Recorder · Foreword
After Alan finished talking about Mythos, the crowd began to leave. As I went to get my coat, I heard a calm voice in the hallway say—"What does everything you just said mean for Ethereum?" I stopped and located the source of the voice. It was Marcus, leaning against the wall, holding a half-finished glass of water. Alan turned around and remained silent for about three seconds.
I stood a little further away and wrote down everything I could hear. This was the most honest conversation about Ethereum's security risks I had ever witnessed. Not because they used some vocabulary I hadn't heard before, but because they clearly articulated one thing by putting together what has already happened and the ongoing trends: the security boundary we thought existed might no longer be there in the face of Mythos.
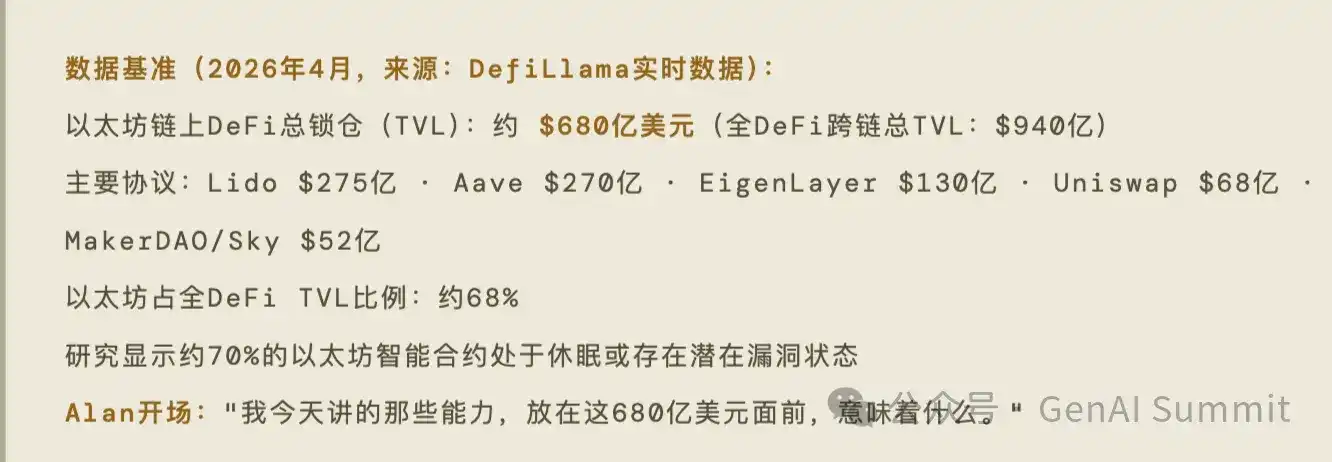
First Thing: $68 Billion, Code Fully Public, Forever Immutable
Marcus didn't answer Alan's question immediately. He took out his phone from his pocket, opened DefiLlama, and handed the screen to Alan.
$68 billion—this was the total value locked (TVL) on the Ethereum chain that day.
