New malware has been discovered that targets crypto wallets and browser extensions while disguising itself as game cheats and mods, says cybersecurity firm Kaspersky.
Kaspersky reported on Thursday that it had uncovered a new infostealer dubbed “Stealka,” which targets Microsoft Windows user data.
Attackers have used the malware, which was discovered in November, to hijack accounts, steal cryptocurrency, and install crypto miners on their victims’ computers while masquerading as video game cracks, cheats, and mods.
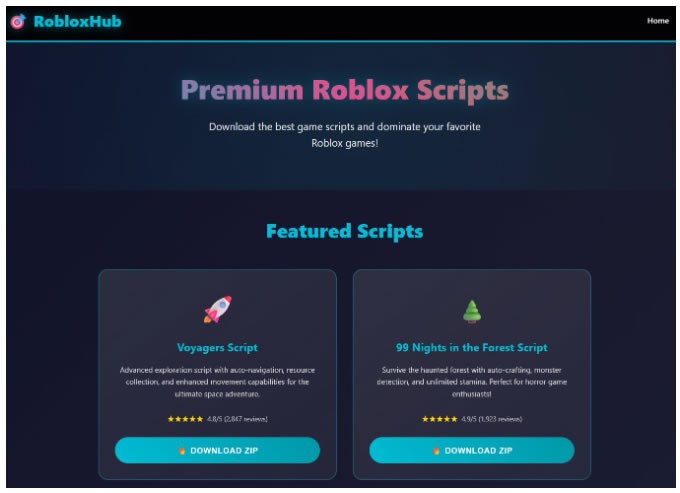
The malicious software has been distributed through legitimate platforms like GitHub, SourceForge, and Google Sites, and disguised as game mods, especially for Roblox, and software cracks for applications such as Microsoft Visio.
Sometimes, attackers go a step further, possibly using artificial intelligence tools, and creating entire fake websites that look “quite professional,” said Kaspersky researcher Artem Ushkov.
Crypto wallets and extensions targeted
Ushkov noted that Stealka has a fairly “extensive arsenal of capabilities,” but is particularly dangerous because its prime target is data from browsers built on the Chromium and Gecko engines.
This puts over 100 different browsers at risk, including popular ones such as Chrome, Firefox, Opera, Yandex, Edge, Brave, and many others.
Related: Hackers are exploiting a JavaScript library to plant crypto drainers
Its primary targets are autofill data, such as sign-in credentials, addresses, and payment card details, but it also targets the settings and databases of 115 browser extensions for crypto wallets, password managers, and 2FA (two-factor authentication) services.
Some of the 80 crypto wallets targeted include Binance, Coinbase, Crypto.com, SafePal, Trust Wallet, MetaMask, Ton, Phantom, Nexus, and Exodus.
Kaspersky also said the messaging apps, including Discord, Telegram, Unigram, Pidgin, and Tox, were also at risk, as were email clients, password managers, gaming clients, and even VPN applications.
Avoid pirated software and game mods
To stay protected, Kaspersky recommended using reliable antivirus software and password managers to avoid storing passwords in browsers. It also cautioned against using pirated software and unofficial game mods.
Cloudflare reported last week that more than 5% of all emails sent worldwide contain malicious content, and more than half of those contained a phishing link, while a quarter of all HTML attachments were found to be malicious.
Magazine: Big questions: Would Bitcoin survive a 10-year power outage?