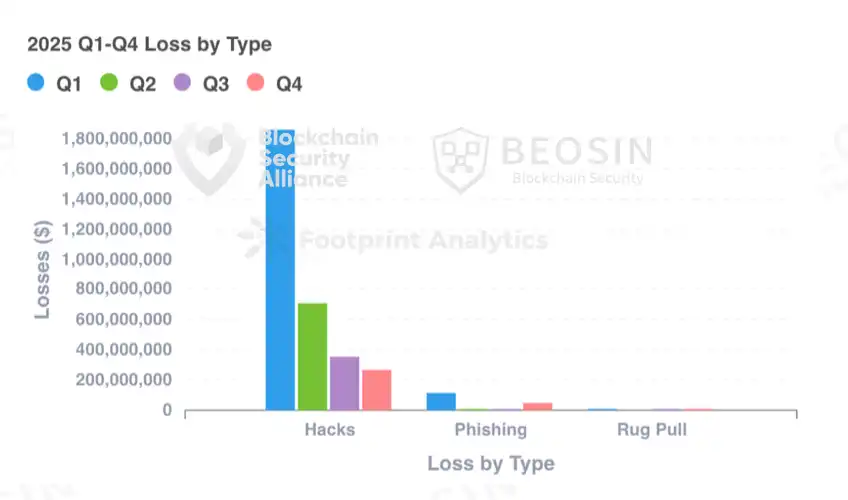
According to monitoring by the Alert platform under blockchain security and compliance technology company Beosin, the total losses in the Web3 field in 2025 due to hacker attacks, phishing scams, and project Rug Pulls reached $3.375 billion. There were 313 major blockchain security incidents, including 191 hacker attack incidents with total losses of approximately $3.187 billion; project Rug Pull incidents with total losses of about $11.5 million; and 113 phishing scams with total losses of approximately $177 million.
Q1 2025 saw the most severe losses, with the vast majority coming from the Bybit hacking incident. The loss amount from hacker attacks decreased quarter by quarter but increased significantly compared to 2024, with a growth rate of 77.85%; Loss amounts from phishing scams and project Rug Pull events decreased significantly compared to 2024, with phishing scam losses decreasing by about 69.15% and Rug Pull losses decreasing by about 92.21%.
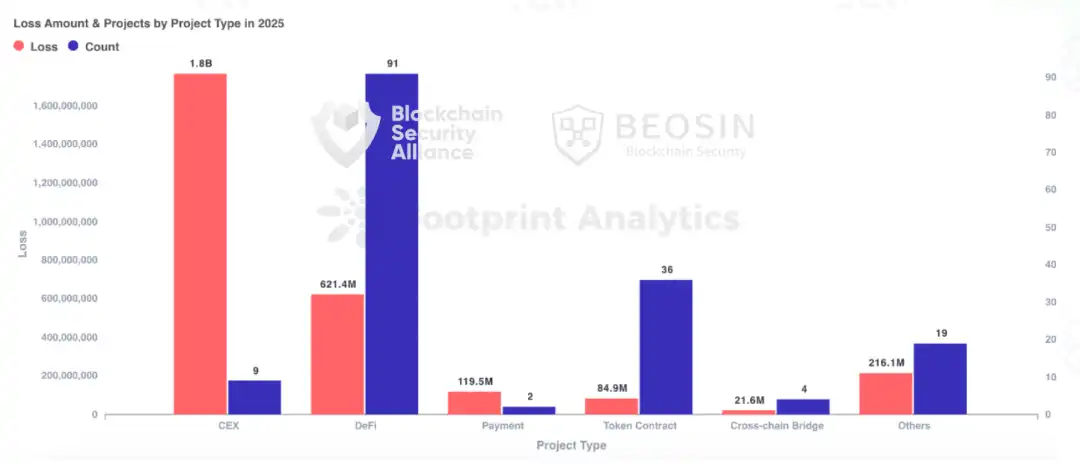
The types of projects attacked in 2025 included DeFi, CEX, public chains, cross-chain bridges, NFT, Memecoin trading platforms, wallets, browsers, third-party code packages, infrastructure, MEV bots, and more. DeFi remained the most frequently attacked project type, with 91 attacks causing losses of about $621 million. CEX was the project type with the highest total loss amount, with 9 attacks causing losses of about $1.765 billion, accounting for 52.30% of the total annual loss.
