Author: Beosin
On March 3, 2026, the Financial Action Task Force (FATF) released the "Special Report on Stablecoins and Non-Custodial Wallets: P2P Transactions." Based on case studies submitted by FATF global network members, industry research, and data analysis, this report provides an in-depth analysis of the risks of stablecoins in money laundering, terrorist financing, and proliferation financing. It reveals how different types of criminal organizations use stablecoins to transfer and launder funds, repeatedly emphasizing that the greatest risk comes from P2P (peer-to-peer) transactions that bypass any regulated intermediaries. When funds circulate between multiple self-custodied wallets, regulatory agencies and financial institutions find it almost impossible to trace the true identities of the transacting parties. FATF did not introduce new mandatory standards this time but reiterated that its existing recommendations (especially Recommendation 15) must apply to all participants in the stablecoin ecosystem, including issuers and intermediaries. This article by Beosin will interpret the core content of the report, helping readers quickly grasp the trends of risk threats in the stablecoin field and enhance their awareness and response capabilities to stablecoin-related risks.
I. Current State of the Stablecoin Market
1. Explosive Growth in Scale
The report points out that the scale and adoption rate of stablecoins have experienced explosive growth in recent years. By mid-2025, there were over 250 stablecoins in circulation, with a market capitalization exceeding $300 billion. Among them, fiat-backed stablecoins, pegged to the US dollar and centrally managed, account for 95% of the market share, with USDT and USDC being the mainstream. Features such as price stability, high liquidity, and cross-chain interoperability make stablecoins increasingly popular in legitimate payments and investments.
2. Abuse in Illegal Activities
According to data disclosed by FATF, of the $154 billion in illegal virtual asset transactions globally in 2025, 84% were completed using stablecoins. Stablecoins have surpassed Bitcoin as the preferred asset for cybercrime-related transactions and are widely used for money laundering, terrorist financing, and large-scale weapons proliferation financing. Below are various criminal cases from the report:
North Korean Hackers: For example, the Lazarus Group attacked an exchange in February 2025, stealing nearly $1.5 billion. The funds were then transferred layer by layer through mixers, cross-chain bridges, and different wallet addresses, ultimately being exchanged for fiat currency via OTC.
Drug Trafficking: According to disclosures from the Canadian FIU, a criminal group exchanged drug proceeds for ETH through a Virtual Asset Service Provider (VASP), then converted the Ethereum into USDT and USDC on decentralized exchanges (DEX) and crypto-to-crypto trading platforms. These funds were then transferred to a wallet controlled by a Canadian shell import-export company. After multiple layers of wallet transfers, the funds were ultimately cashed out via OTC and VASPs.
Terrorist Financing: Terrorist organizations such as ISIL and Al-Qaeda raise funds through encrypted social platforms, using stablecoins to split funds and transfer them across chains to evade sanctions. A case showed that a French VASP, using on-chain analysis tools, discovered a customer frequently transferring small amounts of stablecoins to a wallet suspected of belonging to a terrorist organization, ultimately filing a Suspicious Transaction Report (STR) with TRACFIN.
Human Trafficking and Scam Compounds: Indian nationals working in Southeast Asian scam compounds cashed out USDT through a Southeast Asian payment service provider and transferred the funds to family and friends in India. The Indian Financial Intelligence Unit has investigated hundreds of cases where the involved IP addresses were concentrated in these scam compounds.
