Author: 0x2333, The BlockBeats
A hair dryer, an unattended weather sensor, and two meticulously calculated operations.
On April 6 and April 15, 2026, a weather probe at the Météo-France station at Paris Charles de Gaulle Airport was heated with a portable heating device, causing the temperature readings to spike abnormally within a short period. The actual temperature at Charles de Gaulle Airport did not experience such fluctuations, but the prediction market betting on "Paris Daily Maximum Temperature" on Polymarket settled as usual. In two operations, a total of $34,000 in rewards was transferred from the platform to an anonymous account opened just two days before the incident.
This was not a typical crypto attack. It did not exploit any smart contract vulnerabilities, nor did it target any decentralized governance processes. The entire attack tool was just a hair dryer.
Temperature Spikes 4°C in 12 Minutes, How Did a Single Probe Deceive the Global Prediction Market?
Between 6:30 PM and 6:42 PM on April 6, the temperature reading at the Charles de Gaulle Airport weather station climbed 4°C in 12 minutes, peaking at 22.5°C, before rapidly dropping back within 5 minutes. The actual temperature in Paris that day did not show such drastic fluctuations, and no similar anomalies were recorded at other nearby weather stations.
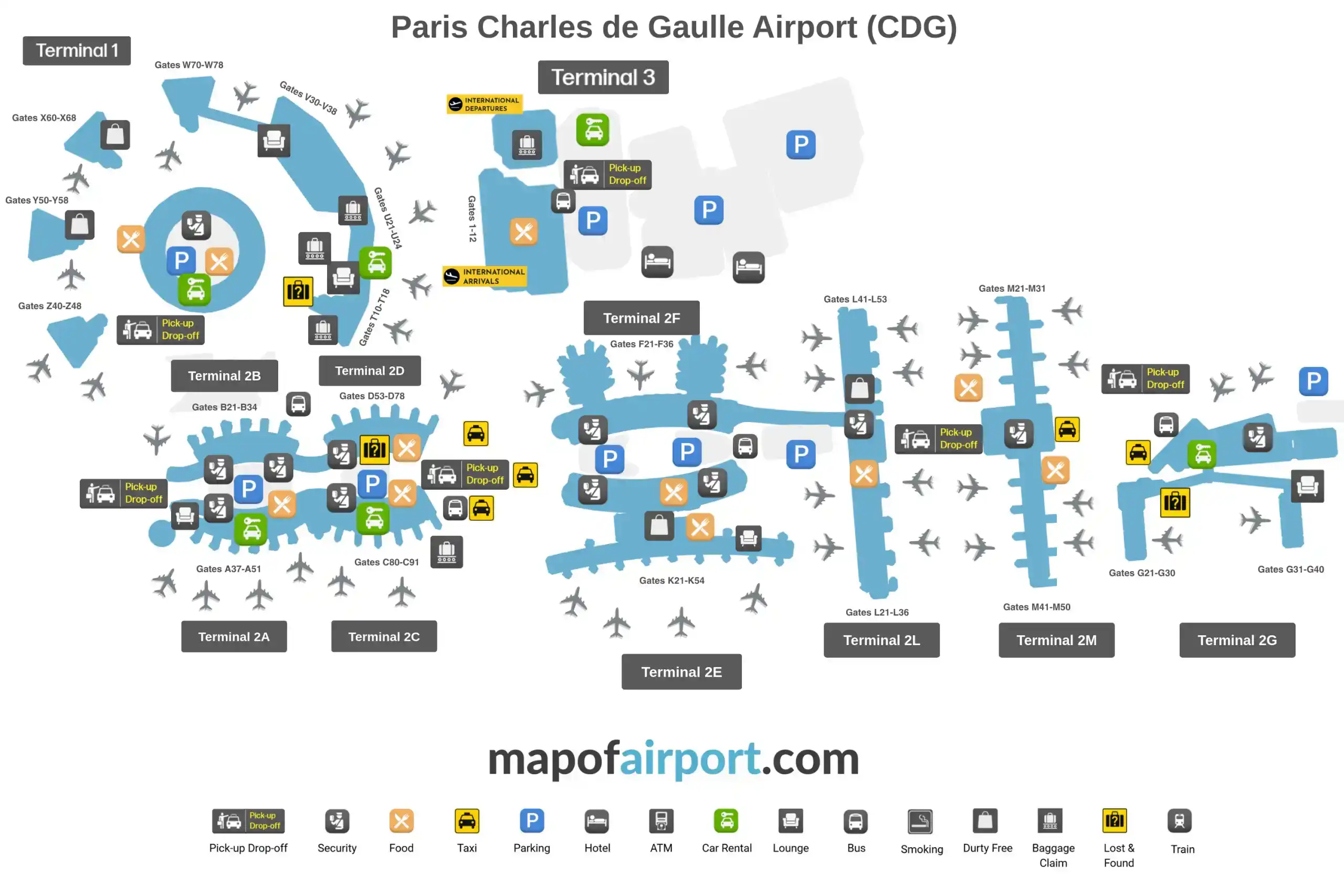
