Written by: nvk
Compiled by: Saoirse, Foresight News
TL;DR
- Bitcoin does not use encryption; it uses digital signatures. The vast majority of articles get this wrong, and the distinction is crucial.
- Quantum computers cannot crack Bitcoin in 9 minutes. This description refers to a theoretical circuit; the machine itself does not exist and will not appear for at least a decade.
- Quantum mining is physically impossible. It requires more energy than the total output of the sun.
- Bitcoin can be upgraded—it has been done successfully before (SegWit, Taproot), and work has already begun (BIP-360). But the community needs to speed up.
- The real reason for upgrading is not the quantum threat, but that classical mathematics has broken countless cryptographic systems, and secp256k1 is likely next. Quantum computers have not broken any cryptographic system to date.
- There is a real hidden danger: the public keys of approximately 6.26 million Bitcoins have been exposed. This is not a reason for panic, but it is worth preparing for in advance.
Core Narrative
To summarize everything I'm about to say in one sentence:
The quantum threat to Bitcoin is real but distant; media coverage is generally exaggerated and inaccurate; and the most dangerous thing is not quantum computers, but complacency disguised as panic or indifference.
Both those who shout "Bitcoin is finished" and those who claim "everything is fine, don't worry" are wrong. Seeing the truth requires accepting two things simultaneously:
- Bitcoin faces no imminent quantum threat at present, and the actual threat is likely much farther away than clickbait headlines suggest.
- But the Bitcoin community should still prepare in advance because the upgrade process itself will take years.
This is not a reason to panic, but a reason to act.
Below, I explain this clearly with data and logic.
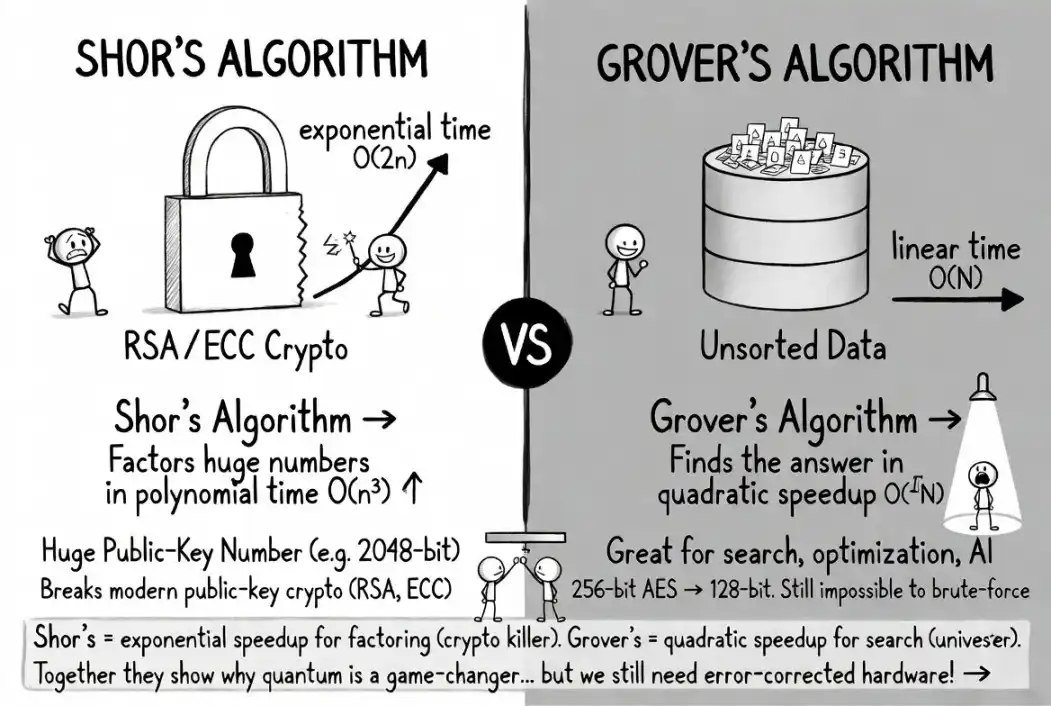
This image compares the two core quantum algorithms: Shor's algorithm (left), the 'cryptography killer' that can exponentially speed up integer factorization and directly break public-key cryptography like RSA/ECC, and Grover's algorithm (right), a general quantum accelerator that provides quadratic speedup for unstructured search. Both highlight the disruptive potential of quantum computing, but are currently limited by error-correction hardware and cannot be deployed at scale.