II. Existing Risks of Stablecoins
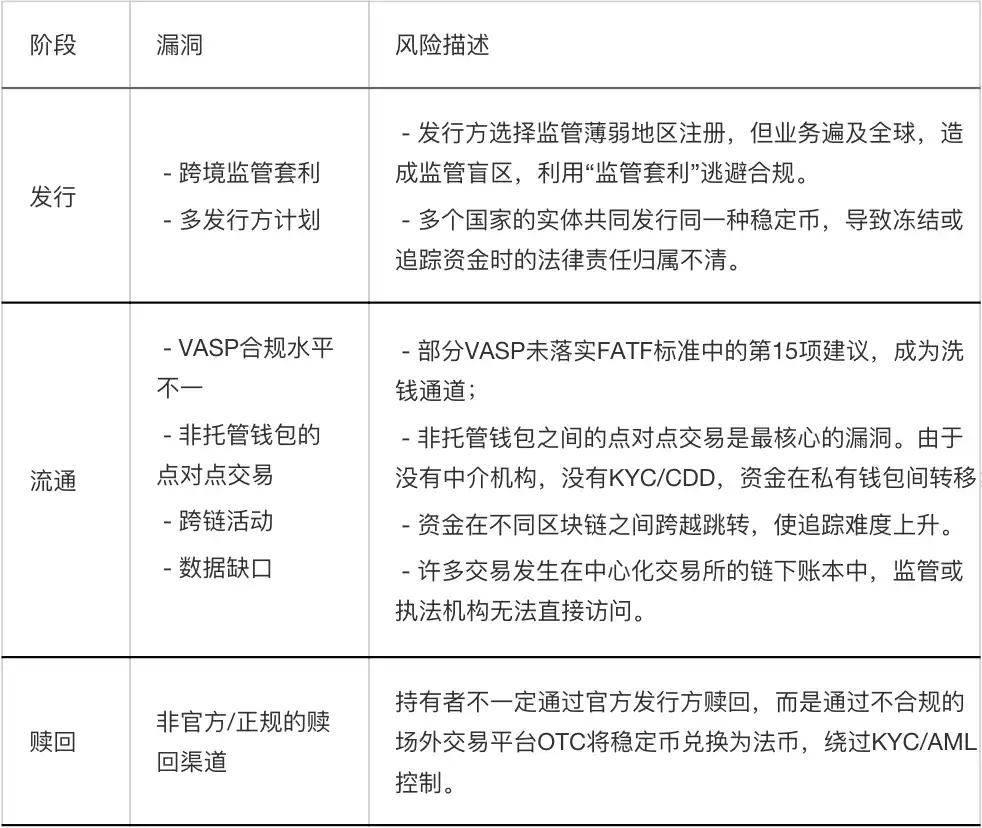
The report divides the stablecoin lifecycle into three stages: issuance, circulation, and redemption, pointing out the risk points at each stage:
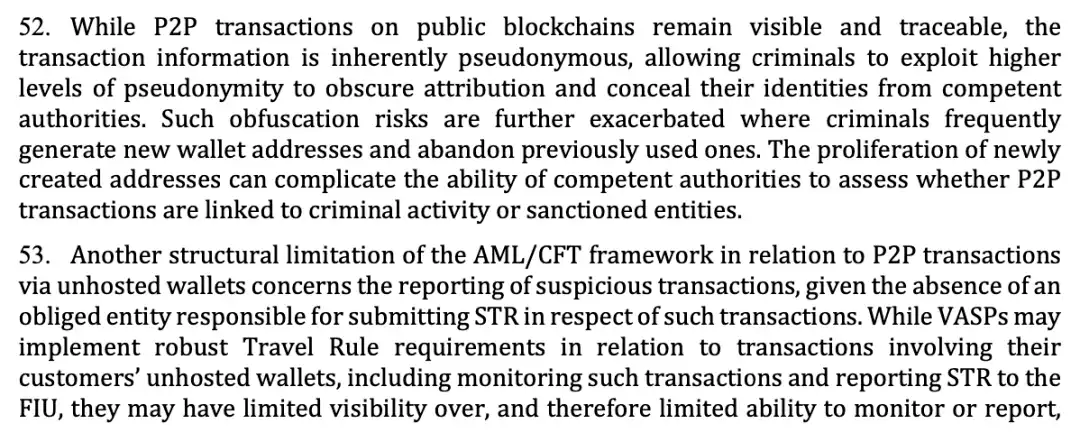
1. Non-Custodial Wallets and Peer-to-Peer (P2P) Transactions
Non-custodial wallets, because users fully control the private keys and do not rely on any regulated VASP or financial institution as an intermediary, make P2P transactions inherently outside the coverage of anti-money laundering (AML) obligations. Criminals are exploiting this characteristic by using layering techniques, frequently creating new addresses and adopting a 'use-and-discard' approach, splitting and dispersing funds, making it difficult for law enforcement to determine whether a P2P transaction is a normal transfer by a regular user or an illegal activity by a criminal network or sanctioned entity. This address proliferation tactic significantly increases the complexity of on-chain tracing. Relying solely on public blockchain data makes it difficult to form an effective evidence chain; it must be combined with off-chain intelligence, address labeling databases, and advanced analytical tools to penetrate the anonymity layer.
