For years, crypto fraud was linked to hackers stealing funds that seemed to vanish on the blockchain. Now, that perception is changing. Three countries have joined forces to stop scams in real time.
Called Operation Atlantic, the initiative brings together the U.S. Secret Service, the UK’s National Crime Agency (NCA), and Canadian authorities.
Instead of only tracing stolen funds after a crime, the operation aims to detect and prevent scams before money is taken.
Main focus of Operation Atlantic
The main target is “approval phishing.” In this scam, victims are tricked into signing a transaction that quietly permits attackers to access their crypto wallets.
By working with private blockchain firms and analyzing real-time data, investigators are now trying to spot risky wallet activity. This marks a shift from reactive investigations to proactive prevention.
Stressing the seriousness of the situation, Brent Daniels, Deputy Assistant Director for the U.S. Secret Service’s Office of Field Operations, said,
Approval phishing and investment scams cost victims millions in financial loss each year.
In response to the rising threat of such crimes, Paul Foster, Deputy Director of Cyber at the UK’s National Crime Agency, added,
Criminals operate across borders, so our response must do the same.
What will the investigators do?
In this effort, authorities will work closely with crypto exchanges and Virtual Asset Service Providers (VASPs) to monitor suspicious transaction patterns.
When they identify a wallet at risk, investigators will contact the potential victim by phone or email before scammers complete the fraud.
Additionally, the other focus is “pig butchering” scams, a long-term social engineering scheme where criminals slowly build trust with victims.
After gaining confidence, scammers trick victims into signing transactions that grant access to their crypto wallets through malicious smart contracts.
To avoid confusion, while pig butchering refers to the broader manipulation strategy, approval phishing is the mechanism that allows scammers to actually drain funds once trust has been established.
Other such initiatives
That said, the initiative also builds on Project Atlas, a 2024 Canadian-led operation that targeted international crypto investment fraud networks.
Remarking on which, Detective Superintendent Jennifer Spurrell, Director of the Financial Crimes Services Bureau at the Ontario Provincial Police, noted,
Project Atlas demonstrated the power of coordinated disruption....As fraud becomes increasingly global, this level of collaboration is essential.
Concerning data sets on rising crypto frauds
Operation Atlantic shows that law enforcement is becoming faster and more coordinated, but crypto fraud still remains a major challenge.
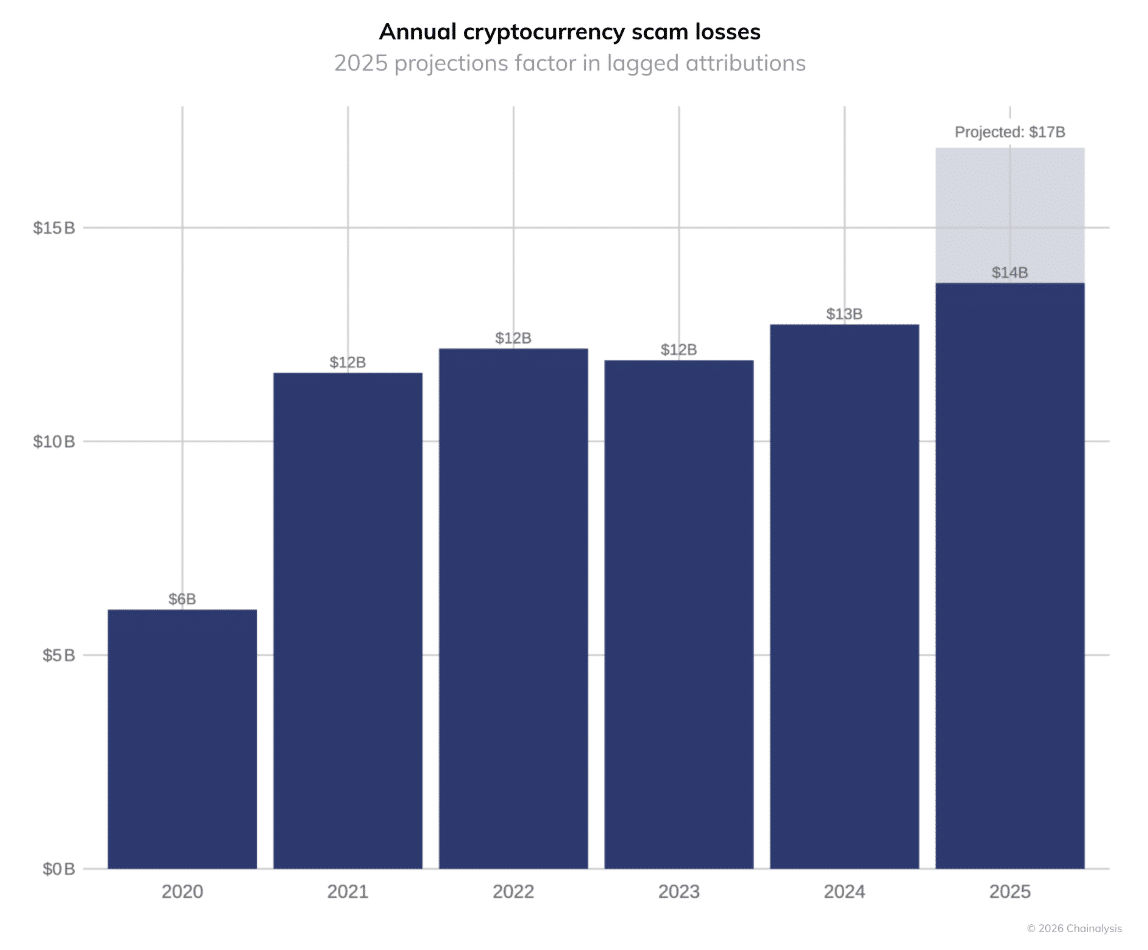
According to Chainalysis, scammers received around $14 billion in crypto in 2025, and investigators could identify over $17 billion as they uncover more illicit wallets.
