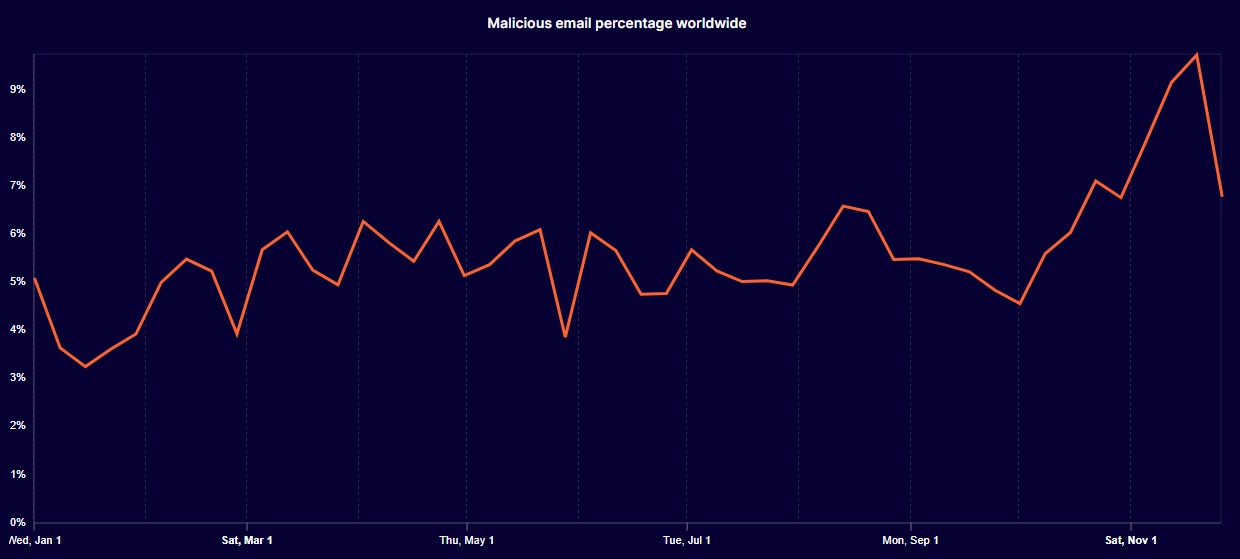
More than 5% of all emails sent worldwide contain malicious content, according to internet infrastructure giant Cloudflare.
The web security giant revealed that an aggregate of 5.6% of global email traffic analyzed by the firm over the past year was found to be malicious. This equates to more than one in every twenty emails containing harmful content.
In November, that figure surged to almost one in ten, nearly double the average for the year, it found.
Malicious emails include those that can cause harm, such as the theft of credentials, data, or money, Cloudflare explained in its 2025 year-in-review report.
The findings are particularly relevant to crypto investors, as phishing attacks targeting crypto traders, investors, and executives have increased in complexity and surged in recent months.
Crypto phishing links can be especially damaging. Once a victim falls for one of these malicious links or sends cryptocurrency to a scammer, there’s usually no way back.
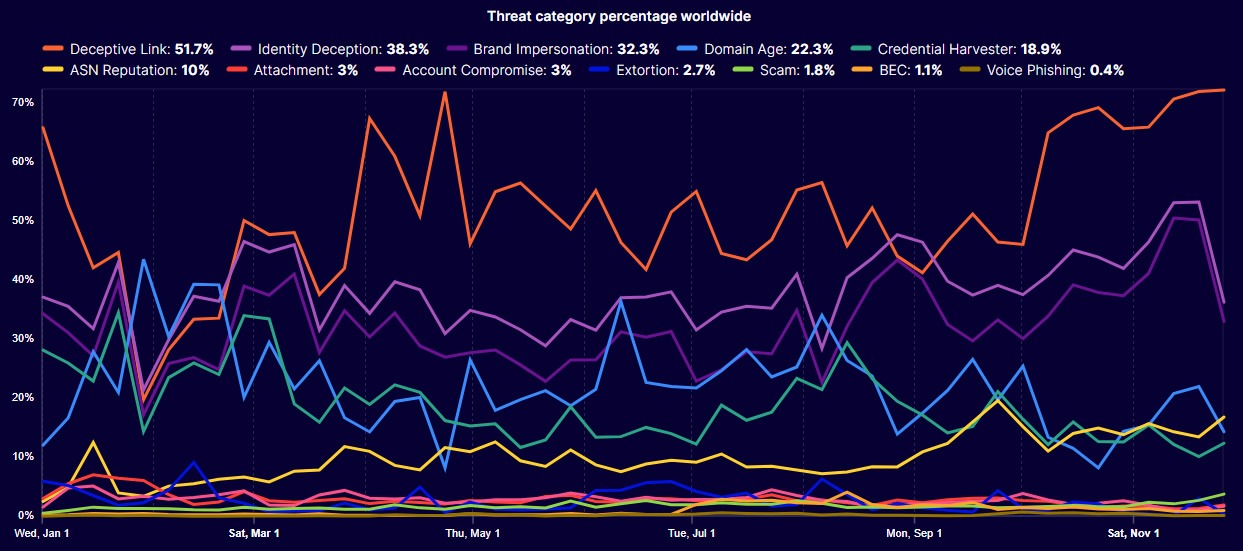
Deceptive links dominate threat categories
More than half of these malicious emails, or 52%, contained a deceptive link, which was the highest threat category, it reported.
Identity deception was the second-highest at 38%, up from 35% in 2024, as attackers impersonated trusted individuals using spoofed domains, similar-looking domains, or display name tricks.
Related: Email auto-reply vulnerability allows hackers to mine cryptocurrency
Cloudflare also revealed that the most abused top-level domain (TLD) extension was “.christmas,” with 92.7% malicious emails and 7.1% spam originating from this domain type.
Other highly abused domain names included “.lol,” “.forum,” “.help,” “.best” and “.click.”
A quarter of HTML attachments are malicious
Earlier this year, researchers at cybersecurity company Barracuda analyzed 670 million emails that were malicious or unwanted spam.
They discovered that email remains the most common attack vector for cyber threats, with malicious attachments and links being used to distribute malware, launch phishing campaigns, and exploit vulnerabilities.
As many as one in four emails were unwanted spam, a quarter of all HTML attachments were malicious, and 12% of malicious PDF attachments were Bitcoin scams, they reported.
In November, Hornet Security reported that email was a “consistent delivery vector” for cyberattacks in 2025, with malware-laden emails surging by 131% year-over-year.
Magazine: Do Kwon sentenced to 15 years, Bitcoin’s ‘choppy dance’: Hodler’s Digest