Quick Facts:
- ➡️ The Infini exploiter resurfaced to purchase approximately $13M in $ETH, highlighting persistent vulnerabilities in legacy blockchain security.
- ➡️ BMIC introduces post-quantum cryptography and Zero Public-Key Exposure to prevent future ‘Harvest Now, Decrypt Later’ attacks.
- ➡️ The BMIC presale has raised over $444K, signaling strong market demand for AI-enhanced, quantum-proof financial tools.
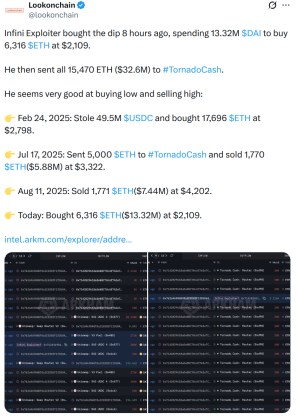
The ghost of a past exploit has returned to the blockchain. On-chain data confirms that the wallet associated with the notorious Infini exploit has broken its silence, moving significant capital to accumulate Ethereum during the recent market dip.
This isn’t just a simple buy order. It’s a strategic reallocation of illicit funds totaling approximately $13M, timed perfectly with $ETH’s local bottom.
That re-emergence signals a troubling shift in crypto market structure: bad actors are becoming sophisticated asset managers. Instead of immediately laundering stolen funds through mixers, these entities are holding, staking, and trading to compound their gains. The market reaction has been mixed. While some traders view the whale-sized buy pressure as a bullish signal for $ETH, security analysts see it as a glaring reminder of the ecosystem’s fragility. Frankly, it’s a wake-up call.
This event exposes a critical failure in current blockchain architecture. If a wallet can be compromised and the funds monitored but not frozen, the underlying security model isn’t ready for institutional adoption. The industry is effectively playing a game of whack-a-mole with legacy vulnerabilities.
But a shift is happening. While hackers exploit the transparency of current chains, next-generation protocols are building immune systems against them. That’s where BMIC ($BMIC) comes in, a project deploying quantum-secure cryptography to render these types of wallet exploits mathematically impossible.
Closing The Door On ‘Harvest Now, Decrypt Later’
The Infini incident highlights a specific vulnerability: the exposure of public keys and the persistence of compromised data. In the current EVM landscape, once a wallet interacts with a malicious contract, the user’s assets are often exposed forever.
BMIC fundamentally alters this dynamic by introducing the first full Quantum-Secure Finance Stack. By utilizing post-quantum cryptography (PQC) and ERC-4337 Smart Accounts, BMIC ensures that even if a bad actor intercepts data today, they can’t decrypt it. Not now, and not when quantum computers eventually break standard encryption.
Why does this matter? Because the threat vector is evolving. The ‘Harvest Now, Decrypt Later’ strategy means hackers are scraping encrypted data today to unlock it when computing power advances. BMIC counters this with a proprietary Zero Public-Key Exposure model. Unlike traditional wallets that broadcast keys, BMIC transactions remain shielded. It offers a level of sovereign protection that legacy wallets simply can’t match.
Plus, the integration of AI-Enhanced Threat Detection adds a proactive layer to this defense. While the Infini hacker relied on the passive nature of the blockchain to execute their trades unnoticed until it was too late, BMIC’s infrastructure actively monitors for anomalies. This creates a secure environment for ecosystem fuel, governance, and staking, ensuring that users, not exploiters, retain control of their digital future.
FIND OUT MORE ABOUT THE BMIC QUANTUM STACK
Smart Money Rotation Into Quantum Infrastructure
While the Infini hacker buys $ETH for short-term gains, forward-looking investors are positioning themselves in infrastructure plays that solve the security crisis permanently. The $BMIC presale has emerged as a focal point for this capital rotation, already raising over $444K from early adopters who recognize that the quantum transition is inevitable.
At the current token price of $0.049474, the entry point offers a distinct asymmetry compared to buying established Layer-1s. The market is beginning to value ‘insurance’ protocols, tech that protects the trillions of dollars in TVL from catastrophic failure. BMIC ($BMIC) isn’t merely a wallet; it’s a ‘Burn-to-Compute’ utility token powering a Quantum Meta-Cloud. It bridges the gap between decentralized finance and high-performance computing, making it one of the best crypto presales.
The utility here extends beyond simple storage. By enabling quantum-secure staking with no exposed keys, $BMIC solves the dilemma of earning yield without risking the principal. As regulatory scrutiny tightens on money laundering (highlighted by the Infini hacker’s movements), enterprises will be forced to migrate to compliant, secure environments.
BMIC provides that sanctuary. The current presale phase represents a rare opportunity to acquire the standard for future digital security before the wider market reprices the risk of legacy chains.
EXPLORE THE $BMIC PRESALE
The content of this article does not constitute financial or investment advice. Cryptocurrencies are highly volatile assets, and presales carry significant risk. Always conduct your own due diligence before making any financial decisions.