Step by step
Bitcoin was not born in 2008. In fact, it is the result of decades of study and research in the field of computing. To best understand the origins of Bitcoin, we have to go back in time to 1933. Its prehistory is full of important events and to understand where we are today, we have to take a not inconsiderable time plunge.
From 1930 to 1940#
In 1933, Franklin Delano Roosevelt signed Executive Order 6102 that prohibited the private use of money in direct form, such as doubloons and coins, or in indirect form, such as banknotes representing collateral, such as gold. At the time, inflation in America was heavy, the federal public coffers were collapsing, and the economic situation was difficult. Consequently, the government confiscated all the gold of private citizens. This event is important to understand the history of bitcoin, as we are talking about the land of the free, the home of constitutional liberal democracy, not North Korea.
Jumping forward in time, in 1936, a young Alan Turing published a paper entitled On Computable Numbers, with an Application to the Entscheidungsproblem, which formed the theoretical basis for the practical digital revolution and of course Bitcoin could never have come into being without the digital revolution. Shortly afterwards, in 1938, the first computer working with electromagnetic pulses, called torpedo data computer, was built on top of a submarine. Although it could only perform trigonometric calculations, it was not a all-purpose computer like the ones we are used to today. In 1939, the first digital computer was born, called Z2, built by a German engineer, although there is some controversy as to the actual authorship of this calculator.
From 1970 to 1980#
In 1971 a very serious event happened, known as the Nixon Shock. Because of the war in Vietnam and the general recession, the US federal government needed money and President Richard Nixon decided to suspend the convertibility of the dollar into gold.
Until then, the entire world economic system was based on the following scheme: all official state currencies were convertible into US dollars and each country’s central bank promised the convertibility of its local currency into US dollars, while the US central bank promised the convertibility of these dollars into gold.
Nixon, claiming to want to protect the dollar from speculators, announced on live television that the convertibility of the dollar into gold would be temporarily suspended. It is now 2022 but Nixon’s suspension is still in full force.
------------------------------------------------------------------------------------------
From economics we return once again to technology. In 1974, Cerf and Kahn published a study entitled A Protocol for Packet Network Intercommunication, a protocol that allowed different computer networks to be connected together, known today as IP (Internet Protocol).
------------------------------------------------------------------------------------------
In 1976, researchers Diffie and Hellman published the paper New directions in cryptography.
Until then, encryption used a symmetric key, which worked (for example) as follows:
•Alice has a plaintext that she wants to encrypt and send to Bob;
•Alice “moves forward” each letter of the text by seven positions, resulting in a block of text with no logical meaning;
•Alice sends Bob the encrypted text;
•To recover the original text, Bob must “move back” each letter of the block of text received from Alice by seven positions.
•All cryptographic systems until 1976 were of this type and were insecure because they were based on the concept that one can ’turn a key one way’ and ’turn it the other way’ very easily.
In “New directions in cryptography” (asymmetric cryptography) theorised by Diffie and Hellman, it is still very easy to turn a key one way', but virtually impossible to turn the key the other way'.
Example of asymmetric encryption:
•Each party in a cryptographic exchange has two keys, a public and a private key;
•Alice generates a private key;
•Alice mathematically and deterministically calculates the public key associated with the private key;
•Alice can send her public key to anyone;
•Bob, who wants to communicate encrypted with Alice, will use Alice’s public key to make a text unreadable;
•The content of the text can only be decrypted by Alice’s private key.