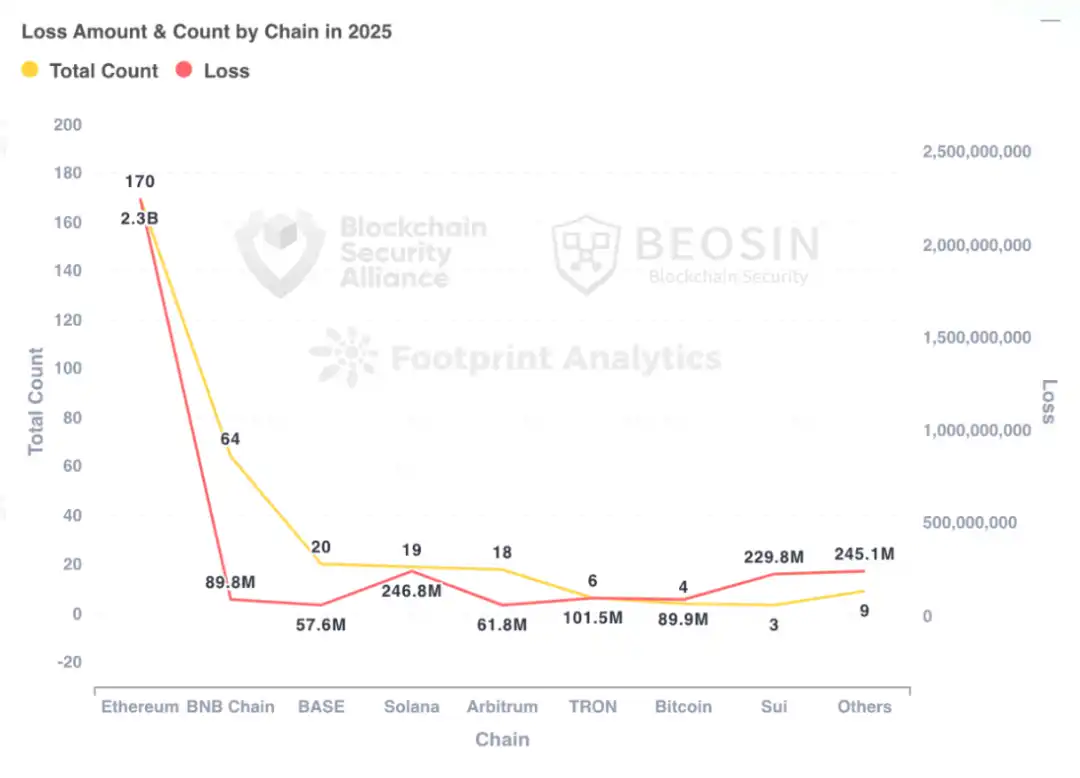
In 2025, Ethereum remained the public chain with the highest loss amount, with 170 security incidents on Ethereum causing approximately $2.254 billion in losses, accounting for 66.79% of the total annual loss.