This weather station (code: LFPG) is located at the edge of the Charles de Gaulle Airport runway, near a public area adjacent to a road. Its relatively open physical location made it possible for the suspect to approach the sensor and perform physical intervention.
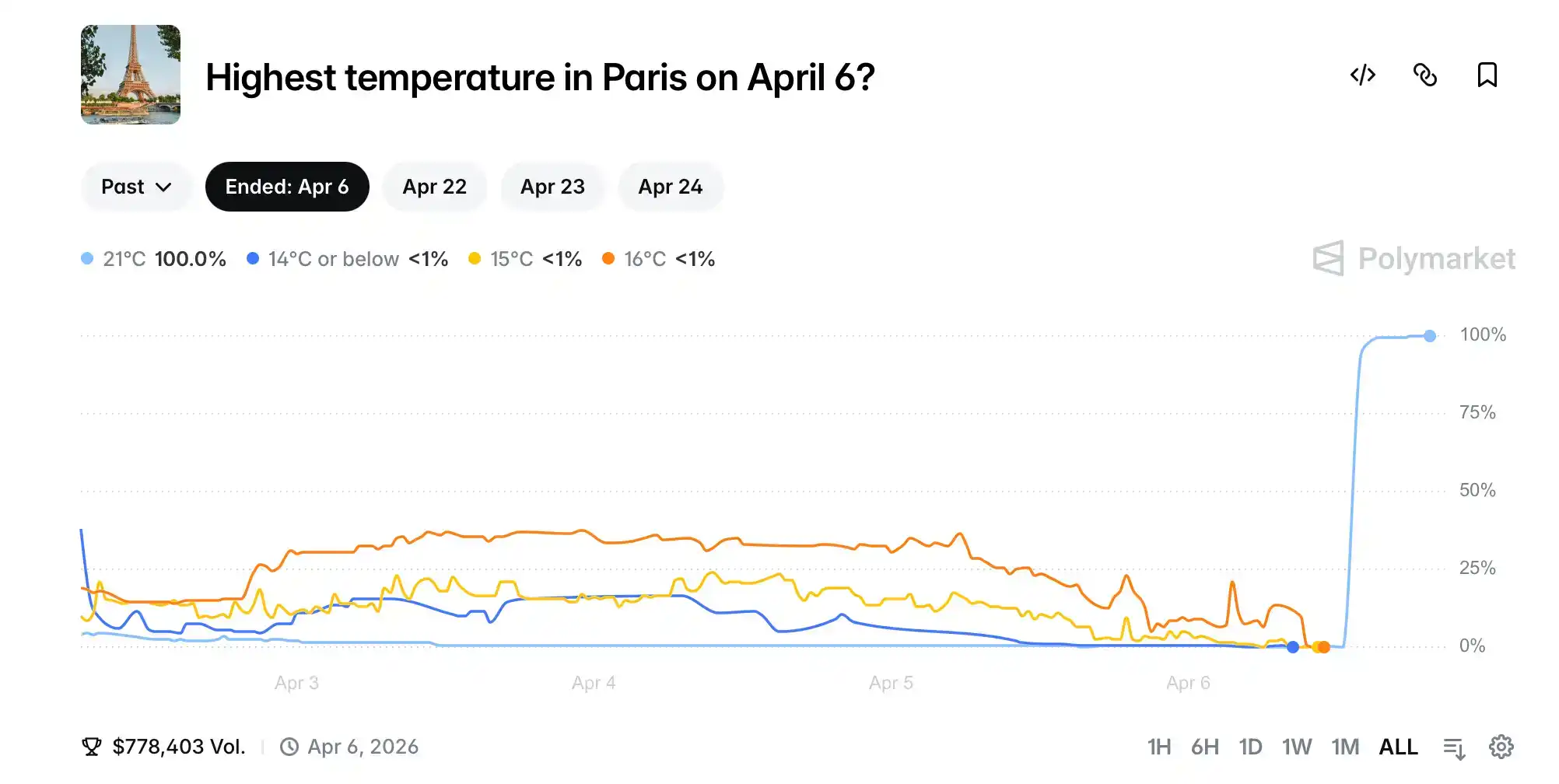
This brief period of "high temperature"恰好 hit the "21°C" option on Polymarket, a previously almost ignored outcome. After the abnormal data was accepted by the platform as the day's maximum temperature, it settled to Yes. An account behind it took away approximately $14,000.
Nine days later, around 9:30 PM on April 15, almost the exact same script played out again. On a cloudy, windless night, the temperature reading at Charles de Gaulle Airport bizarrely climbed to 22°C. The probability of the "22°C" option on Polymarket soared from 0.1% to 95% in just 30 minutes. A second prize of over $20,000 flowed into the same account.
Paul Marquis, founder of French E-Meteo Service and a meteorologist, provided a technically almost irrefutable judgment: "There was no change in wind direction or relative humidity at the time, and no anomalies were recorded at other surrounding weather stations. Physical intervention is the most reasonable explanation, such as placing a heating device near the sensor probe."
Météo-France subsequently conducted a physical inspection of the sensor, found evidence of tampering, and formally filed a criminal complaint with the Roissy Air Transport Gendarmerie. The charge is "disrupting the operation of an automated data processing system." Under French law, this offense carries a maximum penalty of 7 years imprisonment and a fine of 300,000 euros.
The profile of the involved account is also questionable. It was created on April 4, 2026, just 48 hours before the first operation. The initial funds were only a few dozen dollars, transferred via a cryptocurrency exchange. It almost exclusively participated in the "Paris weather" market, specifically buying extremely low-probability "high temperature" options. After two successful attempts, the funds were quickly transferred through mixers and decentralized exchanges, making on-chain tracking significantly more difficult.
On one side is a common household hair dryer, retailing for less than 30 euros. On the other side is a global climate prediction market with a daily trading volume exceeding $2 million. The extreme asymmetry between the cost of the attack and the potential gain.
The abnormal data was first discovered by local French weather enthusiasts on the Infoclimat forum. The event was subsequently spread to the English-speaking crypto community, followed by reports from French media such as Le Monde, Le Figaro, and BFMTV. Polymarket officials have not issued any public statement on the matter, nor have they revoked the already paid $34,000 reward.
Rule Vulnerability, How Does a Single Sensor Reading Decide Six-Figure Prizes?
The true protagonist of this incident is not the hair dryer, but rather the settlement rules of Polymarket's weather market.
