Editor's Note: On April 18, Kelp DAO was attacked, with approximately $292 million in assets stolen. So, in a completely transparent on-chain system, how exactly was this money step-by-step "cleaned" to become liquid assets?
This article uses this incident as a starting point to dissect a highly industrialized path for crypto money laundering: from the preparation of anonymous infrastructure before the attack, to using Tornado Cash to sever on-chain links; from leveraging Aave and Compound to mortgage "toxic assets" and exchange them for clean liquidity, to using THORChain, cross-chain bridges, and the UTXO structure to exponentially increase tracking difficulty, ultimately funneling into the USDT system on Tron and being converted into cash in the real world via over-the-counter (OTC) networks.
Throughout this process, there were no complex black-box operations; almost every step was "playing by the rules." Precisely because of this, what this path reveals is not a single vulnerability, but the structural tension within the DeFi system under its openness, composability, and uncensorability—when the protocol design itself permits these operations, so-called "fund recovery" is no longer a technical problem but a systemic boundary issue.
The Kelp DAO incident is therefore not just a security breach; it's more like a stress test of the crypto world's operating logic: it shows how hackers turn your money into their money, and it also shows why this system, in principle, struggles to prevent this process from happening.
As you know, on April 18, a North Korean hacker stole $292 million from Kelp DAO. Five days later, over half of it had vanished, fragmented across thousands of wallets, exchanged through unstoppable protocols, and ultimately funneled to a very specific destination.
The interesting part is: how to turn $292 million of documented stolen crypto assets, with no one able to stop it, into cash in Pyongyang's pockets.
The purpose of this article is to reveal why the modern crypto money laundering pipeline works, why it is structurally unstoppable, and what each laundered dollar ultimately buys.
Phase 1: Setup (Hours Before the Attack)
The attacker did not start with the direct theft. The Lazarus Group's playbook always begins with infrastructure preparation.
Approximately 10 hours before the attack, 8 brand new wallets were pre-funded via Tornado Cash—a mixer that severs the link between the source and destination of funds.
Each wallet received 0.1 ETH, used to pay for the Gas fees of all subsequent operations. Since these wallets' funds came from a mixer, they had no exchange KYC records, no historical transaction traces, and could not be linked to any known entity. Clean slates.
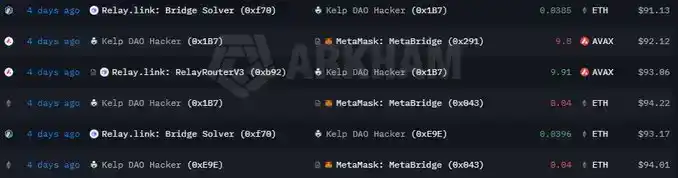
On the eve of the attack, the attacker initiated 3 cross-chain transfers from Ethereum mainnet to Avalanche and Arbitrum—clearly aiming to pre-fund Gas on these two L2s and test the bridge operations, ensuring smooth large transfers.
Phase 2: Theft
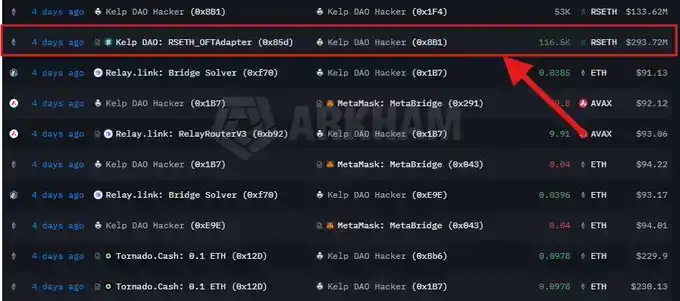
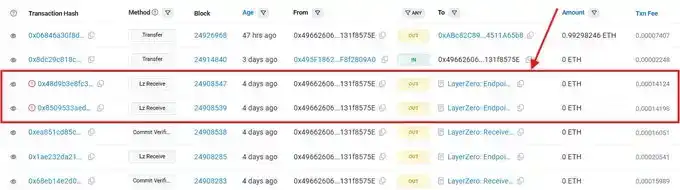
An independent attack initiation wallet (0x4966...575e) called a function named lzReceive on the LayerZero EndpointV2 contract. As the validator had been successfully deceived, this call was treated as a legitimate cross-chain message. Kelp's bridge contract, Kelp DAO: RSETH_OFTAdapter (Etherscan address: 0x85d...), subsequently released 116,500 rsETH to 0x8B1.
