Original | Odaily Planet Daily (@OdailyChina)
Author | Azuma (@azuma_eth)
On April 19th, Beijing time, DeFi security suffered another major blow.
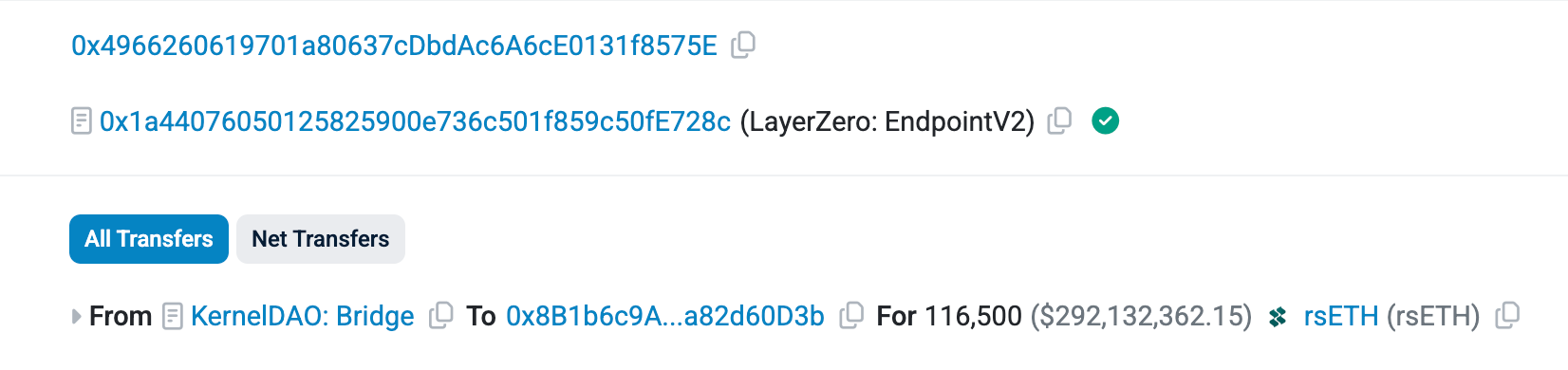
On-chain data shows that around 1:35 this morning, the rsETH bridge contract of Kelp DAO, the second-largest liquid staking protocol based on LayerZero, was suspected to be exploited by hackers, resulting in a loss of 116,500 rsETH, valued at approximately $292 million.
Further tracing the on-chain records, the attacker's address received 1 ETH in initial funds from the mixing protocol Tornado Cash about 10 hours before the incident. Subsequently, this address called the lzReceive function on the LayerZero EndpointV2 contract. This call triggered Kelp's bridge contract, transferring 116,500 rsETH to another attacker address.
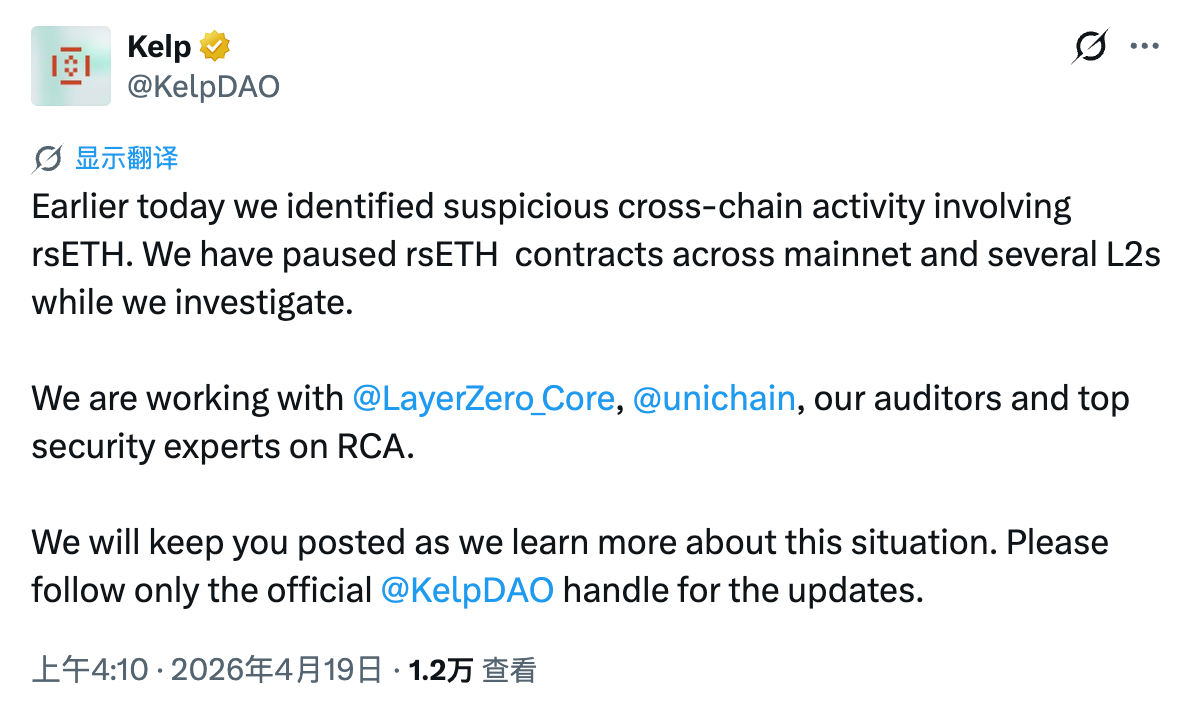
About two and a half hours after the incident, Kelp DAO officially confirmed the attack on X: "Earlier today, we detected suspicious cross-chain activity involving rsETH. During the investigation, we have paused the rsETH contracts on the mainnet and multiple Layer 2s. Our auditors are working with security experts from LayerZero and Unichain to closely monitor the situation. We will keep you updated on the latest developments. Please follow official channels."
