On March 12, the U.S. Department of the Treasury's Office of Foreign Assets Control (OFAC) announced sanctions against 6 individuals and 2 entities involved in a North Korea-led IT worker fraud network. The announcement stated that these participants systematically defrauded U.S. companies to provide funding for weapons of mass destruction programs, with the amount involved in 2024 alone approaching $800 million.
https://home.treasury.gov/news/press-releases/sb0416
Sanctions Details
According to the U.S. OFAC disclosure, North Korea-controlled IT teams used forged documents, stolen identities, and fabricated personas to conceal their true identities and gain employment at legitimate companies in the U.S. and other countries. The North Korean government seizes the vast majority of these overseas IT workers' salaries, obtaining hundreds of millions of dollars in funding to support its weapons of mass destruction and ballistic missile programs. In some cases, North Korean-linked personnel also secretly implanted malicious software into corporate networks to steal proprietary and sensitive information.
This round of sanctions targets a total of 6 individuals (Nguyen Quang Viet, Do Pyong Kyong, Hoang Van Nguyen, Yun Song Guk, Hoang Minh Quang, York Louis Celestino Herrera), identified as providing substantial assistance to North Korean IT workers through cryptocurrency exchange, money laundering, bank account opening, IT business对接 (liaison), etc.; and 2 corporate entities (Amnokgang, Quangvietdnbg), identified as key operators and facilitators of the IT worker fraud network.
Sanctioned Address Analysis
This sanctions action locked a total of 21 cryptocurrency addresses. According to the OFAC notification, from mid-2023 to mid-2025, Quangvietdnbg's CEO Nguyen Quang Viet exchanged approximately $2.5 million worth of cryptocurrency for the North Korean side, identifying cryptocurrency as a key channel for North Korean IT workers to transfer funds and evade sanctions.
Analysis was conducted on these 21 addresses using the on-chain anti-money laundering analysis platform Beosin KYT and the tracking investigation tool Beosin Trace, with results as follows:
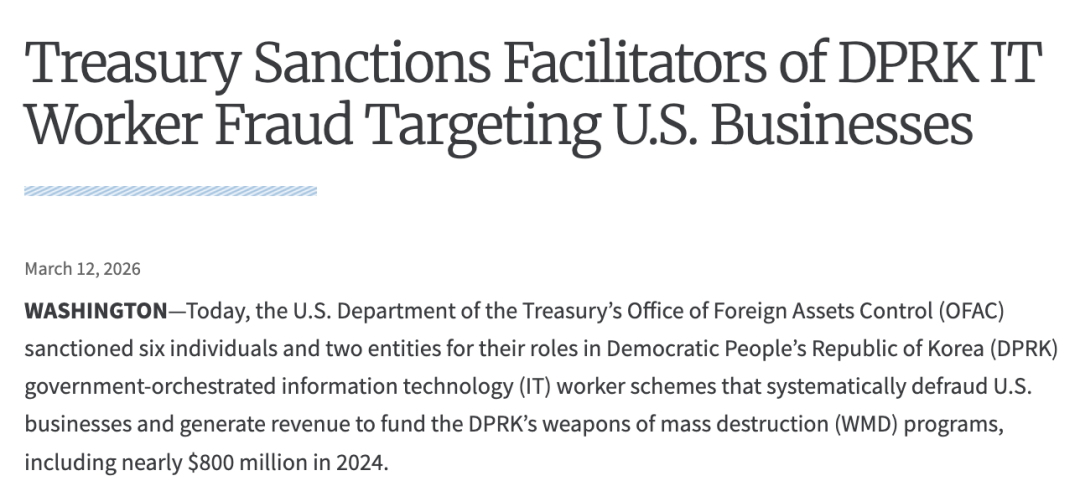
YUN, Song Guk (North Korean national, head of IT workers in Boten, Laos)
ETH:
0xb637f84b66876ebf609c2a4208905f9ddac9d075
0x95584C303FCd48AF5c6B9873015f2AD0ca84EaE3
According to Beosin Trace statistics, approximately 200,851 USDT previously flowed out to various centralized exchanges.