The report further emphasizes that P2P transactions between non-custodial wallets have no legal entity obligated to submit Suspicious Transaction Reports (STRs) to financial intelligence units. Although compliant VASPs fulfill the Travel Rule and monitor transactions when customers transfer funds to their non-custodial wallets, once the funds leave the VASP's sight and undergo multiple hops between non-custodial wallets, the VASP can no longer continue tracking, allowing criminals to escape the regulatory net. This may represent a structural loophole in the AML regime for virtual assets. When funds operate entirely outside licensed institutions, the traditional 'person-focused' regulatory model becomes ineffective. In the future, regulators may require VASPs to implement stricter due diligence measures for non-custodial wallet transactions, even promoting technical solutions (such as built-in whitelist/blacklist functions in smart contracts).
Original Content
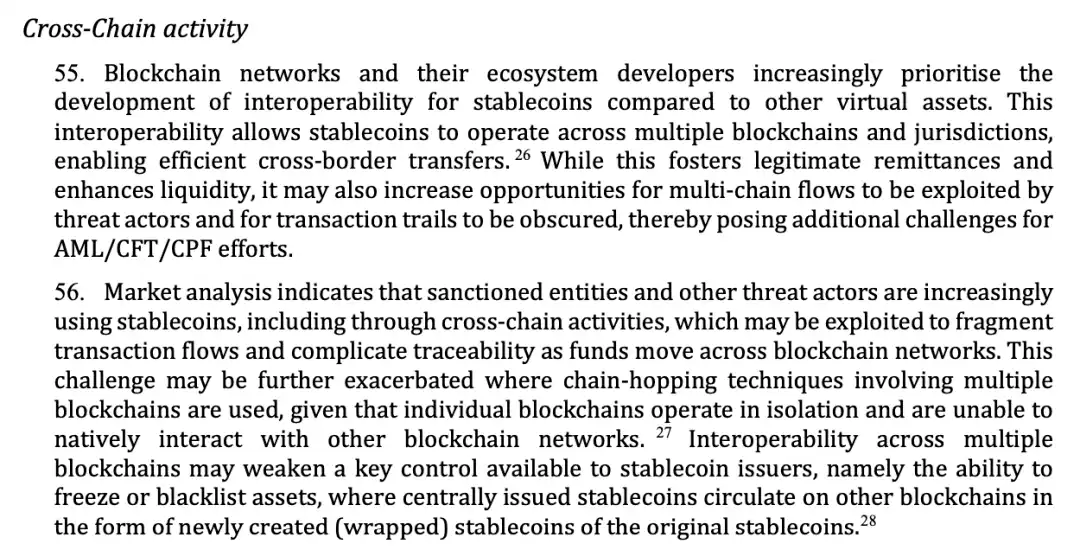
2. Cross-Chain Transaction Activities
Compared to other virtual assets, blockchain networks and developers are prioritizing the development of cross-chain interoperability for stablecoins. This technology allows stablecoins to flow freely across multiple blockchains (such as Ethereum, Solana, TRON, etc.) and different jurisdictions, enabling efficient cross-border transfers. However, cross-chain transactions increase traceability difficulties, weaken the ability of stablecoin issuers to implement controls, and can lead to related stablecoin transactions moving outside the regulated system.
Market analysis shows that sanctioned entities and other threat actors are increasingly utilizing cross-chain activities to use stablecoins. They employ "chain hopping" techniques, splitting a single transaction into multiple segments and repeatedly transferring them across different blockchain networks, thereby fragmenting fund flows and complicating tracking paths. Each blockchain operates independently and naturally cannot interact with others. When funds are transferred via a cross-chain bridge, tracking tools on the original chain become ineffective. Furthermore, cross-chain interoperability may also weaken one of the most critical control powers of stablecoin issuers—the ability to freeze or blacklist.
