Authored by: Chainalysis
Compiled by: Chopper, Foresight News
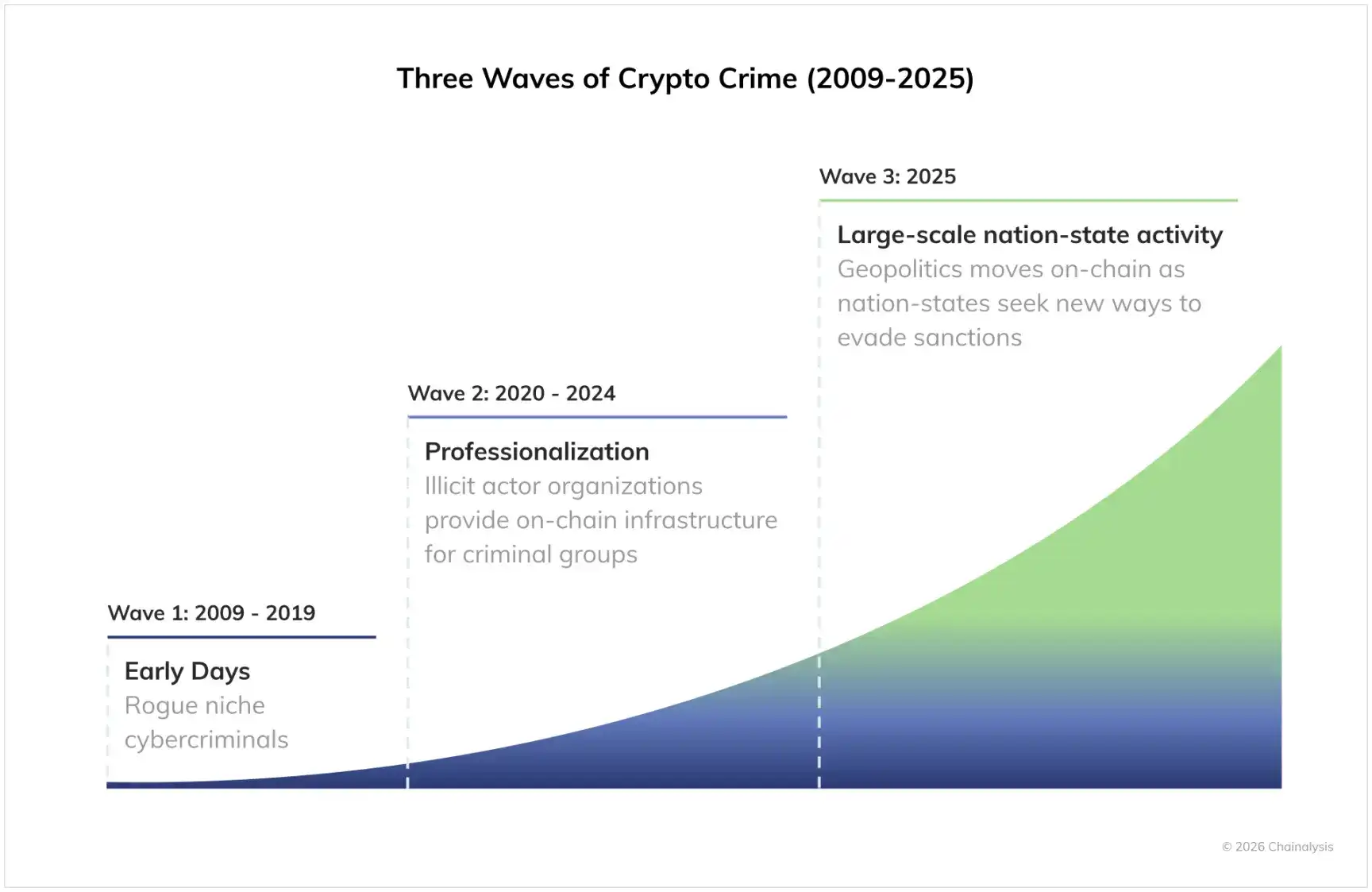
In 2025, we observed a significant increase in state-level cryptocurrency-related activities, marking a new mature phase in the development of the illegal on-chain ecosystem. Over the past few years, the professionalization within the crypto crime sphere has deepened; illicit organizations have established large-scale on-chain infrastructure to support transnational criminal networks in procuring goods and services and laundering crypto crime proceeds. Against this backdrop, national governments have also begun to engage in this domain, leveraging these mature professional service providers on one hand, and building their own customized infrastructure on the other, to evade sanctions on a large scale. As governments tap into this illicit cryptocurrency supply chain originally built for cybercriminals and organized crime groups, government agencies, compliance, and security teams now face severe challenges in terms of consumer protection and national security.