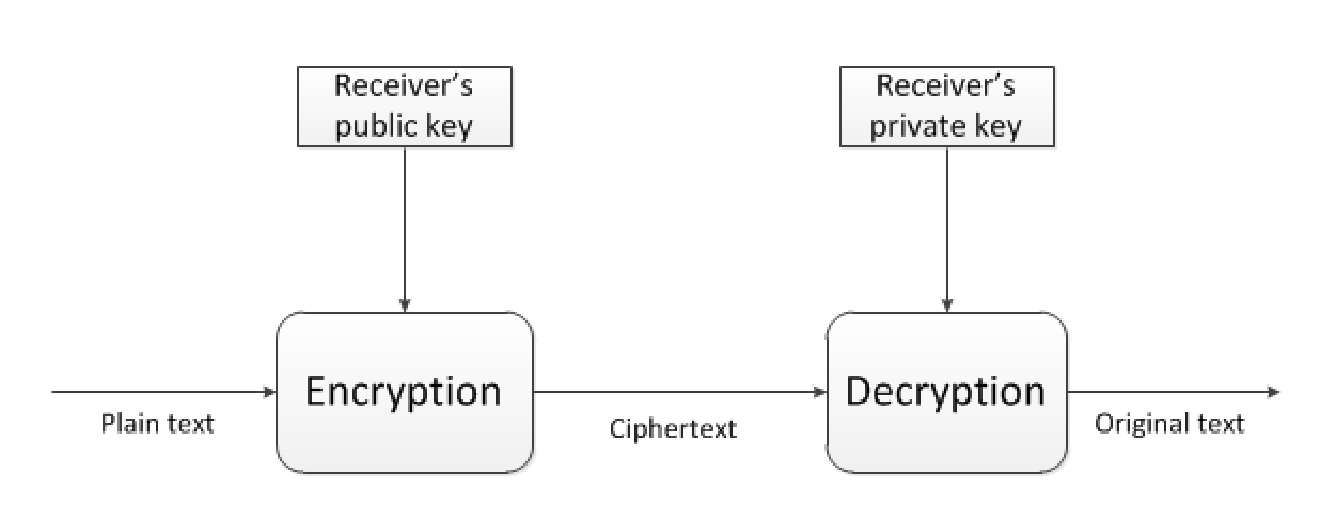
Example of asymmetric encryption
------------------------------------------------------------------------------------------
Two years later, in 1978, Rivest, Shamir and Adleman published a study entitled A Method for Obtaining Digital Signatures and Public-Key Cryptosystems. These three authors developed an algorithm that effectively made the asymmetric key cryptography introduced in 1976 possible, based on the use of prime numbers.
Prime numbers have an important characteristic: if I asked you to multiply the number 3 by the number 5, it would be very simple; but if I asked you for the prime factors of a prime number like 15, this operation is generally more complex. You would probably think it obvious that the prime factors of 15 are 3 and 5, but if you were to move this argument to very large numbers, it would be impossible to determine the solution, since there is no simple algorithm for solving this kind of problem.
The same year, a very influential book by a Nobel Prize winner in economics came out, entitled Denationalisation of Money by F.A. Hayek, an exponent of the Austrian school of economics. Hayek was very much against the state monopoly on money, which in his opinion `has never existed in the history of mankind’. According to Hayek, total monopoly is destructive and the idea he proposed was that money should go back to being issued (and chosen) by market actors, without any form of centralisation that could generate corruption and systemic crises.
In a way, Hayek predicted the immaculate conception of Bitcoin. 😁
In 1979, a mathematician named Claus P. Schnorr patented the idea of the merkle tree. To simplify, the basic idea of the merkle tree is to have a structure used to verify the integrity of a data set. It works by dividing the data into small parts, then creating pairs of these parts and calculating the hash (a unique, unpredictable and non-reversible value) of each pair. This process is repeated until all the parts have been included in a single root, called the merkle root, which summarises all the parts.
When you want to check the integrity of a data set, simply calculate the hash of each part and check that it is the same as the one found in the merkle tree. If the hash of a part is different, it means that the data has been modified or altered in some way. The merkle tree by the way is very efficient because it requires little disk space and allows the integrity of the data to be verified even when it is divided into small parts and distributed over a network.
From 1980 to 1990#
In 1980, Samuel Konkin III published the New Libertarian Manifesto, in which he advocated agorist thinking, i.e. the idea that:
It is not enough to proclaim the beauty of freedom and the ugliness of the state, but we must act pragmatically and build technical instruments capable of defeating the state.
– Samuel Konkin III
This thought would later be adopted by the chyperpunks movement.
