In response to the persistent attacks by North Korean hackers on the cryptocurrency industry, Chainalysis's 2025 Hacking Report provides a detailed analysis of their activities. The details are as follows.
Key Points:
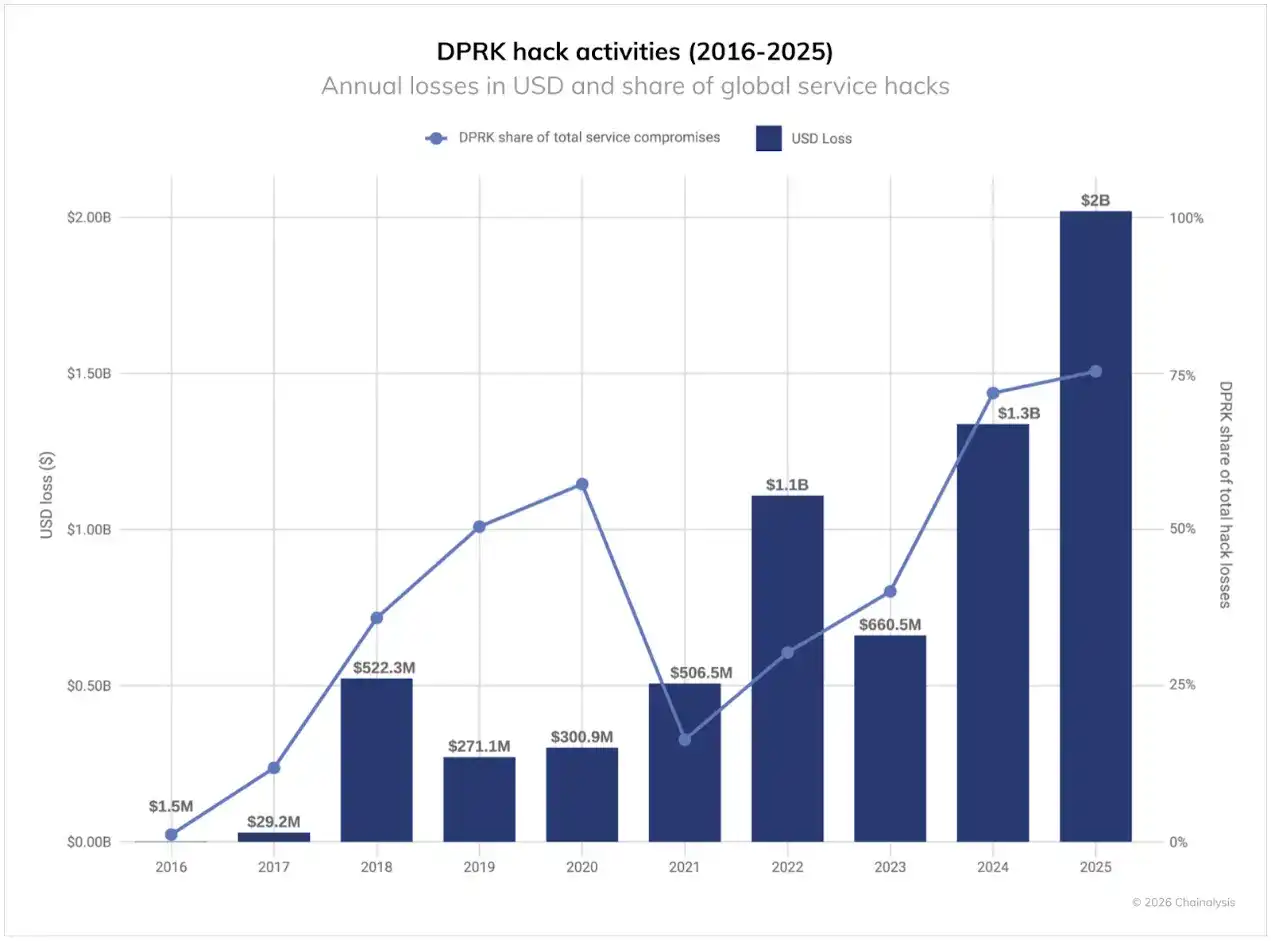
· North Korean hackers stole $2.02 billion worth of cryptocurrency in 2025, a 51% increase year-over-year. Despite a decrease in the number of attacks, their cumulative theft total has reached $6.75 billion.
· North Korean hackers stole more cryptocurrency with fewer attacks, often by infiltrating crypto services with IT workers or using sophisticated impersonation tactics targeting executives.
· North Korean hackers show a clear preference for Chinese money laundering services, cross-chain bridge services, and mixing protocols. The money laundering cycle after major thefts is approximately 45 days.