HOANG, Minh Quang (Collaborated to complete IT service transactions exceeding $70,000)
BTC: bc1qyy5pt5cx3zth8xlj92lq5y87dh8xv3nwgs4ncq
Previously, 0.57462 BTC flowed into a Coinbase account.
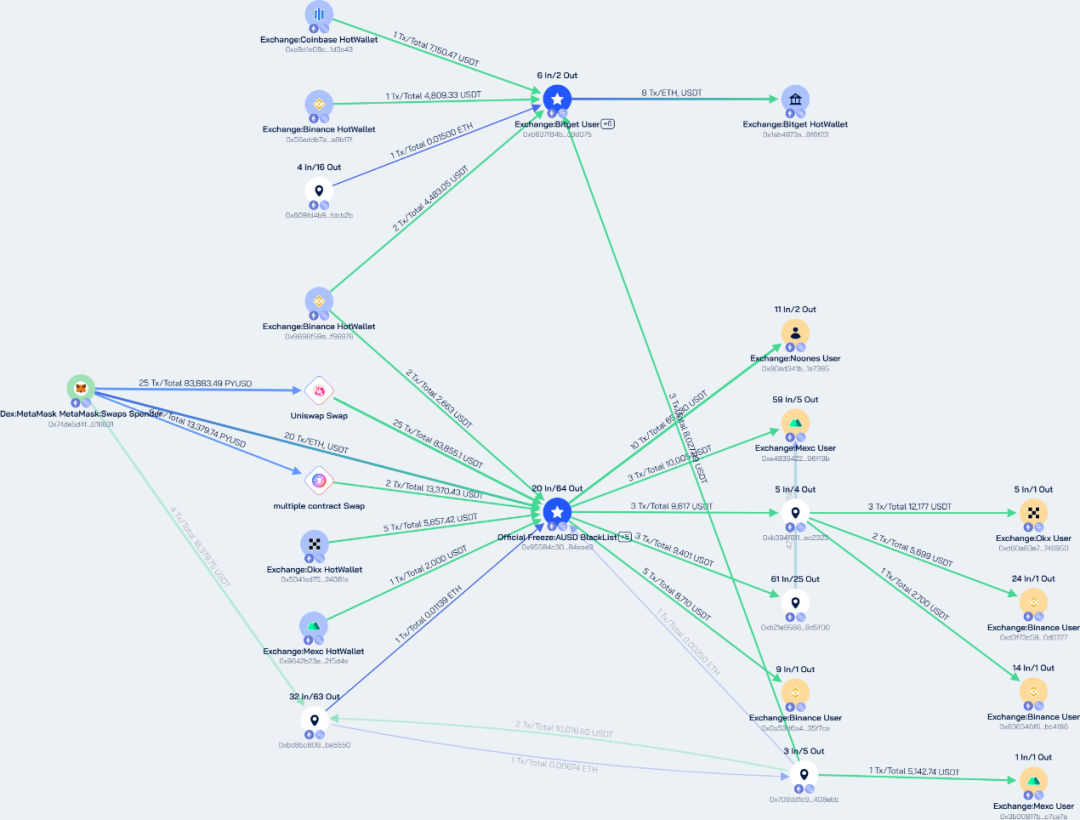
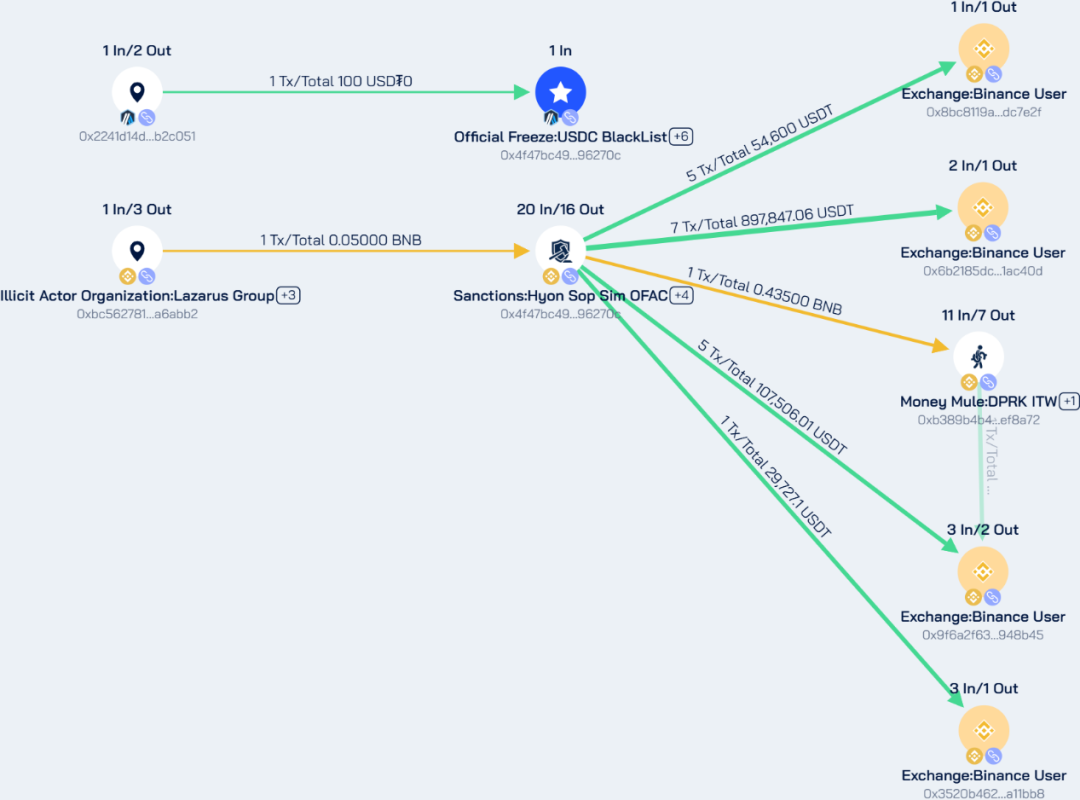
SIM, Hyon Sop (Representative of North Korea's Kwangsong Bank in China, 11 new addresses added)
Originally frozen address (ETH network):