What are the specific on-chain manifestations of these developments and other industry changes? Next, we will analyze them by combining data and macro trends.
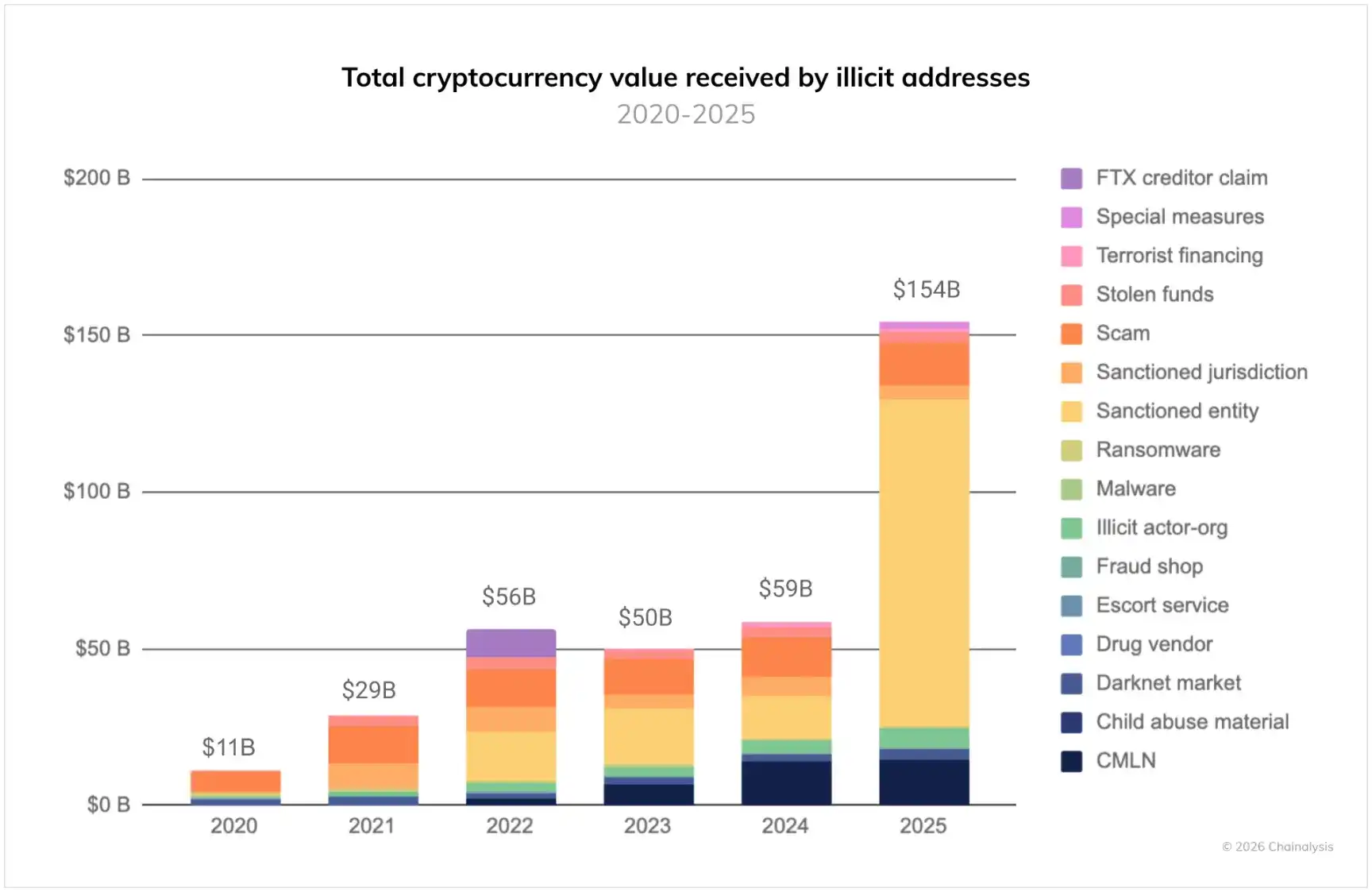
According to our monitoring data, the scale of funds flowing into illicit cryptocurrency addresses in 2025 reached at least $154 billion, a sharp increase of 162% year-on-year. This growth was primarily driven by a surge in fund inflows to sanctioned entities, which soared by 694% year-on-year. However, even excluding the growth from sanctioned entities, 2025 still stands as a record year for crypto crime, as the vast majority of illicit activity categories saw growth.