Media Formula: Clickbait is the Biggest Hidden Danger
The same cycle repeats every few months:
- A quantum computing lab publishes a rigorous research paper with many caveats.
- Tech media immediately writes: "Quantum Computer Cracks Bitcoin in 9 Minutes!"
- Crypto Twitter simplifies it to: "Bitcoin is dead."
- Your friends and relatives message you asking if they should sell quickly.
- But the original paper never said that.
In March 2026, Google's Quantum AI team published a paper stating that the number of physical qubits required to crack Bitcoin's elliptic curve cryptography could be reduced to under 500,000, a 20-fold improvement over previous estimates. This is indeed important research. Google was very cautious, did not disclose the actual attack circuit, and only released a zero-knowledge proof.
But the paper never said: Bitcoin can be cracked now, there is a clear timeline, or everyone should panic.
Yet the titles read: "Breaks Bitcoin in 9 minutes."
CoinMarketCap once published an article titled "Will AI-Accelerated Quantum Computing Destroy Bitcoin in 2026?", with the body explaining that the answer is almost certainly "no." This is a classic formula: use a sensational headline for clicks, keep the text cautious for accuracy. But 59% of shared links are never clicked—for most people, the headline *is* the information.
As one saying aptly puts it: "The market prices risk extremely fast. You can't steal something that becomes worthless the moment you get it." If quantum computers were truly about to颠覆 everything, Google's own stock price (which also uses similar cryptography) would have already crashed. But Google's stock is stable.
Conclusion: The headline is the real misinformation. The research itself is real and worth understanding. Let's look at it seriously.
What Quantum Computers Really Threaten, and What They Don't
Biggest Misconception: "Encryption"
Almost every article about quantum and Bitcoin uses the word "encryption." This is wrong, and the error affects the entire picture.
Bitcoin does not protect assets with encryption, but with digital signatures (ECDSA, and later Schnorr via Taproot). The blockchain itself is public; all transaction data is forever visible to everyone. There is nothing to "decrypt."
As Adam Back, inventor of Hashcash (cited in the Bitcoin whitepaper), said: "Encryption implies data is hidden and can be decrypted. Bitcoin's security model is based on signatures, used to prove ownership without exposing the private key."
This is not nitpicking. It means the most pressing quantum threat of "harvest now, decrypt later" largely does not apply to Bitcoin asset security. There is no encrypted data to harvest; the public keys exposed are already public on the chain.
Two Quantum Algorithms: One is a Real Threat, One is Negligible
- Shor's Algorithm (Real Threat): Provides exponential speedup for the mathematical problems underlying digital signatures. It can derive the private key from the public key and forge transaction signatures. This is the one to worry about.
- Grover's Algorithm (Not a Threat): Only provides quadratic speedup for hash functions like SHA-256. It sounds scary, but a simple calculation shows it's completely unrealistic.
A 2025 paper, "Kardashev-Scale Quantum Computing and Bitcoin Mining," calculated that under Bitcoin's current difficulty, quantum mining would require:
- Approximately 10^23 physical qubits (currently only about 1500 exist globally)
- Approximately 10^25 watts of energy (the sun's total output is about 3.8×10^26 watts)
Using a quantum computer to mine Bitcoin would require energy consumption roughly equivalent to 3% of the sun's total output. Humanity is currently a ~0.73 Kardashev scale civilization. Quantum mining would require energy on a scale only a Type II civilization could manage, which is far beyond current human capabilities and physically almost impossible.
(Note: Kardashev civilization scale: Type I: Can utilize all energy of a planet (Earth); Type II: Can utilize the total energy output of a star (Sun))
For comparison: Even under the most ideal design, a quantum miner's hashrate would be only about 13.8 GH/s; an ordinary Antminer S21 can achieve 200 TH/s. Traditional ASIC miners are about 14,500 times faster than quantum miners.
In short, quantum mining is not feasible. Not now, not in 50 years, maybe never. If someone says quantum computers can "break Bitcoin mining," they are confusing two completely different algorithms.
8 Common Claims, 7.5 of Which Are Wrong
Claim 1: "Once quantum computers arrive, all Bitcoin will be stolen overnight"
Fact: Only Bitcoin whose public keys are already exposed is at risk. Modern Bitcoin addresses (P2PKH, P2SH, SegWit) do not reveal the public key until you initiate a transfer. As long as you never reuse an address and have never sent funds *from* that address, your public key will not appear on the blockchain.