0x4f47bc496083c727c5fbe3ce9cdf2b0f6496270c
This address had a liquid flow volume of 21,937,732.52 USDT and 2,071,126.59 USDC. Currently, 58,148.62 USDT remains dormant at this address.
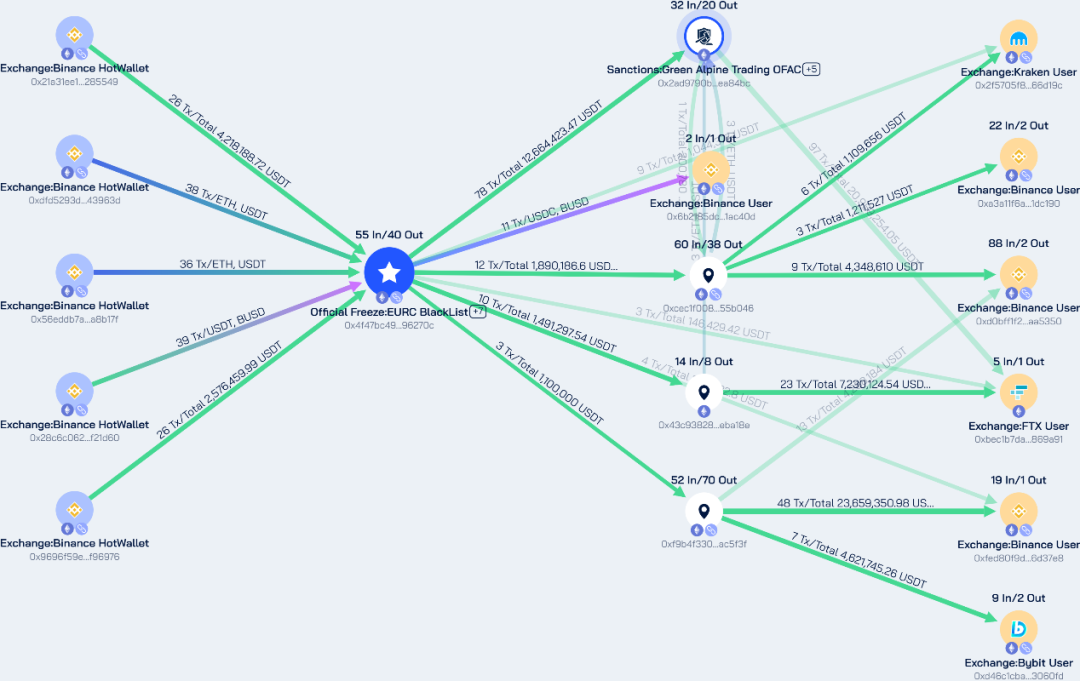
Newly sanctioned addresses (ETH network):
0xd04E33461FEA8302c5E1e13895b60cEe8AEfda7F
0x76EA76CA4Eb727f18956aB93445a94c5280412B9
0xFb3eFf152ea55D1BfA04Dbdd509A80fD7b72cdEB