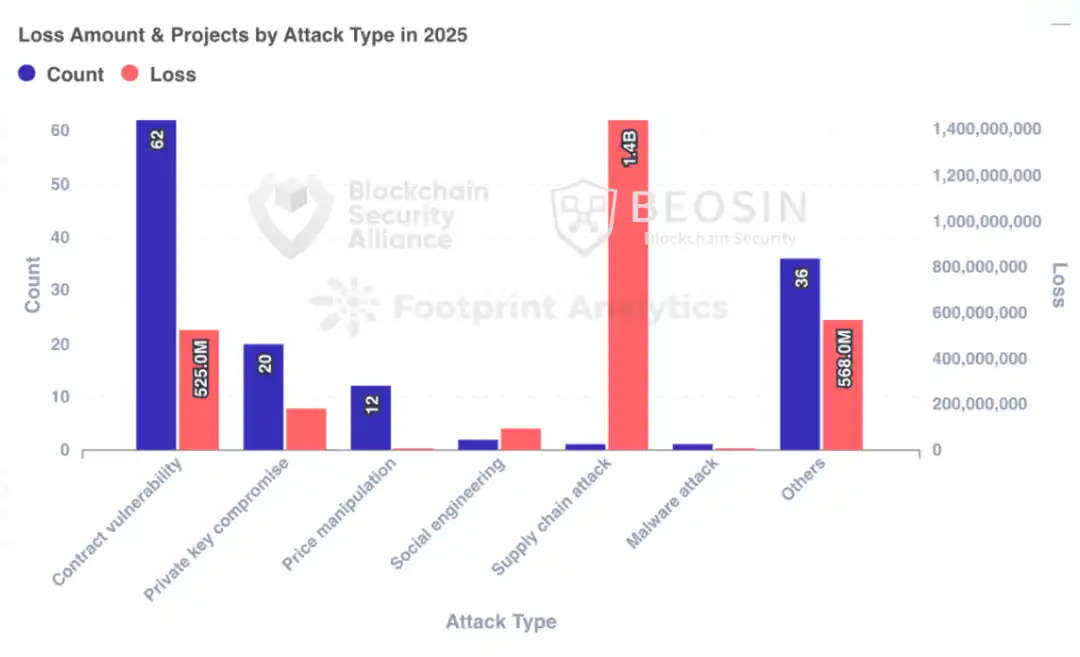
In terms of attack methods, the Bybit incident caused approximately $1.44 billion in losses due to a supply chain attack, accounting for 42.67% of the total loss, making it the attack method causing the most losses. Apart from this, contract vulnerability exploitation was the most frequently occurring attack method, with 62 out of 191 attack incidents stemming from contract vulnerability exploitation, accounting for 32.46%.
2. Top 10 Security Incidents of 2025
In 2025, there were 3 security incidents with losses exceeding $100 million: Bybit ($1.44 billion), Cetus Protocol ($224 million), and Balancer ($116 million), followed by Stream Finance ($93 million), BTC Whale ($91 million), Nobitex ($90 million), Phemex ($70 million), UPCX ($70 million), Ethereum User ($50 million), and Infini ($49.5 million).
Unlike previous years, this year's top 10 security incidents included 2 cases of huge losses by individual users, with the cause being social engineering/phishing attacks. Although this type of attack is not the method causing the largest loss amount, its frequency has been increasing yearly, becoming a major threat to individual users.
*Specific details of the top 10 security incidents can be viewed in the full report.
3. Types of Attacked Projects
Centralized exchanges became the project type with the highest loss amount
In 2025, the project type with the highest losses was centralized exchanges, with 9 attacks on centralized exchanges causing approximately $1.765 billion in losses, accounting for 52.30% of the total loss amount. Among them, the exchange with the largest loss was Bybit, losing about $1.44 billion. Other exchanges with significant losses include Nobitex (loss of about $90 million), Phemex (loss of about $70 million), BtcTurk ($48 million), CoinDCX ($44.2 million), SwissBorg ($41.3 million), and Upbit ($36 million).
DeFi was the most frequently attacked project type, with 91 attacks on DeFi causing losses of approximately $621 million, ranking second in loss amount. Among them, Cetus Protocol was hacked for about $224 million, accounting for 36.07% of DeFi stolen funds, Balancer lost about $116 million, and other DeFi projects with significant losses include Infini (about $49.5 million), GMX (about $40 million), Abracadabra Finance ($13 million), Cork Protocol (about $12 million), Resupply (about $9.6 million), zkLend (about $9.5 million), Ionic (about $8.8 million), and Alex Protocol (about $8.37 million).