18% of the total circulating rsETH. Gone in one function call.
46 minutes later, at 18:21 UTC, Kelp's emergency multi-signature wallet paused the protocol. At 18:26 and 18:28 UTC, the attacker attempted two more operations in exactly the same way, each trying to steal about 40,000 rsETH (approx. $100 million each). Both were rolled back due to Kelp's timely shutdown. Had this not happened, the total theft could have approached $500 million.
Phase 3: Aave + Compound Operations
rsETH is a receipt token; once Kelp paused the bridge or blacklisted the stolen tokens, its value would immediately drop to zero. The attacker had only minutes to convert it into assets that could not be frozen. Kelp paused 46 minutes after the theft—it was already too late.
Selling $292 million of illiquid restaking tokens on the open market would crash the price by over 30% in minutes. So he did not choose to sell, but instead used DeFi lending protocols as money laundering tools for a quick exit.
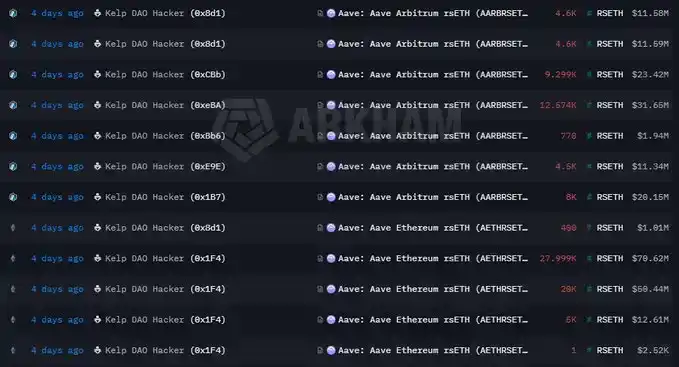
The receiving wallet 0x8B1 dispersed the 116,500 stolen rsETH to 7 other branch wallets. Each branch then entered Aave and Compound V3, deposited a portion of the rsETH as collateral, and borrowed ETH.
The cumulative positions of the 7 branches were as follows:
· Deposited Collateral: 89,567 rsETH
· Borrowed: approx. 82,650 WETH + 821 wstETH, totaling approx. $190 million in clean, liquid Ethereum assets
· The health factor for each branch was set between 1.01 and 1.03—the absolute upper limit allowed by the protocol before liquidation
The attacker exchanged this batch of $292 million worth of marked and nearly unsellable rsETH for $190 million worth of ETH. When this rsETH was eventually marked as nearly worthless (because Kelp's bridge became insolvent and unredeemable), the lending protocol's depositors bore the loss.
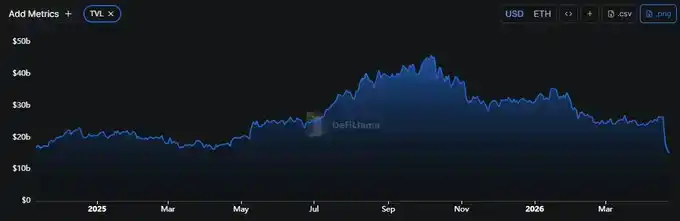
As the market realized Aave was holding over $200 million in bad debt, users panicked and withdrew funds. Aave lost $8 billion in TVL (Total Value Locked) within 48 hours. The largest DeFi lending protocol experienced its first true bank run—triggered by an attacker using it exactly as designed.
Phase 4: Fund Consolidation and Splitting
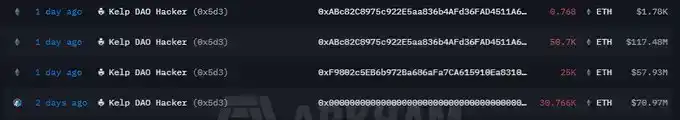
After completing the Aave/Compound borrowing, the 7 branches pushed the borrowed ETH to a third-layer consolidation wallet (0x5d3).