0xFda1Ec4A6178d4916b001a065422D31EBE5F62FF
0x747AFB5c7A7fc34B547cD0FDEbf9b91759C5a52b
Fund flow diagram as follows:
Approximately 98,139.11 USDT, 21,300 USDC, and 0.51268 ETH flowed out.
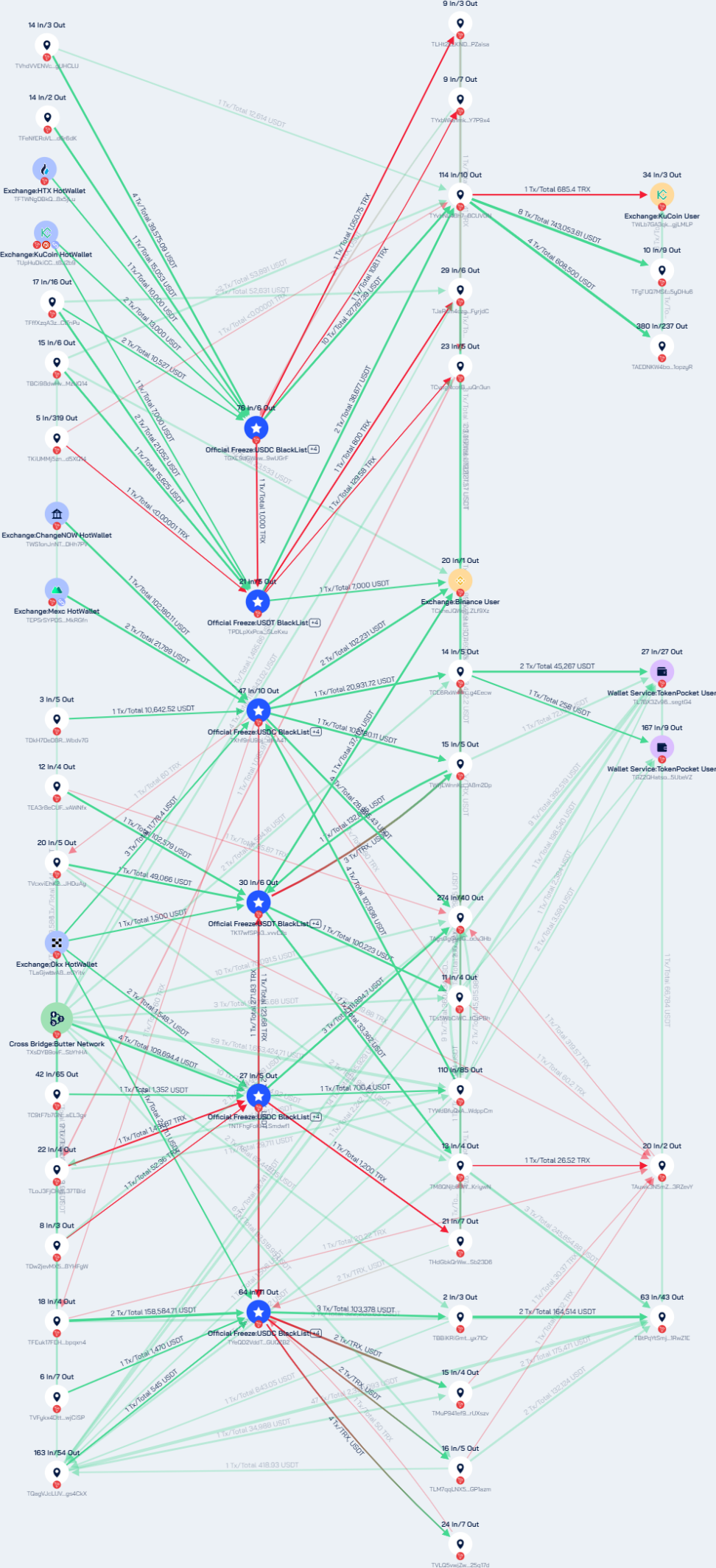
New TRX addresses:
TPDLpXxPcaSsupEZ3yrVksmNkYP5SLeKxu
TGXE9dGWawjfd3xqFSho1h1bRbRv9wUGrF
TNTFhgFoKH4srBMiWbfrVFqP2AThSmdwf1
TXhf9nU9bjo1j9z5qEesHdr6gtdndfnA4T