After the incident, various DeFi projects and security agencies analyzed the cause. An analysis by D2 Finance was frequently cited within the community — LayerZero Scan marked the source's counterpart as Kelp DAO, meaning the message came from a legitimately deployed endpoint contract by Kelp itself, and this path had previously recorded 308 message nonces. Therefore, the root cause of this attack was a "compromise of the source chain private key."
Steven Enamakel, a developer at TinyHumans AI, added that the contract was secured by only a 1/1 validator set (DVN), meaning a single erroneous transaction from the validator was enough to cause the issue.
Hacker Escapes via Aave, Suspected Bad Debt Incurred
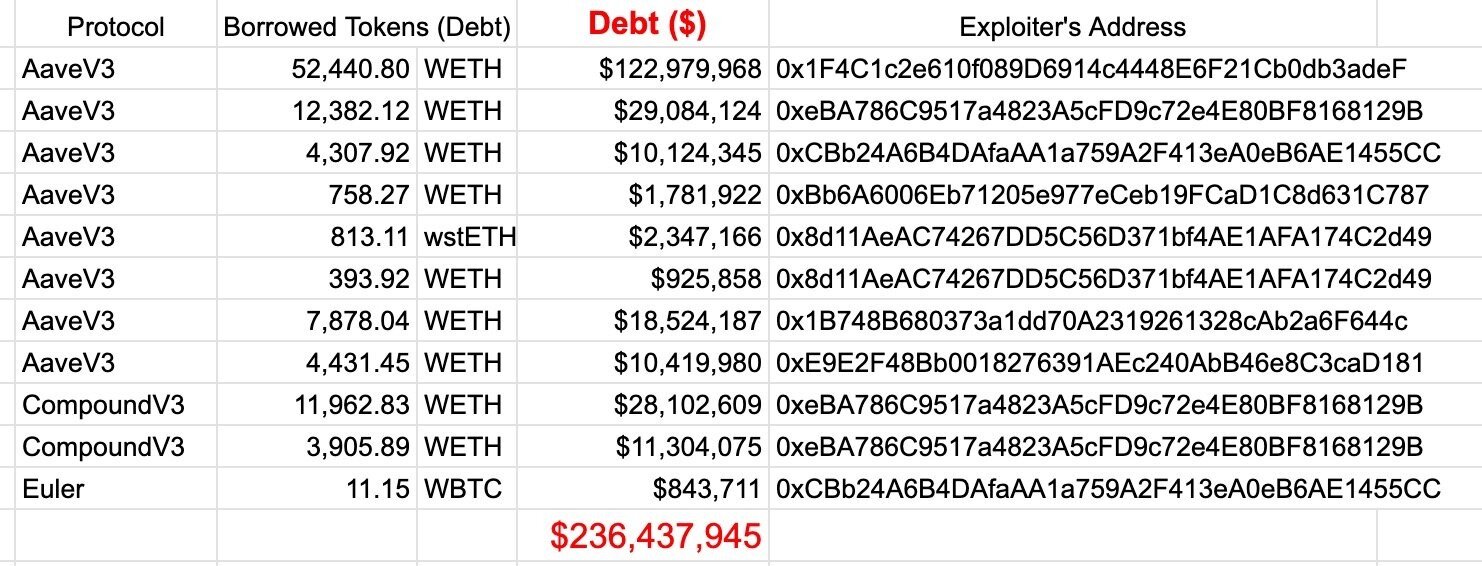
Due to the limited trading liquidity of rsETH itself, the hacker's chosen escape strategy was to route through lending protocols like Aave, using the stolen rsETH as collateral to borrow more liquid wETH.
According to monitoring by PeckShield Alert, as of 4:30 this morning, the hacker's address had deposited the stolen rsETH into lending protocols including Aave V3, Compound V3, and Euler, borrowing a significant amount of WETH, with a total debt exceeding $236 million — of which Aave alone accounted for $196 million, Compound $39.4 million, and Euler only $840,000.