Breakdown:
- Tier A (Directly at Risk): ~1.7 million BTC in legacy P2PK format, public key fully exposed.
- Tier B (At Risk but Fixable): ~5.2 million BTC in reused addresses and Taproot addresses, users can migrate to avoid risk.
- Tier C (Temporarily Exposed): Public key temporarily exposed for ~10 minutes while a transaction waits in the mempool to be confirmed.
According to Chaincode Labs estimates, a total of ~6.26 million BTC are at risk due to public key exposure, about 30%–35% of the total supply. A significant amount, but far from "all Bitcoin."
Claim 2: "Satoshi's coins will be stolen, causing a crash to zero"
Half-right, half-wrong: Satoshi's ~1.1 million BTC are in P2PK format, public keys fully exposed, and are indeed high-risk assets. But:
- The quantum computer capable of cracking these private keys does not exist yet.
- Nations with early quantum technology would prioritize intelligence and military systems, not stage a "public spectacle of stealing Bitcoin" (Quantum Canary Research Group).
- Scaling from the current ~1500 qubits to hundreds of thousands will require years of engineering breakthroughs, and progress is highly uncertain.
Claim 3: "Bitcoin cannot upgrade — it's too slow, governance is chaotic"
Incorrect, though not without some basis. Bitcoin has successfully executed several major upgrades in its history:
- Segregated Witness (SegWit, 2015–2017): Highly controversial, nearly failed, led directly to the Bitcoin Cash fork, but ultimately succeeded.
- Taproot (2018–2021): Smooth rollout, took about 3.5 years from proposal to mainnet activation.
The leading quantum-resistant proposal, BIP-360, was formally added to the Bitcoin BIP library in early 2026, adding a new bc1z address type and removing the quantum-vulnerable key path spending logic from Taproot. It is currently a draft, and the testnet is running the Dilithium post-quantum signature instruction set.
BIP-360 co-author Ethan Heilman estimates a full upgrade cycle of about 7 years: 2.5 years development & review, 0.5 years activation, 4 years ecosystem migration. He admits: "This is a rough estimate; no one can give a definitive timeline."
Objective conclusion: Bitcoin *can* upgrade, and the process has started, but it's still in the early stages and needs to accelerate. Claiming "upgrading is impossible" is wrong, but claiming "the upgrade is complete" is equally untrue.
Claim 4: "We only have 3–5 years left"
Most likely untrue, but not something to be completely complacent about. Expert estimates vary wildly:
- Adam Back (Hashcash inventor, cited in Bitcoin whitepaper): 20–40 years
- Jensen Huang (NVIDIA CEO): Practical quantum computers still need 15–30 years
- Scott Aaronson (UT Austin, quantum computing authority): Refuses to give a timeline, says cracking RSA might require "hundreds of billions of dollars in investment"
- Craig Gidney (Google Quantum AI): 10% probability by 2030; also believes that under current conditions, qubit requirements are unlikely to see another 10x optimization, the optimization curve may be flattening.
- Survey of 26 quantum security experts: 28%–49% probability of risk within 10 years
- ARK Invest: "A long-term risk, not imminent"
Notably, Google's Willow chip broke the quantum error correction threshold in late 2024. This means that for each level of increased error correction code distance, the logical error rate decreases by a fixed factor (2.14 for Willow). This error suppression improves exponentially, but the actual scaling speed depends entirely on hardware—it could be logarithmic, linear, or extremely slow. Breaking the threshold only means scaling is feasible, not that it will be fast, easy, or inevitable.
Furthermore, Google's March 2026 paper did not公开 the actual attack circuit, only a zero-knowledge proof. Scott Aaronson also warns that future researchers might stop publishing resource estimates for breaking cryptography. Therefore, we might not get much advance warning of a "quantum doomsday."
Even so, building a computer with hundreds of thousands of fault-tolerant qubits remains a massive engineering challenge. The most advanced quantum computers today cannot factor numbers larger than 13 digits, while cracking Bitcoin's cryptography is equivalent to factoring a ~1300-digit number. This gap cannot be closed overnight, but the technological trend deserves attention, not dismissal.
Claims 5–8: Quick Clarifications
"Quantum computing will destroy mining"
Wrong. Energy requirements are near the sun's total output, see Part 2.