4. Loss Amounts by Chain
Ethereum is the chain with the highest loss amount and the most security incidents
As in previous years, Ethereum remains the public chain with the highest loss amount and the most security incidents. 170 security incidents on Ethereum caused approximately $2.254 billion in losses, accounting for 66.79% of the total annual loss.
The public chain with the second highest number of security incidents was BNB Chain, with 64 security incidents causing total losses of approximately $89.83 million. BNB Chain has many on-chain attacks with relatively small loss amounts, but compared to 2024, the number of security incidents and loss amounts have increased significantly, with the loss amount increasing by 110.87%.
Base was the blockchain with the third highest number of security incidents, with a total of 20 security incidents. Solana followed closely with 19 security incidents.
5. Attack Method Analysis
Contract vulnerability exploitation is the most frequently occurring attack method
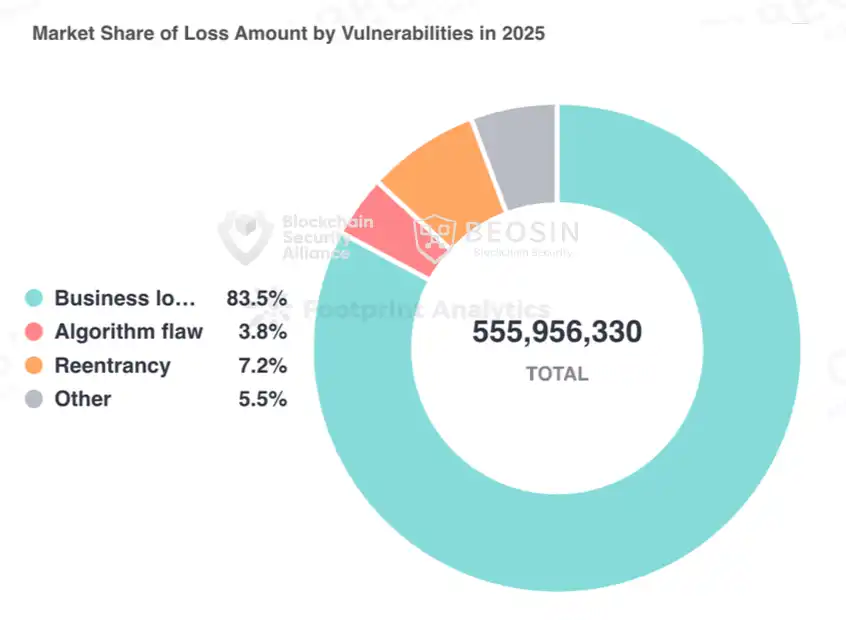
Out of 191 attack incidents, 62 were from contract vulnerability exploitation, accounting for 32.46%, causing total losses of $556 million, making it the attack method with the largest loss amount besides the Bybit supply chain attack.
Breaking down contract vulnerabilities, the vulnerability causing the most losses was: business logic vulnerabilities, with a total loss amount of $464 million. The top three contract vulnerabilities by occurrence were business logic vulnerabilities (53 times), access control vulnerabilities (7 times), and algorithm defects (5 times).
This year, private key leakage incidents totaled 20 times, with total losses of approximately $180 million. The number of occurrences and resulting losses decreased significantly compared to last year. Exchanges, project parties, and users have improved their awareness of private key protection.