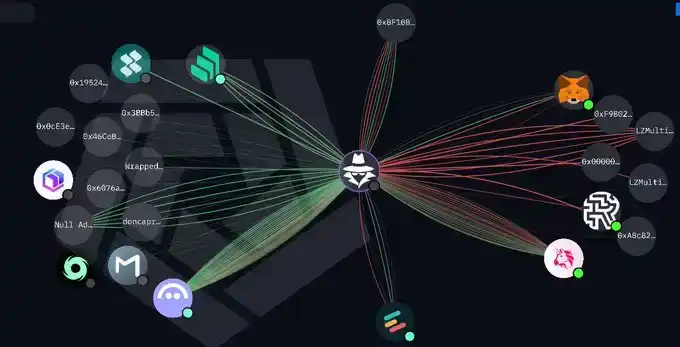
The operational cluster now showed a clear three-tier structure:
1. Receipt: 0x8B1 (also funded via Tornado Cash), received the original theft of 116,500 rsETH
2. Operations: 7 branch wallets funded via Tornado Cash, executed Aave/Compound operations
3. Consolidation: 0x5d3 re-aggregated the borrowed funds, approx. 71,000 ETH, unifying them for the laundering process
The funds were then distributed across two chains:
· 75,700 ETH remained on Ethereum Mainnet
· 30,766 ETH on Arbitrum (approx. $71 million)
The Arbitrum Security Council voted to freeze these assets on Arbitrum, moving the $71 million to a governance-controlled wallet that could only be unlocked by subsequent governance decisions.
Shortly after the freeze, the hacker moved the remaining ETH on Mainnet and accelerated the laundering process. These actions suggested he clearly did not anticipate Arbitrum taking such action.
Phase 5: First Wave of Laundering
Four days after the attack, 0x5d3 began to empty. Arkham tracked 3 independent transfers within hours.
The timing was deliberately chosen: Tuesday during European trading hours. US investigators were still resting, European compliance departments were dealing with Monday's backlog, and Asian exchanges were nearing close.
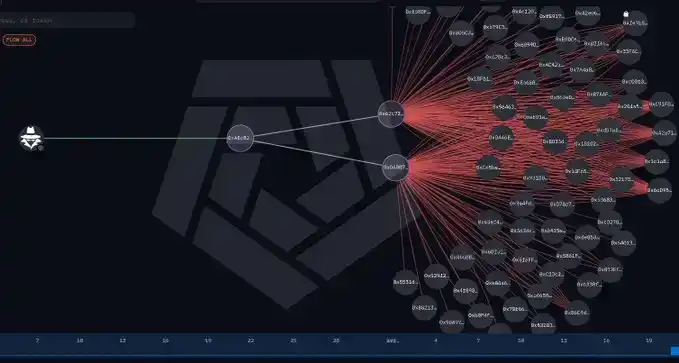
Then, the transfer pattern began to explode. Every first-wave destination immediately fragmented further: 0x62c7 pushed to about 60 newly generated wallets, 0xD4B8 pushed to another ~60. Within hours, the neat cluster of 10 wallets expanded to over 100 disposable addresses, all funded in parallel, each holding amounts small enough to evade detection.
Lazarus runs HD wallet scripts—a single seed phrase can mathematically derive thousands of new addresses in seconds,配合 a worker pool (Python + web3, ethers.js, or their own internal tools) to sign and broadcast the entire address tree in parallel. They have been iterating on this code since 2018.
By the end of this phase, the linearly traceable chain had disappeared. The operational cluster of 10 wallets exploded into over 100 fragmented wallets, with funds entering privacy channels simultaneously from dozens of independent entry points.
Phase 6: THORChain – The Escape Machine
The real breakpoint happened at THORChain.
THORChain is a decentralized protocol supporting cross-chain native asset swaps. You send ETH on Ethereum, it gives you BTC on the Bitcoin network.
On April 22 alone, THORChain's 24-hour swap volume reached $460 million. The protocol's normal daily volume is around $15 million. This single hack accounted for 30 times the protocol's normal usage in one day.
Within the same 24-hour window, the protocol generated $494,000 in revenue, shared among bonders (node operators), liquidity providers, the development fund, alliance integrators, and the marketing fund.
Simultaneously, funds also flowed through a set of smaller but complementary privacy rails:
· Umbra: A stealth address protocol on Ethereum. Allows sending funds to disposable addresses, only the recipient can calculate the address using a shared key. On-chain monitors cannot know the true destination. Initial activity of ~$78,000 was tracked here before tools lost the trail.
· Chainflip: Another cross-chain DEX, similar to THORChain.
· BitTorrent Chain: A low-cost, low-regulation sidechain connected to Tron.
· Tornado Cash: The same mixer used for the initial Gas pre-funding. The US Treasury Department sanctioned it in 2022.
Each layer of protocol increases the tracking cost by roughly a factor of 10. After 5 layers, forensic firms could theoretically still track every fragment, but the economic cost exceeds the recoverable value.