TK17wfSPp32RWrnzZPrGpv7TxdNFvvvE2s
TYeQD2VddTZ9NkFkAnT9DD8cUGetGUQZB2
Approximately 6,236.74 TRX and 999,014.46 USDT flowed out.
Same address cross-chain:
ARB: 0x4f47bc496083c727c5fbe3ce9cdf2b0f6496270c
BSC: 0x4f47bc496083c727c5fbe3ce9cdf2b0f6496270c
1,133,025.26 USDT, 935,943.84 BUSD, and 17,811.05 USDC flowed out to various centralized exchanges.
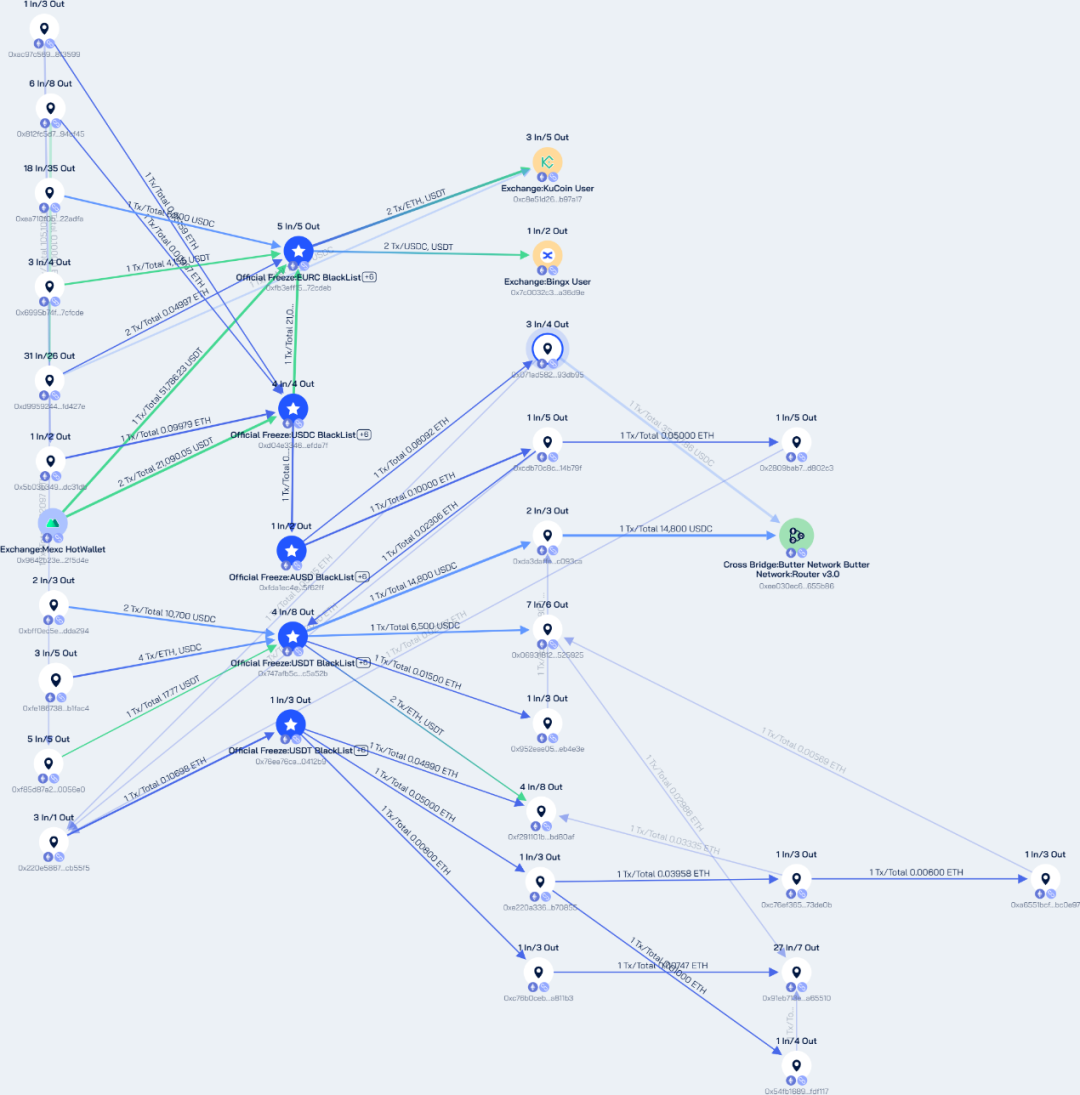