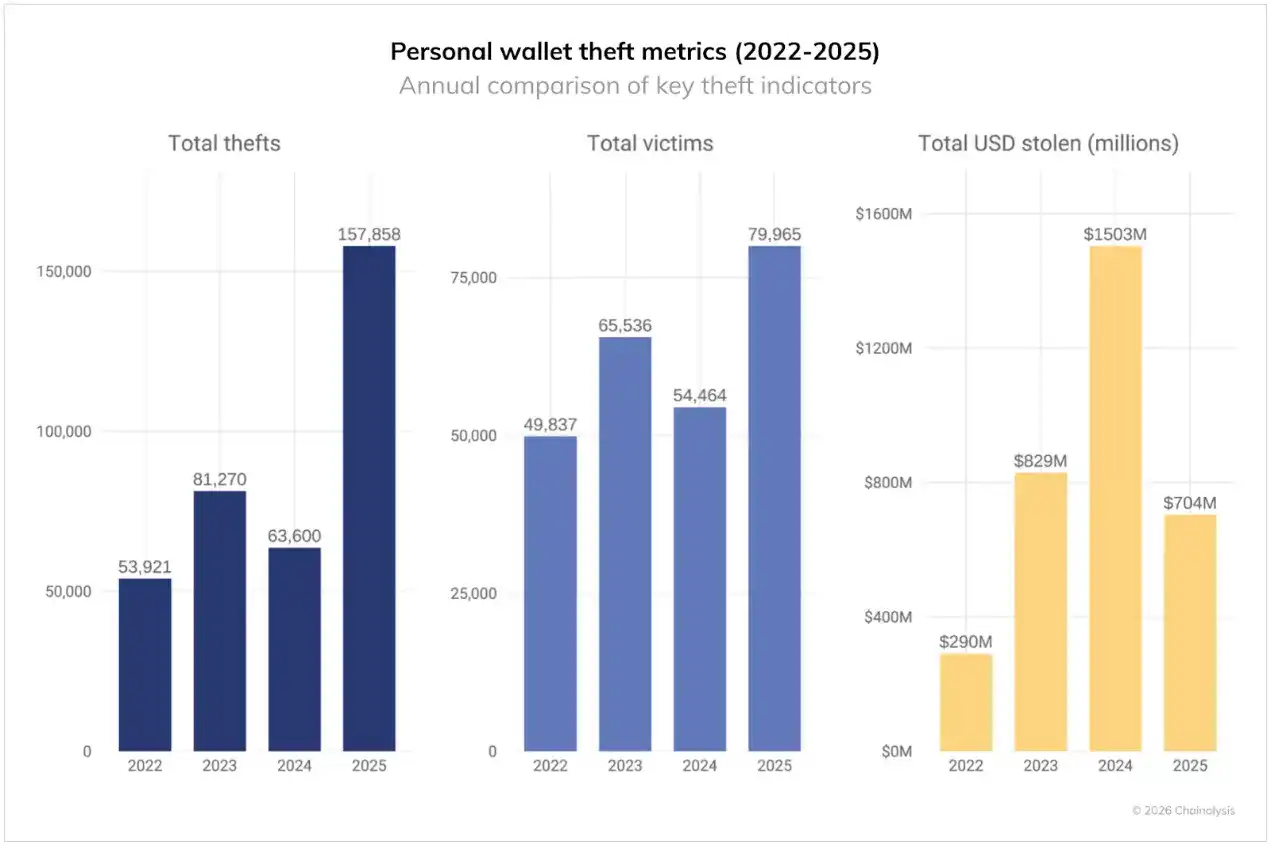
· In 2025, individual wallet thefts surged to 158,000 incidents, affecting 80,000 users, although the total value stolen ($713 million) decreased compared to 2024.
· Despite an increase in Total Value Locked (TVL) in DeFi, hacking losses from 2024 to 2025 remained relatively low, indicating that improvements in security measures are having a significant effect.
In 2025, the crypto ecosystem faced severe challenges again, with stolen funds continuing to rise. Analysis reveals four key characteristics of crypto theft patterns: North Korean hackers remain the primary threat source; individual attacks targeting centralized services are becoming more severe; individual wallet theft incidents are surging; and DeFi hacking trends show an unexpected divergence.
Overall Situation: Over $3.4 Billion Stolen in 2025
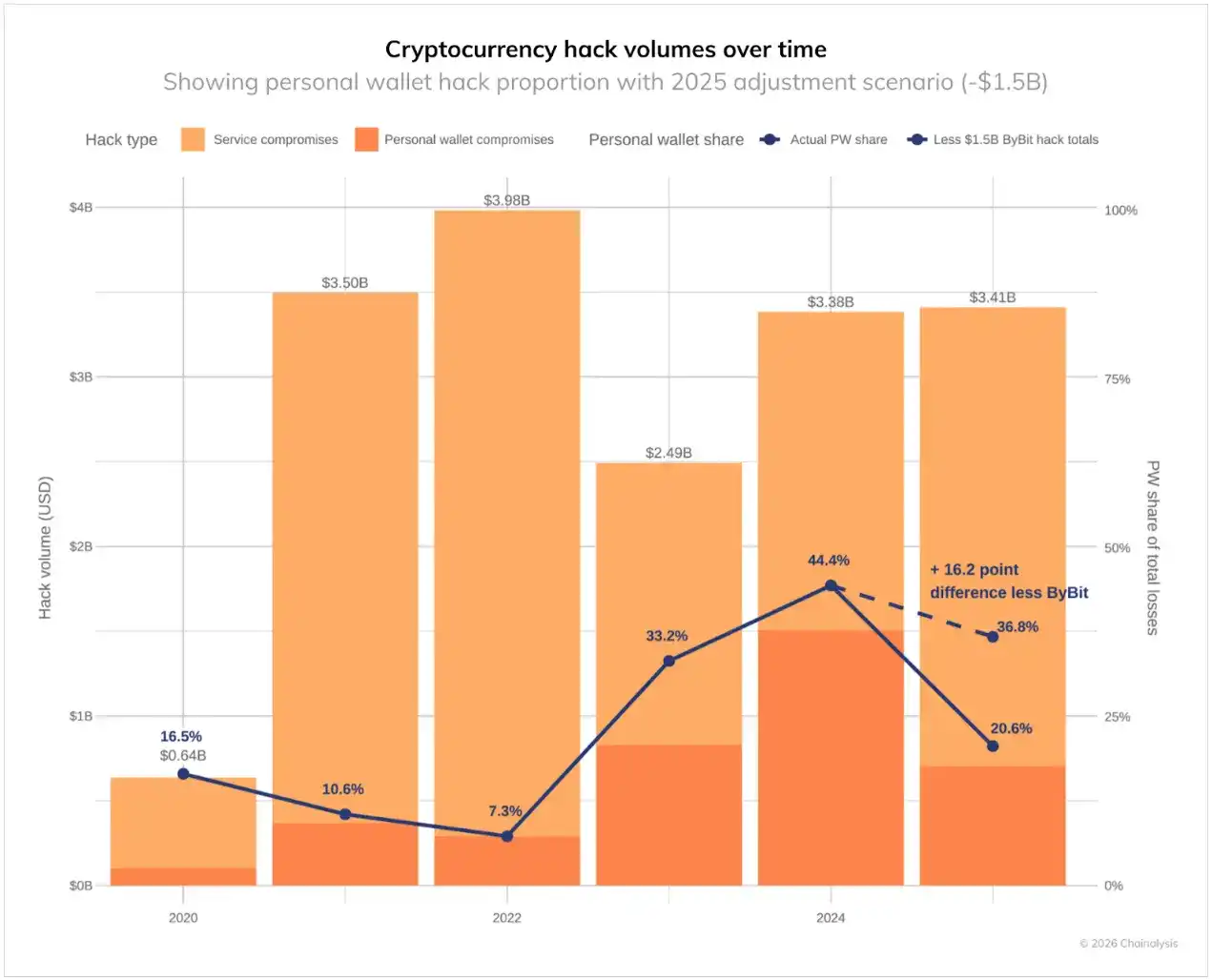
From January to early December 2025, over $3.4 billion was stolen from the crypto industry, with the February attack on Bybit alone accounting for $1.5 billion.