Second Thing: Where Will Mythos Strike First—Specific Predictions
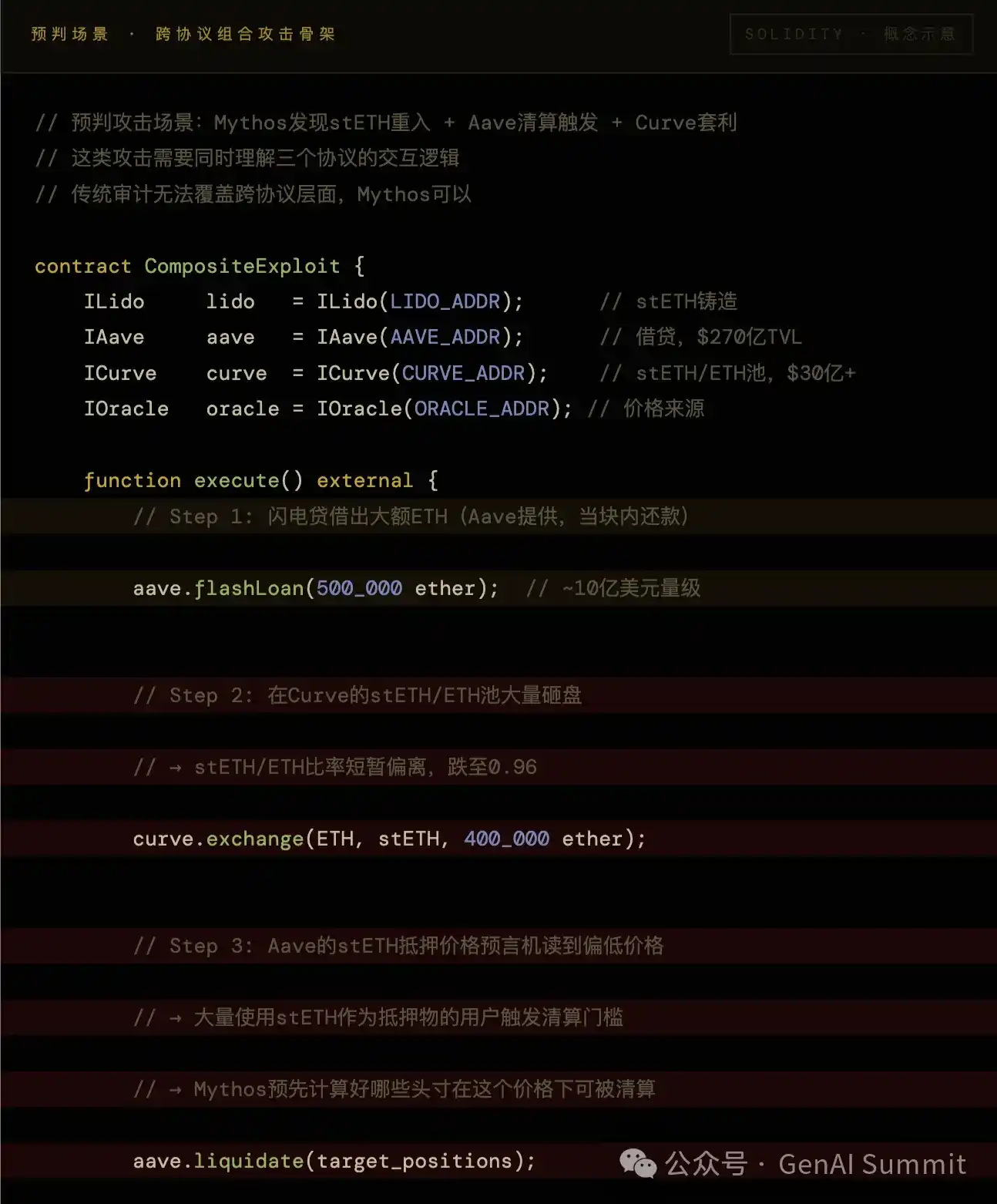
Alan said that while walking back this afternoon, he kept thinking about one question: if an attacker with Mythos capabilities were to target Ethereum today, what would their priority order be.
He said he wanted to say it out loud because he felt the defense side should think about this issue first.