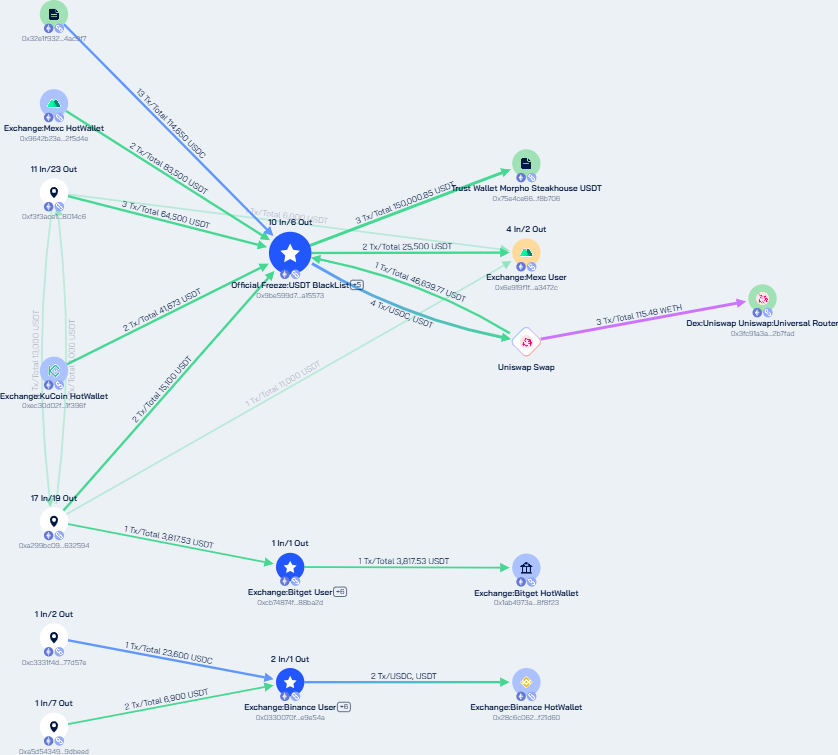
AMNOKGANG TECHNOLOGY DEVELOPMENT COMPANY
ETH:
0xcB74874f1e06Fcf80A306e06e5379A44B488bA2D
0x0330070FD38Ec3bB94F58FA55D40368271E9e54A
0x9Be599d7867f5E1a2D7Ec6dB9710dF2b98A15573
A total of approximately 205.02 ETH, 274,531.15 USDT, and 228,496.97 USDC were involved. Among these, 96.05 ETH remains dormant in address 0x9be599d7867f5e1a2d7ec6db9710df2b98a15573.