The data also reveals significant changes in these theft incidents. Individual wallet thefts increased substantially, rising from 7.3% of the total stolen value in 2022 to 44% in 2024. Were it not for the massive impact of the Bybit attack, this proportion could have reached 37% in 2025.
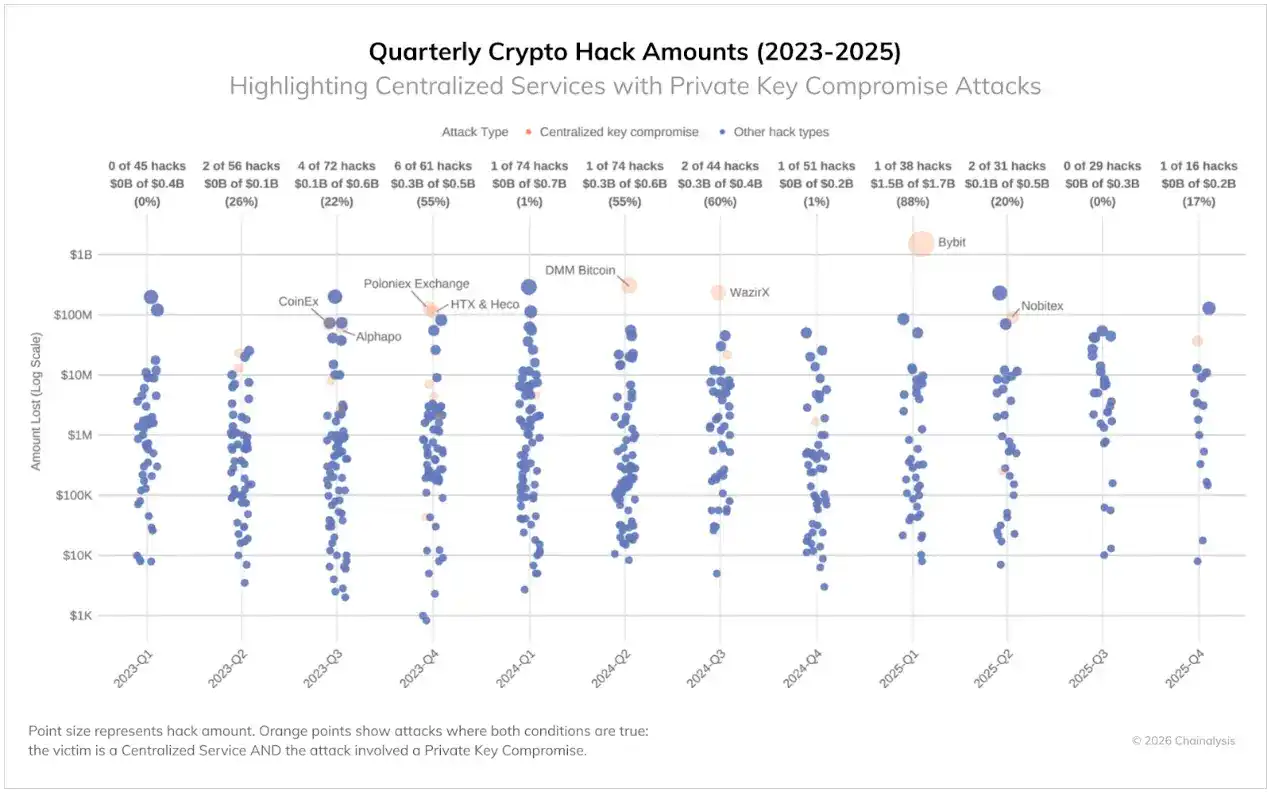
Meanwhile, centralized services are suffering increasing losses due to sophisticated attacks targeting private key infrastructure and signing processes. Despite having institutional resources and professional security teams, these platforms remain vulnerable to threats that can bypass cold wallet controls. Although such intrusions are not frequent (as shown in the chart below), when they occur, they result in massive stolen funds, accounting for 88% of total losses in Q1 2025. Many attackers have developed methods to exploit third-party wallet integrations and trick signers into authorizing malicious transactions.
Although crypto security may have improved in some areas, the persistently high amount stolen indicates that attackers can still succeed through multiple avenues.
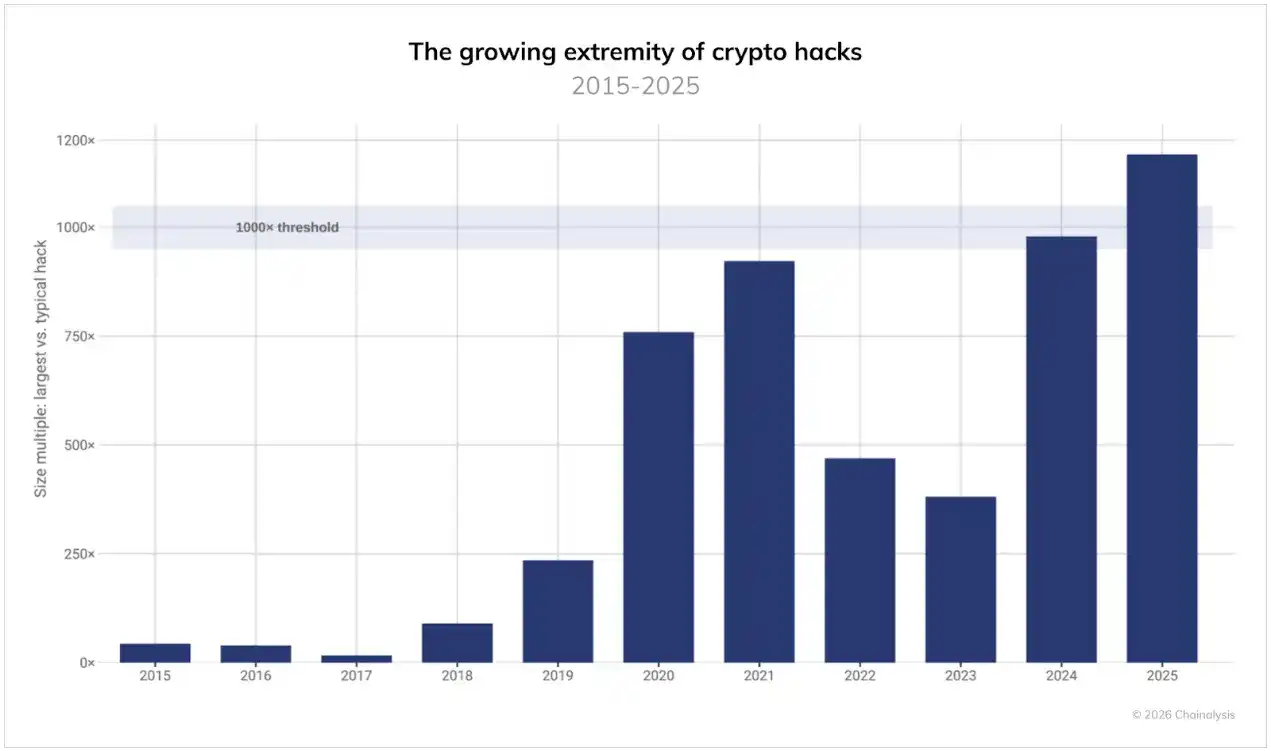
Top Three Hacks Account for 69% of Total Losses, Extreme Values Reach 1000x the Median
Fund theft incidents have historically been driven by extreme events, with most hacks being relatively small in scale, but a few being enormous. However, the situation worsened in 2025: the ratio between the largest hack and the median of all incidents broke the 1000x threshold for the first time. The funds stolen in the largest attacks are now 1000 times those in ordinary incidents, even exceeding the peak during the 2021 bull market. These calculations are based on the USD value of the stolen funds at the time of theft.
