Original Title: 'Help! My robot vac is stealing my Bitcoin': When smart devices attack
Original Author: Felix Ng, Cointelegraph
Original Compilation: Deep Tide TechFlow
Smart robotic vacuums and other smart home devices are easily hacked and can be used to record your password inputs or seed phrases.
Imagine waking up one morning to find your robotic vacuum out of control, your refrigerator demanding a ransom, and your cryptocurrency and bank account funds wiped out.
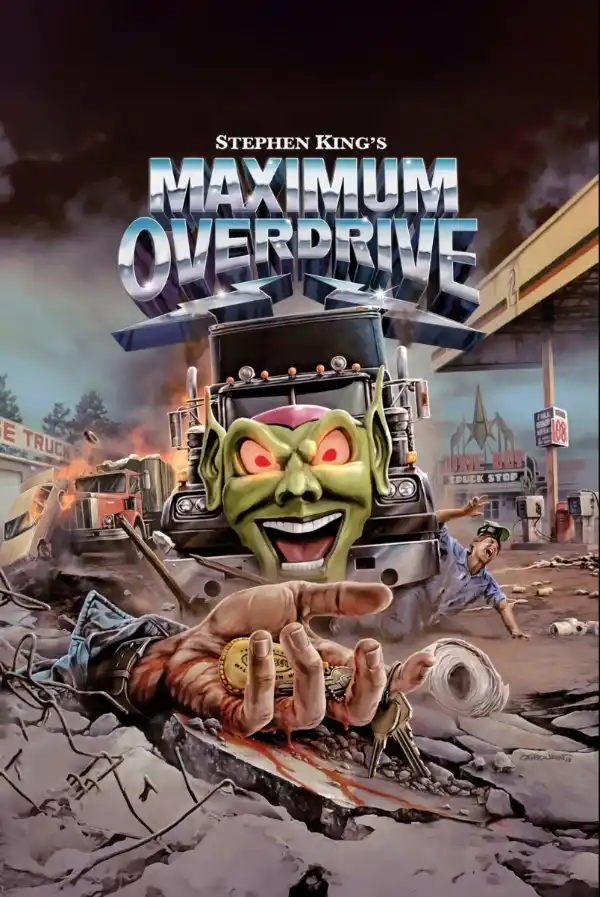
This isn't a scene from Stephen King's 1986 horror film "Maximum Overdrive"—a story about a rogue comet triggering a global machine killing spree.
Instead, it's the real risk that could occur if hackers infiltrate your computer through the smart devices in your home. With the global number of IoT devices expected to reach 18.8 billion and an average of about 820,000 IoT attacks occurring daily, the likelihood of this scenario is increasing.
"Insecure IoT devices (such as routers) can become entry points into home networks," said Tao Pan, a researcher at blockchain security company Beosin, in an interview.
As of 2023, the average U.S. household has 21 connected devices, and one-third of smart home device consumers have experienced a data breach or scam in the past 12 months.
"Once hacked, attackers can move laterally to access connected devices, including computers or phones used for cryptocurrency transactions, and can also capture login credentials between the device and the exchange. This is particularly dangerous for users who use APIs for cryptocurrency trading," he added.
So, what exactly can hackers steal from your home, and what damage can they cause?
"Magazine" has collected some of the most bizarre hacking incidents from recent years, including a case where an access control sensor was hacked to mine cryptocurrency. We've also compiled some practical tips to protect your data and cryptocurrency security.
Hacking the Coffee Maker
In 2019, Martin Hron, a researcher at cybersecurity company Avast, demonstrated how easily hackers can access home networks and their devices.
He chose a simple target: remotely hacking his own coffee maker.
Hron explained that, like most smart devices, the coffee maker used default settings that allowed the device to connect to WiFi without a password, making it easy to upload malicious code to the machine.
"Many IoT devices first connect to the home network through their own WiFi network, which is only used to set up the device. Ideally, consumers would immediately secure this WiFi network with a password," Hron explained.
"But many devices do not come with a password to protect the WiFi network from the factory, and many consumers do not set one," he added.
Original video link: Click here
"I could do whatever I wanted because I could replace the firmware, the software that operates the coffee maker. And I could replace it with whatever I wanted. I could add features, delete features, and also break through the built-in security measures. So, I could do whatever I wanted," he said in a video released by Avast.
In his demonstration, Hron displayed a ransom note through the coffee maker, locking the device until a ransom was paid.
You could choose to turn off the device, but that would mean you'd never get coffee again
(Avast/YouTube)
However, beyond displaying a ransom note, the coffee maker could also be used for more malicious actions, such as turning on the heater to create a fire hazard or喷射沸水 to threaten the victim.