The report specifically mentions that when centrally issued stablecoins are "wrapped" into new tokens on another chain via a cross-chain bridge (e.g., cross-chaining USDC from Ethereum to Solana, becoming "Wormhole Wrapped USDC" on the Solana chain), these wrapped tokens often fall outside the direct control of the original issuer. The issuer's command to freeze assets on the original chain may not be transmitted to the wrapped assets on other chains. Beosin believes that stablecoin issuers should closely monitor the circulation of their tokens in the cross-chain ecosystem. Where conditions allow, issuers should establish cooperation mechanisms with cross-chain bridge project parties to ensure that freezing instructions can be transmitted to wrapped assets as much as possible. VASPs and compliance teams should also deploy analytical tools capable of supporting multi-chain tracking and cross-chain溯源, maintaining high vigilance for transactions involving cross-chain bridges and wrapped assets.
Original Content
3. Data Gaps
The blockchain architecture of stablecoins both assists and hinders AML/CFT supervision. Although all transactions are immutably recorded on the public blockchain, these records lack crucial off-chain information. This is precisely why FATF Recommendations 10 and 15 (regarding customer due diligence) are so important: law enforcement agencies must be able to obtain customer identity information and geographic location from VASPs and financial institutions. Without this off-chain information配合, looking at on-chain data alone根本无法锁定犯罪嫌疑人. Furthermore, the lack of underlying wallet geographic location information severely weakens the ability for international cooperation between law enforcement agencies in different countries. When the flow of funds is unclear, and even the jurisdiction where it occurred is unknown, information sharing and joint law enforcement become impossible.
Relying solely on public data from blockchain explorers only shows the flow of funds but not who is behind it or where they are located. This is why criminals dare to act recklessly on public chains—they know that as long as they don't cash out through KYC exchanges, the on-chain address is a "safe shell."
Secondly, not all transactions occur on-chain. When two users transfer funds internally within the same exchange, it is essentially an off-chain transaction. Asset changes are only recorded on the exchange's internal ledger and are not actually broadcast and confirmed on the blockchain. These transactions are usually faster and cheaper (no miner fees), but the trade-off is that they completely脱离公共区块链的视线. If the exchange is unlicensed or unregistered, the situation is completely out of control. There is no regulated intermediary to collect customer identity information, and no one submits suspicious transaction reports. Law enforcement agencies are completely unaware that the transaction occurred, let alone able to investigate it. This is a replication of the traditional financial "underground banking" problem in the virtual asset field. Off-chain transactions create a "dark forest" for regulation; funds are controllable while circulating within licensed institutions, but once they enter the internal accounting system of an unlicensed institution, they completely disappear from regulatory view. Criminals only need to send funds into an unlicensed exchange, transfer them around a few times on the internal ledger, and then withdraw them, completely中断链上追踪线索. In response to the data gap issue revealed by FATF, Beosin recommends increasing efforts to crack down on unlicensed, unregistered exchanges, cutting off channels for criminals to "launder" funds through off-chain transactions. For licensed institutions, customer due diligence information is not only a compliance requirement but also a firewall protecting themselves from being used by criminals. Institutions should also establish完善的内部账本监控体系 to identify abnormal internal transfer patterns.
Original Content
Issuers and regulatory agencies should consider proactively monitoring the circulation of stablecoins in the secondary market based on risk. Beosin's Stablecoin Monitoring system monitors the total issuance, minting, and burning volumes of stablecoins in real-time during the issuance phase, dynamically presenting changes in supply; during the circulation phase, it deeply analyzes the number of holders, holder categories (e.g., exchanges, institutions, individuals) and entity attribution, mapping anonymous addresses to off-chain entities and identifying high-risk VASPs. This monitoring system supports statistics on daily transaction volume and active address numbers, providing insights into real market demand. Combined with price volatility and peg stability analysis, the system can promptly detect de-peg risks caused by market manipulation or liquidity crises, indirectly identifying potential money laundering activities. The system具备跨链活动追踪能力, can track fund flows across different blockchains, solving the难题 of tracking funds "chain hopping," and through address association and behavioral pattern analysis,弥补中心化交易所“链下账本”的数据缺口, inferring possible off-chain transaction scale and trends. In the redemption phase, the system will, through the identification and clustering analysis of over-the-counter (OTC) platform and P2P transaction addresses, proactively discover behaviors where holders exchange stablecoins for fiat currency through unofficial channels. Once funds flowing to high-risk platforms are detected, the system will issue real-time alerts, helping various stakeholders in the ecosystem to intervene promptly and block the money laundering chain.