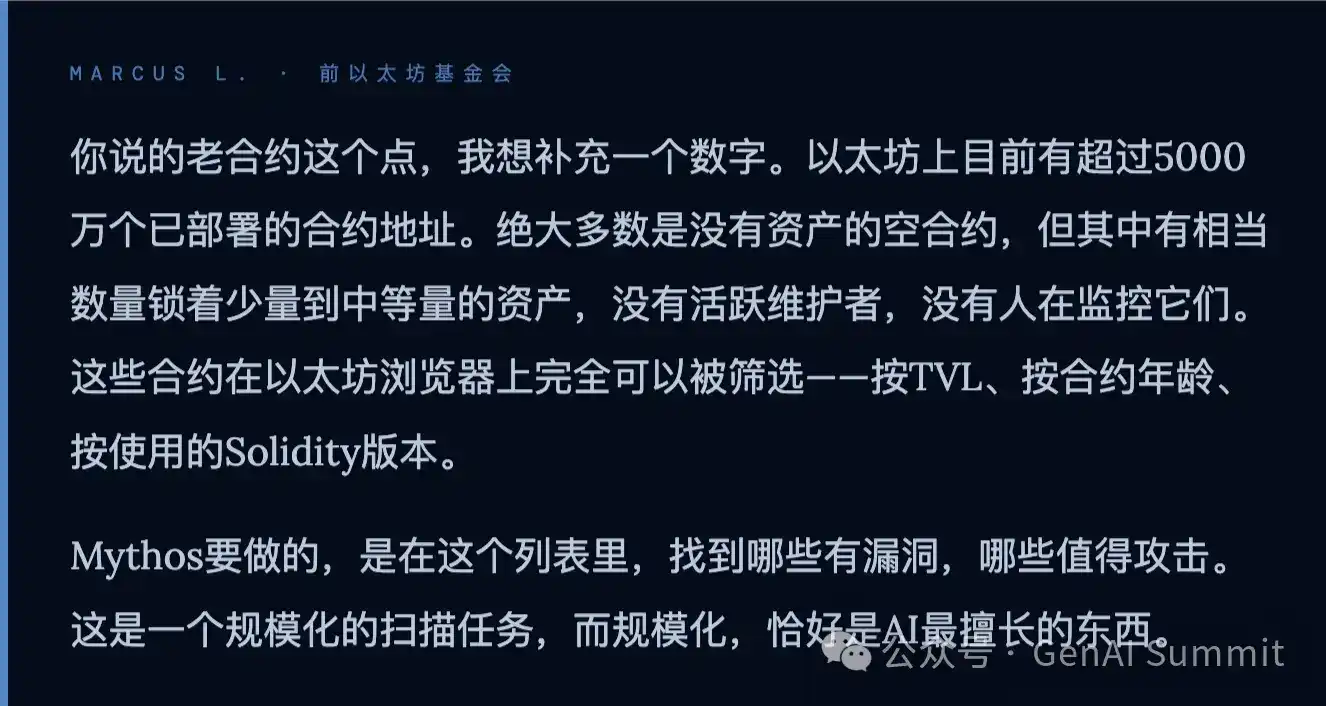
"The attacker's priority is clear: find contracts with a lot of money, old code, and no one guarding them. Mythos compresses the months needed for manual screening into hours."
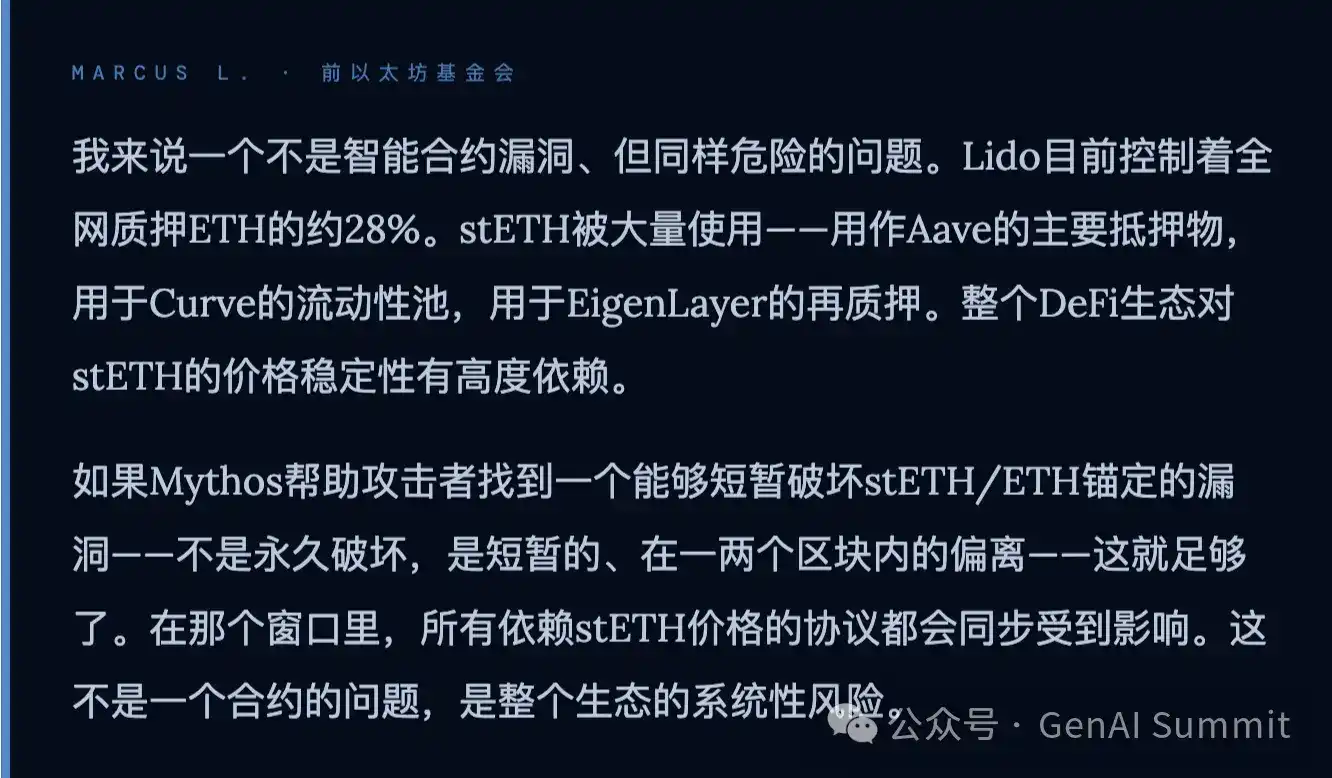
Third Thing: Lido Controls 28% of Staked ETH—This Is Another Type of Vulnerability
"stETH is the oxygen of Ethereum DeFi. You don't need to burn down the entire city; you just