More frighteningly, it could quietly become an entry point into the entire network, allowing hackers to monitor your bank account information, emails, and even crypto seed phrases.
Hacking the Casino Fish Tank
One of the most famous cases occurred in 2017 when hackers transferred 10GB of data by hacking into a connected fish tank in the lobby of a Las Vegas casino.
The fish tank was equipped with sensors for regulating temperature, feeding, and cleaning, which were connected to a computer on the casino's network. The hackers entered other areas of the network through the fish tank and sent data to a remote server in Finland.
The fish tank might have looked something like this
<极m>(Muhammad Ayan Butt/ Unsplash)
Although the casino had deployed常规的 firewalls and antivirus software, the attack was successful. Fortunately, the attack was quickly identified and handled.
Nicole Eagan, CEO of cybersecurity company Darktrace, told the BBC at the time: "We stopped it immediately, and no damage was done." She added that the growing number of internet-connected devices means "it's a hacker's paradise out there."
Door Sensors Can Also Secretly Mine
In 2020, in offices closed globally due to the COVID-19 pandemic, cybersecurity company Darktrace discovered a secret cryptocurrency mining operation—hackers were using a server controlling office biometric access for illegal mining.
The clue to this incident came from the server downloading a suspicious executable file from an external IP address that had never appeared on the network before. Subsequently, the server repeatedly connected to external endpoints associated with the Monero mining pool.
This type of attack is called "cryptojacking." Microsoft's Threat Intelligence team found more such cases in 2023, with hackers targeting Linux systems and smart devices connected to the internet.
Microsoft's investigation found that attackers launch attacks by brute-forcing Linux and IoT devices connected to the internet. Once inside the network, they install backdoor programs and then download and run cryptocurrency mining malware. This not only causes electricity bills to soar but also directs all mining proceeds directly into the hacker's wallet.
Cases of this cryptojacking are层出不穷, with one of the latest involving embedding cryptojacking code into fake 404 HTML pages.
Hacking Smart Devices: Destroying the Power Grid
More frighteningly, security researchers at Princeton University once proposed a hypothesis: if hackers could control enough high-energy-consuming devices, such as 210,000 air conditioners, and turn them on simultaneously, it could cause a power outage equivalent to the population of California—about 38 million people.
(Unsplash)
These devices would need to be concentrated in a certain part of the power grid and turned on simultaneously to cause certain power lines to overload, damaging or triggering the protective relays on the lines to shut them off. This would shift the load to the remaining lines, further stressing the grid and ultimately triggering a chain reaction.
However, this scenario would require precise malicious timing, as grid fluctuations are common during special weather conditions (such as heat waves).
The Robotic Vacuum Is Watching You
Last year, robotic vacuums in various parts of the United States suddenly started up on their own. It turned out that hackers had discovered a serious security vulnerability in a Chinese-made Ecovac robotic vacuum.
According to reports, hackers could remotely control these devices, using them to scare pets, shout profanities at users through built-in speakers, and even use built-in cameras to spy on users' homes.
An image from the live feed of a hacked Ecovac robotic vacuum
(ABC News)
"A serious problem with IoT devices is that many manufacturers still pay insufficient attention to security issues," said cybersecurity company Kaspersky.
It goes without saying that if hackers have video footage of you entering passwords or recording seed phrases, the consequences would be disastrous.
How to Protect Yourself from Smart Device Hacks?
Look around, and you might find that almost every device in your home is connected to the internet—robotic vacuums, digital photo frames, doorbell cameras. So how do you keep your Bitcoin safe?
One option is to adopt the method of professional hacker Joe Grand: completely avoid using any smart devices.
"My phone is the smartest device in my home, but even then, I use it reluctantly, only for navigation and communication with family," he once told "Magazine." "But smart devices? Absolutely not."
Avast's Hron said the best approach is to ensure you set passwords for smart devices and avoid using default settings.
Other experts recommend using a separate guest network for IoT devices, especially those that don't need to share a network with computers and phones; disconnecting devices when not in use; and keeping software up to date.
Additionally, there are paid search engines that can help users view the connected devices in their homes and potential vulnerabilities.
Recommended Reading:
RootData 2025 Web3 Industry Annual Report
Binance Power Shift: The Dilemma of a 300 Million User Empire
Beyond Stablecoins: Circle Releases 2026 Strategy Report, Internet Financial System Has Fully Emerged
InfoFi Narrative Collapses, Kaito, Cookie, and Others相继关停 Related Products