This widening gap leads to highly concentrated losses. The top three hacks in 2025 accounted for 69% of all losses, with individual events having an exceptionally significant impact on the annual total. Although attack frequency may fluctuate, and the median loss increases with rising asset prices, the potential loss from individual major vulnerabilities is rising at an even faster rate.
Despite a Decrease in Confirmed Attacks, North Korea Remains the Primary Threat
Despite a significant drop in attack frequency, North Korea remains the most serious threat to crypto security, stealing a record high of at least $2.02 billion in cryptocurrency funds in 2025 ($681 million more than in 2024), a year-over-year increase of 51%. In terms of value stolen, this is the worst year on record for North Korean cryptocurrency thefts. Attacks attributed to North Korea accounted for 76% of all intrusions, a historical high. Overall, the cumulative total stolen by North Korea has reached a conservative estimate of $6.75 billion.
North Korean hackers are increasingly gaining privileged access and carrying out major attacks by placing IT personnel (a primary attack vector) inside crypto services. This year's record thefts may partly reflect North Korea's increased reliance on infiltrating exchanges, custodians, and Web3 companies with IT workers, which can expedite initial access and lateral movement, creating conditions for large-scale theft.
However, recent hacker groups linked to North Korea have completely subverted this IT worker model. Instead of just applying for jobs and infiltrating as employees, they are increasingly impersonating recruiters from well-known Web3 and AI companies, orchestrating fake hiring processes that ultimately obtain victims' login details, source code, and access to their current employer's VPN or Single Sign-On (SSO) under the guise of "technical screening." At the executive level, similar social engineering tactics appear as contact from fake strategic investors or acquirers, who use pitch meetings and pseudo due diligence to probe for sensitive system information and potentially high-value infrastructure—an evolution built directly upon North Korean IT worker fraud operations and focused on strategically important AI and blockchain companies.
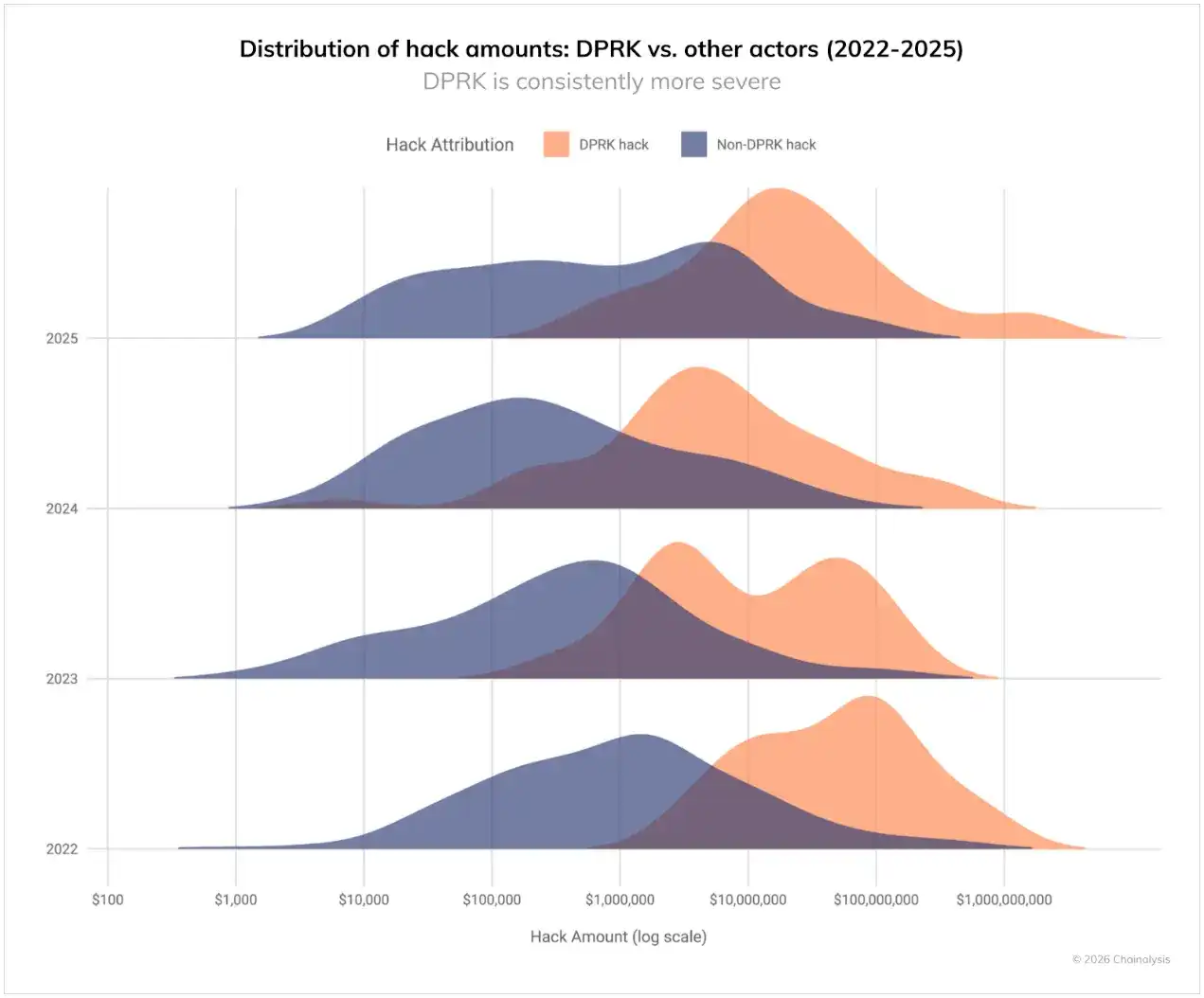
As seen in past years, the value of ongoing cyberattacks by North Korea far exceeds that of other hackers. As shown in the chart below, from 2022 to 2025, North Korean hacks occupy the highest value brackets, while non-North Korean hacks show a more normal distribution across all theft sizes. This pattern further suggests that when North Korean hackers strike, they target large services, aiming for maximum impact.
