A patch has been available for nearly a year, but millions of Android users may still be running vulnerable crypto wallet apps — leaving their funds and private keys exposed to a known security flaw.
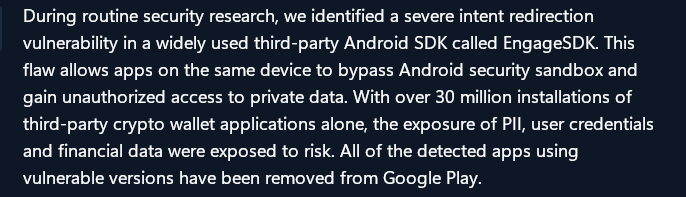
Microsoft’s Defender Security Research Team went public last week with details of a vulnerability it first caught in April 2025. The flaw lived inside a widely used software component called the EngageLab SDK, version 4.5.4.
Because that SDK is baked into thousands of Android apps, a single malicious app could trigger a chain reaction that reached far beyond itself.
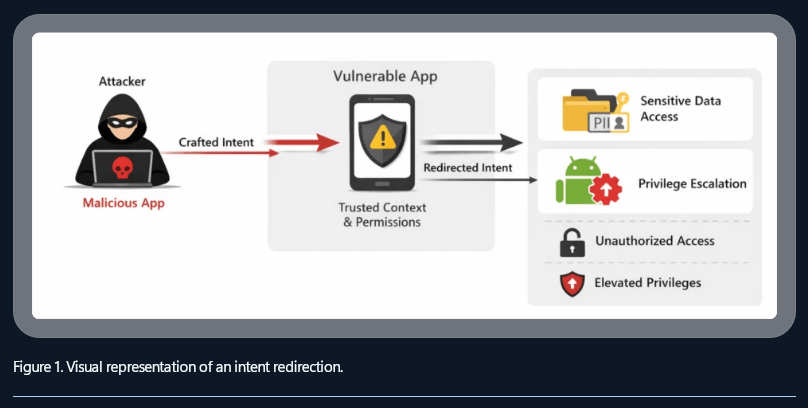
How The Attack Works
The method is called “intent redirection.” An attacker’s app sends a specially crafted message to any app running the flawed SDK version. Once that message lands, the targeted app is tricked into handing over read and write access to its own data — including stored seed phrases and wallet addresses.
Source: Microsoft
Android’s built-in sandbox system, which normally keeps apps from seeing each other’s data, was bypassed entirely. According to Microsoft, the attack affected more than 50 million apps across the Android ecosystem, with roughly 30 million of those being crypto wallets.
The vulnerability did not require the user to do anything wrong. No suspicious links. No phishing pages. Just having the wrong apps installed at the same time was enough.
Source: Microsoft
Response From Microsoft And Google
Microsoft moved quickly after its discovery. By May 2025, the company had brought Google and the Android Security Team into the response. EngageLab released a fixed version — SDK 5.2.1 — shortly after.
Reports indicate that both Microsoft and Google have since directed users on how to verify whether their wallet apps have been updated through Google Play Protect.
BTCUSD trading at $72,906 on the 24-hour chart: TradingView
Officials also pointed to a broader concern: apps installed as APK files from outside the Play Store are at higher risk, since they bypass the security checks that Google applies to apps listed in its official marketplace.
What Users Should Do Now
For most users who update their apps regularly, the risk has likely passed. But for anyone who has not updated since mid-2025, the recommended action goes beyond a simple app refresh.
Security teams are advising those users to move their funds into entirely new wallets, generated with fresh seed phrases. Any wallet that was active and unpatched during the exposure window should be treated as potentially compromised.
The disclosure comes alongside a separate Android chip vulnerability flagged the previous month and a new US Treasury initiative that pairs government agencies with crypto firms to share cybersecurity threat information — a sign that mobile security in the crypto space is drawing attention at the highest levels.
Featured image from Bleeping Computer, chart from TradingView