III. Stablecoin Regulation, Risk Response, and Recommendations
1. Regulatory Practices
In response to the financial risks posed by stablecoins, the report shares practices from multiple countries and regions in stablecoin regulation and recommends that stablecoin issuers embed functions such as "whitelist/blacklist" or "freeze/destroy" in smart contracts to control illegal funds in the secondary market as required by law enforcement agencies. Beosin believes these technologies are becoming key bridges connecting decentralized technology with centralized regulation, providing practical and feasible solutions to address the regulatory challenges posed by non-custodial wallets.
The report points out that stablecoin issuers can set allowlists in smart contracts, permitting only pre-approved entities or wallet addresses to hold, receive, or transfer the stablecoin. This function is implemented by adding access control lists to the smart contract; any transaction initiated by an address not on the whitelist will be automatically rejected. The whitelist mechanism represents a "proactive defense" compliance approach. It establishes an "admission wall" requiring identity authentication within the decentralized blockchain environment. Although this approach may somewhat limit openness, for stablecoin projects pursuing high compliance standards, it is an effective means to ensure ecosystem security and prevent exploitation by criminals.
Original Content
2. Blockchain Analysis Tools
The report clearly states that blockchain analysis tools hold significant value in identifying money laundering, terrorist financing, and proliferation financing risks within the stablecoin ecosystem. FATF has previously analyzed and encouraged the use of such tools on multiple occasions, and international organizations like the UN Security Council Counter-Terrorism Committee have adopted similar positions. The report specifically mentions that technological advancements in areas such as artificial intelligence, machine learning, and big data analytics are substantially enhancing the capabilities and application potential of these tools. This means that blockchain analysis tools are no longer limited to simple address labeling and transaction tracking but can discover more隐蔽的犯罪模式 through intelligent algorithms. Against the backdrop of surging stablecoin transaction volumes and frequent cross-chain activities, manual review alone is completely incapable of covering the massive number of transactions. With the help of AI, machine learning, and blockchain analysis tools (such as Beosin KYT), institutions can achieve automated identification and预警 of suspicious behavior, analyzing and tracking over 120 complex cross-chain protocols and mixing transactions, significantly improving regulatory efficiency.
Original Content
Beosin believes that different analysis tools have their own focuses, and using them in combination can provide mutual verification and complement each other's strengths. On-chain evidence needs to be corroborated with off-chain intelligence and investigations in the physical world; technical output provides clues, while human insight draws conclusions. VASPs should establish tool evaluation mechanisms and not blindly rely on a single supplier. At the same time, increased investment should be made in cultivating virtual asset investigation talent, forming复合型专业团队 that understand both blockchain technology and financial compliance.
This FATF report conveys a清醒而务实的信息: blockchain analysis tools are powerful weapons in the fight against money laundering. True regulatory effectiveness comes from the organic combination of advanced technical tools, traditional methods, and professional talent. Beosin will continue to深耕区块链安全与合规领域, providing regulatory agencies and industry clients with comprehensive solutions that penetrate both on-chain and off-chain. To date, Beosin KYT has accumulated over 4.9 billion on-chain address labels, covering 29 high-risk categories including sanctions, terrorist financing, mixing, scams, hacking, dark web, gambling, and phishing. Using advanced technologies like machine learning, it helps over 300 institutions assess the risk of on-chain transaction counterparty addresses and transactions, including stablecoins, in real-time.