This year's record losses come from a significant reduction in known incidents. This shift (fewer incidents but much larger losses) reflects the impact of the massive Bybit hack in February 2025.
North Korea's Unique Money Laundering Patterns
The influx of a large amount of stolen funds in early 2025 reveals how North Korean hackers launder cryptocurrency on a large scale. Their patterns are distinct from other cybercriminals and have evolved over time.
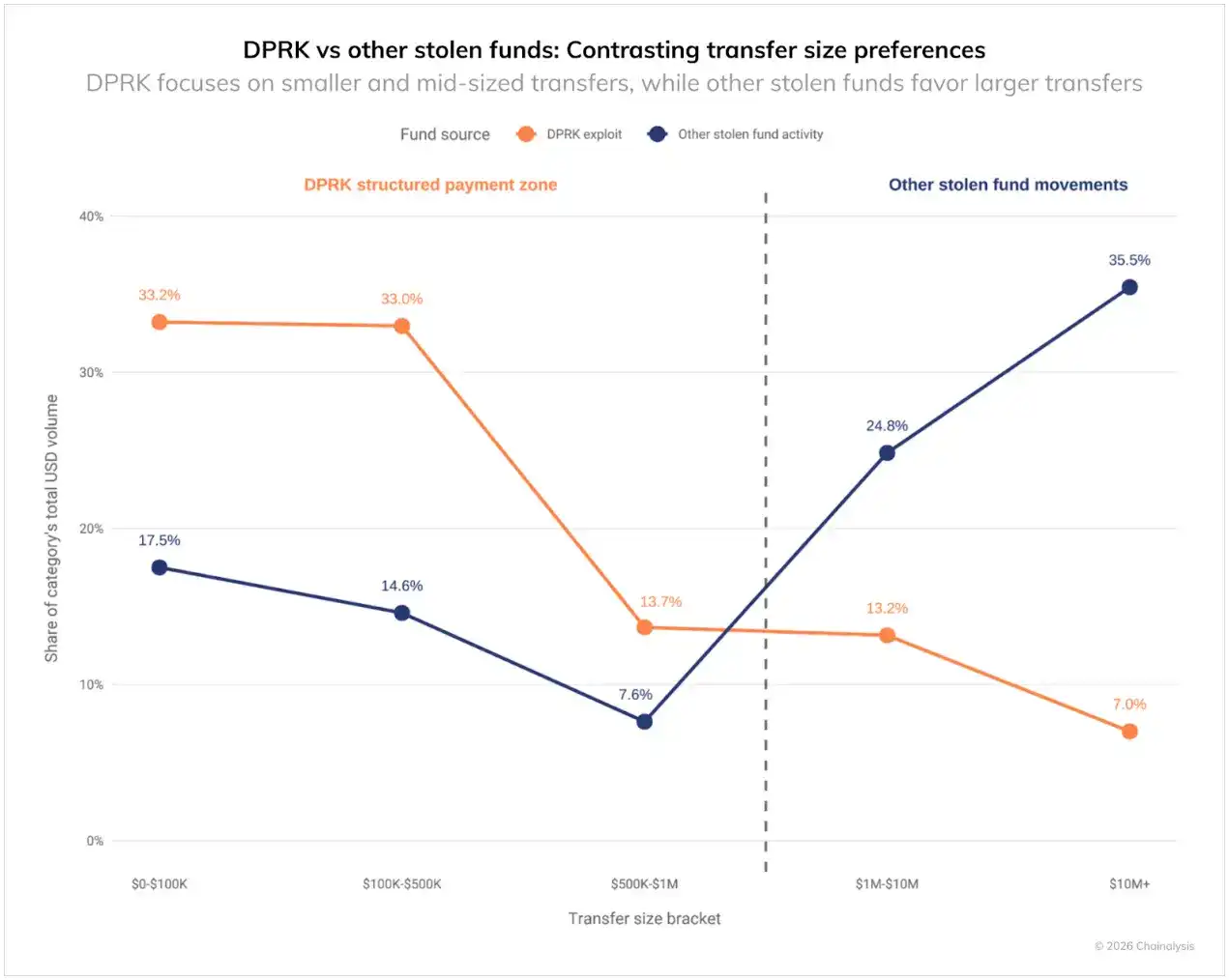
North Korea's money laundering activities show a distinct "bucketing" pattern, with over 60% of transaction volumes concentrated below $500,000. In contrast, other hackers batch over 60% of their on-chain movements in the $1 million to over $10 million range. Although North Korea launders larger amounts per incident than other hackers, they break on-chain transfers into smaller batches, highlighting the sophistication of their laundering methods.