"Harvest data now, decrypt later"
Does not apply to stealing assets (the blockchain is public anyway), only a minor risk to privacy.
"Google said it cracks Bitcoin in 9 minutes"
Google referred to a theoretical circuit runtime of ~9 minutes on a non-existent 500,000-qubit machine. Google itself has explicitly warned against such panic and withheld the attack circuit details.
"Post-quantum cryptography isn't mature yet"
NIST has standardized algorithms like ML-KEM, ML-DSA, SLH-DSA. The algorithms themselves are mature; the difficulty lies in deploying them within the Bitcoin system, not inventing them from scratch.
My Five Real Concerns
A debunking article that denies everything loses credibility. Here are five issues that genuinely worry me:
- Estimates for the number of qubits needed to break cryptography continue to fall, though this trend may be slowing. In 2012, breaking crypto was estimated to require 1 billion qubits; by 2019, it was 20 million; by 2025, it was below 1 million. In early 2026, Oratomic claimed that using a neutral atom architecture, only 10,000 physical qubits would be needed. However, all nine authors of that study are Oratomic shareholders, and their estimate relies on an unverified 101:1 physical-to-logical qubit ratio (historical ratios are closer to 10000:1). Also, the task that takes "9 minutes" on Google's superconducting architecture would take 10^264 days on neutral atom hardware—completely different devices, vastly different speeds. Gidney himself says the algorithm optimization curve may be plateauing. Still, no one knows when the inflection point between "qubits needed" and "qubits available" will arrive. The most objective conclusion is: there is great uncertainty.
- The scope of exposed public keys is expanding, not shrinking. Bitcoin's newest, most promoted address format, Taproot, publicly reveals the tweaked public key on-chain, giving quantum attackers an unlimited offline cracking window. Bitcoin's latest upgrade ironically reduced quantum resistance, a point worth pondering. The problem isn't just on-chain addresses: Lightning Network channels, hardware wallet connections, multisig schemes, and extended public key (xpub) sharing services are designed to disseminate public keys. In a world with Cryptographically Relevant Quantum Computers (CRQCs), "protecting public key privacy" is unrealistic when the entire system is built around sharing them. BIP-360 is just the first step, far from a complete solution.
- Bitcoin's governance process is slow, but there is a time window. The Bitcoin base layer protocol hasn't activated a soft fork in over four years since November 2021, a long period of stagnation. Google plans to complete its own quantum-resistant migration by 2029, while Bitcoin's most optimistic estimate is around 2033. Given that practical密码-cracking quantum computers are likely still far off (most reliable predictions point to the 2040s, or may never materialize), this is not an immediate crisis, but绝不能 justify complacency. The earlier preparations start, the more从容 the process will be later.
- Satoshi's coins are an unsolvable game theory problem. ~1.1 million BTC are in P2PK addresses. Since no one holds the corresponding private keys (or Satoshi is gone), these assets can never be migrated. Whether left alone, frozen, or destroyed, the consequences are severe; there is no perfect solution.
- The blockchain is a permanently locked target list for attack. All exposed public keys are recorded forever and for free. State actors can start preparing now and wait patiently. Defense requires proactive coordination; attack only requires patience.
These are real challenges, but there's another side to consider.
Why the Quantum Threat Might Be Extremely Distant, or Never Arrive
Several serious physicists and mathematicians (not fringe figures) argue that fault-tolerant quantum computing at a scale needed for密码 cracking might face fundamental physical obstacles, not just engineering challenges:
- Leonid Levin (Boston University, co-discoverer of NP-completeness): "Quantum amplitudes need to be precise to hundreds of decimal places, but we have never found any physical law that holds beyond about a dozen decimals." If nature doesn't allow precision beyond ~12 decimals, the entire field of quantum computing hits a physical ceiling.
- Michel Dyakonov (University of Montpellier, theoretical physicist): A 1000-qubit system requires controlling ~10^300 continuous parameters simultaneously, a number exceeding the total number of subatomic particles in the universe. His conclusion: "Impossible. Forever impossible."
- Gil Kalai (Hebrew University, mathematician): Quantum noise has irreducible correlated effects that worsen with system complexity, making large-scale quantum error correction fundamentally impossible. His conjecture remains unproven after 20 years, but some experimental predictions have shown mixed results.
- Tim Palmer (Oxford University, physicist): His resonant quantum mechanics model predicts a hard limit of ~1000 qubits for quantum entanglement, far below what's needed for密码 cracking.
