Background Introduction
On January 27, 2026, we monitored an attack on the PGNLZ project on the BNB Smart Chain:
https://bscscan.com/tx/0xa7488ff4d6a85bf19994748837713c710650378383530ae709aec628023cd7cc
After detailed analysis, the attacker continuously launched attacks against the PGNLZ project on January 27, 2026, resulting in a loss of approximately 100k USD.
Attack and Incident Analysis
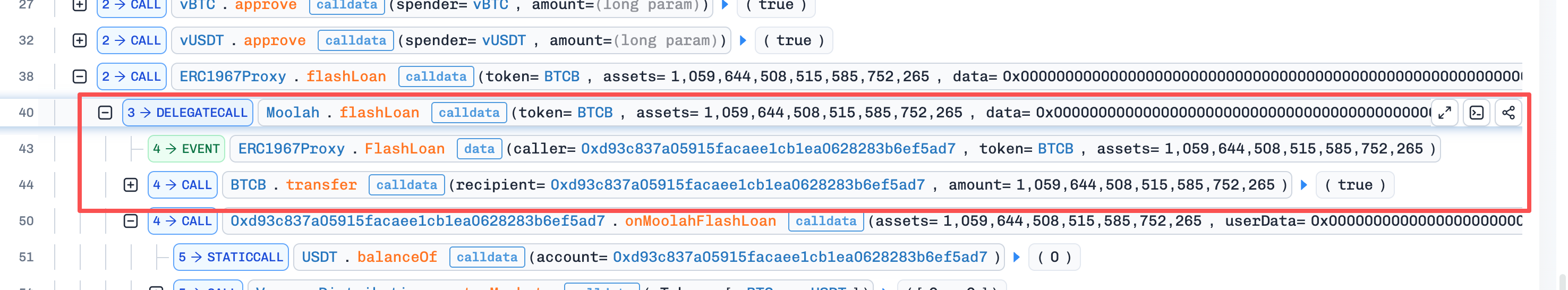
The attacker first borrowed 1,059 BTCB via a flash loan from Moolah Protocol,
Subsequently, they collateralized the 1,059 BTCB on Venus Protocol to borrow 30,000,000 USDT.
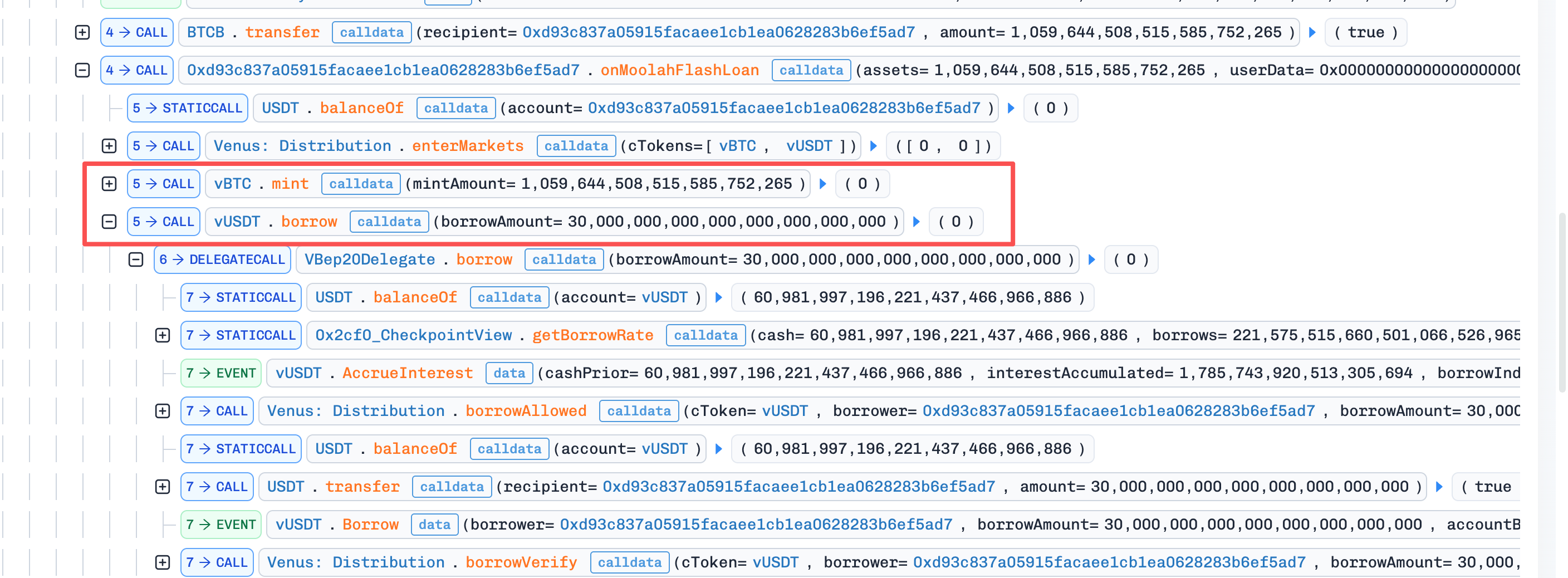
Next, the attacker called the function `swapTokensForExactTokens` on PancakeSwap, using 23,337,952 USDT to exchange for 982,506 PGNLZ, but then burned these PGNLZ (sent them to 0xdead).