Nevertheless, the scale of these illicit transactions still pales in comparison to the overall cryptocurrency economy, where legitimate transactions remain the mainstay. We estimate that although the proportion of illicit transactions in the total traceable cryptocurrency transaction volume in 2025 increased slightly compared to 2024, it remained below 1%.
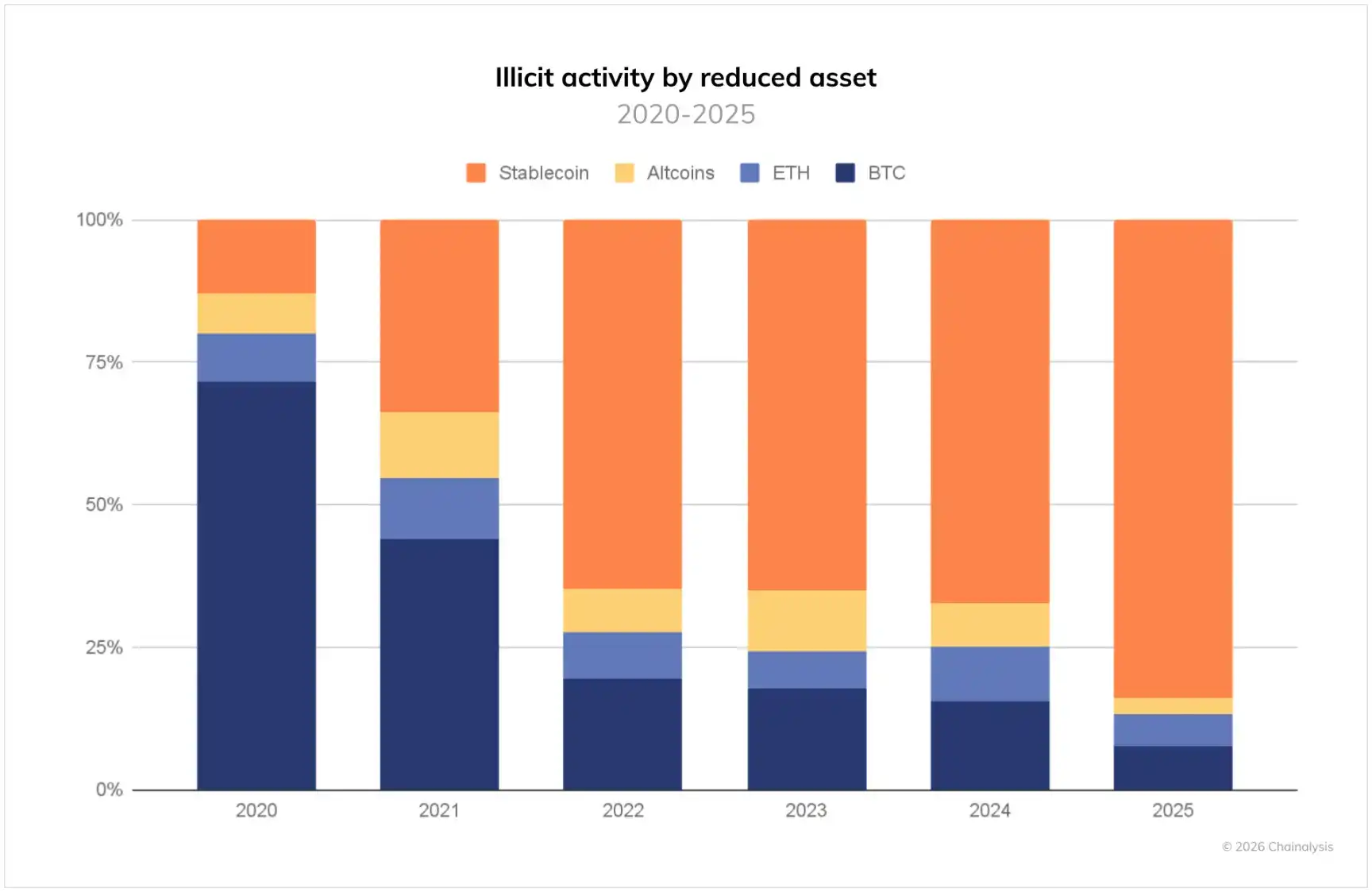
As shown in the figure below, we also observed a continuing shift in the types of assets involved in crypto crime.