need to make the oxygen disappear for two minutes at the most critical moment."
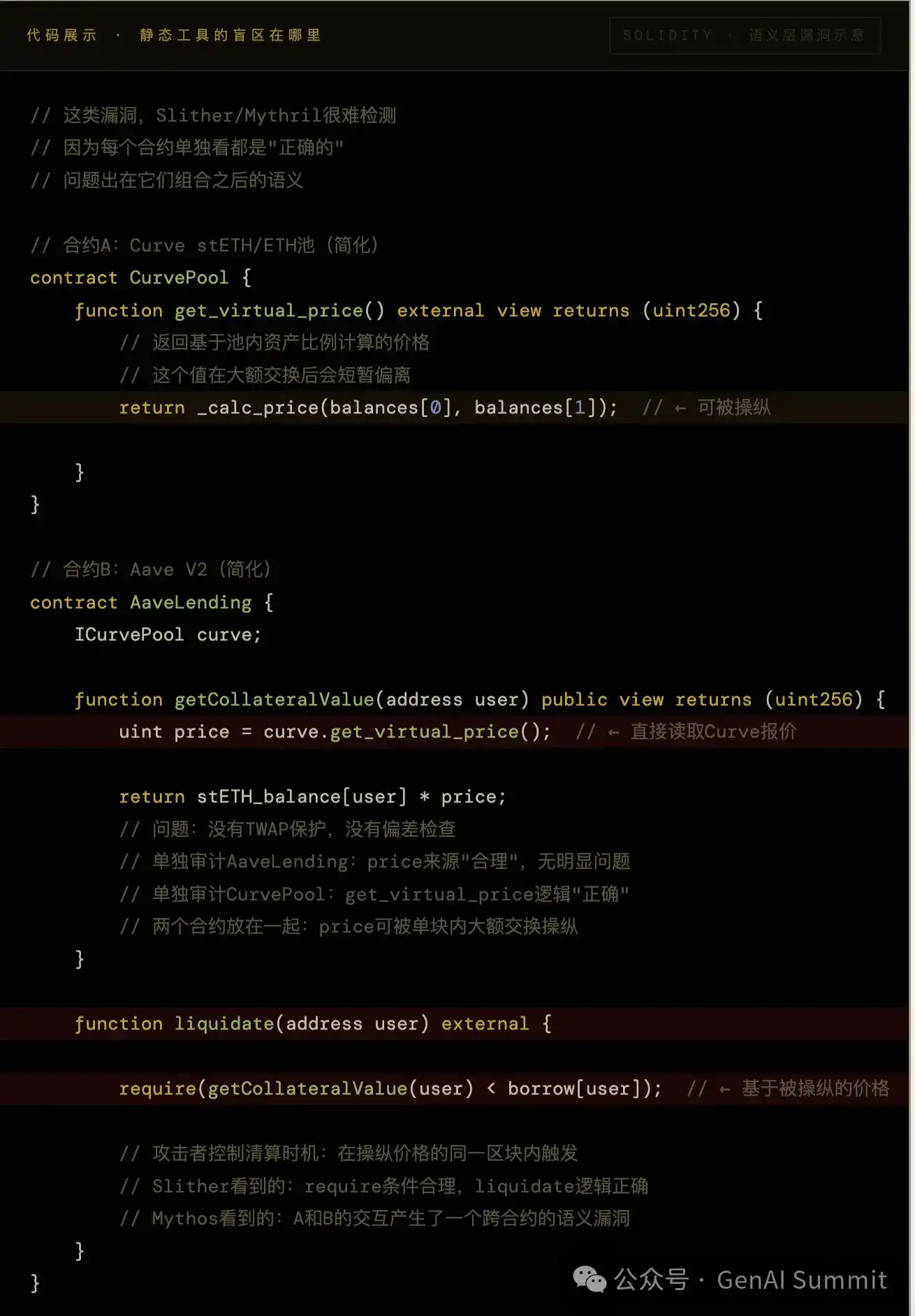
Fourth Thing: Audited Code Equals Unaudited in the Face of Mythos
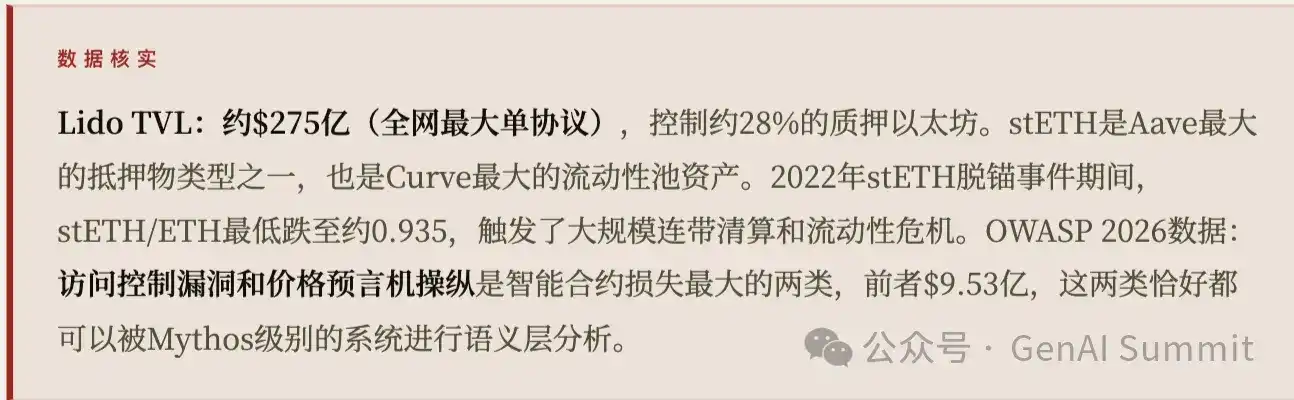
These types of cross-contract semantic vulnerabilities are the source of the largest historical attack losses. Audits are typically single-contract in scope; Mythos's analysis is whole-call-graph in scope.
"An audit is a snapshot from 2021. The operating environment of the contract in 2026 is different from the scene in that snapshot. Mythos is looking at today's reality, not that snapshot."
Fifth Thing: Governance Is the Moat, But Also the Slowest Leg
Alan asked Marcus: If Mythos discovered a severe vulnerability in Aave tomorrow that endangered tens of billions of dollars, how quickly could the Ethereum ecosystem effectively respond?