Before the swap, the PancakeSwap Pool contained 100,901 USDT and 982,506 PGNLZ, making the price of PGNLZ 1 PGNLZ = 0.1 USDT. After the swap, the PancakeSwap Pool had 23,438,853 USDT and 4,240 PGNLZ remaining, making the price of PGNLZ 1 PGNLZ = 5,528 USDT.
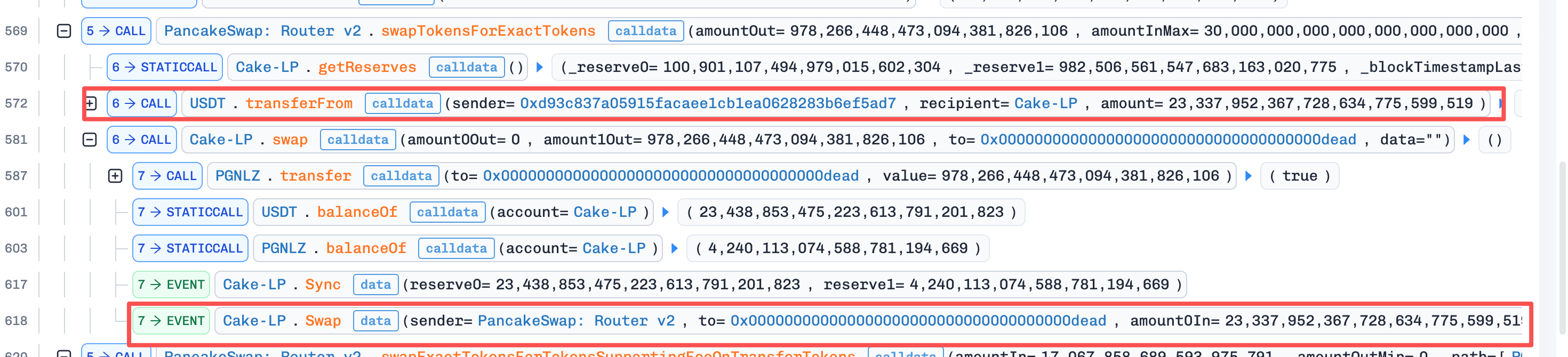
Subsequently, the attacker called the function `swapExactTokensForTokensSupportingFeeOnTransferTokens`. This function primarily supports Fee-On-Transfer Tokens, i.e., tokens that incur fees on transactions. PGNLZ uses `_update` to handle transaction fees. The specific call chain is: transferFrom -> _spendAllowance -> _transfer -> _update
Since this was a sell, `_handleSellTax` was called.
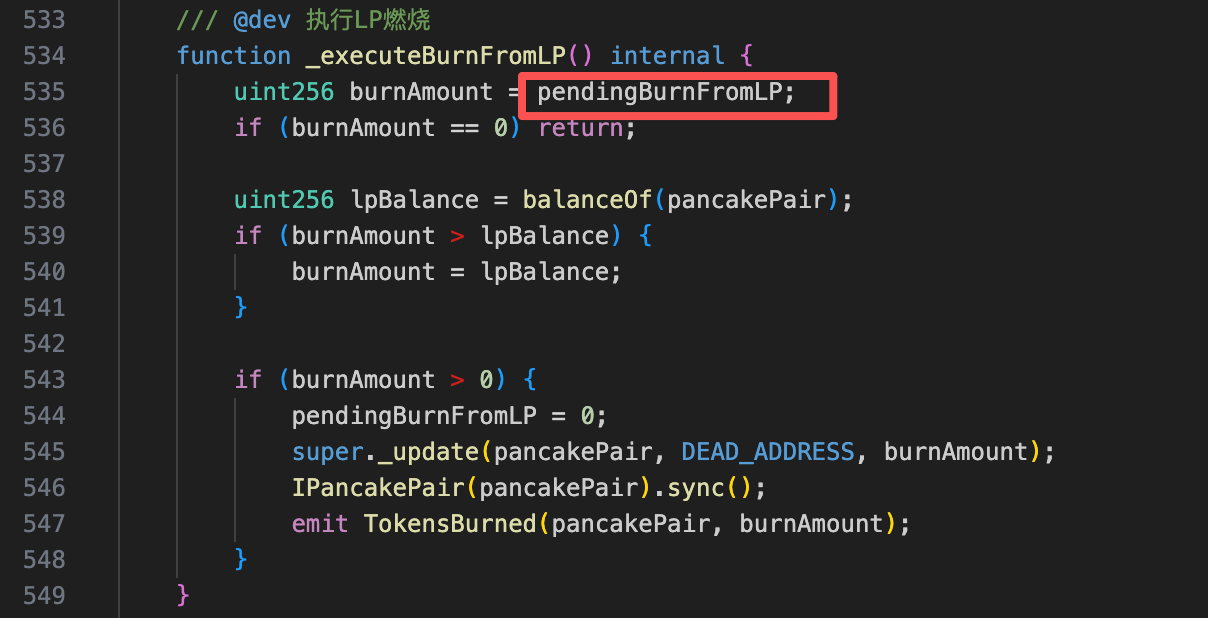
Let's look at how `_executeBurnFromLP` is implemented.