In 1981, two significant events occurred:
•The Internet Protocol reached version 4, and it is fascinating to think that in 2022 this obsolete version is still being used (for example to read this site), despite the fact that the Internet has become the backbone of the modern world;
•Mr. David Chaum imagined an untraceable electronic mail protocol using digital pseudonyms and published the paper Untraceable electronic mail, return addresses, and digital pseudonyms. This publication is very important because it marks the beginning of the use of the concept of asymmetric cryptography to sign messages instead of encrypting texts.
To better understand the difference from the asymmetric encryption example above, let us look at this example:
•Alice sends a message to Bob and wants to prove that she is the owner of the message;
•Alice signs the message with her private key;
•Alice sends Bob the plaintext and the encrypted text with her private key;
•Bob knows Alice’s public key, so he can decrypt the text with Alice’s public key;
•If Alice actually signed the message with her private key, then the plaintext and the encrypted text (decrypted by Bob) will be identical.
Alice then certified the communication by proving that she had signed with her private key 🎉
From 1982 to 1988 there were several key steps:
•In 1982 there is no real key passage but it is indicative of a general culture that was spreading: the paper The Ethics of Liberty is published in which Murray N. Rothbard (another Austrian economist) suggests the abolition of the US Federal Reserve and a return to market money;
•In 1983, David Chaum published the paper Blind signatures for untraceable payments and for the first time the idea of using a cryptographic signature system to make untraceable digital payments was introduced;
•Two years later, in 1985, Koblitz published Elliptic curve cryptography proposing an alternative way to RSA to make public key signatures based on finite-field eliptic curves.
•Finally, 1988 saw the appearance of the Crypto Anarchist Manifesto by Timothy May, an anarchist agorist like Konkin III. In brutal summary Timothy states:
In the physical world the state controls us, but in the digital world, of the Internet, thanks to cryptography, the state will not be able to control us if we develop the right tools. We could create pseudonyms by exchanging ideas, services and products without necessarily having to be monitored.
– Timothy May
In 1989, David Chaum, developed an electronic payment system (with patent) based on asymmetric cryptography and blind signatures, called DigiCash.
The idea behind DigiCash was to provide an electronic means of payment that was secure, anonymous and guaranteed users’ privacy. To achieve this, Chaum used cryptography to protect transactions and to ensure that only the sender and the recipient could see the transaction details, all bundled with a system of ‘digital signatures’ to verify the authenticity of transactions and to prevent forgery.
DigiCash’s system was based on the digital currency ecash, which could be transmitted over the network and used to make online payments. Users could purchase ecash from banks or other financial institutions and use it to make payments quickly and securely.
It’s not Bitcoin yet, but we’re getting closer.
""
From 1990 to 2000#
In 1990, Claus Schnorr patented a type of signature using elliptic curve cryptography, which proved to be very effective and possessed certain features such as formal security demonstrability and aggregability of signatures. If Alice and Bob signed a text with their private keys and then summed their signatures, the result was a valid public key signature that was the sum of Alice and Bob’s public keys. Headaches? All in the norm, these technicalities have been important for the recent development of Bitcoin (such as taproot) and we will examine them later.
In 2008, Satoshi Nakamoto did not use Schnorr’s signatures, even though the patent had already expired, as he felt it would be dangerous to put an important system based on a new and untried technology into production without audit, test or peer review. Instead, he chose to use a less efficient algorithm called ECDSA, which among other things did not allow the aggregation of signatures like Schnorr’s.
In 1991, two important events occurred:
•Phil Zimmermann invented PGP (Pretty Good Privacy), which basically works by creating a public key and a private key for each user. The public key is used to encrypt messages or documents that are sent to the user, while the private key is used to decrypt messages or documents that are received by the user. In this way, only the user can read the messages or documents he receives, since he alone has the private key to decrypt them;
Researchers Haner and Stornetta published the paper How to time-stamp a Digital Document, also cited by Satoshi Nakamoto in his paper on Bitcoin. In this paper, the two researchers discovered how to prove the existence of a document at a given instant in time, but Bitcoin had to do a bit more: prove, in the same interval, both existence and uniqueness.
