Author | Asher(@Asher_0210)
Last night, on-chain investigator ZachXBT exposed an 18-year-old hacker from the United States named Dritan Kapllani Jr. According to the disclosed information, this young man is suspected of involvement in multiple social engineering attacks targeting crypto users, with a total involved amount of approximately $19 million. Although he has not been formally charged yet, he has been included in U.S. judicial documents as a 'co-conspirator'.
This case quickly drew attention, not only due to the massive amount involved but also because of its highly dramatic starting point—a voice call meant for showing off wealth became the breakthrough for the entire investigation.
Just Bragged Once on Discord
On April 23, 2026, a dispute in a Discord voice channel kicked off this series of events.
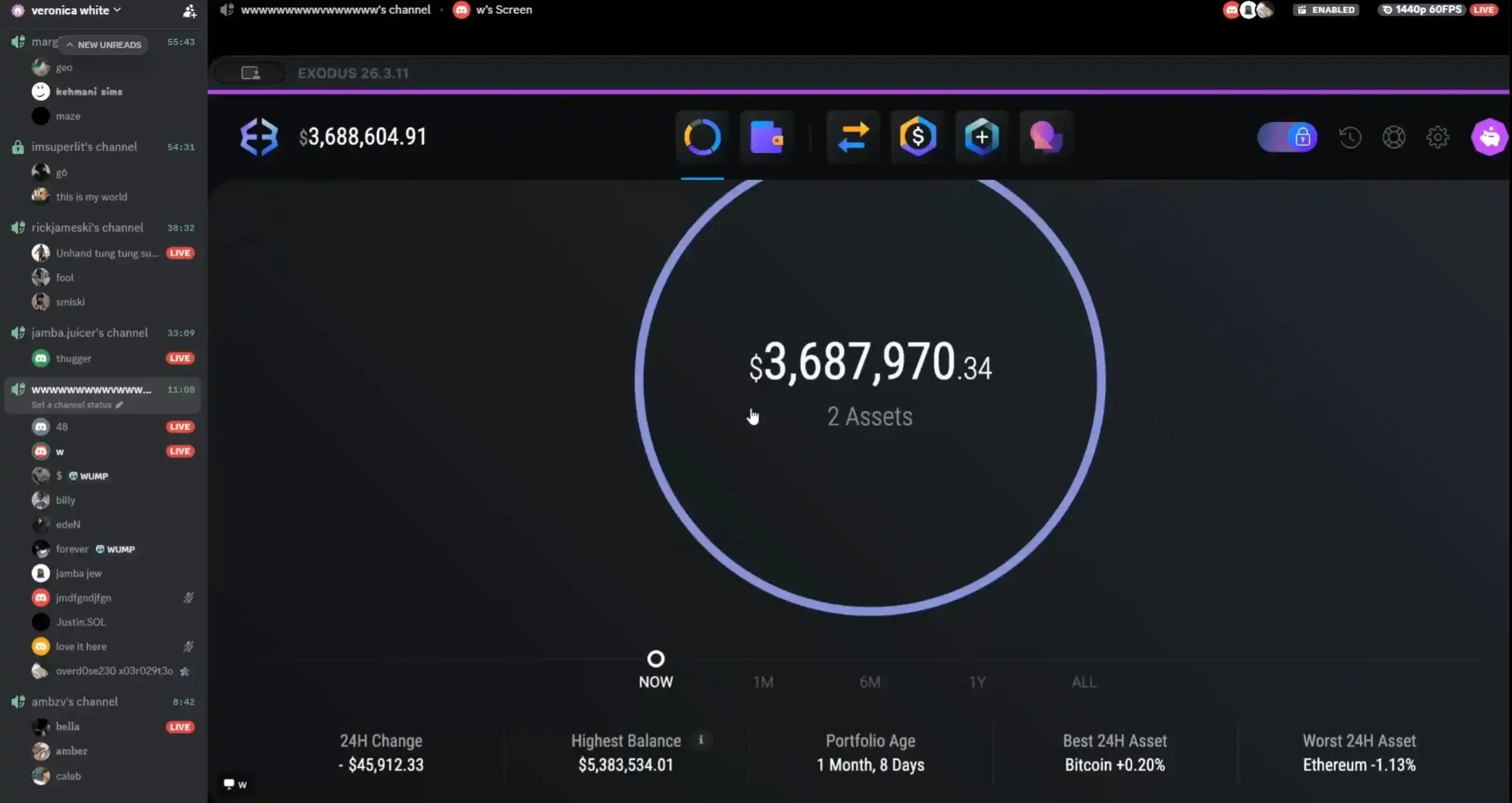
It was a voice call known as 'Band 4 Band', where participants compared their 'strength' in the most direct way—by displaying their holdings. The atmosphere quickly shifted from banter to competition. Driven by this mood, in order to prove he was richer, Dritan directly started a screen share, showing his Exodus wallet interface with a balance of about $3.68 million.
A few weeks later, this scene was revisited. On-chain investigator ZachXBT started from this address, piecing together originally scattered transactions one by one, gradually revealing a longer trail of funds.