Phase 7: Bitcoin UTXO Fragmentation
Completing the ETH-to-BTC conversion via THORChain essentially turns the money into confetti.
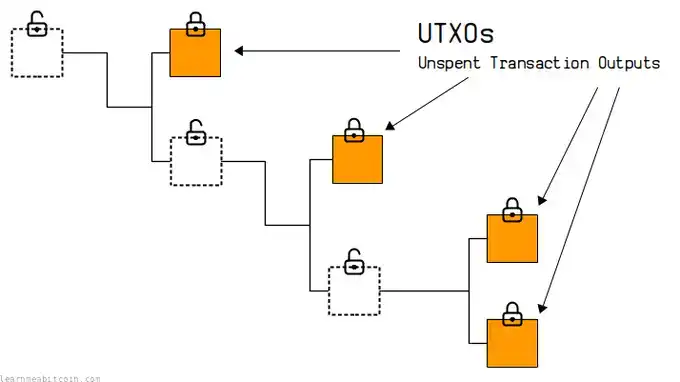
Ethereum uses an account model; your balance is a number attached to an address, simple and direct. Bitcoin is different; it uses a UTXO (Unspent Transaction Output) model—each UTXO is a specific chunk of a coin with a complete transaction history. Every time you spend Bitcoin, these chunks are split and recombined, forming new chunks.
Imagine tearing a $100 bill into 87 pieces, then tearing each piece into another 87 pieces, repeating this cycle 7 times. Technically, every fragment can be traced back to that original bill. Practically, no manual forensic team can track thousands of parallel chains in real-time and piece together the complete picture fast enough to take action.
Thus, THORChain accomplished two things simultaneously: moving funds across a boundary no sanction could cross, and fragmenting the funds into untraceable dust.
Phase 8: Tron USDT Rail
After passing through Bitcoin and privacy layers, the funds reconverged on the same endpoint: USDT on Tron.
Most people assume the main battlefield for money laundering is BTC; this is incorrect. The real main battlefield is USDT on Tron. Data shows USDT-Tron consistently ranks first in annual illicit crypto asset transaction volume, exceeding the sum of all other chains.
In this Kelp fund flow, the specific path was: cross-chain transfer from BTC to Tron, exchange for USDT, then multiple transfers between Tron addresses. Each hop on Tron costs mere pennies, allowing for another 10 layers of fragmentation.
Phase 9: Cashing Out – Crypto to Cash
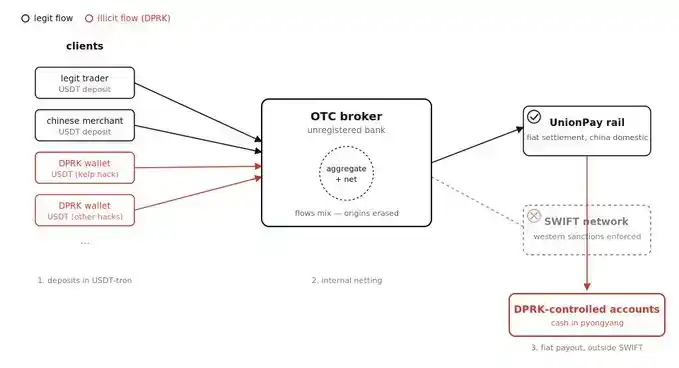
The endpoint of every hack sees the funds converted into fiat cash through a specific, well-known network of human intermediaries.
A group of over-the-counter (OTC) brokers active in mainland China and Southeast Asia receive USDT-Tron deposits and settle in local currency cash. These brokers are essentially unlicensed underground banks. They aggregate fund flows from multiple clients (compliant and non-compliant), net them internally, and settle in fiat via China's domestic payment network (UnionPay)—which operates completely outside the SWIFT system and Western sanction enforcement.
From accounts controlled by these brokers, funds flow into North Korean-controlled bank accounts, often held in the name of shell companies registered in Hong Kong, Macau, or third-party jurisdictions. From these accounts, funds are sent back to Pyongyang through Hawala-style informal clearing, physical cash transport, and procurement front companies.
The UN Security Council, FBI, and US Treasury Department have independently documented the final destination of these funds. North Korea's ballistic missile program, nuclear weapons development, and circumvention of international sanctions rely on the continuous support of such fund flows.
A 2024 UN report estimated that crypto hacks account for about 50% of North Korea's total foreign exchange income, making it the primary funding source for its weapons program—exceeding the sum of coal exports, arms sales, and labor exports.
[Original Title]