Marcus paused for a few seconds:
"Decentralization分散了响应决策给所有人。当AI将攻击准备时间压缩到零时,'所有人一起决策'这件事变成了最慢的那条腿。"
Sixth Thing: How Long Can Ethereum Survive Then
The hallway was now empty except for the two of them and me. A cleaner pushed a cart from afar. Marcus spoke first:
"How long Ethereum can survive equals the speed at which its community treats this matter with urgency. The technical answer has been given by Mythos. The human answer has not." They shook hands and walked away in different directions. I stood in the hallway, flipping through the densely packed notes on my phone. Ethereum: $68 billion, code fully public, contracts immutable, 28% of staked ETH concentrated in one protocol, governance response takes days. Mythos: The time to analyze a contract might be shorter than the time it takes me to flip through this page of notes. I don't know when the first truly AI-driven, Ethereum-scale security event will happen. I only know that Alan's words were right: In blockchain history, conversations about 'should have done something earlier' have happened too many times, always after the fact. Hopefully, this time is different.
Palo Alto · April 2026
TVL Data Source: DefiLlama Real-time Data (April 2026)
<极i data-index-in-node="53" data-path-to-node="20" style="font-size: inherit; font-family: PingFang SC,Helvetica Neue,Helvetica,Arial,Hiragino Sans GB,Heiti SC,Microsoft YaHei,WenQuanYi Micro Hei,sans-serif;">Vulnerability Statistics Source: OWASP Smart Contract Top 10 2026, coinlaw.io 2026 Security Report, arxiv 2504.05968
Dialogue compiled from现场笔记, Marcus L. is a pseudonym
Alan Walker doesn't use question marks.
Original Article Link
Related Questions
QWhat is the core security threat that Mythos poses to the Ethereum ecosystem, according to the article?
AMythos represents an AI-driven threat that can rapidly analyze and exploit vulnerabilities across the entire Ethereum smart contract landscape. It fundamentally changes the security paradigm by compressing the months of manual work required to find lucrative exploits into mere hours, targeting contracts that are valuable, old, and poorly defended.
QWhy does the article claim that 'audited contracts are equivalent to unaudited' in the face of Mythos?
ABecause traditional audits are like a 'photo from 2021'—a static snapshot of a contract's security in a past environment. Mythos performs a dynamic, system-wide analysis of the entire call graph in the current 2026 runtime environment, uncovering complex, inter-contract semantic vulnerabilities that old, isolated audits could never catch.
QWhat specific vulnerability related to Lido is highlighted as a major systemic risk?
AThe article highlights the centralization risk where Lido controls 28% of all staked ETH. An attacker with Mythos could target this point of failure, not to destroy the entire network, but to cause a critical, short-term disruption (e.g., making stETH 'disappear for two minutes'), which would severely impact the DeFi ecosystem that relies on it as 'oxygen'.
QHow does the decentralized governance model of major protocols like Aave become a liability against AI-powered threats?
ADecentralized governance, which distributes decision-making to a wide community, becomes the 'slowest leg' in a crisis. While an AI like Mythos can identify and prepare an attack in near-zero time, the human-driven process of achieving consensus, voting, and implementing a fix across a decentralized protocol could take days, creating a critical window of vulnerability.
QWhat is the ultimate conclusion about the survival of the Ethereum ecosystem in the context of the Mythos threat?
AThe conclusion is that Ethereum's survival is not a technical question—Mythos has already provided that answer by demonstrating the capability to find exploits. The real determinant is a 'human answer': how quickly and with what urgency the Ethereum community treats this new threat. The ecosystem's longevity depends on its speed of adaptation and response to this AI-powered security paradigm shift.
Related Reads
Trading
Hot Articles
Ethereum's DeFi Sector May Be the First to Surge in the Rotation Cycle
In the cryptocurrency market, rotation cycles are a common pattern of capital flow, especially during bull markets.
44.7k Total ViewsPublished 2025.08.20Updated 2025.08.20
Manyu: A Rising Meme Star on Ethereum Poised to Usher in a New Era of Shiba Culture
Manyu is a Meme token issued on Ethereum that delivers decentralized cultural and entertainment value through viral social media influence and community-driven engagement.
47.9k Total ViewsPublished 2025.11.27Updated 2025.11.27
In-Depth Research Report on Account Abstraction (AA): Generational Leap in Ethereum’s Account System & Landscape Reshaping in the Next Five Years
As a major evolution of Ethereum’s account system, AA is designed to address the fundamental security and experience bottlenecks of the “private key equals account” model in the EOA era.
3.5k Total ViewsPublished 2025.12.18Updated 2025.12.18