Preface
In the blockchain world, every on-chain operation relies on Gas fees. It is the "fuel" that powers the network, but it has also become a target for malicious actors. From infinite approvals leading to assets being "silently" transferred away, to Gas fee hijacking forcing users to pay far more than expected, these traps are becoming increasingly hidden.
Unlike traditional phishing attacks, these attacks often disguise themselves as normal operations like "approval," "minting NFTs," or "participating in DeFi mining," exploiting users' unfamiliarity with contract mechanisms to consume or even steal assets without their knowledge. To help everyone recognize these risks, the Zero Time Technology security team, based on industry security practices and a series of blockchain security科普 (popular science) articles, focuses on Gas fees and transaction security. We will break down common traps, share practical prevention techniques, and outline emergency response plans for asset loss.
Part 01-Common Gas Fee and Transaction Security Traps
Gas fees, as the "pass" for on-chain transactions, directly relate to user asset security. Malicious actors exploit users' blind spots regarding Gas fee mechanisms and contract approvals to design various hidden traps, often disguised as normal on-chain interactions, making them hard to detect. Common traps mainly fall into the following 3 categories:
1. Infinite Approval
Infinite approval occurs when a user grants a smart contract "unlimited" permission to use a specific token in their wallet. This is currently one of the most common and harmful asset drainage traps.
◆How it works: When you click the "Approve" button in a DApp without carefully checking the approval amount, you might sign an "infinite approval" agreement. This means the contract can theoretically transfer all tokens of that type from your wallet at any time without needing your confirmation again.
◆Typical scenario: When minting niche NFTs, participating in unaudited DeFi liquidity mining, or using an unknown DEX for trading, malicious contracts may default to "infinite approval,"诱导 (luring) users to confirm quickly, then batch transfer assets from the wallet without the user's knowledge.
2. Gas Fee Hijacking
Gas fee hijacking refers to attackers forcing users to pay Gas fees far exceeding normal levels through malicious contracts or tampered transaction data, or even directly stealing the Gas fees paid by users. The essence is to seek illegal benefits by manipulating Gas fee parameters.
◆How it works:
-
Front-end tampering: The DApp front-end controlled by the attacker automatically sets the Gas price or Gas limit to extremely high levels when the user initiates a transaction, far exceeding the fees during normal network congestion.
-
Malicious contract consumption: Malicious contracts embed "infinite loop" code. When executed, they continuously consume Gas until the user-set Gas limit is exhausted. The transaction ultimately fails, but the Gas fee has already been deducted by the blockchain nodes.
◆ Typical scenario: A user participates in a hot NFT whitelist mint via a non-official link. After clicking confirm, the wallet instantly deducts ETH dozens of times the normal level as Gas fees, but the NFT is not received.
3. Fake Approval / Fake Transaction
Attackers诱导 (lure) users to sign malicious data by forging approval requests or transaction pop-ups, thereby directly stealing assets or gaining control of the wallet. Often overlaps with Gas fee traps.
◆How it works:
-
Phishing link诱导: Users click "official links" in phishing emails, Discord DMs, or social media ads, entering fake websites highly similar to genuine DApps.
-
Malicious request forgery: The "approval" pop-up on the fake website表面 (superficially) shows "approving tokens for trading," but the transaction data has been tampered with. It is actually an instruction to directly transfer user assets to the attacker's wallet.
◆ Typical scenario: A user receives a DM saying "Your wallet has security risks, urgent approval verification required." After clicking the link and completing the approval, not only is a high Gas fee paid, but the main tokens in the wallet are instantly transferred out.
Part 02-Wallet Security Settings and Preventive Measures
To counter the above Gas fee and transaction security traps, the core lies in "preventive measures." Users don't need to master complex blockchain technology. By focusing on the three cores of approval management, Gas fee settings, and transaction verification, and developing good operational habits, risks can be effectively avoided. Specifically, start with the following 3 points:
1. Strictly Control Approval Amounts, Adhere to the "Principle of Least Privilege"
Approval operations are the main突破口 (point of entry) for asset loss. Controlling the approval amount cuts off the risk at the source. The core is "don't approve excess amounts, revoke when not in use."
◆Reject infinite approval: When performing any approval operation in a DApp,务必 (be sure to) abandon the "default option." Choose "custom amount," approving only the minimum token quantity needed for the current operation (e.g., minting an NFT might only require approving 0.01 ETH, a trade only the amount for this transaction).