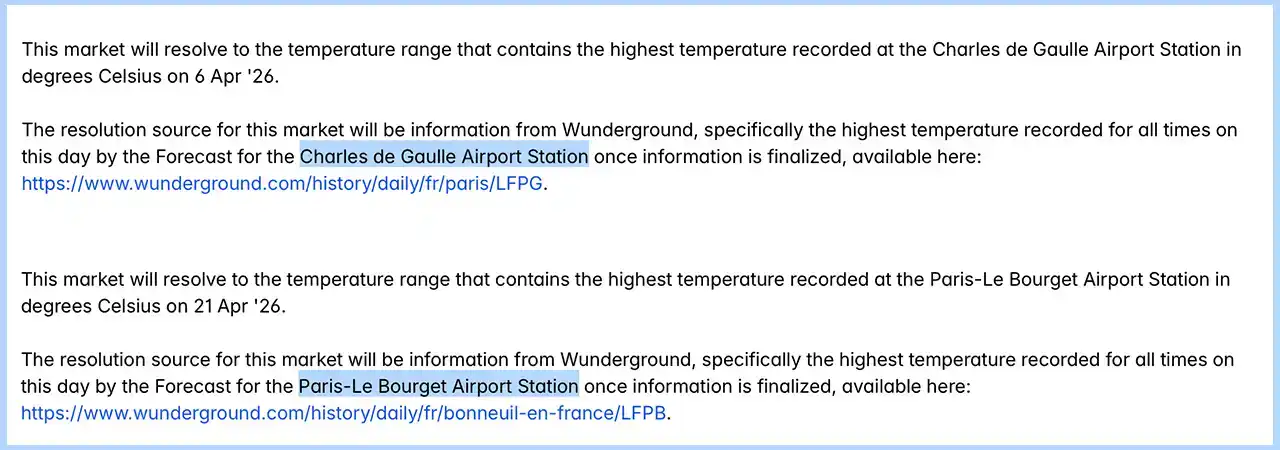
Polymarket's weather markets have grown rapidly in recent years, with the number of active markets now reaching 173, covering temperature, precipitation, hurricanes, tornadoes, earthquakes, volcanoes, and even pandemics. Among them, the "Paris Daily Maximum Temperature" market uses an extremely simple settlement mechanism, locking the data source to the readings from one specific weather station hosted on the Wunderground website.
Before this incident, this station was the Charles de Gaulle Airport weather station (code LFPG), with temperature rounded to the nearest whole degree Celsius. Most crucially, the market settles immediately after the data is finalized, and "does not consider any subsequent data revisions."
This last point means that even if Météo-France later discovers data anomalies and revises the historical records, Polymarket will still pay out rewards based on the contaminated original reading. The rules are written clearly and executed without ambiguity.
The vulnerability thus clearly presents itself in three points:
First, a single point of failure. The settlement of the entire six-figure prize pool relies entirely on the reading from one sensor. Polymarket did not design mechanisms for multi-station weighting, redundant comparison, or anomaly熔断. The so-called "data source" is that single metal probe by the runway at Charles de Gaulle Airport.
Second, physical accessibility. The Charles de Gaulle Airport weather station is located near the edge of the runway, adjacent to a public area next to a road, allowing any ordinary person to approach within meters of the probe. This geographical detail lowers the barrier to "physical intervention" from theoretical possibility to an almost zero-cost practical operation.
Third, the rigidity of the settlement mechanism. The invalidity of post-hoc revisions means that once an attack is successful, there is no possibility of "reversal." The rules ensure the certainty of settlement on one hand, but also guarantee that manipulation, once successful, is irreversible.
Fibo Crypto analyst Victor gave this technique a technically elegant name: "Physical Oracle Attack." Unlike previous "Digital Oracle Attacks" that targeted UMA governance votes and relied on large-scale token voting to manipulate oracle results, physical oracle attacks bypass the entire on-chain logic, acting directly on the first mile of the data pipeline—the metal probe in the real world.
On April 17, two days after the incident was exposed, Polymarket quietly completed a rule change, switching the settlement data source for the Paris weather market from Charles de Gaulle Airport (LFPG) to Paris-Le Bourget Airport (LFPB). The switch was not accompanied by any official announcement, public technical explanation, or any response to the two manipulations that had already occurred.
Changing a probe is much easier than publicly admitting a vulnerability. Polymarket's weather market was initially designed as a mirror, reflecting the market's collective judgment about the future. But when the image in the mirror is valuable enough, the odds steep enough, and the probe accessible enough, someone will always walk over with a 30-euro hair dryer and blow their desired result into it.