A small but growing group of Bitcoin advocates and crypto fund managers is urging the network to accelerate work on quantum-resistant signatures, arguing that the perception of a future “quantum threat” could become a market risk long before it becomes a practical one.
Some supporters are pointing to a draft Bitcoin Improvement Proposal known as BIP-360, which would introduce a post-quantum signature option for Bitcoin addresses that could be vulnerable to future advances in quantum computing.
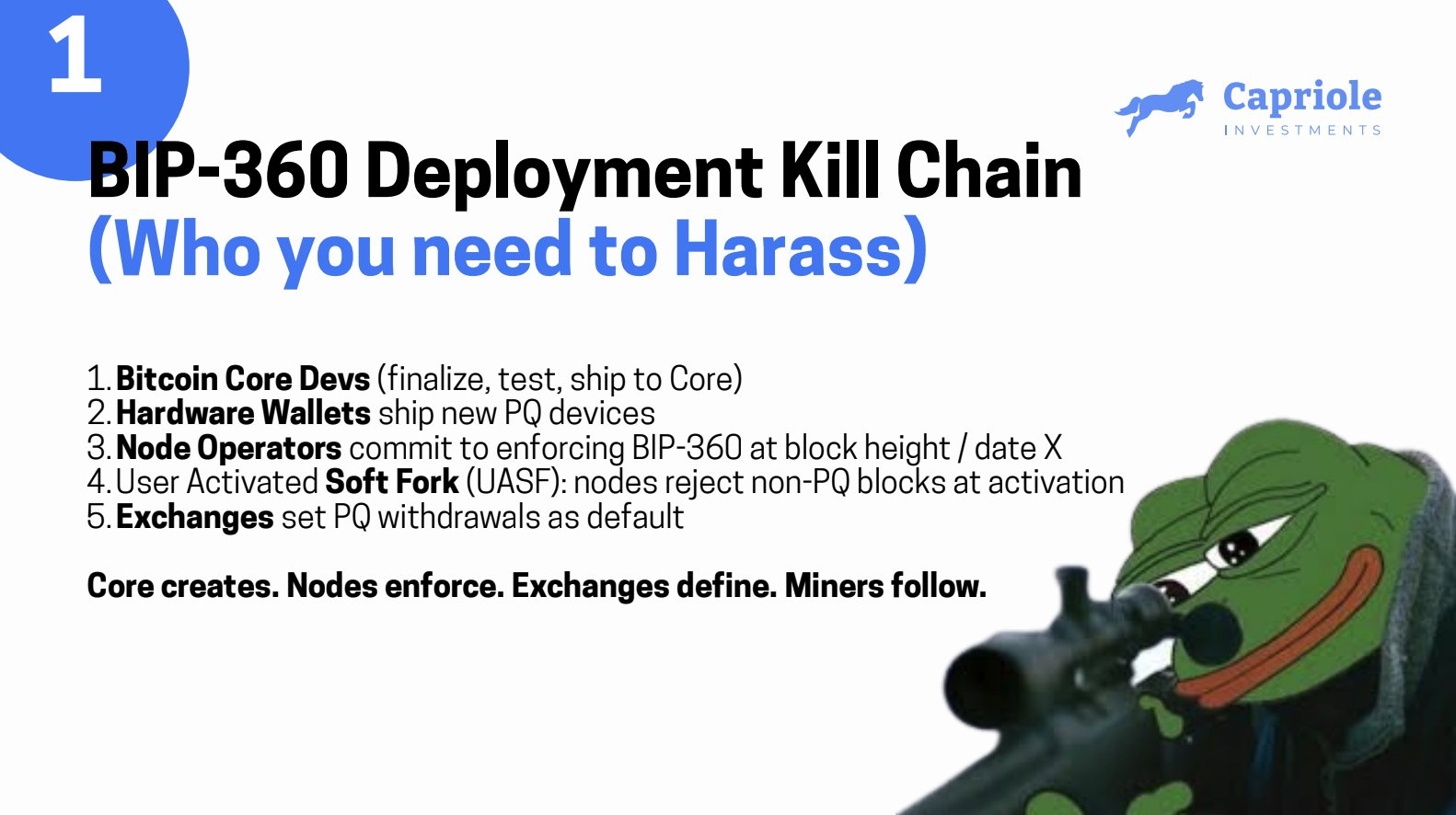
The implementation must be finalized and deployed in 2026, said Charles Edwards, the founder of quantitative Bitcoin (BTC) and digital asset fund Capriole.
However, the implementation of the new standard would require wider consensus among hardware wallet providers, node operators and cryptocurrency exchanges, added Capriole in a Thursday X post. Around “20-30% of Bitcoin will be taken by a quantum hacker in the next few years,” Edwards said. “I believe we should burn all coins that do not migrate to BIP-360 by 2028.”
Related: Bitcoin treasuries stall in Q4, but largest holders keep stacking sats
However, other industry watchers see quantum computing as a short-term risk for Bitcoin’s price.
“Pro-tip for quantum FUD promoters. Bitcoin does not use encryption. Get your basics right, or it’s a tell,” wrote Adam Back, co-founder and CEO of Blockstream, and the inventor of Hashcash, in a Thursday X post, adding that the quantum computing threat is still “decades away.”
Samson Mow, the CEO of Bitcoin technology company Jan3, also mocked the idea of early quantum computing threatening the Bitcoin network.
“Quantum computing can’t even factor 21, yet people are panic selling because they think it will kill Bitcoin,” wrote Mow in a Wednesday X post.
Related: Bitcoin investor loses retirement fund in AI-fueled romance scam
Taproot questions and competing proposals
Bitcoin’s latest Taproot format, which is perceived as quantum vulnerable, is declining in usage, from 42% of transactions in 2024 to just 20%, signaling that users may be worried about Bitcoin's quantum threat.
“I’ve NEVER seen the latest format losing adoption before. Taproot is Quantum Vulnerable, while older SegWit and Legacy are not,” wrote Bitcoin analyst Willy Woo, in a Wednesday X post.
Bitcoin’s Taproot update is the most important upgrade the cryptocurrency has experienced since 2017, when Segregated Witness (SegWit) was activated. Taproot aimed to upgrade the privacy and efficiency of the Bitcoin network.
Meanwhile, Back, one of the leading cryptographers, proposed a new hash-based signature scheme as a promising post-quantum alternative for Bitcoin, where security would rely solely on hash function assumptions similar to the ones currently used in the Bitcoin network’s design.
Hash-based signature schemes like ECDSA and Schnorr signatures “offer a promising path for securing Bitcoin in a post-quantum world,” according to the paper released by Back’s Blockstream Research on Dec. 5.
The Elliptic Curve Digital Signature Algorithm (ECDSA) uses elliptic-curve cryptography to verify the authenticity and integrity of a message. Schnorr signatures are another signature scheme praised for enhancing privacy and reducing data size, due to their ability to combine multiple signatures into one.
Magazine: Bitcoin vs. the quantum computer threat — Timeline and solutions (2025–2035)