6. Analysis of Typical Security Incident Attacks
6.1 Analysis of the Cetus Protocol $224 Million Security Incident
Incident Summary
On May 22, 2025, DEX Cetus Protocol on the Sui ecosystem was attacked. The vulnerability stemmed from an implementation error in the left-shift operation within an open-source library code. Taking one attack transaction (https://suivision.xyz/txblock/DVMG3B2kocLEnVMDuQzTYRgjwuuFSfciawPvXXheB3x?tab=Overview) as an example, the simplified attack steps are:
1. Enable flash loan: The attacker borrows 10 million haSUI via a flash loan.
2. Create liquidity position: Open a new liquidity position with a price range of [300000, 300200].
3. Add liquidity: Only 1 unit of haSUI is used to add liquidity, but an extremely high liquidity value of 10,365,647,984,364,446,732,462,244,378,333,008 is obtained.
4. Remove liquidity: Immediately remove liquidity in multiple transactions to drain the liquidity pool.
5. Repay flash loan: Repay the flash loan and keep about 5.7 million SUI as profit.
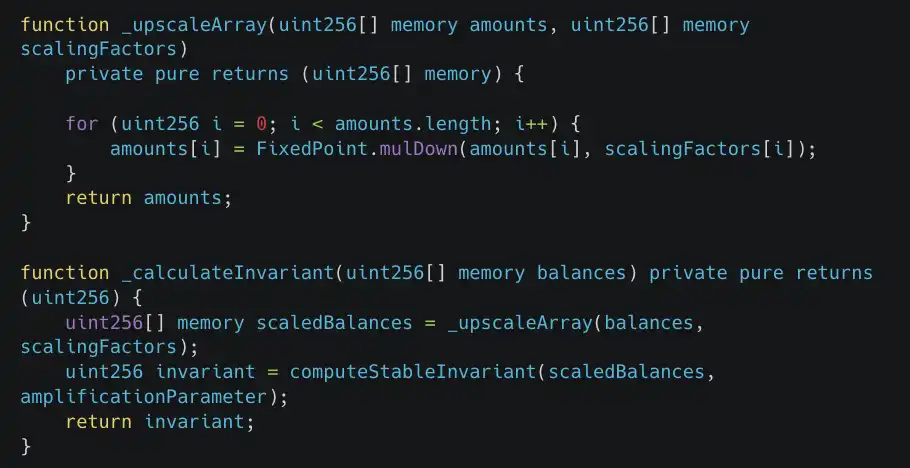
Vulnerability Analysis
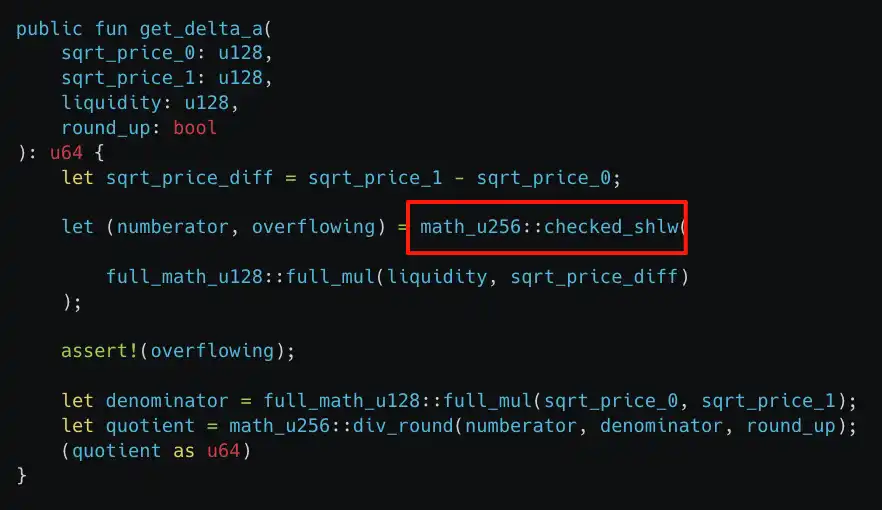
The root cause of this attack lies in the incorrect implementation of `checked_shlw` in the `get_delta_a` function, causing the overflow check to fail. The attacker only needed a small amount of tokens to exchange a large amount of assets from the liquidity pool, thus achieving the attack.