These are not marginal views. Existing evidence also strongly suggests that quantum computing threatening cryptography is either much harder in reality than in theory, or fundamentally impossible due to unknown laws of the physical world. The analogy to self-driving cars is apt: demos look good, attract huge investment, but have been "five years away" for over a decade.
The media's default assumption that "quantum computers will eventually break crypto, it's just a matter of time" is a conclusion driven by hype cycles, not evidence.
The Core Reason for Upgrading Has Nothing to Do with Quantum
Here's a key fact rarely mentioned (thanks to @reardencode for pointing this out):
- Cryptographic systems broken by quantum computers to date: 0;
- Cryptographic systems broken by classical mathematics: Countless.
DES, MD5, SHA-1, RC4, SIKE, the Enigma machine... all fell to clever mathematical analysis, not quantum hardware. SIKE was a NIST post-quantum finalist, broken in one hour on a laptop by a single researcher in 2022. Classical cryptanalysis has been breaking supposedly secure systems since the dawn of cryptography.
Bitcoin's secp256k1 elliptic curve could fail at any moment due to a mathematical breakthrough, no quantum computer needed. Just one brilliant number theorist making a new advance on the discrete logarithm problem. It hasn't happened yet, but the history of cryptography is a history of "proven secure" systems being broken.
*This* is the real reason Bitcoin should adopt alternative cryptography: Not because quantum computers are coming—they might never arrive—but because relying on a single cryptographic assumption for a multi-trillion dollar network is a risk that rigorous engineering must proactively guard against.
Ironically, the panic炒作 around quantum threats obscures this quieter, more real vulnerability. Also ironically, the preparations made for the quantum threat (BIP-360, post-quantum signatures, hash-based alternatives) also protect against classical cryptanalysis. People are doing the right thing for the wrong reason—which is fine, as long as it gets done.
What Should You Actually Do?
If you hold Bitcoin:
- Don't panic. The threat is real but distant; you have plenty of time.
- Stop reusing addresses. Every reuse exposes a public key. Use a new address for every receipt.
- Follow the progress of BIP-360. Migrate assets promptly once quantum-resistant addresses are available.
- For long-term storage, keep funds in addresses that have never sent transactions, keeping the public key hidden.
- Don't be led by headlines; read the original papers. They are more interesting and less scary than the reports.
If you are a Bitcoin developer:
- BIP-360 needs more reviewers. The testnet is running; the code needs scrutiny.
- The 7-year upgrade cycle needs compression. Every year delayed shrinks the safety buffer.
- Start governance discussions about old unspent transaction outputs (UTXOs). Satoshi's Bitcoin won't protect itself; the community needs a plan.
If you just saw a sensational headline: Remember, 59% of shared links are never clicked. Headlines are for煽动情绪; papers are for思考. Read the source.
Conclusion
The quantum threat to Bitcoin is not black and white; it exists in a middle ground. On one end, "Bitcoin is finished, sell now," on the other, "Quantum is a scam, zero risk"—both extremes are wrong.
The truth lies in the rational, feasible middle: Bitcoin faces a clear engineering challenge, the parameters are known, R&D is underway, time is tight but manageable—provided the community maintains a reasonable sense of urgency.
The most dangerous thing is not the quantum computer, but the舆论循环 oscillating between panic and indifference, preventing rational engagement with a problem that is fundamentally solvable.
Bitcoin has survived the block size wars, exchange hacks, regulatory attacks, and its founder's disappearance. It can survive the quantum era too. But only if the community starts preparing steadily now—without panic, without complacency—with the robust engineering mindset that made Bitcoin strong in the first place.
The house is not on fire, and it may never catch fire from the direction everyone fears. But cryptographic assumptions never hold forever. The best time to reinforce the cryptographic foundations is always before the crisis, not after.
Bitcoin has always been built by people preparing for threats that haven't materialized yet. That's not paranoia; that's engineering.
References: This article draws on 66 research documents from two major thematic wikis, covering quantum computing resource estimates, Bitcoin vulnerability analysis, debunking psychology, and content dissemination mechanisms. Key sources include Google Quantum AI Lab (2026), the "Kardashev-Scale Quantum Mining" paper (2025), BIP-360 proposal documentation, Berger and Milkman research (2012), the "2020 Debunking Handbook," and commentary from practitioners like Tim Urban, Dan Lu, and patio11. The full wiki is open for peer review.