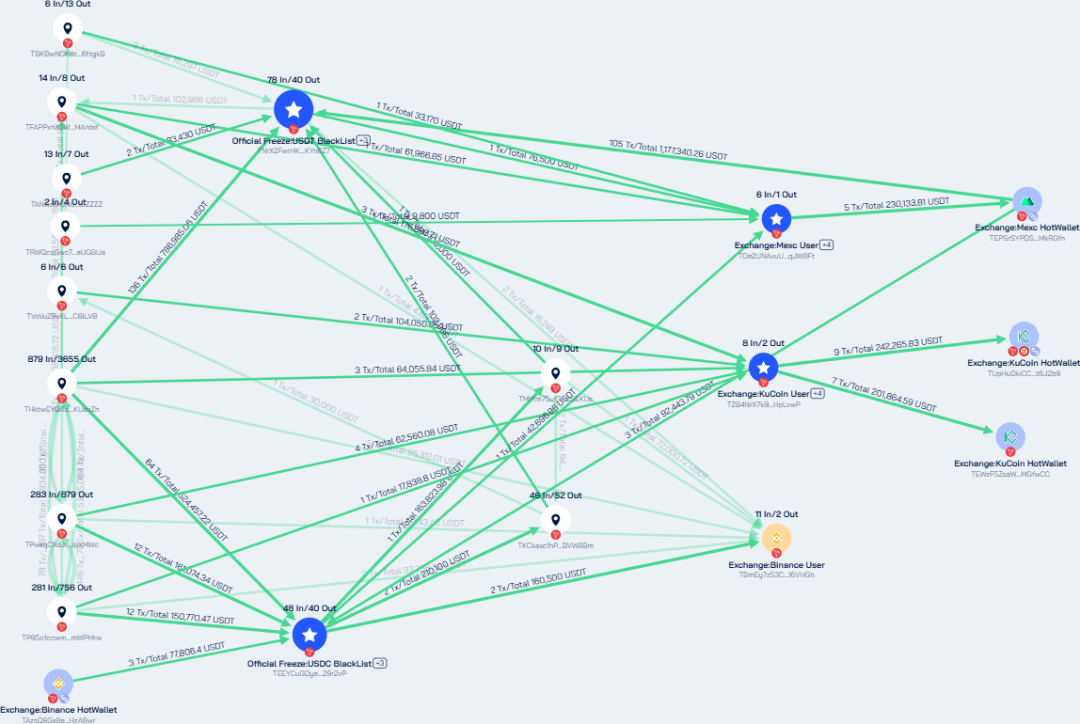
Tron network
TNrX2FwrHKoo4XACGkmSzqeK4pdnKYn6Z7
TEEYCuGDyeNkuDj4u6GQRXxXo3Nh29r2vP
TZB4NrX7k9ZsV6PRc1GigAztLL8WHpLvwP
TDe2UNAvuUnTbbDo7518eMe3TXN5qJW8Ft
2,744.75 TRX and 4,941,817.62 USDT flowed out to various centralized exchanges.
Beosin Anti-Money Laundering Recommendations
This action is another measure by the U.S. Treasury Department to continuously combat North Korea's use of cryptocurrency to evade sanctions. For the virtual asset industry, how to conduct anti-money laundering compliance screening and identify addresses involved in high-risk funds has become a key capability for Virtual Asset Service Providers (VASPs).