Kentucky is under scrutiny ahead of its planned passage of a key crypto legislation that would ban self-custody wallets.
According to the Bitcoin Policy Institute, a research and advocacy group, Kentucky’s HB 380 amendment would harm residents. The firm noted,
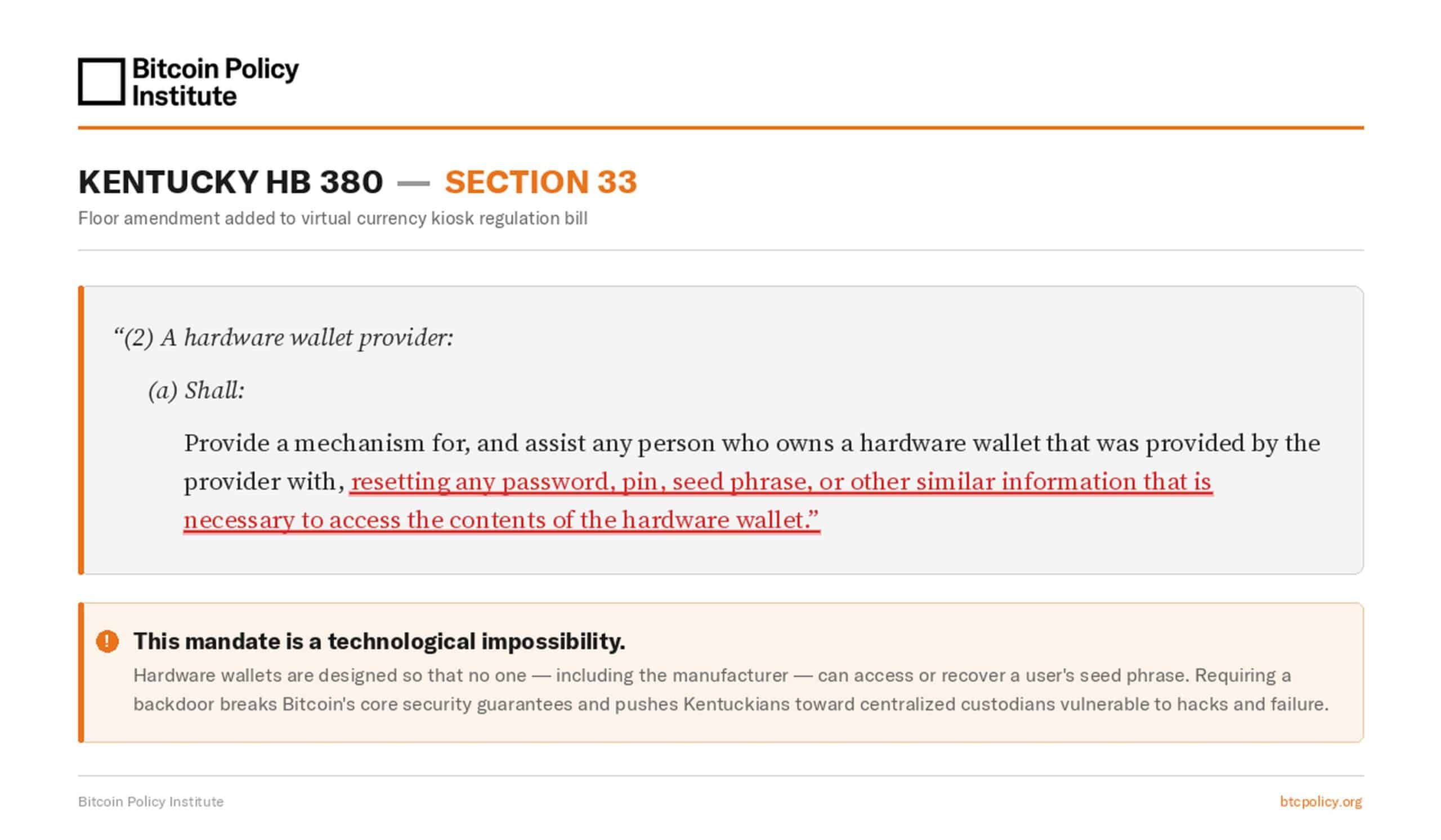
BPI has just learned of an amendment buried in Kentucky HB 380 that would require hardware wallet providers to reset users’ seed phrases on request. This would effectively outlaw self-custody in Kentucky.
Kentucky crypto plans
The HB 380 is an amendment to the 77-page virtual currency kiosk legislation, part of a broader effort to regulate crypto ATMs, especially those that facilitate BTC transfers.
It was a last-minute amendment added in January. It requires hardware providers to be able to reset and recover users’ hardware wallet passwords and seed phrases, something BPI called ‘technologically impossible.’
The mandate is technologically impossible for non-custodial wallets. Requiring a backdoor for seed phrase recovery breaks Bitcoin’s fundamental security guarantees and pushes users toward centralized custodians that are vulnerable to hacks and failures.
The advocacy group wrote to the Kentucky Senate, informing it of the harmful nature of the amendment’s language. It added that the legislators should “protect Kentucky constituents’ right to secure their property.”
However, one analyst noted that ‘commercial hardware wallets’ are vulnerable to government overreach because their parent firms are legal entities operating in different jurisdictions.
Race for strategic Bitcoin reserve
Last year, at the state level, the race for the strategic Bitcoin reserve (SBR) became hot. But, as of 2026, only a handful of states in the U.S. have managed to codify the plans into law. Currently, only seven states have approved an SBR, including Arizona, Texas, and New Mexico.
At the federal level, however, there’s been little commitment or update on whether the U.S. SBR will be established. Even so, the U.S. now holds 328,272 BTC, about 1.5% of the total supply.
This was nearly half of the total 650,296 BTC held by governments, making the U.S. the top holder, followed by China at 190,000 BTC and the UK at 61,245 BTC.
Final Summary
- The Bitcoin Policy Institute pressed the Kentucky Senate to reconsider its recent amendment on crypto ATM rules to safeguard self-custody.
- There are about 7 U.S. states with approved strategic BTC reserve frameworks.