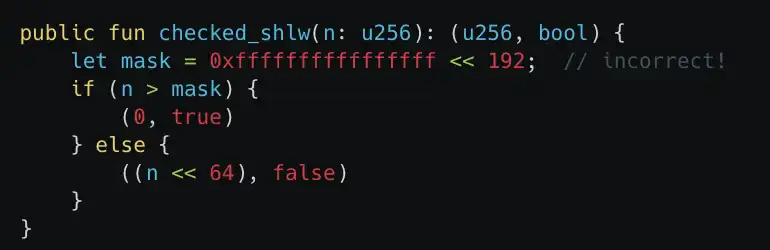
As shown in the figure below, `checked_shlw` is used to determine whether left-shifting a u256 number by 64 bits would cause an overflow. Input values less than `0xffffffffffffffff << 192` would bypass the overflow detection, but the input value might exceed the u256 maximum value (overflow) after being left-shifted by 64 bits, and `checked_shlw` would still output that no overflow occurred (false). This would lead to a severe underestimation of the required token amount in subsequent calculations.
Furthermore, in Move, the safety of integer operations is designed to prevent overflow and underflow, as they can lead to unexpected behavior or vulnerabilities. Specifically: If the result of addition and multiplication is too large for the integer type, it causes the program to abort. Division aborts if the divisor is zero.
The unique aspect of the left shift (<<) is that it does not abort on overflow. This means that even if the number of bits shifted exceeds the storage capacity of the integer type, the program will not terminate, potentially leading to incorrect values or unpredictable behavior.
6.2 Balancer $116 Million Security Incident Analysis
On November 3, 2025, the Balancer v2 protocol was attacked, with multiple projects including its fork protocols losing about $116 million across multiple chains. Taking the attacker's transaction on Ethereum as an example: 0x6ed07db1a9fe5c0794d44cd36081d6a6df103fab868cdd75d581e3bd23bc9742
1. The attacker first initiated an attack transaction through the batch swap function, using BPT to swap out a large amount of the pool's liquidity tokens, causing the pool's liquidity token reserves to become very low.
2. The attacker then began swapping the liquidity tokens (osETH/WETH).
3. Then, the liquidity tokens were swapped back to BPT tokens, and the above operations were repeated across multiple pools.
4. Finally, a withdrawal was made to realize profits.
Vulnerability Analysis
ComposableStablePools use Curve's StableSwap invariant formula to maintain price stability between similar assets. However, scaling operations performed during the invariant calculation introduce errors.
The `mulDown` function performs integer division with rounding down. This precision error propagates into the calculation of the invariant, causing the calculated value to be abnormally low, thus creating profit opportunities for attackers.
7. Anti-Money Laundering Typical Case Analysis
7.1 US Sanctions Drug Trafficking Group Led by Ryan James Wedding
According to information disclosed by the US Treasury Department, Ryan James Wedding and his team smuggled tons of cocaine through Colombia and Mexico to the US and Canada. The criminal organization used cryptocurrency for money laundering to clean huge amounts of illegal wealth.