•In 1992, the chyperpunks were born in San Francisco, libertarian activists who advocated the intensive use of computer cryptography as part of a path of social and political change, for instance by hacking confidential archives to make public certain inconvenient truths.
The famous journalist Julian Assange was part of this movement.
In the following two years, 1993 and 1994, the following were published respectively:
•A chyperpunk’s Manifesto: the difference cyhperpunks and cryptoanarchists is that the latter advocate the use of cryptographic technology as a means to promote anarchy and individualism in society while chyperpunks are activists who use cryptography to change society and politics;
•The chypernomicon by Timothy May which in some ways is prophetic as it examines how cryptographic technology can be used to protect the privacy of personal data, to create a network for the exchange of goods and services without the control of government institutions, and to protect freedom of speech and expression in an increasingly interconnected world.
At this time, some chyperpunks were fighting the Crypto Wars in which the US government had declared that cryptographic systems and software for making cryptography were considered weapons and that exporting cryptography was tantamount to carrying ammunition. Hence the famous (and ridiculous) story of the illegal numbers.
Still in 1994, an alternative version of Chaum’s DigiCash called CyberCash was created by Daniel C. Lynch.
CyberCash was also based on fiat currencies like DigiCash, but had something more: a test system with a finite number of dollars. Test dollars had no value, but the fact that they were finite was a point in their favour, as they later became more valuable than CyberCash’s production dollars. The test dollars had become a collector’s item. 💀
Two years later, in 1996, lawyer Barry Downey and oncologist Douglas Jackson founded e-gold in California, because they argued that given the inconvertibility of the US dollar in gold and the lack of limits on the central bank’s printing of money, the state monetary system would be doomed to implode. However, gold was unsuitable for an internet age, so they decided to create a company that would use gold as collateral (subject to strict audits) and someone would pay with e-gold, they would write a digital cheque (using a system very similar to Chaum’s DigiCash) that could be sent to others via email addresses. This idea made it possible to exchange digital securities representing grams of gold.
During the same period, the US NSA also published a paper on how to create an online currency similar to DigiCash/CyberCash, although the actual purposes of this publication are not known.
Three important events took place in 1997:
•Adam Back created HashCash to solve the following problem: Adam Back, being a chyperpunk, talked to other people via (anonymous) e-mail and these were disposable. This created a problem, that of spam. To avoid spam, Adam used a very creative method. I explain with an example:
•Alice creates the e-mail message: Hello, how are you? with today’s date and then hashes the message;
•Alice sends Bob the text and the hash;
•Bob decides that if the message hash starts with 0 he will read the message, otherwise he will not read it;
•If Alice notices that the hash of her email starts with 1, she doesn’t send the message, and will edit the text slightly to create a new hash: if it comes out 0 she’ll send it (and Bob will read it), otherwise she’ll have to try again.
•And so on.
If Bob notices that he is still receiving too much spam, he can change the difficulty by dictating that he will only read emails if the message hash starts with 00 instead of 0. I only point out that in this way the difficulty does not double, it increases quadratically.
It’s exactly proof-of-work of Bitcoin! 👌
Satoshi Nakamoto cites Adam Back and his HashCash in the paper as the basis for the creation of Bitcoin.
There had already been a similar idea with the ‘92 paper Pricing via Processing or Combatting Junk Mail.
To conclude 1997, two other significant events occurred:
1.The computer scientist (and chyperpunk) Nick Szabo publishes a text that talks for the first time about smart contracts (this proves that smart contracts are not the invention of some recent shitcoiner). What Nick states in the paper Formalising and Securing Relationships on Public Networks is that not only is it possible to send cash from one public key to another as David Chaum does in DigiCash, but the problem can be generalised and stated that it is possible to use cryptography to secure online communications and transactions, thus protecting sensitive information and digital assets. Szabo mentions smart contracts, automated programmes that perform specific actions according to predefined conditions, to formalise relationships on the network and ensure their security, e.g. by implementing time or multi-signature tests;
2.The book The Sovereign Individual is published, which is also very prophetic and which we can summarise for simplicity with:
The world of sovereign states is coming to an end because the Internet will bring the possibility of choosing where to live, the sovereign individual will be able to go around with different nationalities, different residences, different passports. In doing so, the individual will be able to shop for the best state, the state will no longer be his ruler but will be his service provider.
