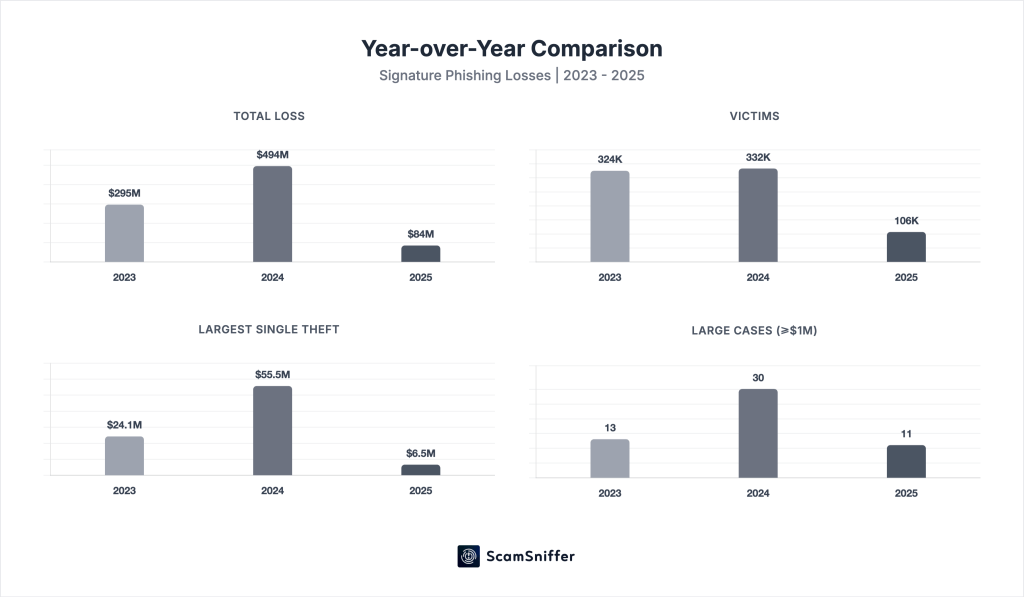
Phishing losses fell drastically in 2025 by over 83% compared to the previous year. However, the underlying data show that reduced figures do not translate to a decline in security threats.
Crypto Phishing Losses Down From $494M To $84M In 2025
A phishing attack occurs when an unsuspecting user is tricked into giving up sensitive information or signing off on malicious transactions. In the crypto space, signature phishing attacks are a major security concern and are facilitated using wallet drainers.
According to Web3 security outfit Scam Sniffer, total phishing losses in 2025 were valued at $83.85 million across 106,106 victims, representing respective drops of 83% and 68% from 2024. There were also 11 large cases of theft over $1 million compared to 30 in 2024. Meanwhile, the single largest theft was a $6.5 million loss via a permit signature attack in September, which was 8x lower than that of 2024.
While the latest figures represent a significant decline from the previous year, Scam Sniffer analysts state there is no direct translation to decreased market threat as losses moved in parallel with the market cycle. Therefore, losses increased or decreased in relation to the global crypto user activity.
Notably, monthly losses varied from $2.04 million in December to $12.17 million in August. However, Q3, which was the busiest market period, accounted for the largest portion (29% i.e $31 million) of the yearly losses. However, figures dropped to $13 million in Q4, as user activity cooled off.
Related Reading: Aave Founder Responds To Governance Tension With Strategic Plan – Details
EIP-7702 Emerges As Latest Phishing Signature Type
According to Scam Sniffer’s report, EIP-7702 exploitation emerged as a new threat in the signature-based wallet-drainer ecosystem. Leveraging account abstraction introduced in the Pectra upgrade in May 2025, attackers can bundle multiple malicious operations into a single signature.
Notably, the largest EIP-7702 losses, with two incidents culminating in $2.54 million, were recorded in August. Meanwhile, Permit/ Permit2 signature types lead the space, accounting for $8.72 million in losses across three major incidents, I.e. 38% of all large-case losses.
Beyond signature phishing types, Scam Sniffer also highlighted other phishing attack types that threaten the crypto space. The Bybit incident in February stands out, after the Lazarus group breached a Safe (Wallet) developer machine and launched a program that imitated the multi-sig interface, resulting in losses of $1.46 billion.
In conclusion, while reported signature phishing losses have declined, the threat landscape remains active. Moreover, the fall in trackable losses may suggest attackers are employing harder-to-track vectors such as private key breaches or targeted social engineering.