FATF also listed in the report various risk mitigation measures currently adopted by jurisdictions and the private sector:
a. Transaction Limits: Setting a "Safety Valve" for Fund Outflows
This is the most direct and basic risk control measure. By setting single or daily withdrawal limits to self-custodied wallets, even if a customer account is compromised by malicious actors, the financial loss and money laundering scale can be controlled within a certain range. In practice, many compliant exchanges have set withdrawal limits to external wallets for users who have not completed advanced verification.
b. Enhanced Due Diligence: Piercing to Identify the Actual Controller of the Wallet
VASPs should apply enhanced due diligence measures to transactions involving self-custodied wallets, including verifying the beneficial owner identity of that self-custodied wallet. Traditional KYC only verifies the customer themselves, but who the customer sends funds to (i.e., the holder of the self-custodied wallet) is often a blind spot. Requiring verification of the counterparty's identity effectively extends the compliance触角 to the on-chain environment, significantly increasing the difficulty for criminals to use non-custodial wallets to receive funds.
c. Blockchain Analysis: Risk Rating of Transaction Counterparties
VASPs use blockchain analysis tools to assess the risk level of their customers' transaction counterparties (i.e., the party holding the self-custodied wallet). This is a typical scenario where technology empowers compliance. Through analysis tools (like Beosin KYT), VASPs can understand whether the non-custodial wallet their customer wants to transfer to has high-risk labels (e.g., associated with mixers, darknet markets, sanctioned addresses). If the counterparty address risk score is too high, the system can intervene or trigger manual review (Counterparty Risk Profiling).
d. Full Lifecycle Coverage: Imposing Compliance Obligations on Self-Custodied Wallets at Issuance and Redemption Stages
At the two critical entry and exit points where users purchase stablecoins with fiat currency (issuance) or exchange stablecoins back to fiat currency (redemption), identity verification should be conducted even if self-custodied wallets are used. This effectively prevents criminals from exploiting loopholes when funds enter or exit the blockchain.
e. Source Control: Denying Licenses to Platforms Allowing Transfers to Self-Custodied Wallets
If an exchange's business model allows users to freely transfer coins to any self-custodied wallet without verification, regulators can directly refuse to grant a license, keeping it out of the compliant market. Beosin can assist regulators in identifying non-compliant platforms through on-chain monitoring and auditing. Although this measure is strict, it can fundamentally eliminate the risk from this channel.
Original Content
3. Summary of Recommended Measures
The report also lists multiple recommendations for jurisdictions and the private sector to prevent the misuse of stablecoins, including:
● Apply FATF Recommendation 15 to the entire stablecoin ecosystem, defining the AML/CFT responsibilities of participants such as issuers and VASPs, and imposing corresponding compliance requirements based on risk, for example, requiring stablecoin holders to complete due diligence in advance (whitelisting).
● Require issuers to possess the technical capability to execute destruction, freezing, and recovery of stablecoins in the secondary market; implement customer due diligence at the redemption stage; limit issuance activities on high-risk blockchains; consider requiring issuers to implement whitelist and blacklist mechanisms; establish strict pre-issuance and pre-authorization supervision and compliance review mechanisms to prevent stablecoin-related ML/TF risks in advance.
● Strengthen the technical capacity building of regulatory agencies and law enforcement departments, fostering their understanding of emerging risks, modus operandi, business models, smart contract functions, and cross-chain transaction mechanisms, and enhancing their ability to effectively use blockchain analysis tools.
This can be achieved through in-depth technical exchanges with blockchain analysis tool service providers and regular research on emerging criminal techniques.
● Provide regulatory agencies and law enforcement departments with the necessary tools for rapid cooperation with domestic and international counterparts, including through established channels, MOUs, and legal provisions, to enable the rapid exchange of stablecoin-related information.
● Consider establishing public-private partnership mechanisms to strengthen cooperation between regulatory agencies, law enforcement, and stakeholders in the stablecoin ecosystem regarding criminal patterns, risk indicators, and emerging threats; establish cooperative relationships where necessary, especially in investigations involving off-chain transactions or stablecoin freezing/destruction.
Conclusion
The FATF report shows that the illegal abuse of stablecoins has become a global regulatory focus, with non-custodial wallet P2P transactions, cross-chain activities, and data gaps being the core risk vulnerabilities. FATF recommends that jurisdictions apply FATF Recommendation 15 to all participants in the stablecoin ecosystem, clarify the compliance obligations of issuers, VASPs, and other entities, strengthen programmable control through smart contracts (e.g., whitelist/blacklist, freeze/destroy functions) and the application of blockchain analysis tools, and establish public-private partnership mechanisms, among other methods, to enhance the regulation of stablecoins and balance their innovative value with financial security.