Following the incident, Aave promptly froze the rsETH market on Aave V3 and V4. The team subsequently issued an official statement on X: "Aave contracts have NOT been exploited. The exploit is related to rsETH. Freezing rsETH is to prevent new rsETH deposits and borrowing against rsETH collateral while the situation is assessed. We are reviewing the borrows of rsETH that occurred on Aave post-exploit and will share more details as soon as possible."
Shortly after the initial statement, Aave updated the post, adding: "Should the protocol accrue bad debt from this incident, we will explore avenues to cover the shortfall."
As of the time of writing, the specific amount of bad debt caused by this incident is still unclear.
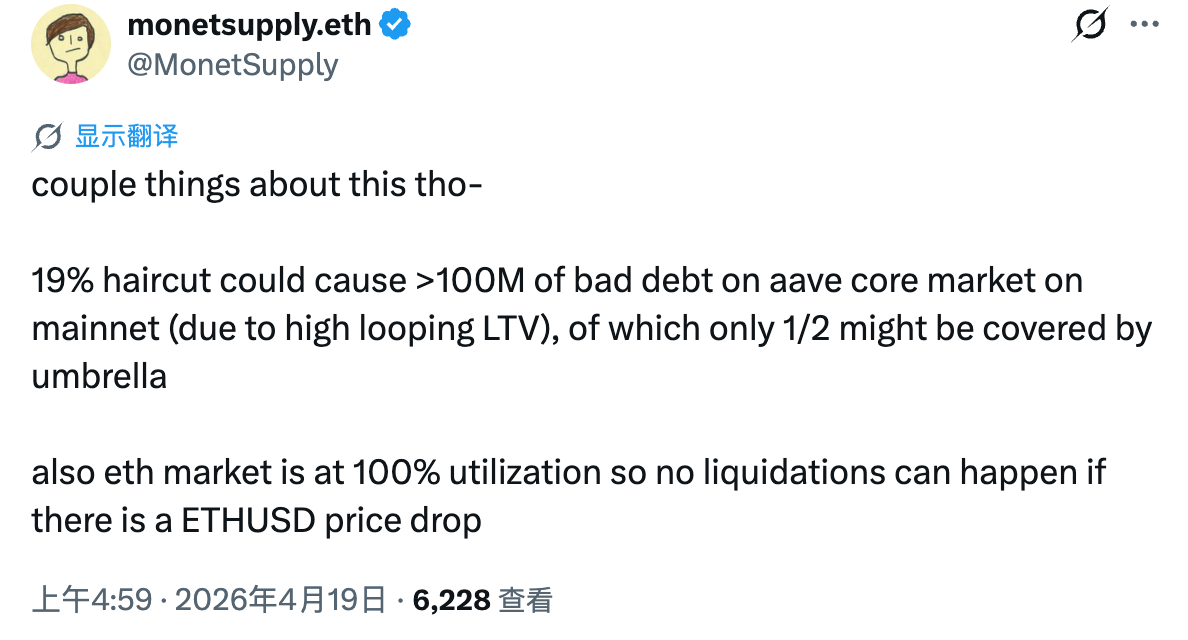
monetsupply.eth, Head of Strategy at Aave's direct competitor Spark, stated that if rsETH experiences a 19% devaluation (the stolen amount represents 19% of the total rsETH supply), Aave could potentially incur over $100 million in bad debt due to highly leveraged recursive borrowing.
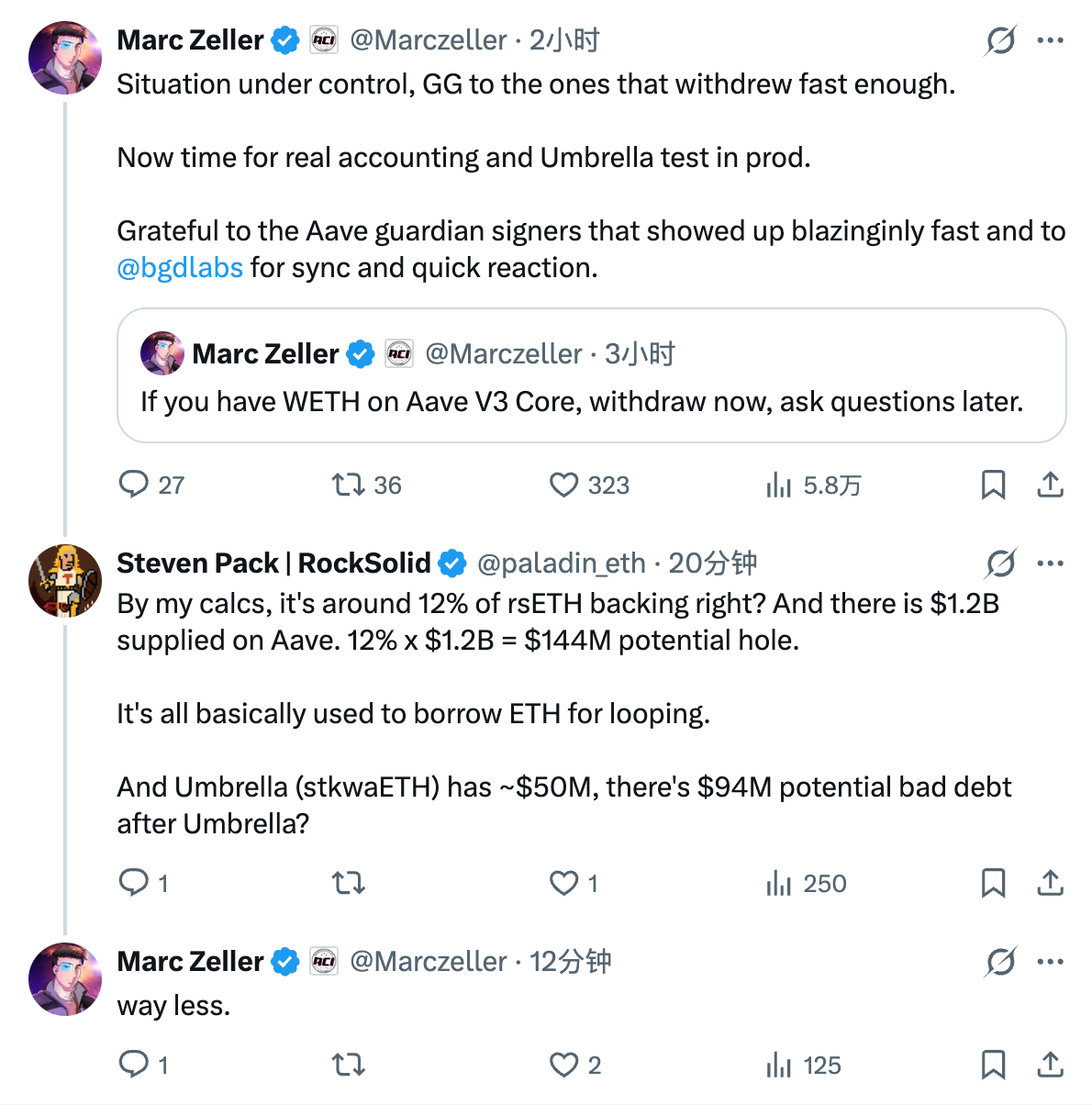
However, Marc Zeller, founder of the representative Aave governance team Aave Chan Initiative (ACI) (who has announced his departure from Aave in July due to governance disagreements), offered a different perspective. Zeller initially