Original Author: Sanqing, Foresight News
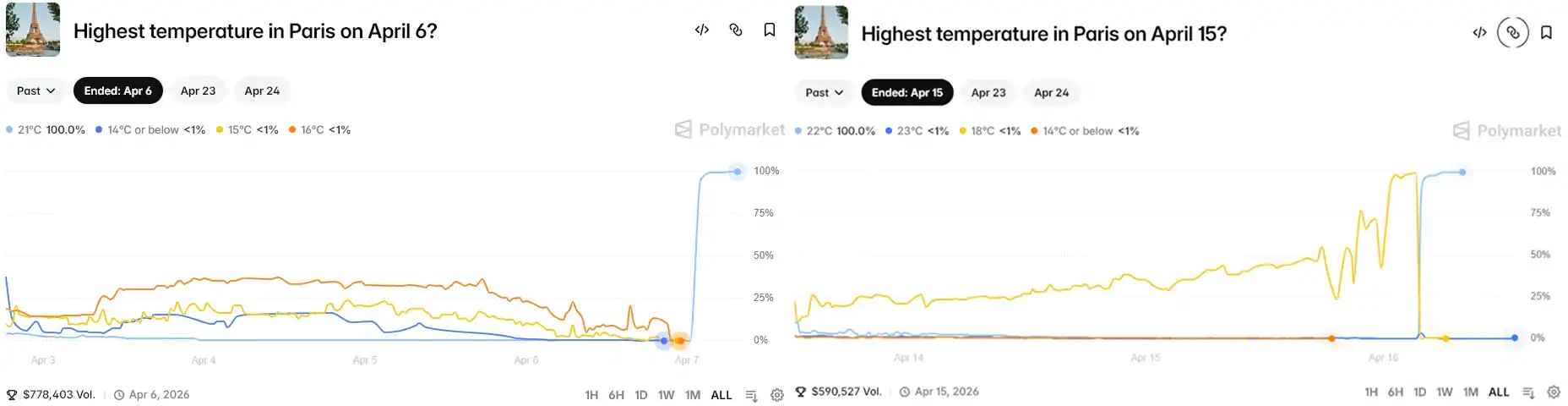
According to French media Le Monde, on April 6th and 15th, the meteorological sensors at Paris Charles de Gaulle Airport experienced two anomalies. The temperature surged by more than 3°C within minutes before quickly returning to normal, as if nothing had happened. Behind each anomaly, someone had placed bets on the corresponding low-probability temperature range on Polymarket in advance. From a principal of just tens of dollars, they collectively walked away with approximately $34,000 from these two incidents. The account that placed the first bet was created just two days before the anomaly occurred.
Météo-France subsequently conducted a physical inspection of the sensors and found signs of human intervention. They filed a criminal complaint with the Charles de Gaulle Airport Gendarmerie, with the charge being "interfering with an automated data processing system." According to an analysis in an AR15 forum post, based on Article 323-2 of the French Penal Code, and because Météo-France is a public institution, the related charges could carry a maximum penalty of 7 years imprisonment and a fine of 300,000 euros.
The Technical Sophistication of This Scam Is Approximately Zero
The settlement chain for Polymarket's Paris temperature market is as follows: Physical Sensor → Météo-France → Weather Underground → Polymarket Contract.
On this chain, the smart contract part is audited, data transmission is automated, and Weather Underground's data scraping is real-time. The only weak point is at the very beginning: a thermometer standing by the airport roadside, without fencing, without cameras, accessible to anyone who walks by.
All the attacker needed was a battery-powered heat gun/hairdryer.
Polymarket bases its settlement on the day's maximum temperature. This means that creating one brief temperature peak is enough to rewrite the official record for the day.
Acting in the evening or at night is more ideal, as the daytime high has usually already passed, making subsequent readings more likely to become the new record. Therefore, the suspect chose 7 PM on April 6th and 9:30 PM on April 15th.
The operational procedure was likely: buy the low-probability option in advance, walk to the sensor at night, turn on the heat gun, wait for the reading to cross the target temperature, stop, leave, and wait for on-chain settlement.
The entire operation required no technical skill whatsoever, just some understanding of the settlement mechanism and a willingness to walk to the edge of the airport.
Polymarket's Response: Quietly Swapped the Thermometer
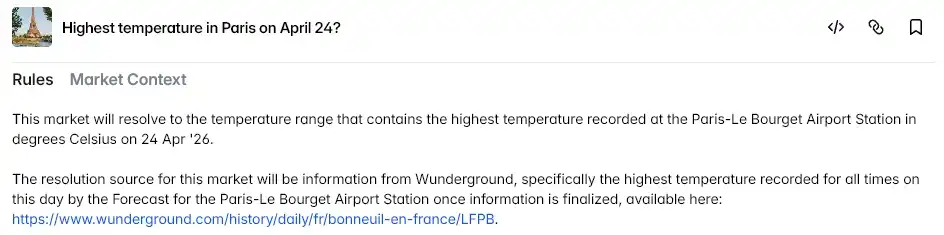
Polymarket has not issued any official statement regarding this incident. The only thing it did was change the settlement data source for the Paris temperature market from Charles de Gaulle Airport (LFPG) to Le Bourget Airport (LFPB).
The profits from the two accounts were not revoked; the market settled normally according to the on-chain records.
The sensor at Le Bourget Airport is also placed outdoors, similarly without physical protection. They changed the address, but the problem remains entirely unchanged.
This is not Polymarket's first controversy. In October 2024, a French trader was accused of manipulating Trump election odds using 4 linked accounts, reportedly profiting $85 million; in March 2025, a whale used 5 million tokens to forcibly push through a UMA governance vote, settling a controversial market with a "Yes" outcome, involving $7 million; in January and March 2026, anomalous bets appeared in markets related to Venezuela and Iran respectively, with the latter already drawing attention from the US Congress...
Previous incidents at least required millions of dollars in capital or governance tokens; this time the cost was just a heat gun.
The Contract Was Audited, The Thermometer Was Not
This story has an absurd sense of humor. A prediction market running on the blockchain, touting decentralization and immutability, was thoroughly exploited twice by a battery-powered heat gun. Cryptography was of no help in this matter because it never verifies whether the input data is real.
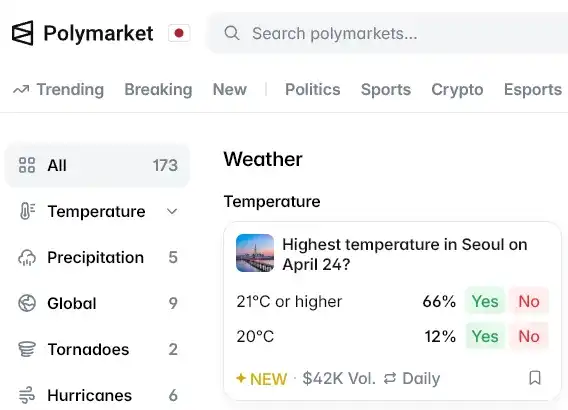
Polymarket currently has 173 active weather markets. The settlement basis for most of these markets is a single physical sensor in some location.
When a sensor is used as a meteorological tool, its credibility comes from the fact that no one has a motive to tamper with it. Polymarket gave it a new incentive structure but provided no new physical protection.
The Météo-France thermometer dutifully recorded the temperature it sensed. It just didn't know it had become a financial settlement terminal.