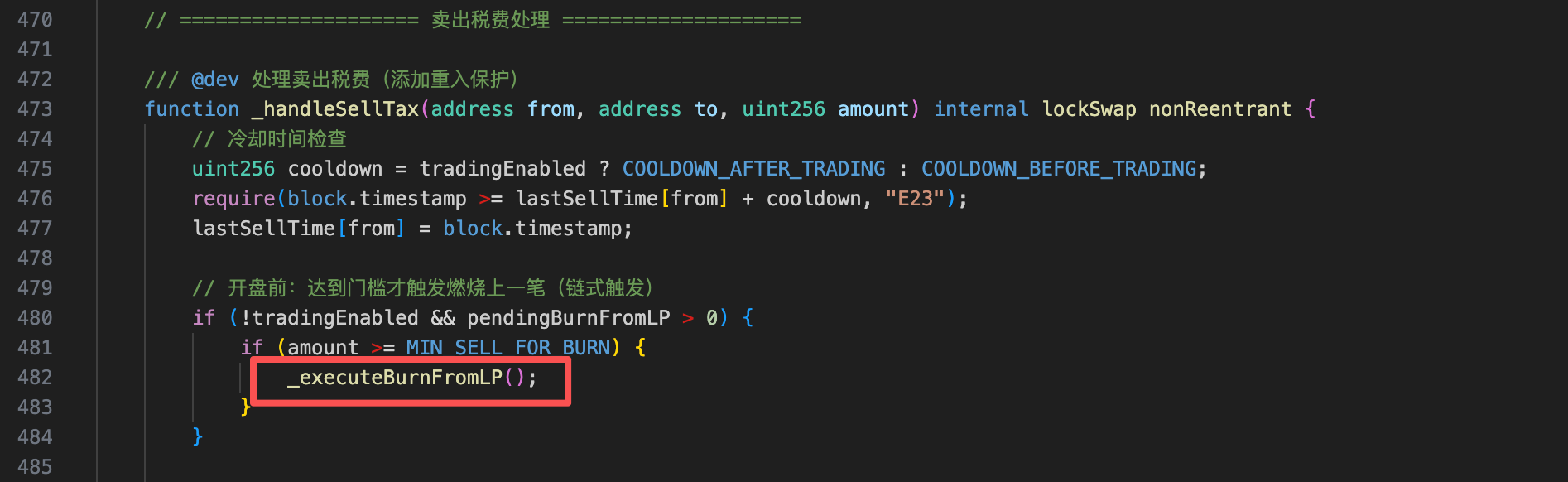
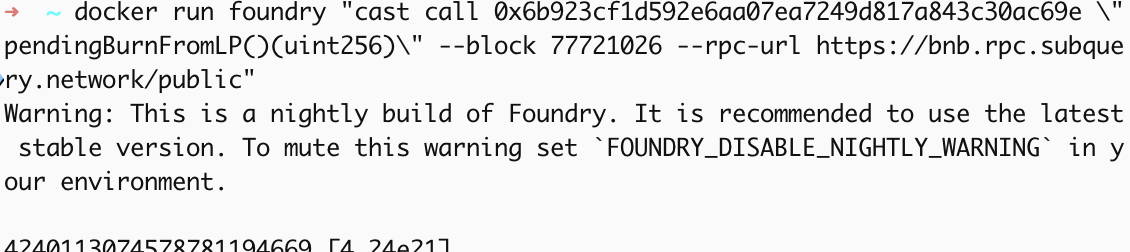
It can be seen that `_executeBurnFromLP` uses `_update` to burn the quantity of PGNLZ specified by `pendingBurnFromLP`. In the previous block, `pendingBurnFromLP` was queried as 4,240,113,074,578,781,194,669.
After the burn, the LP Pool was left with only 0.00000001 PGNLZ, making the price 1 PGNLZ = 234,385,300,000,000 USDT, a 40 Billion-fold increase.
Finally, the attacker drained the LP Pool, repaid the flash loan, and profited 100k USDT.
Summary
The cause of this vulnerability was the deflationary economic model, which lacked validation during fee deductions or LP Pool burns. This allowed the attacker to manipulate the token's price using its deflationary characteristics. It is recommended that project teams conduct thorough multi-party validation when designing economic models and code execution logic. Before contract deployment, opt for cross-audits from multiple auditing firms during the audit phase.