A Crypto platform confirmed that their main domain website had been hacked, which exposed its users to a wallet draining exploit.
A No-Fun Crypto Hijack
It is a truth universally acknowledge that, no matter the size of a global geopolitical crisis, hackers will continue to ravage through the crypto market. This time, the victim was memecoin issuance platform Bonk.fun. In a March 12 post on the social network X, Tom (@SolportTom), one of its operators, warned the users not to interact with the domain “until further notice”, as hackers had injected a crypto wallet drainer on it:
Do not use the https://t.co/4xXs3cMJx0 domain until further notice, hackers have hijacked a team account forcing a drainer on the DOMAIN.
URGENT.
— Tom (@SolportTom) March 12, 2026
The official X account of the Solana token launchpad, backed by Raydium and the BONK community, also announced the hack and echoed Tom’s striking warning:
A malicious actor has compromised the BONKfun domain, do not interact with the website until we have secured everything.
— BONK.fun (@bonkfun) March 12, 2026
Who Is Affected And How
Tom explained that the phishing scam set up a fake “Terms of Services” (TOS) signature prompt which, when signed, allowed the drainer to move the unaware user’s funds. According to Tom, the only users compromised were the ones who interacted with the fake TOS. He clarified that neither previously connected users nor traders of bonk fun tokens on third-party terminals were affected. He also assured that the security breach was spotted early so “the losses are minimal to date”:
To answer the concerns I’m seeing:
1. No if you connected to bonk fun in the past you’re not affected
2. No if you trade bonk fun tokens on terminals etc you’re not affected
3. The only people affected were people who signed a fake TOS message on the bonkfun domain after...
— Tom (@SolportTom) March 12, 2026
This is not a Raydium or BONK smart contract exploit, but the case of a Web2 infrastructure failure that bled directly into Web3. This type of domain hijacking and phishing drainer scripts work by the attackers taking over the frontend and presenting normal-looking prompts that abuse wallet approvals.
A Pattern Of Exploited Vulnerabilities
In recent years, approval-phishing and “fake UI” attacks have stolen billions of dollars: one Chainalysis investigation reported the amount of $14 billion in on-chain scam inflows in 2025, with projections pointing above the $17 billion as more wallets continued to be identified.
As scam revenues grow and AI‐driven impersonation scales, crypto security in 2026 is less about the perfect code and more about defending everything around it: from domains to social accounts, employees and users decision-making. In February last year, attackers hijacked Pump.fun’s X account to push a fake PUMP token, as covered by our sister website NewsBTC. Not too long ago, OG trader Sillytuna was drove out of the crypto market after a multimillion-dollar theft that combined online address poisoning and offline violent actions.
The times are testing traders online and offline, both inside and outside the bloc. As the crypto landscape grows more complex, traders would do well to heighten their caution: prefer direct contract interaction or trusted aggregators, and use tools to monitor and regularly revoke token approvals.
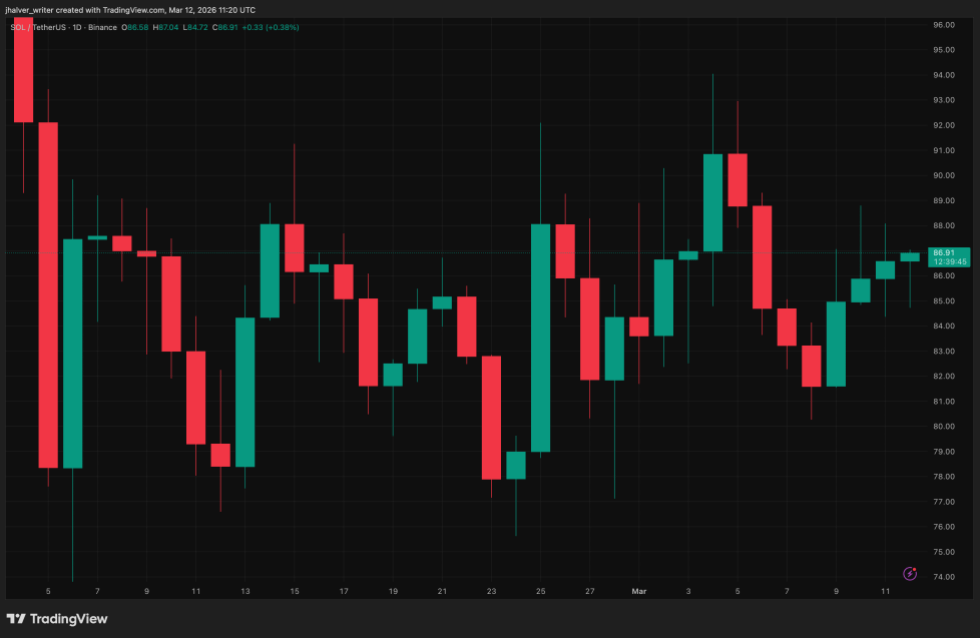
SOL’s price trends to the upside on the daily chart. Source: SOLUSDT on Tradingview
Cover image from Perplexity, SOLUSDT chart from Tradingview