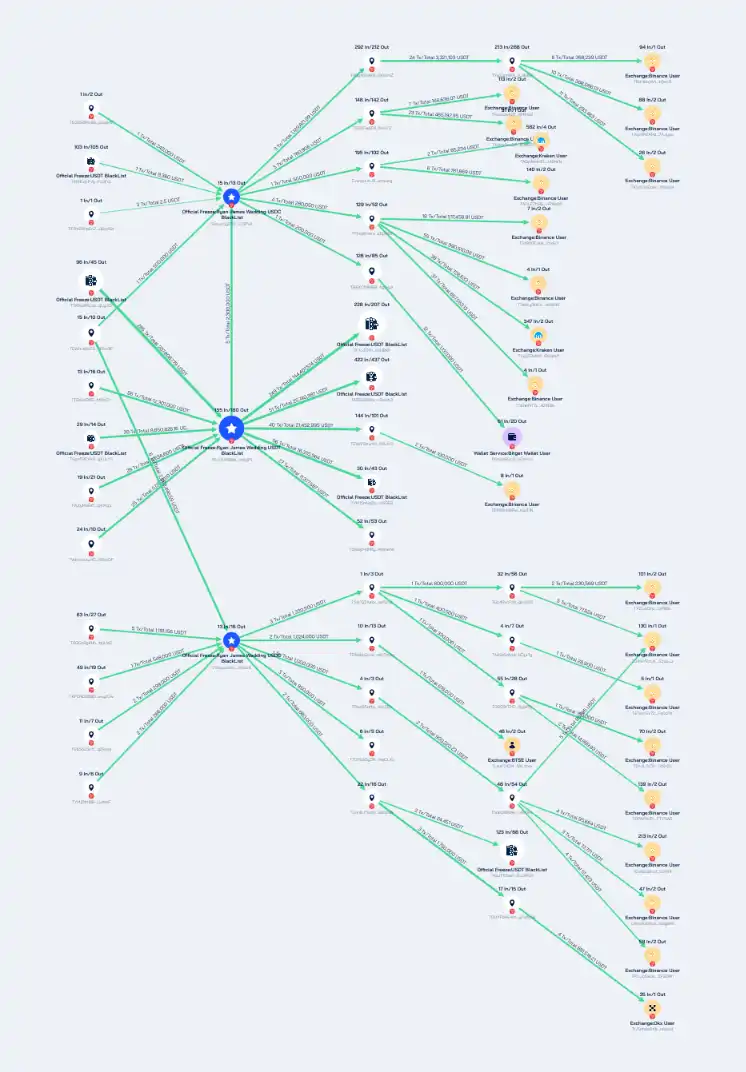
Using Beosin Trace, the on-chain tracking and investigation tool under Beosin, an analysis was conducted on cryptocurrency addresses associated with Wedding's drug trafficking group. The analysis results are as follows:
The 3 addresses held by Wedding, TAoLw5yD5XUoHWeBZRSZ1ExK9HMv2CiPvP, TVNyvx2astt2AB1 Us67ENjfMZeEXZeiuu6, and TPJ1JNX98MJpHueBJeF5SVSg85z8mYg1P1, handled a total of 266,761,784.24 USDT. Some assets have been frozen by Tether officially, but most assets have been laundered through addresses with high-frequency transactions and multi-level transfers, and deposited into platforms such as Binance, OKX, Kraken, and BTSE.
His accomplice Sokolovski holds addresses on multiple blockchain networks (BTC, ETH, Solana, TRON, BNB Beacon Chain). The fund flow analysis results can be viewed in the full report.
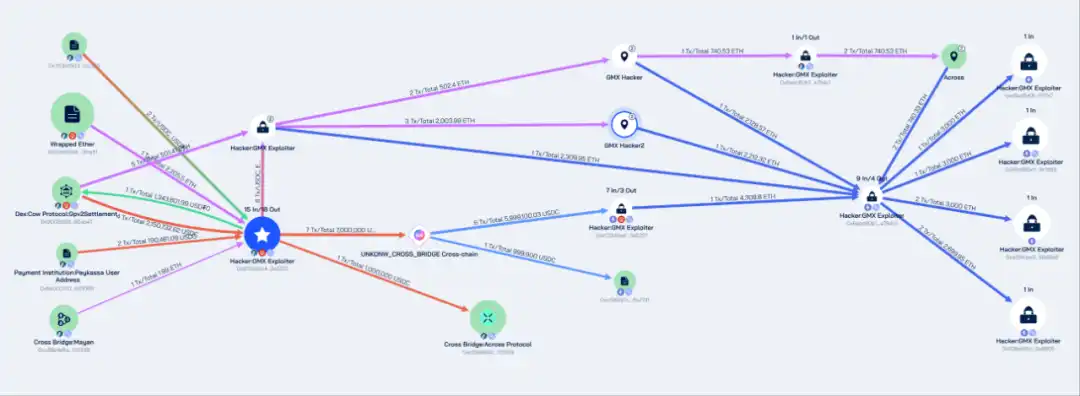
7.2 GMX $40 Million Fund Theft Case
On July 10, 2025, GMX was attacked due to a reentrancy vulnerability, with the hacker profiting about $42 million. Beosin Trace tracked the stolen funds and found: The attacker's address 0x7d3bd50336f64b7a473c51f54e7f0bd6771cc355 exchanged various stablecoins and altcoins for ETH and USDC through DEX protocols after profiting, and transferred the stolen assets to the Ethereum network through multiple cross-chain protocols.
