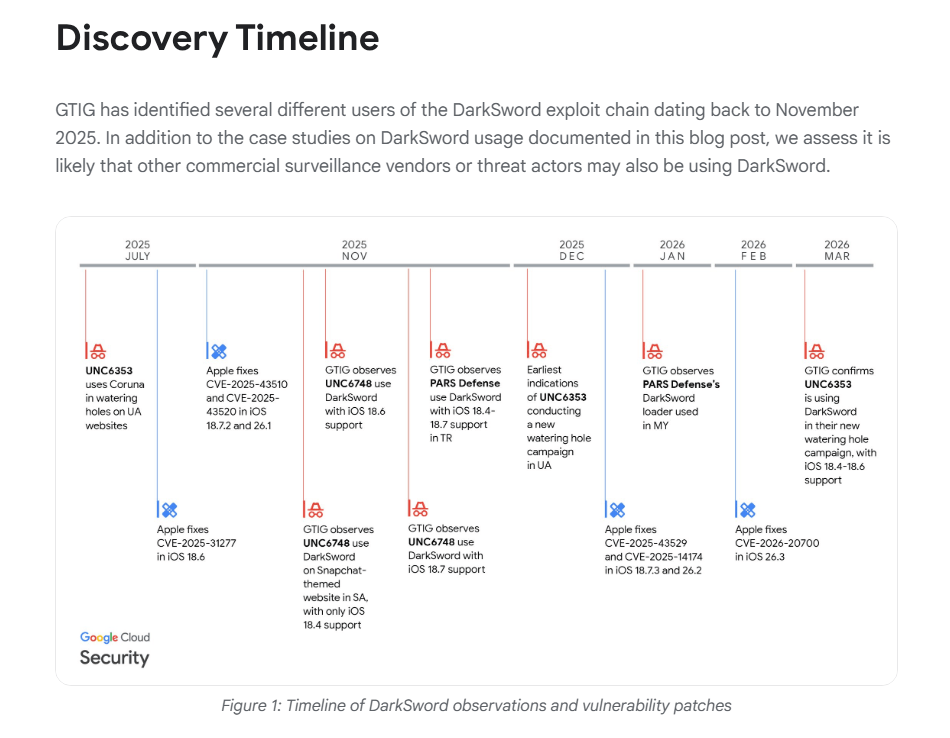
Private crypto holders took the heaviest losses from hacking, phishing, and digital theft attempts in February 2026, according to blockchain intelligence firm Nominis — and a newly identified strain of iOS malware may explain part of why individual users have become the preferred target.
Designed To Strike Fast And Disappear
Google Threat Intelligence has identified a JavaScript-based malicious tool called Ghostblade, built specifically to hit Apple iOS devices, extract sensitive data, and go quiet before anyone notices.
The software is one of six tools bundled inside a broader package researchers are calling DarkSword. Together, the tools are engineered to steal cryptocurrency private keys, messaging data, and personal information from infected devices.
Ghostblade runs once, takes what it needs, and stops. No persistent background activity. No extra software required to make it work. That design makes it far harder to catch than malware that keeps running after an infection.
Source: Google
The tool also covers its tracks in a specific way. After it finishes, it wipes crash logs from the compromised device. Those logs are what Apple normally collects to identify software problems and flag suspicious activity. Without them, Apple receives no signal that anything went wrong.
What Ghostblade Can Actually Access
The scope of what Ghostblade can pull from a device is wide. Based on Google’s report, the malware is capable of reaching messages from iMessage, WhatsApp, and Telegram.
It can also collect SIM card details, location data, multimedia files, and system-level settings. For crypto users, the most direct threat is private key exposure — the kind of access that gives an attacker full control over a digital wallet with no way to reverse transactions once funds are moved.
The DarkSword suite represents a new chapter in browser-based attacks aimed at the crypto space, with Ghostblade serving as one of its most technically refined components.
Hackers Shift Focus From Code To People
Total losses from crypto-related hacks dropped sharply in February, falling to close to $50 million from $385 million the month before, Nominis data shows. But that decline does not signal a safer environment.
Reports indicate the drop reflects a change in method, not ambition. Attackers moved away from exploiting code vulnerabilities and toward phishing schemes, wallet poisoning, and other approaches that rely on tricking users rather than breaking systems.
Fake websites built to mirror legitimate platforms are a common vehicle. Users who land on them and interact with any element can have credentials and keys lifted without realizing it.
The Ghostblade alert from Google arrives against that backdrop — a reminder that high-value individual users, not just exchanges or protocols, are firmly in the crosshairs.
Featured image from Unsplash, chart from TradingView