◆Approve on demand, revoke after use: For DApps used temporarily, revoke the approval immediately after completing the operation. For compliant DApps used long-term, regularly check approval amounts to avoid asset risks due to contract vulnerabilities.
2. Fine-tune Gas Fee Settings, Prevent Malicious Hijacking
Gas fee parameter settings are key to preventing Gas fee hijacking. You need to actively control Gas fee setting permissions, not let malicious front-ends or contracts manipulate them, reducing unnecessary cost losses.
◆Enable advanced Gas control: In mainstream wallets (like MetaMask, TokenPocket), enable the "Advanced Gas Management" function. Manually set the upper limits for Gas price and Gas limit to avoid parameter tampering by malicious front-ends.
◆Refer to on-chain data: Before initiating a transaction, query the current network average Gas price through block explorers like Etherscan, Arbiscan. Reject transaction requests明显 (obviously) higher than market levels.
◆Avoid peak congestion times: During times like热门 (hot) project mints, major policy announcements, network Gas fees spike. Pause non-urgent operations during these times, or choose Layer2 networks to complete interactions, reducing costs and risks.
3. Strengthen Transaction Security Defenses, Avoid Basic Traps
Besides approvals and Gas fee settings, verifying the details of each transaction and the security of the interaction scenario are also important links in preventing traps.需做到 (Need to achieve) "verify carefully, reject suspicious."
◆Verify core transaction information: When confirming a wallet pop-up, must check three points — whether the receiving contract address matches the official one, whether the transaction amount is correct, and whether the Gas fee parameters are reasonable. All are essential.
◆Verify DApp authenticity: Only obtain DApp links through official websites, verified social media accounts (Blue V). Check the website SSL certificate and contract address. Refuse to click on links of unknown origin.
◆Isolate risky assets: Adopt a "dual wallet strategy." The hot wallet only holds a small amount of assets for daily interactions. Large amounts are stored in a hardware wallet or cold wallet,彻底 (completely) isolating on-chain interaction risks.
Part 03-Handling Asset Loss and Tool Recommendations
Even with precautions, one might still encounter malicious attacks due to negligence. At this time, fast and accurate handling can minimize losses. Based on practical experience, the Zero Time Technology security team has compiled "Emergency Handling Steps" and "Essential Security Tools" to help users take the initiative in a crisis.
1. Emergency Three-Step Process (Golden 10 Minutes)
Approval operations are the main突破口 (point of entry) for asset loss. Controlling the approval amount cuts off the risk at the source. The core is "don't approve excess amounts, revoke when not in use." (Note: This paragraph seems to be a copy-paste error from Part 02. The correct content for Part 03 step 1 is likely the following points, which are described later in the text)
◆Immediately freeze wallet and revoke approvals: Upon detecting abnormal asset transfers or high Gas fee deductions, first use the wallet's "pause transactions" function to freeze operations. Simultaneously, open an approval management tool and batch revoke all approvals for suspicious contracts, cutting off the attacker's asset transfer channel.
◆Secure evidence and report to platforms: Screenshot and save key evidence like transaction hash (TxID), malicious contract address, approval records, DApp access link. Submit the transaction hash to a block explorer, marking the transaction as "suspicious attack." Also provide feedback to the wallet official and DApp platform, requesting assistance in interception.