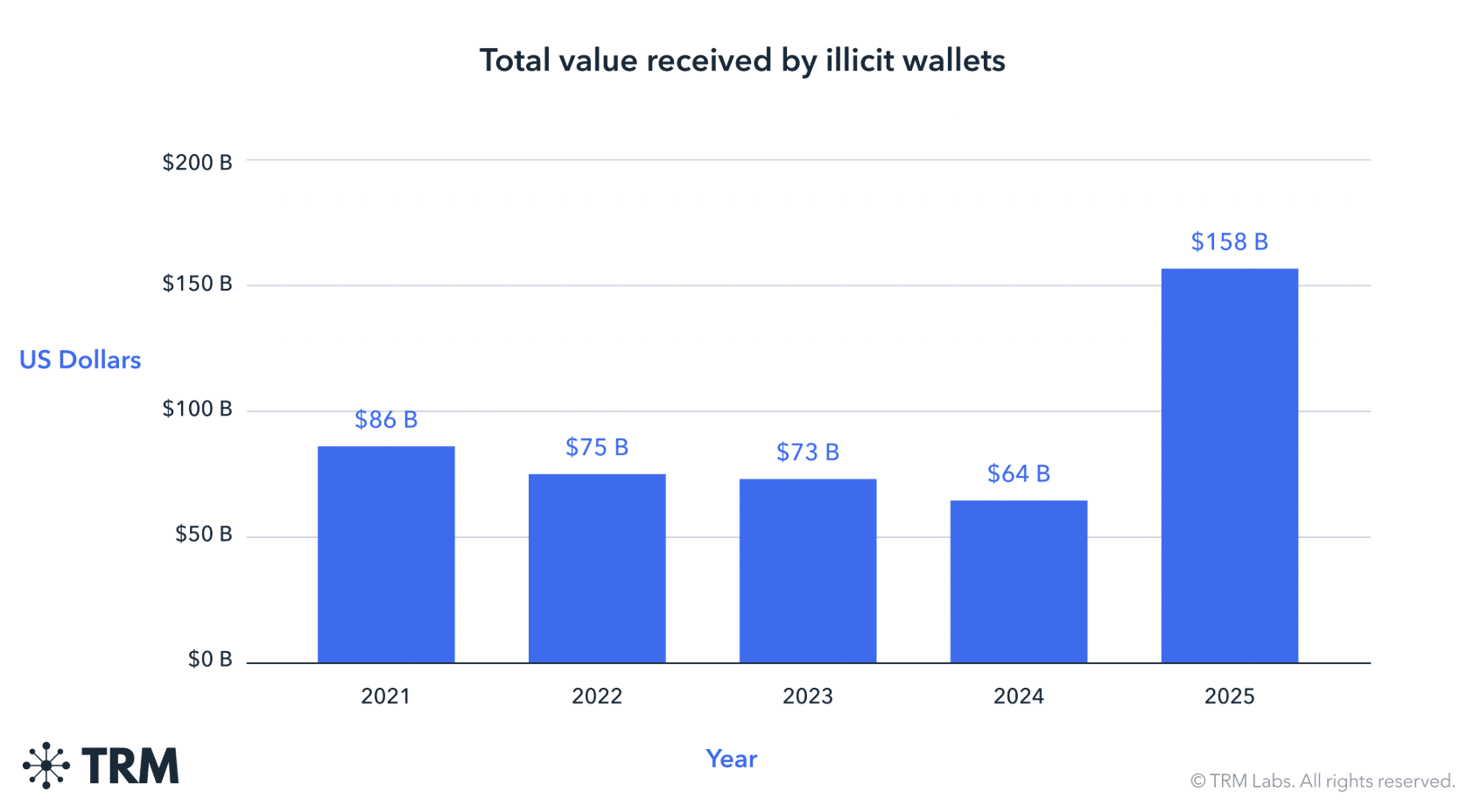
However, TRM Labs reports a positive trend.
Illicit crypto activity reached $158 billion last year, but it accounted for only about 1.2% of total market activity. This suggests that despite rising fraud, the legitimate crypto economy is expanding at a much faster pace.
Final Summary
- The rise of approval phishing scams exposes a key weakness in Web3 design, wherein many users do not fully understand the permissions they grant to smart contracts.
- Billions lost to scams indicate that criminal networks are scaling just as quickly as the crypto industry itself.