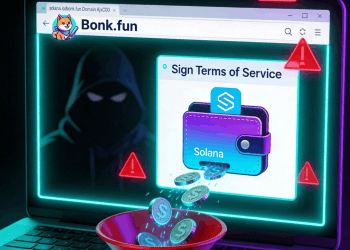
Artículos Relacionados con Exploit
El Centro de Noticias de HTX ofrece los artículos más recientes y un análisis profundo sobre "Exploit", cubriendo tendencias del mercado, actualizaciones de proyectos, desarrollos tecnológicos y políticas regulatorias en la industria de cripto.

Technology Trends
- 160 Curated Skills, Workflows & Open-Source Projects: The Ultimate Claude Advanced List
- 2Tiger Research: What AI Services Do Crypto Companies Offer?
- 3Existing AI Agents Are All Pleasing Humans, None Truly Know How to 'Survive'
- 4Slow Down: The Answer in the Age of Agents
- 5Dialogue with MIT Economist: Don't Panic About 'AI Doomsday Theory', Verification Capability is a Scarce Resource
Project Updates
- 1Coinbase disables Ronin trading as Ethereum L2 migration enters execution phase
- 2Ethereum Foundation locks $46 mln in ETH – Here’s why the market isn’t reacting
- 3Cardano Founder Hoskinson Just Released A Free Book On Zero-Knowledge
- 4Whale Buyers Focus on Ozak AI After Price Appreciation Above 1,300% From Initial Presale Rounds Signals Strong Demand
- 5Tether Hires Big Four Auditor, USDT Enters Verifiable Stage for the First Time