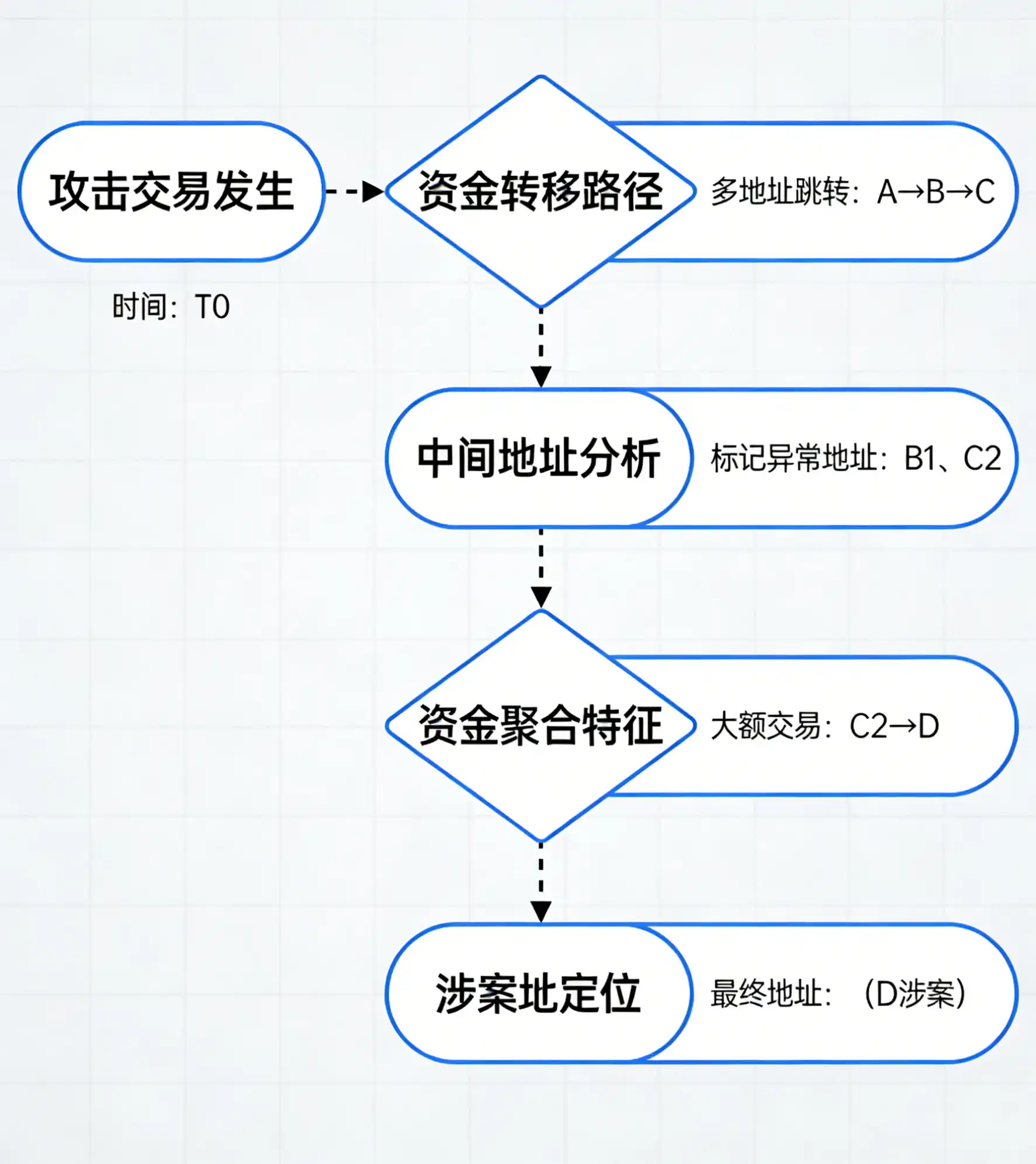
◆Seek help from professional security organizations: If large amounts are involved, immediately contact professional blockchain security organizations (like Zero Time Tech). Provide the complete evidence chain. Security teams can use on-chain tracing technology to track the attacker's fund flow, assist in contacting law enforcement, and attempt to freeze assets in related addresses.
2. Essential Blockchain Security Tool Recommendations
To help users with daily security protection and quick risk handling, 4 practical tools are selected, covering core scenarios like approval management, transaction verification, and risk warning. All are industry-recognized security tools:
3. Common Handling Misconceptions (Pitfall Guide)
To help users with daily security protection and quick risk handling, 4 practical tools are selected... (Note: This intro sentence is repeated from point 2. The content for point 3 is the following misconceptions)
◆Misconception 1: Paying "unfreezing fees" to recover assets — Attackers ask for tokens under the pretext of "helping freeze the involved address," which is essentially a secondary scam. Do not believe it.
◆Misconception 2: Deleting the wallet solves it — Deleting the wallet does not revoke contract approvals. Attackers can still transfer assets. The correct approach is to revoke approvals first, then reset the wallet.
◆Misconception 3: Neglecting on-chain tracing — After significant losses, individuals alone cannot track fund flows. Must seek help from professional organizations and law enforcement. Do not give up on rights protection.
Conclusion
Gas fees and transaction security are the "first line of defense" in the blockchain world. Traps like infinite approval and Gas fee hijacking essentially exploit users'侥幸心理 (gambler's fallacy, wishful thinking) and lack of understanding of technical details. Faced with interaction invitations from various DApps, remember the three principles: "Minimize approvals, hesitate before transacting, handle losses quickly" to effectively avoid most risks.