advised users to quickly withdraw WETH from Aave V3 to avoid losses and confirmed that the USDC and USDT markets on Aave were unaffected. In response to another user's speculation that "bad debt could reach hundreds of millions," he stated: "Far less than that figure."
But Marc Zeller also mentioned that it was time to test Umbrella in a real production environment. Umbrella refers to Aave's automatic safety module, essentially a pool of funds to handle bad debt. Users can deposit assets into it for higher incentives, but the pool also bears potential losses if the protocol incurs bad debt.
Aave protocol data shows that Umbrella currently holds approximately $50 million worth of WETH that could be used to address potential bad debt from this incident, but it is uncertain whether this will be sufficient to cover the shortfall.
Affected by this event, AAVE's price fell sharply by nearly 10% in the short term, trading at around 104.6 USDT at the time of writing.
Another Hundred-Million-Dollar Security Incident in April
This is not the first massive security incident this month.
As early as April 1st, the Solana ecosystem derivatives trading protocol Drift Protocol was attacked, losing up to $280 million (see 《April Fool's Joke? Drift Protocol Hacked for Over $280 Million, Possibly Becoming Solana Ecosystem's Second Largest DeFi Heist》).
Afterwards, Drift Protocol directly blamed "North Korean hackers" for the theft, but fortunately, institutions like Tether pledged $147.5 million for user compensation, giving users some hope for reimbursement.
Just over ten days later, another, even bigger hacking incident erupted. How will this one be resolved?
Is There Any Safe Place Left in DeFi?
Security issues in DeFi are intensifying.
On one hand, there are continuous hacking incidents; on the other, there are persistent security threats posed by AI like Mythos (refer to 《Odaily Interview with Yu Xian: How Does the Leak of Anthropic's Nuclear-Grade New Model Affect Crypto Security Offense and Defense?》). For DeFi users, the previous countermeasure was to concentrate funds towards well-audited, reputable top-tier protocols. But now, even a top-tier protocol like Aave, which retail users subconsciously considered extremely unlikely to have problems, is indirectly affected. Where can users move their funds?
Personally, it is currently not advisable to keep large amounts of funds on-chain. If there is a genuine need, please ensure proper diversification and isolation of positions.
As of the time of writing, many details about this incident remain unclear. Odaily will continue to follow the developments of the event. Please stay tuned.