According to an April 2nd report, the Claude Code source code leak incident caused by an Anthropic human error continues to escalate. Currently, hackers have exploited this hot topic to spread information-stealing malware named Vidar via fake repositories on GitHub.
Upgraded Bait: Claiming to "Unlock Enterprise-Level Features"
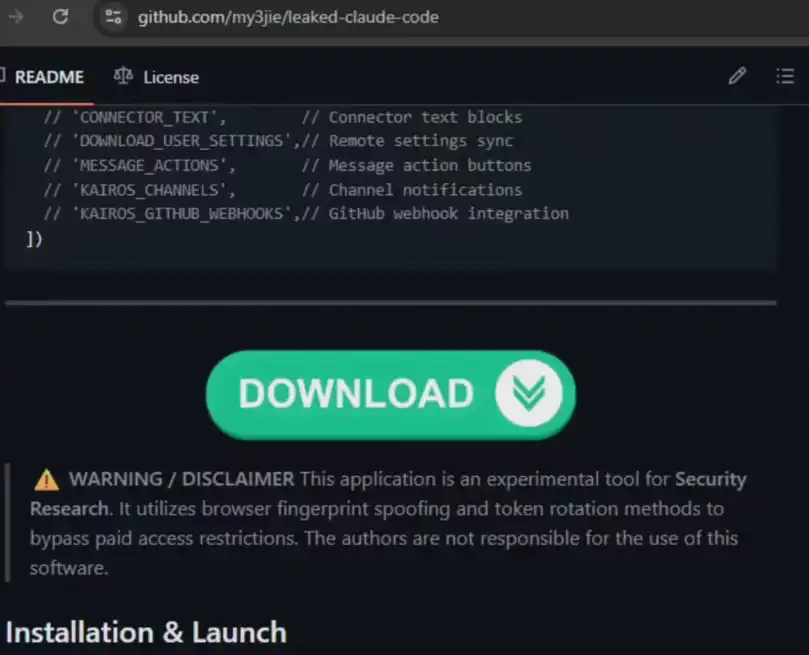
Monitoring reports from security company Zscaler show that a user named idbzoomh has created multiple fake repositories on GitHub.
Precision Phishing: The hacker claims in the repository description to provide leaked source code that "unlocks enterprise features," luring eager developers to download it.
SEO Optimization: To maximize the impact, the attackers optimized for search engine keywords, causing these malicious repositories to often rank at the top when users search for terms like "Claude Code leak".
Virus Profile: Vidar Infiltrates, Data "Relocated"
Once users are deceived into downloading and executing the contained executable files, the system is quickly compromised:
Information Theft: The implanted Vidar is a highly mature malware on the dark web, specifically designed to harvest browser account passwords, cryptocurrency wallets, and various types of sensitive personal information.
Persistent Latency: The virus also simultaneously deploys the GhostSocks proxy tool, setting up a secret channel for subsequent remote control and data exfiltration.
Risk Warning: Beware of "Free Lunches" from Unofficial Channels
Security researchers point out that the malicious compressed files in these fake repositories are updated at an extremely high frequency, making them easy to bypass basic security detection. At least two repositories with similar tactics have been discovered so far, suspected to be tests of different propagation strategies by the same attacker.
Industry Observation: The "Chain Set" of AI Security
From Anthropic's source code packaging mistake to hackers secondarily exploiting the hot topic for phishing, this incident reflects the complexity of security risks in the AI era. When the developer community becomes the target of attacks, basic digital literacy—not running binaries from unknown sources—remains the last line of defense.
Editors remind all developers: Please be sure to obtain tools through official Anthropic channels. Do not fall into the traps carefully designed by hackers out of curiosity or the pursuit of "cracked features."