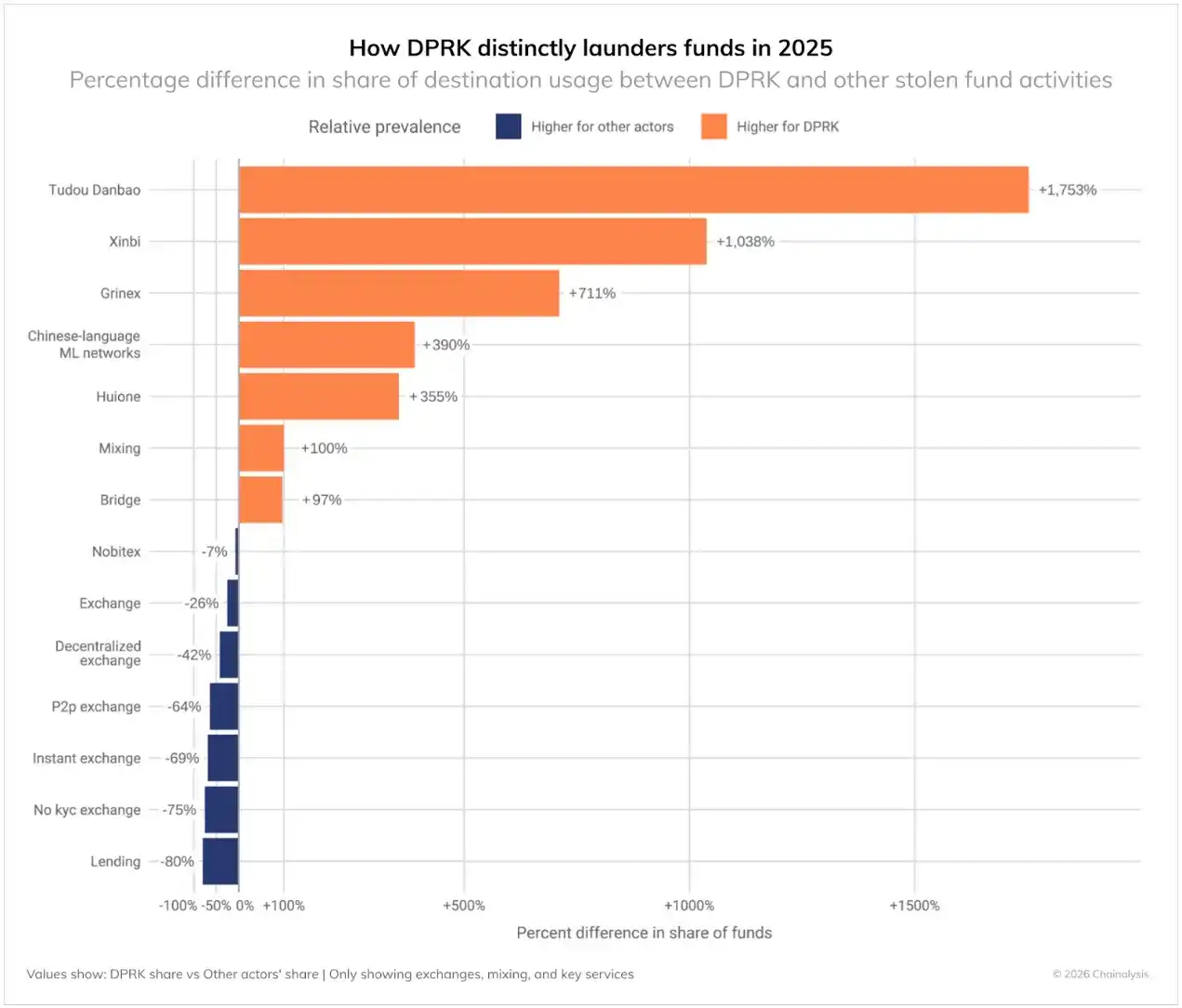
Compared to other hackers, North Korea shows clear preferences in certain laundering channels:
North Korean hackers tend to favor:
· Chinese fund transfer and escrow services (+355% to over 1000%): This is the most distinctive feature, showing heavy reliance on Chinese escrow services and money laundering networks composed of numerous operators potentially subject to weaker compliance controls.
· Cross-chain bridge services (+97%): High reliance on cross-chain bridges to move assets between blockchains and attempt to increase tracing difficulty.
· Mixing services (+100%): Greater use of mixing services to attempt to obscure fund flows.
· Specialized services like Huione (+356%): Strategic use of specific services to aid their laundering activities.
Other hackers involved in money laundering tend to favor:
· Lending protocols (-80%): North Korea avoids these DeFi services, indicating limited integration with the broader DeFi ecosystem.
· Non-KYC exchanges (-75%): Surprisingly, other hackers use non-KYC exchanges more than North Korea.
· P2P exchanges (-64%): North Korea shows limited interest in P2P platforms.
· CEXs (-25%): Other hackers have more direct interaction with traditional exchanges.
· DEXs (-42%): Other hackers prefer DEXs due to high liquidity and anonymity.
These patterns suggest North Korean operations are subject to different constraints and objectives than non-state-sponsored cybercriminals. Their heavy use of specialized Chinese money laundering services and over-the-counter (OTC) traders indicates tight links between North Korean hackers and illicit actors in the Asia-Pacific region.
Timeline of Money Laundering for Stolen Funds After North Korean Hacks
Analysis of on-chain activity following hacking incidents attributed to North Korea between 2022-2025 reveals consistent patterns linking these events to the flow of stolen funds within the crypto ecosystem. Following major thefts, stolen funds follow a structured, multi-stage money laundering path, a process lasting approximately 45 days:
Stage 1: Immediate Layering (Days 0-5)
In the first few days after a hack occurs, a flurry of activity is observed, focused on immediately moving funds away from the compromised source:
· Stolen fund flows to DeFi protocols see the largest increase (+370%), serving as the primary entry point.
· Mixing service volumes also rise significantly (+135-150%), constituting the first layer of obfuscation.
· This stage represents an urgent "first step" action aimed at creating distance from the initial theft.
Stage 2: Initial Consolidation (Days 6-10)
Moving into the second week, laundering strategies shift towards services that help integrate funds into the broader ecosystem:
· Exchanges with fewer KYC restrictions (+37%) and CEXs (+32%) begin receiving fund flows.
· Second-layer mixing services (+76%) continue laundering activities at a lower intensity.
· Cross-chain bridging (e.g., XMRt, +141%) helps disperse and obscure flows across blockchains.
· This stage is a critical transition period where funds begin flowing towards potential off-ramps.
Stage 3: Long-Tail Consolidation (Days 20-45)
The final stage shows a clear preference for services enabling final conversion to fiat or other assets:
· Usage of non-KYC exchanges (+82%) and escrow services (e.g., Tudo Escrow, +87%) grows significantly.
· Instant exchanges (+61%) and Chinese platforms (e.g., Huiwang, +45%) become final cash-out points.
· CEXs (+50%) also receive funds, indicating sophisticated attempts to commingle funds with legitimate ones.
· Less regulated jurisdictions, such as Chinese money laundering networks (+33%) and platforms like Grinex (+39%), complete this pattern.
