Author: Beosin
In the early hours of January 9, an unopen-sourced contract deployed by Truebit Protocol 5 years ago was attacked, resulting in a loss of 8,535.36 ETH (worth approximately $26.4 million). The Beosin security team conducted an analysis of the vulnerability and fund tracking for this security incident and shares the results as follows:
Attack Technique Analysis
For this incident, we take the most significant attack transaction as the analysis subject, with the transaction hash: 0xcd4755645595094a8ab984d0db7e3b4aabde72a5c87c4f176a030629c47fb014
1. The attacker calls getPurchasePrice() to obtain the price
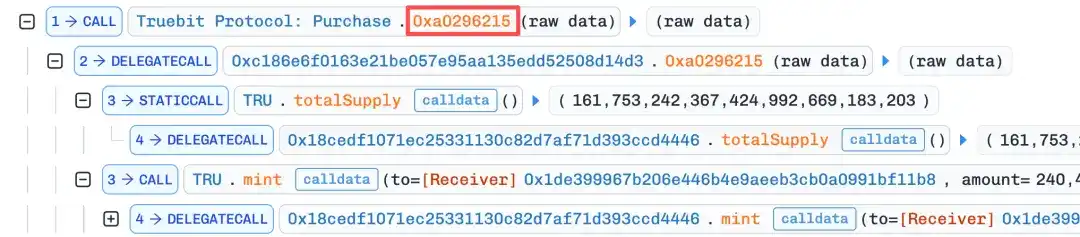
2. Subsequently calls the flawed function 0xa0296215(), setting the msg.value extremely low
Since the contract is not open-source, it is inferred from the decompiled code that this function has an arithmetic logic vulnerability, such as integer truncation issues, allowing the attacker to successfully mint a large number of TRU tokens.
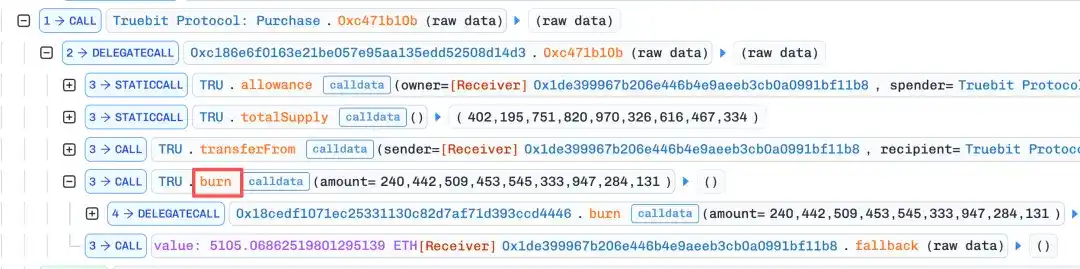
3. The attacker "sells back" the minted tokens to the contract through the burn function, extracting a large amount of ETH from the contract reserves.
This process is repeated 4 more times, with the msg.value increasing each time, until almost all ETH in the contract is extracted.
Stolen Funds Tracking
Based on on-chain transaction data, Beosin conducted a detailed fund tracking through its blockchain on-chain investigation and tracking platform, BeosinTrace, and shares the results as follows:
Currently, the stolen 8,535.36 ETH, after transfers, are mostly held in 0xd12f6e0fa7fbf4e3a1c7996e3f0dd26ab9031a60 and 0x273589ca3713e7becf42069f9fb3f0c164ce850a.
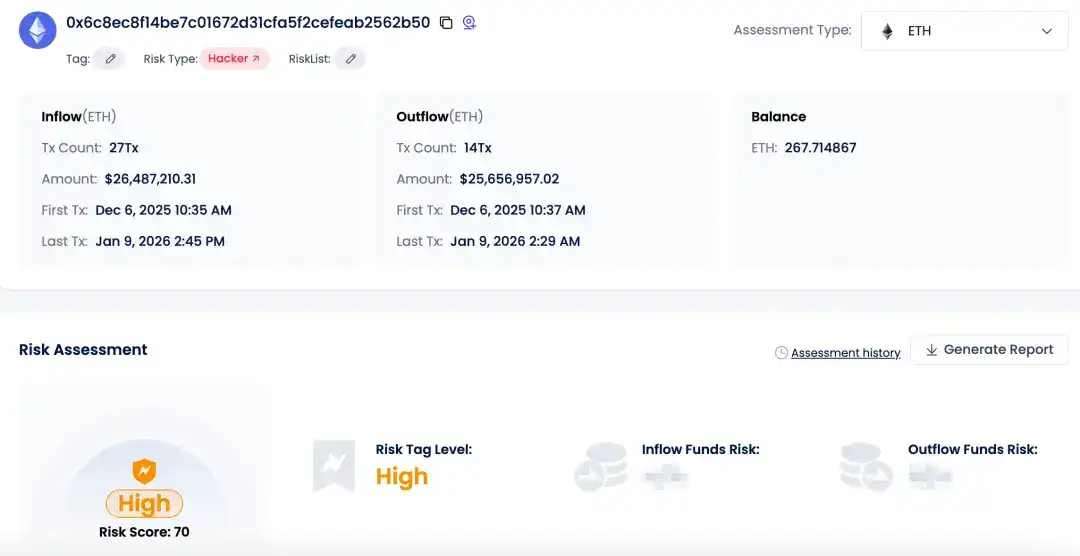
Among them, address 0xd12f holds 4,267.09 ETH, and address 0x2735 holds 4,001 ETH. The address from which the attacker initiated the attack (0x6c8ec8f14be7c01672d31cfa5f2cefeab2562b50) still holds 267.71 ETH. There have been no further fund transfers from these three addresses yet.
Stolen Funds Flow Analysis Diagram by Beosin Trace
The above addresses have been marked as high-risk addresses by Beosin KYT. Taking the attacker's address as an example:
Beosin KYT
Conclusion
This stolen fund incident involves an unopen-sourced smart contract from 5 years ago. For such contracts, the project team should upgrade the contract, introduce emergency pause functions, parameter limitations, and new Solidity security features. Furthermore, security audits remain an essential step for contracts. Through security audits, Web3 enterprises can comprehensively detect smart contract code, identify and fix potential vulnerabilities, and enhance contract security.
*Beosin will provide a complete analysis report of all fund flows and address risks for this incident. Welcome to request it via the official email [email protected].