After the very hot year of 1997 we come to 1998, which is even hotter because Nick Szabo invents a potentially decentralised version of DigiCash, called BitGold. He describes it in 1998 but does not publish it until 2005 in a complete and formal manner. It can be said that he is very close to the idea of Bitcoin even though there is still a fundamental piece missing.
Meanwhile, a very famous chyperpunk called Wei Dai publishes a paper creating B-Money without presenting any code but proposing the use of a system of smart contracts to manage transactions and ensure the security of the system. The smart contracts would have acted as automatic intermediaries for transactions, verifying that the conditions for their execution were met before executing the transactions. In this way, the system would have been able to function without the need for a central control body. There is, however, one problem that plagues both Nick Szabo and Wei Dai and that is that of double spending.
What happens when a user tries to spend the same unit of digital currency twice in a decentralised system? And how could this be prevented?
To this excellent question, Wei Dai proposes to establish an order for transactions and to do this, one votes to determine which transaction arrived first and which arrived later. However, there is a risk that some fake nodes will vote to make it appear that a transaction arrived earlier or later than it really is. Also, not all nodes in the network have the same voting power. Some may vote with more weight because they have placed digital money as collateral, and the weight of their vote depends on how much money they have placed as collateral (stake).
After various analyses, we come to the conclusion that it cannot work because it is a circular mechanism and to achieve this system the weight of the vote that decides which transaction came first is defined by the possession of the money in stake and the possession of the money in stake depends on previous transactions and their technology which in turn depends on a vote that depends on possession and so on. An endless loop. This logical circularity results in a weak system, which easily leads to attacks and centralisation.
This is exactly the proof-of-stake, already theorised and discarded in 1998 due to obvious architectural weaknesses ✔
Other important events in 1998:
•Bernard von NotHaus creates the Liberty dollar, a digital currency based on gold and silver. The Liberty Dollar system provided for the issuance of physical and digital gold and silver coins, as well as credit cards and cheques that could be exchanged as currency. The currency was based on an exchange rate set by the gold and silver market and could be used as an alternative to traditional currencies such as the US dollar. In 2009, the US federal state prosecuted him by sending him to jail, making it clear that there could be no competition in the liberal homeland;
•Peter Thiel creates Coinfinity, an online payment system for e-commerce, but the way he envisions it is something similar to Bitcoin:
In the physical world you will interact with the currency of your state, but when you are on the internet you are a citizen of cyber space and therefore without borders, boundaries and bureaucracy you will pay in the coinfinity currency – Peter Thiel
In 1999, dear Elon Musk entered the game and created X.com, a payment system with the same basic idea as Peter Thiel’s Coinfinity, and the same year, Milton Freeman delighted us with a prophecy:
I think the Internet will be a huge force in reducing the power of government in people’s lives. But there is one thing that is missing –and will soon be invented– and that will be a digital Internet currency in which A can transfer funds to B without B knowing A. This system does not yet exist, but it will exist and it will make the Internet the ultimate revolution. – Milton Freeman
From 2000 to 2007#
In 2000, there was the merger of Elon Musk’s X.com and Peter Thiel’s Coinfinity, which gave rise to PayPal. As always, the regulator arrived, categorically forbidding the development of the PayPal ideal, because there must be no competition with the US dollar. After a few visits from central bankers and the federal government, PayPal abandoned its ideal of an Internet currency, but became a payment network for traditional currencies (above licensed banks, with all that that entails: bureaucracy, censorship, inflation.