This typically 45-day operational window for money laundering provides critical intelligence for law enforcement and compliance teams. The persistence of this pattern over years suggests North Korean hackers face operational constraints, likely related to their limited access to financial infrastructure and the need to coordinate with specific intermediaries.
Although these hackers don't always follow this exact timeline—some stolen funds lie dormant for months or years—this pattern represents their typical on-chain behavior when actively laundering. Furthermore, it's essential to recognize potential blind spots in this analysis, as certain activities (like private key transfers or OTC crypto-to-fiat exchanges) are not visible on-chain without corroborating intelligence.
Individual Wallet Thefts: Growing Threat to Individual Users
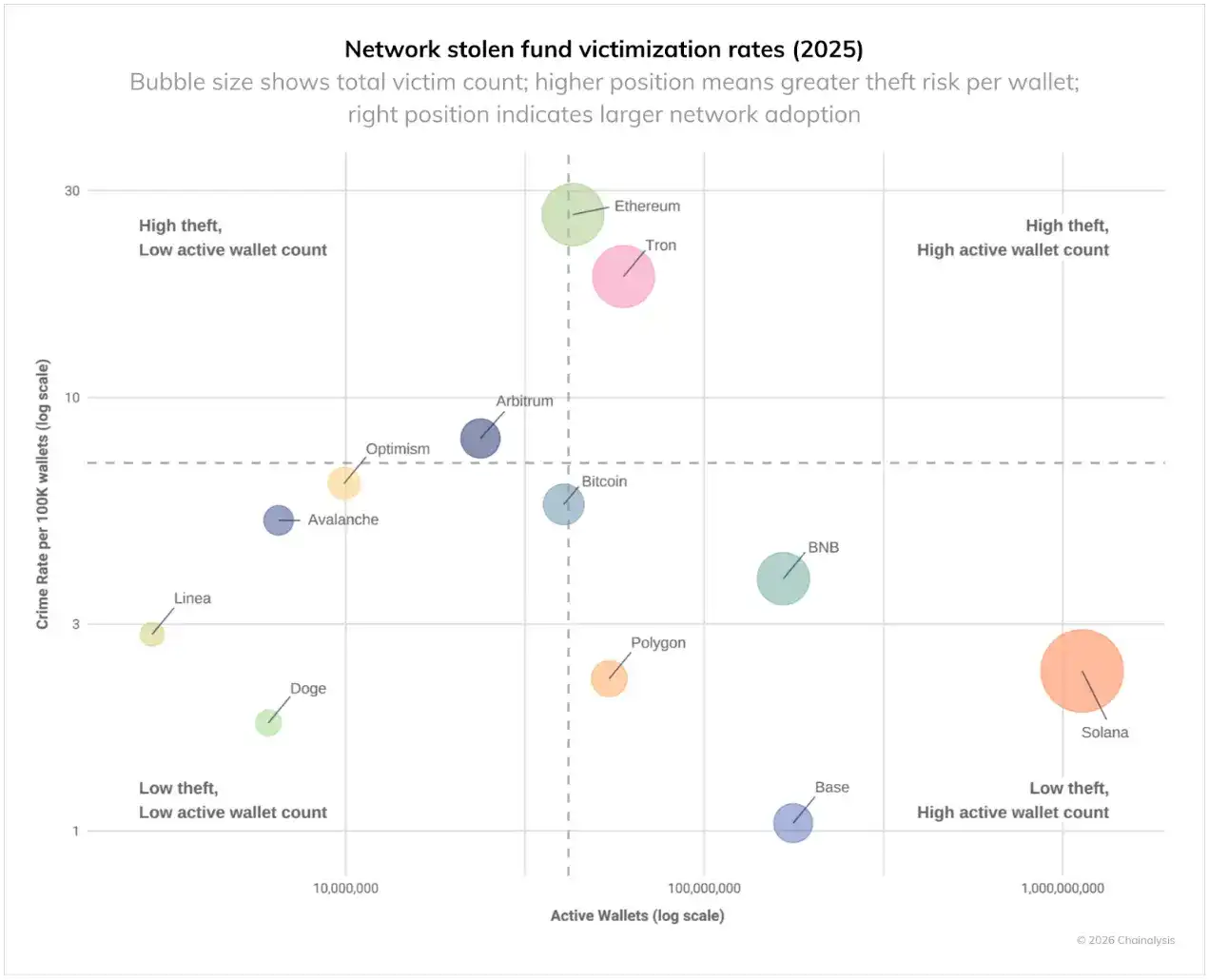
Analysis of on-chain patterns, along with reports from victims and industry partners, provides insight into the severity of individual wallet thefts, although the actual number is likely much higher. Conservatively estimated, losses from individual wallet thefts accounted for 20% of total losses in 2025, down from 44% in 2024, indicating a shift in both scale and pattern. The total number of theft incidents in 2025 surged to 158,000, nearly triple the 54,000 recorded in 2022. The number of victims increased from 40,000 in 2022 to at least 80,000 in 2025. This significant growth is likely due to broader cryptocurrency adoption. For instance, Solana, one of the blockchains with the most active individual wallets, led in the number of theft incidents (approximately 26,500 victims).
However, despite the increase in incidents and victims, the total USD amount stolen per victim decreased from the 2024 peak of $1.5 billion to $713 million in 2025. This suggests attackers are targeting more users, but stealing less from each victim.
Victim data for specific networks provides more insight into which areas pose the greatest threat to crypto users. The chart below shows victim data adjusted for active individual wallets per network. Measured by the 2025 crime rate per 100,000 wallets, Ethereum and Tron have the highest theft rates. Ethereum's large user base indicates both a high theft rate and a high number of victims, while Tron's ranking shows a high theft rate despite a smaller number of active wallets. In contrast, Base and Solana show lower victimization rates despite their large user bases.
This indicates that security risks for individual wallets are not uniform across the crypto ecosystem. Even with similar technical architectures, victimization rates vary between blockchains, suggesting that factors beyond technology—such as user demographics, popular applications, and criminal infrastructure—play significant roles in determining theft rates.