Subsequently, GMX stolen assets worth approximately $32 million in ETH were stored in the following 4 Ethereum network addresses:
0xe9ad5a0f2697a3cf75ffa7328bda93dbaef7f7e7
0x69c965e164fa60e37a851aa5cd82b13ae39c1d95
0xa33fcbe3b84fb8393690d1e994b6a6adc256d8a3
0x639cd2fc24ec06be64aaf94eb89392bea98a6605
Approximately $10 million in assets were stored at address 0xdf3340a436c27655ba62f8281565c9925c3a5221 on the Arbitrum network.
The fund laundering path in this incident is very typical. The hacker used DeFi protocols, cross-chain bridges, and other methods to obfuscate and hide the path of the funds, to evade tracking and freezing by regulatory agencies and law enforcement departments.
8. Summary of the 2025 Web3 Blockchain Security Landscape
In 2025, the monetary losses caused by phishing scams and project Rug Pulls decreased significantly compared to 2024. However, hacker attacks occurred frequently, with losses exceeding $3.1 billion, with the project type suffering the highest losses still being exchanges. Security incidents related to private key leakage decreased. The main reasons for this change include:
After last year's rampant hacker activities, the entire Web3 ecosystem paid more attention to security this year. Efforts were made by all parties, from project teams to security companies, in various aspects, such as internal security operations, real-time on-chain monitoring, increased focus on security audits, actively learning from past contract vulnerability exploitation incidents, and continuously strengthening security awareness in private key custody and project operation security. As it became increasingly difficult to exploit contract vulnerabilities and steal private keys, hackers began to use other means, such as supply chain attacks and front-end vulnerabilities, to trick users into transferring assets to addresses controlled by hackers.
Furthermore, with the integration of the crypto market and traditional markets, attack targets are no longer limited to DeFi, cross-chain bridges, exchanges, etc., but have shifted to various targets such as payment platforms, gambling platforms, crypto service providers, infrastructure, development tools, and MEV bots. The focus of attacks has also shifted to more complex protocol logic flaws.
For individual users, social engineering/phishing attacks and potential violent coercion have become major threats to personal asset security. Currently, many phishing attacks involve small amounts, and the victims are individual users, so they are not publicly reported or recorded. Their loss data is often underestimated, but users should raise their awareness of preventing such attacks. Kidnapping and other physically coercive methods targeting crypto users have appeared multiple times this year. Users need to protect their personal identity information and minimize the public exposure of crypto assets as much as possible.
Overall, Web3 security in 2025 still faces severe challenges, and project teams and individual users must not be careless. In the future, supply chain security may become the top priority of Web3 security. How to continuously protect various infrastructure service providers in the industry and monitor and alert threats in the supply chain is a major challenge that all parties in the industry need to solve together. And AI-driven social engineering/phishing attacks are likely to continue to increase, which requires building a multi-layered, real-time, dynamic defense system from personal awareness to technical barriers, and then to community collaboration to respond.