In 2001 we have three important events:
1.Bram Cohen created BitTorrent, a peer-to-peer protocol with open-source software at its base, impossible to stop due to its decentralised nature. In 2001, Napster already existed to exchange music, films and digital files in general, but it worked in a centralised manner.
Various music groups (e.g. Metallica) and record majors sued Napster, which had to shut down its servers, putting an end to this centralised phenomenon.
With BitTorrent, the fight against pirated music became virtually lost.
2.After the collapse of the Twin Towers on 11 September, the strictest financial regulation in the history of mankind (under the pretext of terrorism) with many sanctions and preventive surveillance was born. It was decided that politicians and bureaucrats of the federal government should know every movement and reason for the movement of funds of every human being, inside and outside the American jurisdiction. Regulations KYC and AML were introduced everywhere.
3.In an e-mail exchange between 16-year-old Peter Todd and the famous Adam Back, the latter explained that, as Wei Dai and Nick Szabo had already hypothesised, HashCash could be used not only as an anti-spam, but as the basis for a digital cash money system. However, Peter Todd pointed out a problem to Adam: the way computational power works is such that, if this proof of work were transferable between subjects, it would be hyperinflationary and the rationale is that with the proof of work you prove that you have incurred a computational cost (of machine time and energy) and the pivotal idea is to make this proof of work transferable, to prove that someone else has spent time and machine and I am just reusing their computational cost already incurred:
•A proof of work done in 2001 would be very different from a proof of work done in 2022, as the power of the machines is exponentially greater and would make the 2001 proof of work ridiculous;
•If there was a lot of demand for this ‘digital currency’, the price would go up, the profitability would go up and many people would do the job test, creating more supply. With more supply, the price would fall and very negative economic cycles would arise, similar to the fiat system.
The solution is automatic difficulty adjustment and will be solved by Satoshi 😎
In 2003, the video game Second Life became very famous thanks to a mechanic whereby one could buy goods, services and land (coff coff, metaverse? 😃) within the game with a currency called Linden Dollar, exchangeable both in-game and out-of-game. The game economy was so flourishing –and with monetary policies less stupid than those of the Federal Reserve– that the value of the single Linden Dollar brutally exceeded that of the US Dollar.
A Maltese company run by two Italians creates a trading centre for virtual shares and bonds in Linden Dollar called The Rock Trading. It is the oldest existing exchange, born even before Bitcoin.
As always and by now unsurprisingly, along came the regulator who banned the exchange of the Linden Dollar against the US Dollar and forced the developers of Second Life to peg the Linden Dollar 1:1 against the Dollar. The Linden Dollar then became irrelevant.
Another year goes by, it is 2004, and a chyperpunk called Hal Finney (creator of PGP 2.0) creates the Reusable Proofs of Work (RPOW) finally making HashCash’s proof of work transferable.
The problem of double spending always remained. Simplifying almost incorrectly, it stated that one had to trust the chip (e.g. Intel) that was inside the computer, which would sign the date of the transaction accurately and avoid double spending. It was a trust system of a hardware third party (the Intel chip) that, in theory, should not have colluded with the participants but was not very successful as a solution. We are at the peak because in 2005 Nick Szabo republished bitgold (conceived in 1998) and supposed to solve the problem of double spending not only by generating the currency but also by voting on the transaction history; the concept was similar to Wei Dai’s proof-of-stake, but instead of weighing the votes on the currency staked, he thought of doing it on the basis of the proof-of-work itself. Szabo sought developers, but then in 2006 removed his publication. We are very close to the idea of Bitcoin, almost within a whisker.
Year zero: 2008#
Two fundamental events happened:
1.The patent on Schnorr’s signature expired (even though Satoshi would not use it);
2.Yet another economic crisis created by fiat currency was triggered, namely the Subprime Mortgage crisis, orchestrated by various government entities whose task was to inflate a market of mortgages that could never be repaid, based on the manipulation of interest rates artificially lowered by the Federal Reserve.
On 31 October 2008 came the immaculate conception: Satoshi Nakamoto published the bitcoin paper.