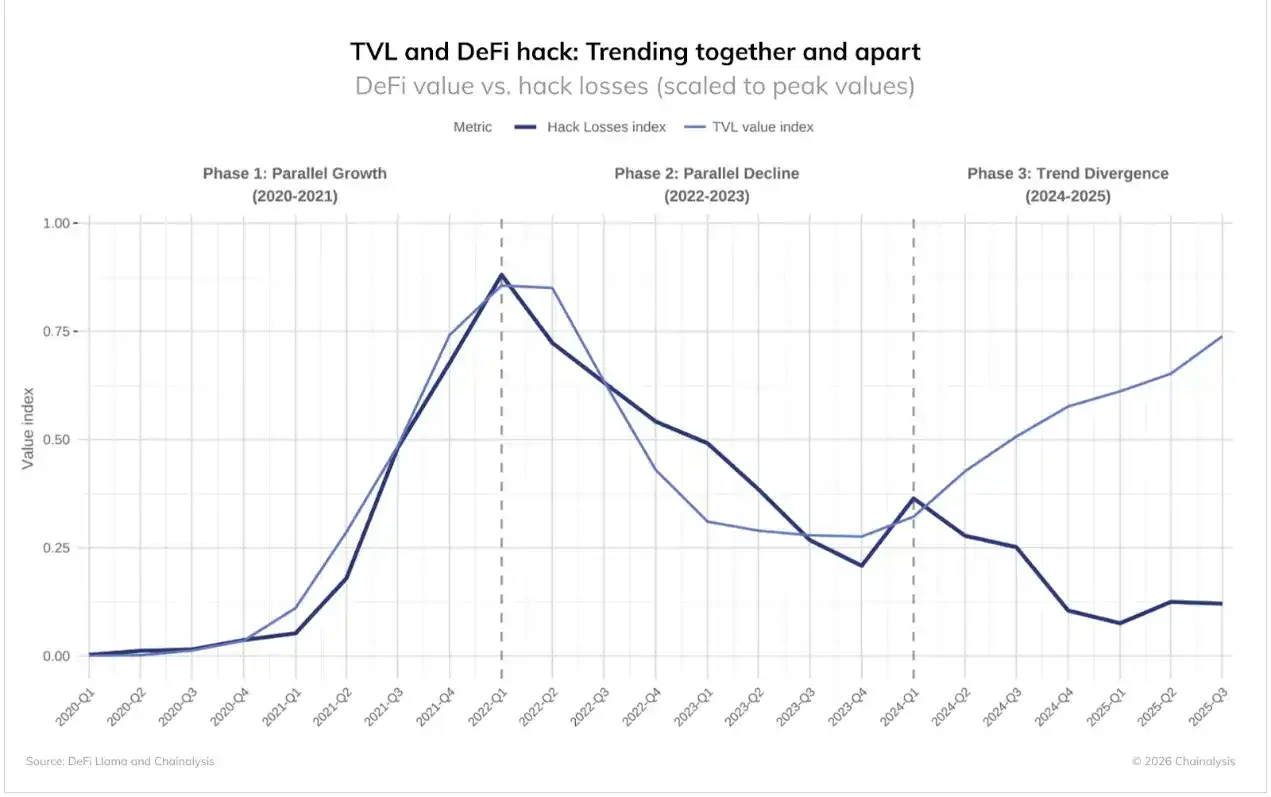
DeFi Hacks: Diverging Patterns Signal Market Shift
The DeFi sector presented unique patterns in the 2025 crime data, showing a clear departure from historical trends.
The data reveals three distinct phases:
· Phase 1 (2020-2021): DeFi TVL and hacking losses grew in sync.
· Phase 2 (2022-2023): Both metrics declined together.
· Phase 3 (2024-2025): TVL recovered, while hacking losses remained stable.
The first two phases followed an intuitive pattern: more value at risk meant more value to steal, and hackers targeted high-value protocols more aggressively. As bank robber Willie Sutton said, "Because that's where the money is."
This makes the divergence in Phase 3 even more notable. DeFi TVL has rebounded significantly from the 2023 lows, but losses from hacks have not followed suit. Despite billions flowing back into these protocols, DeFi hacks have remained persistently low, representing a significant change.
Two factors may explain this divergence:
· Improved Security: Despite growing TVL, hack rates have continued to fall, suggesting DeFi protocols may be implementing more effective security measures than during the 2020-2021 period.
· Shift in Targets: The concurrent rise in individual wallet thefts and centralized service attacks suggests attacker attention may be shifting to other targets.
Case Study: Venus Protocol's Security Response
The September 2025 incident involving the Venus protocol demonstrates that improved security measures are having a tangible effect. At that time, an attacker used a compromised Zoom client to gain system access and tricked a user into granting delegation authority for a $13 million account, a situation that could have had disastrous consequences. However, Venus had恰好 enabled Hexagate's security monitoring platform just one month prior.
The platform detected suspicious activity 18 hours before the attack and issued another alert as soon as the malicious transaction occurred. Within 20 minutes, Venus paused its protocol, preventing any fund movement. This coordinated response showcases the evolution of DeFi security:
· Within 5 hours: Partial functionality restored after security checks.
· Within 7 hours: Forced liquidation of the attacker's wallet.
· Within 12 hours: Full recovery of stolen funds and service restoration.
Most notably, Venus passed a governance proposal freezing $3 million in assets still controlled by the attacker; the attacker not only failed to profit but lost funds.
This incident shows tangible improvements in DeFi security infrastructure. The combination of proactive monitoring, rapid response capabilities, and governance mechanisms able to act decisively makes the ecosystem more agile and resilient. Although attacks still occur, the ability to detect, respond to, and even reverse attacks represents a fundamental shift from the early DeFi era, where successful attacks often meant permanent loss.
Implications for 2026 and Beyond
The 2025 data paints a picture of North Korea's sophisticated evolution as the crypto industry's greatest threat. The country is carrying out fewer attacks but with dramatically greater impact, suggesting increasingly sophisticated and patient methods. The influence of the Bybit event on its annual activity pattern indicates that when North Korea succeeds in a major theft, it reduces its operational tempo, focusing instead on money laundering.
For the crypto industry, this evolution demands increased vigilance regarding high-value targets and improved identification of North Korea-specific money laundering patterns. Their consistent preference for specific service types and transfer amounts provides detection opportunities, distinguishing them from other criminals and helping investigators identify their on-chain behavioral signatures.
As North Korea continues to leverage cryptocurrency theft to fund national priorities and evade international sanctions, the crypto industry must recognize that its operational rhythms differ starkly from typical cybercriminals. North Korea's record performance in 2025 (with a 74% reduction in known attacks) suggests that we may only be seeing the most visible portion of its activity currently. The challenge for 2026 is detecting and disrupting these operations before North Korea launches another Bybit-scale attack.