Over the past few years, stablecoins have gradually become the dominant asset for illicit transactions, currently accounting for 84% of the total illicit transaction volume. This trend aligns with the overall development characteristics of the cryptocurrency ecosystem: with advantages such as convenience for cross-border transfers, low volatility, and wide application scenarios, the share of stablecoins in the entire cryptocurrency transaction volume continues to expand.
The following sections will delve into the core trends that defined the crypto crime landscape in 2025, trends that will remain important to watch in the future.
National-Level Threats Drive Transaction Volume: North Korean Thefts Hit Record High, Russian A7A5 Token Facilitates Large-Scale Sanction Evasion
In 2025, stolen funds remained a major threat to the cryptocurrency ecosystem, with North Korean-linked hacker groups alone stealing $2 billion. This figure was primarily driven by several highly destructive large-scale hacking incidents, the most notable being the attack on the Bybit exchange in February. The incident involved nearly $1.5 billion, making it the largest digital asset theft in the history of cryptocurrency. Although North Korean hackers have long been a major force threatening the cryptocurrency ecosystem, the past year saw record highs both in the amount stolen and in the sophistication of their intrusion and money laundering methods.
Particularly noteworthy is that the scale of on-chain activities by national governments reached unprecedented levels in 2025. Russia introduced relevant legislation in 2024 to promote the use of cryptocurrency to evade sanctions, and this measure was formally implemented in February 2025. The country launched the ruble-backed token A7A5, which saw its transaction volume exceed $93.3 billion in less than a year since its launch.
Meanwhile, over the past few years, Iran's proxy networks have conducted money laundering, illegal oil trading, and procurement of weapons and bulk commodities on-chain through identifiable wallet addresses already on sanctions lists, with a cumulative transaction volume exceeding $2 billion. Despite multiple military strikes, Iran-backed terrorist groups such as Hezbollah, Hamas, and the Houthis continue to use cryptocurrency on an unprecedented scale.
In 2025, Chinese money laundering networks emerged as a dominant force in the illicit on-chain ecosystem. These organizations operate with sophisticated models, significantly driving the diversification and professionalization of crypto crime, offering specialized criminal services including "money laundering services." Building on early illegal operation models like "Huiyin Guarantee," these networks have established full-service criminal enterprises, covering areas such as fraud, scams, laundering proceeds from North Korean hacker thefts, sanction evasion, and terrorism financing.
Full-Stack Illicit Infrastructure Providers Fuel Malicious Cyber Activities
While national governments are increasing their use of cryptocurrency, traditional cybercrime remains rampant: ransomware operators, child sexual abuse and cybercrime platforms, malware distributors, scammers, and illicit marketplaces still rely on vast support networks to maintain operations. Illicit actors and national governments are increasingly dependent on full-stack on-chain infrastructure providers, including domain registrars, secure and reliable hosting services, and other technical infrastructure that can be used for malicious cyber activities.
These infrastructure providers have evolved into comprehensive infrastructure platforms capable of resisting platform takedowns, abuse complaints, and sanction enforcement. As the scale of these services continues to expand, they are likely to become a key force driving economic crime and state-backed entities to broaden the scope of their malicious cyber activities.
Growing Correlation Between Cryptocurrency and Violent Crime
In the perception of many, crypto crime is still confined to the virtual world. The masterminds are merely anonymous figures hiding behind keyboards, not translating into real-world threats. But in reality, the link between on-chain activities and violent crime is deepening. Human trafficking rings are increasingly using cryptocurrency for transactions; at the same time, disturbingly, there has been a significant rise in cases of violent coercion attacks, where criminals use violence to force victims to transfer crypto assets, and such assaults often occur during peak cryptocurrency price periods.
Looking ahead, collaboration between law enforcement agencies, regulatory bodies, and cryptocurrency companies will be key to addressing these complex, evolving, and interconnected threats. Although the proportion of illicit transactions within legitimate cryptocurrency trading volume remains limited, maintaining the integrity and security of the cryptocurrency ecosystem has never been more important.