A Trail of 185 Bitcoin Theft Funds Emerges
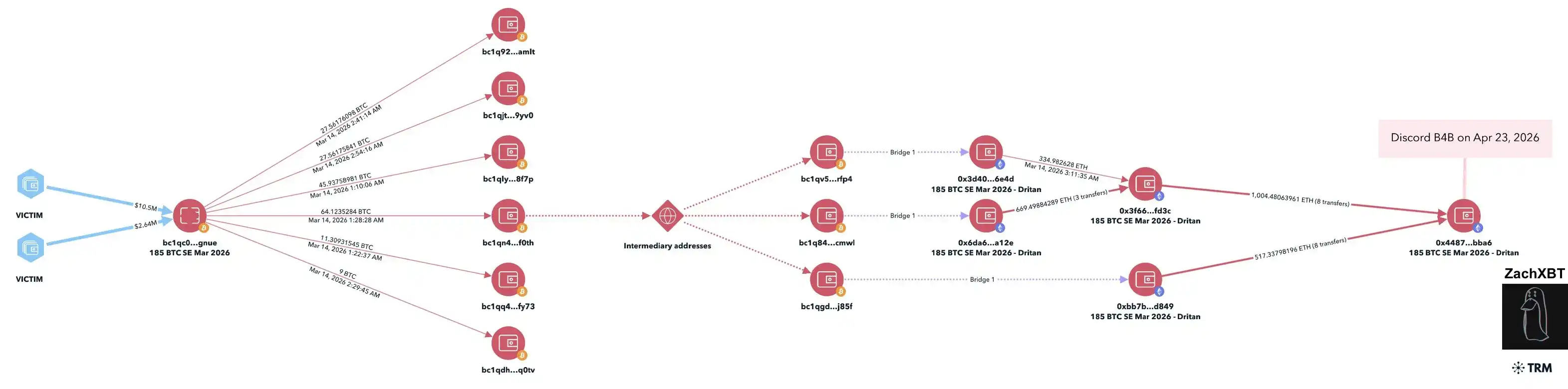
Going back to March 14, 2026, a social engineering theft involving 185 Bitcoins occurred, valued at about $13 million at the time. The funds were quickly moved out of the original address and rapidly entered an on-chain splitting system.
Just the next day, approximately $5.3 million of it was transferred into the wallet Dritan had shown during the Discord voice call (address: 0x4487db847db2fc99372a985743a26f46e0b2bba6). Over the following weeks, this sum of about $5.3 million was continuously split, transferred through multiple addresses, and flowed to different destinations. By the time of the April 23rd voice conversation, about $1.6 million had been further moved.
Not the First Time Involved in Crypto Theft
Tracing back from the wallet address Dritan showed, it soon became clear that the funds inside weren't just from that 185 Bitcoin theft.
According to on-chain analysis, the funds in this wallet can be traced back to multiple social engineering thefts in 2025, totaling over $5.85 million. Different victims, different times, but after the funds were transferred away, they would be quickly split, then moved through a series of addresses, following a very similar path. Matching up these funds transaction by transaction shows that many transfers ultimately landed in this wallet address Dritan displayed.
It's worth noting that Dritan once had a 'Band 4 Band' dispute with hacker John Daghita (Lick). Lick was later arrested for allegedly stealing approximately $46 million in U.S. government funds. In a later deleted Telegram post, he had publicly disclosed Dritan's old address (address: 0x97da0685dbba50b4cbabb0ca9e8336f4fbe41122), an act now appearing more like retaliation.
Judging from the on-chain behavior, this old address is highly consistent with the fund flow of the wallet Dritan displayed in terms of fund splitting methods, transfer paths, and subsequent destinations, and is therefore believed to be used by the same controlling party.
First Official 'Mention' in Judicial Documents
It wasn't until May 11, 2026, that this on-chain fund trail was formally confirmed for the first time in a judicial document. That day, the criminal indictment against Trenton Johnson was unsealed. He was charged for his involvement in the 185 Bitcoin theft case and faces up to 40 years in prison.
In the indictment, a key co-conspirator is labeled as 'Co-Conspirator 1 (CC-1)', and the on-chain analysis community has linked this identity to Dritan Kapllani Jr. Although Dritan has not been formally charged yet, he has moved from being an 'associated address' in on-chain inference to a 'co-conspirator' in the judicial narrative.
Furthermore, the same document mentions another involved person—Meme coin KOL yelotree, who is accused of assisting in money laundering through his Miami-based car rental business and faces up to 30 years in prison.
Turning 18, The End of a Decadent Life
Previously, Dritan had long lived a lavish lifestyle, frequently posting related content on Instagram and interacting with other hackers via Telegram. Within hacker circles, he was once considered to have a sort of 'protagonist aura'—multiple associated groups around him (such as ACG, 41 / RM Boyz, etc.) were successively dealt with by law enforcement, yet he himself remained untouched.
However, as he turned 18, this 'aura' came to an end, and his past actions began to be pursued legally.